The Importance of ROI and Security with IoT
 A Cradlepoint Business Intelligence Report takes a snapshot of the IoT market today, focusing on where organizations stand with regard to IoT implementations.
A Cradlepoint Business Intelligence Report takes a snapshot of the IoT market today, focusing on where organizations stand with regard to IoT implementations.
A New Approach for Virtual Private Cloud to Data Center Connections
 As your organization’s VPC numbers grow, so do your challenges in connecting, securing, and managing them all.
As your organization’s VPC numbers grow, so do your challenges in connecting, securing, and managing them all.
Network Break 192: Dell Goes Public Again; Vodafone Trials Whitebox Optical
Take a Network Break! Dell Technologies is heading back to the public market, Vodafone tests a whitebox optical switch, and an LTE vulnerability rears its head.
Diane Bryant leaves Google Cloud after less than a year. Is Intel beckoning?
A Swedish private equity firm spins out SUSE, Micron products get banned in China, ZTE shuffles its executive ranks to comply with US requirements, and China approves Marvell’s acquisition of Cavium.
We’ve got links to all these stories after our sponsor messages.
Sponsor: InterOptic
InterOptic offers high-performance, high-quality optics at a fraction of the cost. If you re not doing optics correctly, you re going to pay for it upfront (and then later too). Don t be fooled by lesser optics. The difference between generic third-party and brand-equivalent optics matters.
Sponsor: Packet Pushers Ignition
The Packet Pushers have launched a brand new membership site called Ignition. Ignition offers free and premium memberships and hosts exclusive content for subscribers, including videos, reports, blogs, and more. Check it out at ignition.packetpushers.net.
Show Links:
Dell moves to go public, spurns IPO – Reuters
Vodafone begins its trek with Voyager – Cumulus Networks Blog
Vodafone deploys TIP s Voyager in a live network Continue reading
The Week in Internet News: WhatsApp Looks to Combat the Spread of Fake News
Fake messaging: WhatsApp, the popular messaging tool, will pay researchers up to $50,000 to study the spread of fake news through its platform, notes Mashable.com. The announcement came after reports of mob lynchings in India fueled by false information spread on WhatsApp, reports the Washington Post. India’s government asked the app maker to take immediate action to stop the spread of fake news.
Defining fake news: While we’re still on the topic of fake news, Cambodia’s recent crackdown on false information is raising concerns about press freedom in the country, reports The Guardian. A new directive aimed at fake news on websites and social media allows for violators to be jailed for two years and fined US$1,000, but civil rights groups said the new rules could give “authorities the power to silence individuals at the click of a button.”
Fired by a computer: A Los Angeles worker was recently shown the door by an automated process that seemed to assume he was let go after his original manager was laid off, the BBC reports. The case could raise questions about artificial intelligence processes, but the real fix would be a more intelligent machine, The Conversation says.
AI manages Continue reading
Goodbye, content.ipspace.net
It turns out that while I cannot bring myself to writing or creating other content during the summer break, it feels perfectly fine to be a janitor and fix small things on the web site.
One of the long-outstanding items: get rid of the free content web site that never went where I wanted it to go… one can do only so much in 24 hours. All the features available on content.ipspace.net are now part of the main ipSpace.net web site including pointers to free content and list of free presentations.
During the summer break, I’m publishing blog posts about the projects I’m working on. Regular blog posts will return in autumn.
Scales Tip in Cisco-Arista Legal Battle
In the long-running legal dispute between fierce networking rivals, Arista appears to be successfully fending off Cisco's patent and copyright claims.
Rough Guide to IETF 102
Starting next weekend, the Internet Engineering Task Force will be in Montreal for IETF 102, where over 1,000 engineers will discuss open Internet standards and protocols. The week begins on Saturday, 14 July, with a Hackathon and Code Sprint. The IETF meeting itself begins on Sunday and goes through Friday. We’ll be providing our rough guides on topics of mutual interest to both the IETF and the Internet Society as follows:
- Overview of ISOC @ IETF (this post)
- Internet Infrastructure Resilience
- Internet of Things
- IPv6
- DNSSEC, DANE and DNS Security
- Identity, Privacy, and Encryption
For more general information about IETF 102 see:
Immediately prior to the IETF meeting, ICANN are hosting a DNS Symposium on the theme “Attention, Domain Name System: Your 30-year scheduled maintenance is overdue.” The ICANN DNS Symposium will take place in the same venue as the IETF 102 meeting on Friday 13th July.
Here are some of the activities that the Internet Society is involved in during the week.
Applied Networking Research Workshop (ANRW 2018)
The ACM, IRTF and ISOC Applied Networking Research Workshop will take place on the Monday of IETF week, Continue reading
Using JUNOS Firewall Filters for Troubleshooting & Verification | QFX5110
The Junos firewall filter feature can be a really useful tool for troubleshooting and verification scenarios. I was recently troubleshooting a packet loss fault and I was fairly sure it was an asymmetrical routing issue but I needed a quick way of verifying. And then a colleague said, “hey, how about a firewall filter?”. Of course, assuming IP traffic, we can use a Junos firewall filter to capture specific traffic flows.
Overview
In this scenario, we have a pair of Juniper QFX5110 switches that are both connected to an upstream IP transit provider. They are also connected to a local network via a VMware NSX edge. We’re going to use a firewall filter on QFX1 and QFX2 to identify which QFX is being used for egress traffic and which QFX is being used for ingress traffic. More specifically, the flow is an ICMP flow between a host on 212.134.79.62 and Cloudflare’s DNS service.
Topology
Firewall Filter
So we’re essentially going to create a firewall filter to count specific egress traffic and apply as an import filter on both QFX switches. We’re also going to create another firewall filter to count the return traffic and apply Continue reading
Registration Open for “Cyber Diplomacy Meets InfoSec and Technology” Alongside IETF 102
As we recently announced, the Global Commission on the Stability of Cyberspace (GCSC) will host a lunch panel on “Cyber Diplomacy Meets InfoSec and Technology” alongside IETF 102 on Tuesday, 17 July. Registration opens today in two time slots for global time zone fairness, at 08:00 UTC and 20:00 UTC. Register here.
The Global Commission on the Stability of Cyberspace is developing norms and policy initiatives that intend to counter the risk to the overall security and stability of cyberspace due to rise of offensive cyber-activities, and especially those by states. During this session, the Commission wants to inform and engage with the IETF community on its work so far and the work that is in the pipeline.
The Internet Society is assisting with logistics. Internet Society Chief Internet Technology Officer and GCSC Commissioner Olaf Kolkman will moderate the panel. The panelists are:
- Irina Rizmal, researcher at the DiploFoundation specialized in policy analysis in matters pertaining to national security and defense.
- Bill Woodcock, Commissioner and Executive Director at Packet Clearing House, the non-profit agency that supports critical Internet infrastructure.
- Jeff Moss, Commissioner, founder of Black Hat and Defcon, member of the DHS security council, Continue reading
Comparing Serverless Performance for CPU Bound Tasks
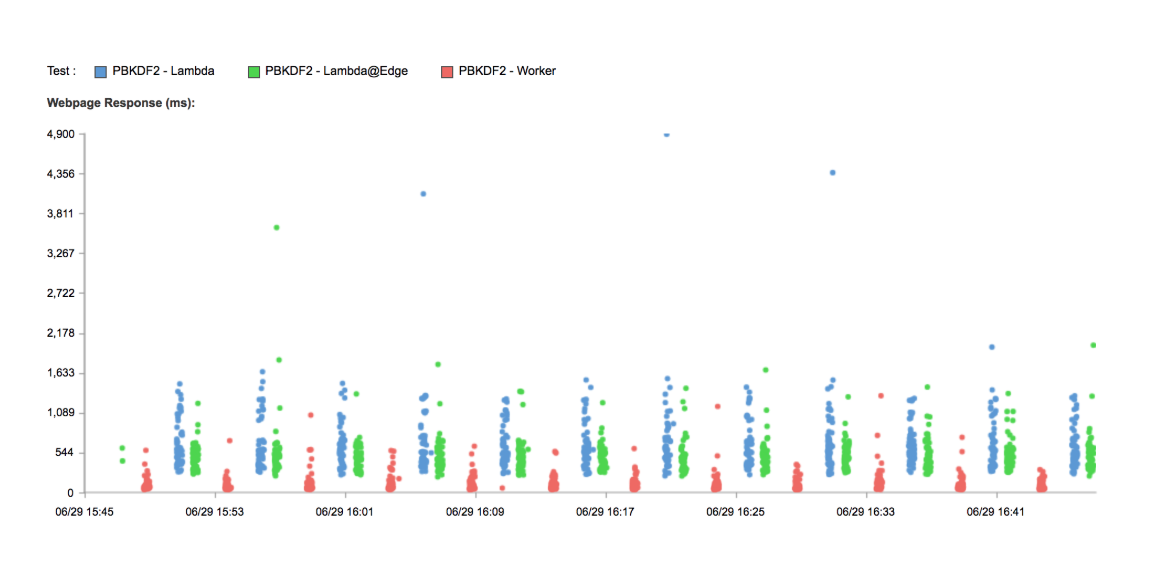
This post is a part of an ongoing series comparing the performance of Cloudflare Workers with other Serverless providers. In our past tests we intentionally chose a workload which imposes virtually no CPU load (returning the current time). For these tests, let's look at something which pushes hardware to the limit: cryptography.
tl;dr Cloudflare Workers are seven times faster than a default Lambda function for workloads which push the CPU. Workers are six times faster than Lambda@Edge, tested globally.
Slow Crypto
The PBKDF2 algorithm is designed to be slow to compute. It's used to hash passwords; its slowness makes it harder for a password cracker to do their job. Its extreme CPU usage also makes it a good benchmark for the CPU performance of a service like Lambda or Cloudflare Workers.
We've written a test based on the Node Crypto (Lambda) and the WebCrypto (Workers) APIs. Our Lambda is deployed to with the default 128MB of memory behind an API Gateway in us-east-1, our Worker is, as always, deployed around the world. I also have our function running in a Lambda@Edge deployment to compare that performance as well. Again, we're using Catchpoint to test from hundreds of locations around Continue reading
