Awesome cyber security facts
And here we are with an another hot topic that summarizes awesome facts about cyber in 2018. The infographic is re-published with a kind permission of its creator Vasiliii Chekalov and it was originally published on https://www.everycloudtech.com. It is definitely worth to read and I hope you will enjoy it as much as I did.

Awesome cyber security facts
SD-WAN Insights: Enabling Cloud POS Over Low-Speed Broadband
 Achieving consistent point-of-sale transactions and cloud application performance over low-speed broadband can be challenging, but finding the right SD-WAN can alleviate some of these difficulties.
Achieving consistent point-of-sale transactions and cloud application performance over low-speed broadband can be challenging, but finding the right SD-WAN can alleviate some of these difficulties.
Can your network handle digital transformation?
Digital transformation means different things to different organizations. Perhaps it means shifting workloads to the cloud, digging deeper into data analytics, giving your employees more options for mobility or automating more processes. But one thing’s for sure: no matter what your digital transformation strategy looks like, your network is going to be either the hero or a hindrance to your digital transformation efforts.
According to Gartner, “the top networking challenge… is improving agility.” Not a big surprise there. But what is surprising is Gartner’s advice to “shift investments away from premium networking products toward [your] existing network personnel.” That’s right: the answer to improving your network’s speed and agility is not by buying expensive, proprietary monster switches and premium automation solutions. Rather, it’s by letting the people who best know your network decide the best way to make your network more agile.
Agile networks require a deep understanding of your organizational objectives. A “one size fits all” approach to networking just doesn’t work anymore. In order to prepare your network for digital transformation, it has to be both customized to fit your organization’s needs and be flexible enough to adapt when those needs change. Agility requires responsive, Continue reading
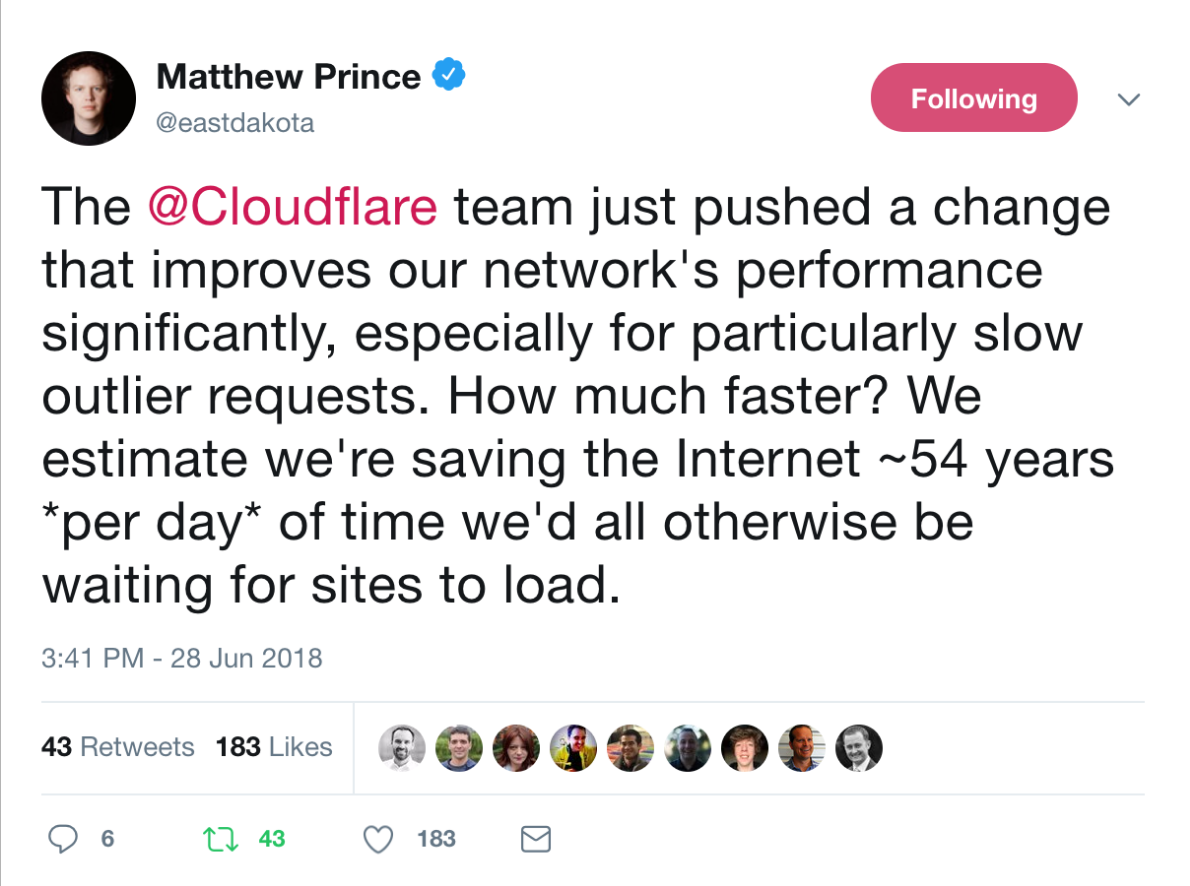
How we scaled nginx and saved the world 54 years every day
The @Cloudflare team just pushed a change that improves our network's performance significantly, especially for particularly slow outlier requests. How much faster? We estimate we're saving the Internet ~54 years *per day* of time we'd all otherwise be waiting for sites to load.
— Matthew Prince (@eastdakota) June 28, 2018
10 million websites, apps and APIs use Cloudflare to give their users a speed boost. At peak we serve more than 10 million requests a second across our 151 data centers. Over the years we’ve made many modifications to our version of NGINX to handle our growth. This is blog post is about one of them.
How NGINX works
NGINX is one of the programs that popularized using event loops to solve the C10K problem. Every time a network event comes in (a new connection, a request, or a notification that we can send more data, etc.) NGINX wakes up, handles the event, and then goes back to do whatever it needs to do (which may be handling other events). When an event arrives, data associated with the event is already ready, which allows NGINX to efficiently handle many requests simultaneously without waiting.
num_events = epoll_wait(epfd, /*returned=*/events, events_len, /*timeout=*/-1);
Continue readingUnderstanding the EIGRP command, “metric rib-scale”
You may recall that, when using Named-Mode EIGRP configuration you have automatic access to EIGRP Wide Metrics. In addition to providing you a new K-Value (K6 which is used against Jitter and Energy) the EIGRP Distance formula has been revised (what they call, “scaled”) to account for links above-and-beyond 10Mbps. Remember that with Classic-Mode EIGRP, the formula looked like this:
metric = ([K1 * bandwidth + (K2 * bandwidth) / (256 - load) + K3 * delay] * [K5 / (reliability + K4)]) * 256
In the formula, the “**bandwidth**” value was represented as:
BW = 10^7 / minimum BW
The problem with this “classic” method was that any link with a bandwidth higher than 10,000,000 bps (which only equates to 10Mbps, or 10^7 bps) was given the same BW value as an Ethernet segment. In other words, whether you put Ethernet into that formula, FastEthernet, Gigabit Ethernet, or anything even higher…they all equate to “1″. So in Classic Mode EIGRP, EIGRP couldn’t distinguish between these types of links to develop an accurate path to a destination.
When EIGRP Wide-Metrics were developed, Cisco “scaled” some portions of the formula to account for faster links (as Continue reading
Three-Day Workshop on Internet Governance Held in Quezon City, Philippines
This month was even more special for our Internet Governance campaign, with two significant (back-to-back) activities in the Philippines.
Earlier this month, the Philippines’ Department of ICT (DICT) signed a Memorandum of Understanding (MoU) with the Internet Society (ISOC) to facilitate the development of its National ICT Ecosystem Framework (NIEF) 2022. More details can be found here.
The following week, the Internet Society Asia-Pacific team conducted a face-to-face workshop on Internet Governance. The three-day workshop was organized as part of the Asia-Pacific Telecommunity 2018 work plan, and hosted by DICT.
Internet Society staff along with facilitators from the ISOC Philippines Chapter delivered this specially designed training workshop through presentations, Q&A sessions, individual and group activities, interactive quizzes, and a debate.
The majority of attendees were government officials from the Department of ICT, the National Privacy Commission, the National Telecommunications Commission, and the Upper and Lower Houses of Congress, but also included members of the technical community and civil society.
The sessions were highly interactive with participants actively asking questions and presenting their own ideas and arguments. The participant-led group discussions provided an opportunity for local issues to be openly discussed, and possible solutions to be considered.
For us, the workshop Continue reading
Connecting Postman to Firepower Management Center API
A few months back, I wrote an article about my Initial Observation on the Firepower FMC API. Today’s article takes this one step further with a step-to-step guide to connecting Postman to the FMC API. It is worth noting that this is not a directly useful process, but a process that should be expanded upon to achieve any objective that is better served by an API. Use cases might include bulk changes or integration with other security applications.
The Official REST API Guide can be found at the following URL.
Firepower REST API Quick Start Guide
It is also worth mentioning that the online API documentation can be found at https://<FMC-IP>/api-explorer on the FMC installation.
The general flow of the process we will be following is:
- Connect to FMC using basic authentication
- View the response to obtain the X-auth-access-token and DOMAIN-UUID
- Leverage the X-auth-access-token and DOMAIN-UUID in a request for access control policies
- Leverage the token, domain and policy ID to obtain a list of rules in that policy
- Leverage the token, domain, policy ID and rule ID to obtain rule details
Throughout this process, we will not store any variables and the process will be completely manual for comprehensive understanding. Continue reading
Selecting an ISP for Business: Factors to Consider
Price is an obvious consideration when picking an ISP, but security and co-location services are among other important criteria to consider.
Minecraft API with Workers + Coffeescript

The following is a guest post by Ashcon Partovi, a computer science and business undergraduate at the University of British Columbia in Vancouver, Canada. He's the founder of a popular Minecraft multiplayer server, stratus.network, that provides competitive, team-based gameplay to thousands of players every week

If you've ever played a video game in the past couple of years, chances are you know about Minecraft. You might be familiar with the game or even planted a tree or two, but what you might not know about is the vast number of Minecraft online communities. In this post, I'm going to describe how I used Cloudflare Workers to deploy and scale a production-grade API that solves a big problem for these Minecraft websites.
Introducing the Problem
Here is an example of my Minecraft player profile from one of the many multiplayer websites. It shows some identity information such as my username, a bitmap of my avatar, and a preview of my friends. Although rendering this page with 49 bitmap avatars may seem like an easy task, it's far from trivial. In fact, it's unnecessarily complicated.

Here is the current workflow to render a player profile on a website given Continue reading
Awake Security CEO Jumped Ship at Cylance to Build a New Unicorn
 Rahul Kashyap joins Awake from endpoint security company Cylance and says while endpoint has seen all the action over the past couple of years, “the network is where the opportunity lies.”
Rahul Kashyap joins Awake from endpoint security company Cylance and says while endpoint has seen all the action over the past couple of years, “the network is where the opportunity lies.”
Turnium Using Mature SD-WAN Platform to Target Juniper, HPE Customers
 The platform uses technology from Multapplied that is used in a white label form by Comcast, Rogers Communications in Canada, and Fusion Broadband in Australia.
The platform uses technology from Multapplied that is used in a white label form by Comcast, Rogers Communications in Canada, and Fusion Broadband in Australia.
ARM Strengthens Its IoT Portfolio With $600M Treasure Data Purchase
 Its push into IoT is undoubtedly initiated by ARM’s parent company SoftBank, which is investing billions in technologies including IoT through its SoftBank Vision Fund.
Its push into IoT is undoubtedly initiated by ARM’s parent company SoftBank, which is investing billions in technologies including IoT through its SoftBank Vision Fund.
IBM Trials Blockchain Platform With Barclays, Citi
 The company also scored a $140 million digital banking deal with Thai bank Krungsri.
The company also scored a $140 million digital banking deal with Thai bank Krungsri.