3 people passed CCDE Practical/Lab exam on February 2018 from my class
3 people sent me their feedbacks after they pass February 2018 CCDE Practical/Lab exam. Exam result was announced on May 2018 (2 to 3 months after according to new CCDE Practical exam result policy) but I couldn’t find a chance to share their results on the website. I can’t count anymore how …
Continue reading "3 people passed CCDE Practical/Lab exam on February 2018 from my class"
The post 3 people passed CCDE Practical/Lab exam on February 2018 from my class appeared first on Cisco Network Design and Architecture | CCDE Bootcamp | orhanergun.net.
3 people passed CCDE Practical/Lab exam on February 2018 from my class
3 people sent me their feedbacks after they pass February 2018 CCDE Practical/Lab exam. Exam result was announced on May 2018 (2 to 3 months after according to new CCDE Practical exam result policy) but I couldn’t find a chance to share their results on the website. I can’t count anymore how …
Continue reading "3 people passed CCDE Practical/Lab exam on February 2018 from my class"
The post 3 people passed CCDE Practical/Lab exam on February 2018 from my class appeared first on Cisco Network Design and Architecture | CCDE Bootcamp | orhanergun.net.
Jask Raises $25M Series B Funding for Autonomous Security Platform
 This brings its total to $39 million. Kleiner Perkins led the funding round with participation from Battery Ventures, Dell Technologies Capital, TenEleven Ventures, and Vertical Venture Partners.
This brings its total to $39 million. Kleiner Perkins led the funding round with participation from Battery Ventures, Dell Technologies Capital, TenEleven Ventures, and Vertical Venture Partners.
Ciena’s Blue Planet Dynamically Connects to a Variety of Clouds
 The company’s SDN technology was chosen by CoreSite Realty to help its customers connect to public and private clouds and to adjust bandwidth as needed.
The company’s SDN technology was chosen by CoreSite Realty to help its customers connect to public and private clouds and to adjust bandwidth as needed.
Codefresh Kubernetes-Native CI/CD Platform Lures Microsoft Cash
 The company's platform helps developers to automate their application deployment to Kubernetes in as little as 10 minutes and is more Kubernetes-centric than Spinnaker.
The company's platform helps developers to automate their application deployment to Kubernetes in as little as 10 minutes and is more Kubernetes-centric than Spinnaker.
NSX Cloud Blog Series Part 2: A Consistent Security Posture Across Your Hybrid Cloud
We now dig deeper into the cloud security use-case. As more and more companies embrace cloud, the cloud IT teams are tasked with the responsibility of ensuring that these cloud deployments are secure. Cloud inherently brings in new environments, and these cloud security teams are now faced with ensuring Enterprise security policy consistency across these multiple disparate cloud environments.
VMware NSX Cloud addresses these challenges, offering a common security and micro-segmentation platform across the on-premises and cloud environment. Together with NSX Data Center, it provides a single pane of glass to provision and manages consistent security controls not only for cross-cloud communication but also within each cloud.
Let’s start with VISIBILITY. You can’t protect what you can’t see. As a cloud infrastructure/security team, you may have to manage 1 AWS cloud account (subscription in Azure) and 1 AWS VPC (VNET in Azure) … or you may be managing 500+ accounts/subscriptions, each having multiple VPCs / VNETs. As cloud deployments bring automation and higher levels of agility, the cloud footprint that you would be responsible for can quickly become large and constantly evolve. How do you ensure that this dynamic environment is secure?
Focused on this specific Continue reading
T-25 days until Chrome starts flagging HTTP sites as “Not Secure”
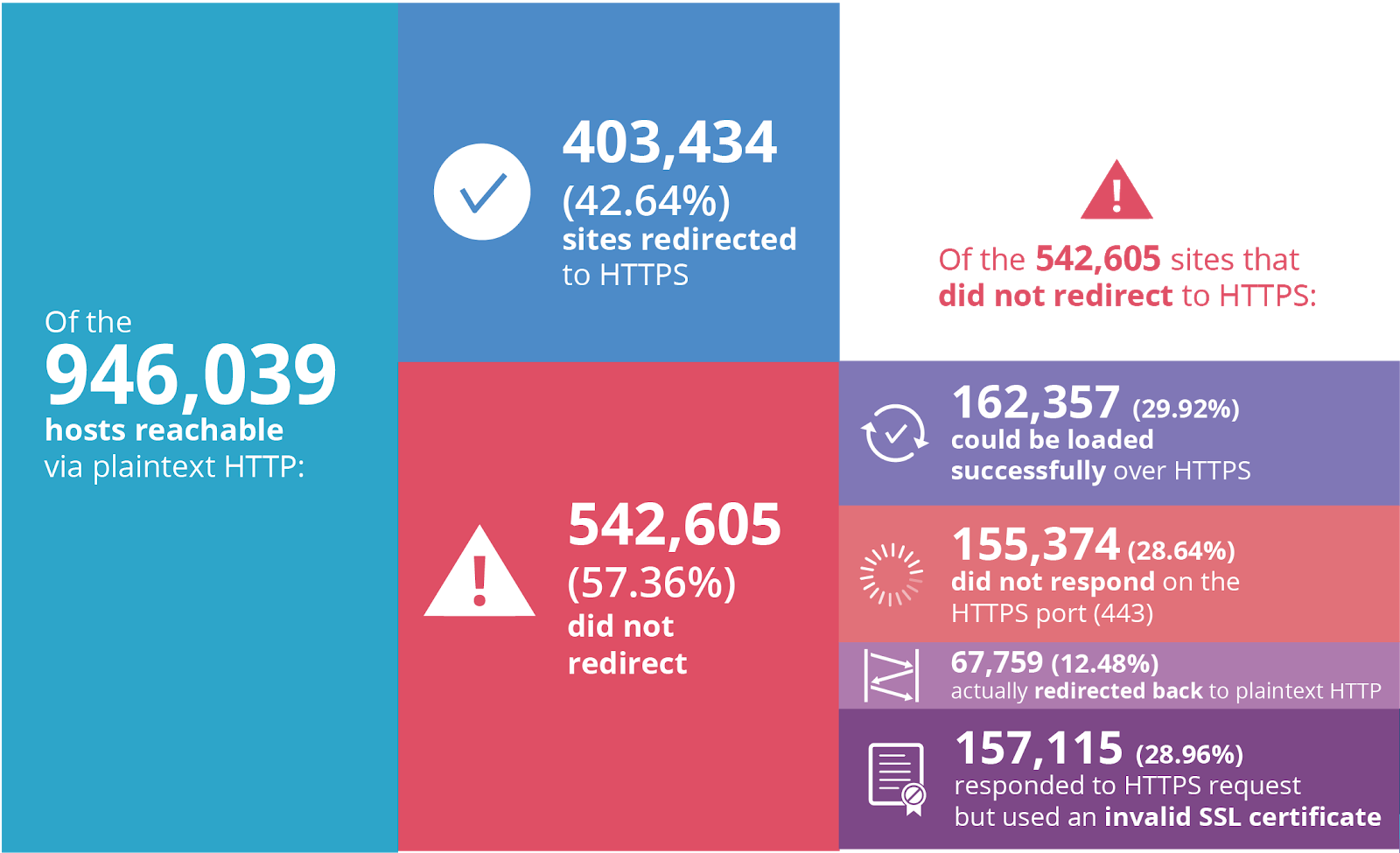
Less than one month from today, on July 23, Google will start prominently labeling any site loaded in Chrome without HTTPS as "Not Secure".
When we wrote about Google’s plans back in February, the percent of sites loaded over HTTPS clocked in at 69.7%. Just one year prior to that only 52.5% of sites were loaded using SSL/TLS—the encryption protocol behind HTTPS—so tremendous progress has been made.
Unfortunately, quite a few Continue reading
Data Center Tech ‘Graduation’: What IT Pros Have Learned
What new technologies have IT pros deployed and experimented with this year? SolarWinds finds out what tech its THWACK community members have tried out in 2018.
Techniques of a Network Detective: A New Series
Put your detective hat on your head and your Network Detective badge on your lapel. Introducing a new blog series – Techniques of a Network Detective. This series will focus on the detective work (troubleshooting side) of our jobs as network engineers.
For over 30 years I’ve been playing in the “world of IT”. During those years there have been a lot of changes in our world. But through all that change, there has been a thread, for me, that has always remained constant. A thread and a passion that always seemed to be with me in every job over all these years.
Troubleshooting!
Being a “Network Detective” is much the same as being a regular detective in many ways. As a Network Detective we get put on a “case” – the “Case of the Missing Packets” maybe. We go to the crime scene and try to find answers so we can solve the “who done it”
When a “crime” happens you need to be right there interviewing the suspects, surveying the crime scene, asking the right questions. Trying to quickly figure out what is happening, where it is happening, and why it Continue reading
Network Infrastructure as Code in Network Automation Online Course
In mid-May, I ran an onsite network automation workshop, and the manager organizing the workshop for his team invited me to a dinner with his peers. Not surprisingly, they wanted to hear about the topics covered in the workshop, and as soon as I mentioned Network-Infrastructure-as-Code several of them said “yes, that definitely needs to be covered.”
Read more ...