Upcoming Webinars: June 2018 and Beyond
Wow. Where did the spring 2018 go? It’s almost June… and time for a refreshed list of upcoming webinars:
- Christoph Jaggi will run do another free webinar – this time on Ethernet Encryptors– on June 5th;
- I’ll run an Amazon Web Services Networking workshop in Zurich on June 13th;
- We had to change the schedule a little bit: the last webinar before the summer break will be an overview of real-life automation wins on June 19th.
Network Break 186: VPNFilter Malware Spreading; Happy GDPR Day!
Take a Network Break! Security researchers are tracking the VPNFilter malware, which has infected an estimated 500,000 devices, GDPR regulations have gone into effect, and the OpenStack Summit debuts a new project called Airship.
Startup Lumina Networks bags $10 million in funding from Verizon, AT&T, and others; Pica8 releases PicaPilot for network fabric orchestration; and Huawei wins “Supplier of the Decade” from Vodaphone.
HPE released its quarterly earnings and warned of challenges for the second half of the year, and Amazon’s Echo unexpectedly recorded and sent a couple’s conversations.
Get links to all these stories after our sponsor message, and stay tuned for a Coffee Talk with Silver Peak.
Sponsor: Cisco Systems
Find out how Cisco and its trusted partners Equilibrium Security and ePlus/IGX can help your organization tackle the General Data Protection Regulation, or GDPR. Tune into Packet Pushers Priority Queue episode 147 to get practical insights on how to get your arms around these wide-ranging rules.
Coffee Talk: Silver Peak and Solis Mammography
On today’s Coffee Talk conversation we discuss SD-WAN with Solis Mammography and how its Silver Peak SD-WAN deployment helped the company streamline the movement of about a petabyte of imaging data efficiently and security.
Show Links:
Research: BBR Congestion-Based Congestion Control
Congestion control has proven to be one of the hardest problems to solve in packet based networks. The “easy” way to solve this problem is with admission control, but this “easy” solution is actually quit deceptive; creating the algrorithms and centralized control to manage admission control is much more difficult than it seems. This is why many circuit switched networks just use some form of Time Division Multiplexing (TDM), giving each device connected to the network a single “slot,” and filling empty slots with idle frames, ultimately throwing bandwidth away in the name of simpler computation of fairness.
The problem space has, however, attracted a lot of research. In this post, I’ll be looking at one such effort, a research paper published in the October 2016 edition of ACM Queue describing a system called BBR, a congestion-based congestion control system. At the heart of this system is the concept of the bottleneck link, or bottleneck in the path, which is the lowest bandwidth, highest delay, or perhaps the most congested link in the path between two hosts. The authors use the following figure to describe the current operational point of most congestion control systems, and then the optimal point of Continue reading
Advertising Multiple Paths in BGP (BGP-Addpath)
The post Advertising Multiple Paths in BGP (BGP-Addpath) appeared first on Noction.
On Why I’m Shifting my Career Focus to Software
For the past few months I’ve been involved in a case study project with some colleagues at Cisco where we’ve been researching what the most relevant software skills are that Cisco’s pre-sales engineers could benefit from. We’re all freaking experts at Outlook of course (that’s a joke  ) but we were interested in the areas of programming, automation, orchestration, databases, analytics, and so on. The end goal of the project was to identify what those relevant skills are, have a plan to identify the current skillset in the field, do that gap analysis and then put forward recommendations on how to close the gap.
) but we were interested in the areas of programming, automation, orchestration, databases, analytics, and so on. The end goal of the project was to identify what those relevant skills are, have a plan to identify the current skillset in the field, do that gap analysis and then put forward recommendations on how to close the gap.
This probably sounds really boring and dry, and I don’t blame you for thinking that, but I actually chose this case study topic from a list of 8 or so. My motivation was largely selfish: I wanted to see first-hand the outcome of this project because I wanted to know how best to align my own training, study, and career in the software arena. I already believed that to stay relevant as my career moves along that software skills would be essential. It was just a question of what type of skills and in which specific areas.
EIGRP: A Multi-Vendor Demo
In this video, David Bombal runs the open version of Cisco's EIGRP protocol between a Linux-based router and Cisco devices.
Happy Eyeballs v2 (and how I Was Wrong Again)
In Moving Complexity to Application Layer I discussed the idea of trying to use all addresses returned in a DNS response when trying to establish a connection with a server, concluding with “I don’t think anyone big enough to influence browser vendors is interested in reinventing this particular wheel.”
I’m really glad to report I was wrong ;) This is what RFC 8305 (Happy Eyeballs v2) says:
Read more ...On Why I’m Shifting my Career Focus to Software
For the past few months I've been involved in a case study project with some colleagues at Cisco where we've been researching what the most relevant software skills are that Cisco's pre-sales engineers could benefit from. We're all freaking experts at Outlook of course (that's a joke ?) but we were interested in the areas of programming, automation, orchestration, databases, analytics, and so on. The end goal of the project was to identify what those relevant skills are, have a plan to identify the current skillset in the field, do that gap analysis and then put forward recommendations on how to close the gap.
This probably sounds really boring and dry, and I don't blame you for thinking that, but I actually chose this case study topic from a list of 8 or so. My motivation was largely selfish: I wanted to see first-hand the outcome of this project because I wanted to know how best to align my own training, study, and career in the software arena. I already believed that to stay relevant as my career moves along that software skills would be essential. It was just a question of what type of skills and in which specific Continue reading
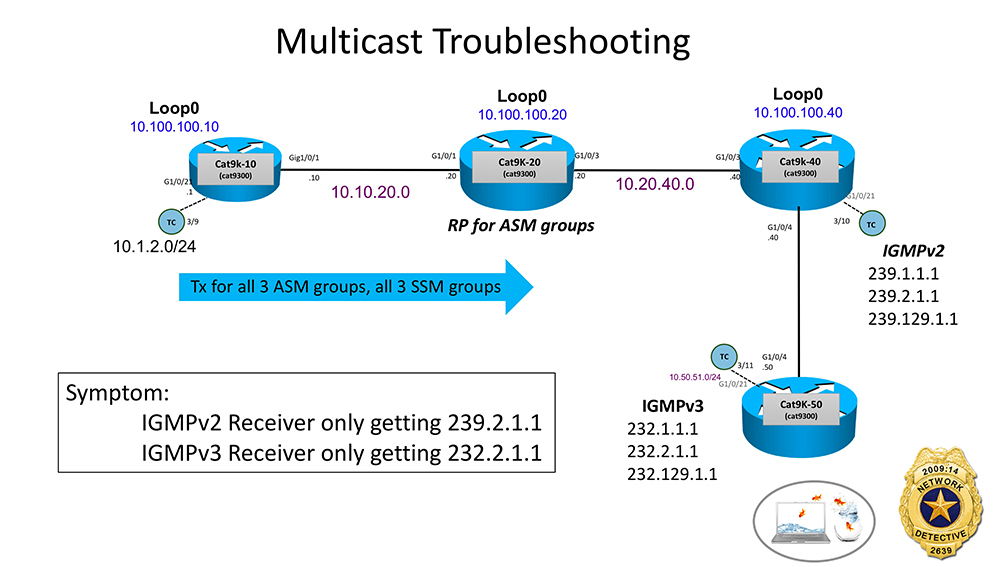
Network Detective Ride-Along: Troubleshooting Multicast
Grab your Network Detective badge! It’s time for another Network Detective ride-along.  Multicast this time.
Multicast this time.
We need to solve the case of the missing Multicast streams. ONLY 2 multicast streams (232.2.1.1 and 239.2.1.1) are getting thru to the hosts who requested them. The other 4 streams the same hosts requested are NOT getting thru. Let’s go to the crime scene and review the facts.
Fact #1 – Host off of Cat9K-40 is sending IGMPv2 membership reports to join ASM groups 239.1.1.1, 239.2.1.1 and 239.129.1.1
Fact #2 – Host off of Cat9K-50 is sending IGMPv3 membership reports to join SSM groups 232.1.1.1, 232.2.1.1 and 232.129.1.1
Fact #3 – All multicast sources are off of Cat9k-10 in subnet 10.1.2.0/24. They are sending the mcast for all 3 SSM groups and all 3 ASM groups
Fact #4 – Cat9K-20 is the Rendezvous Point (RP) for all 3 ASM groups
Any thoughts at first glance? Time to go to the YouTube ride-along ~11 minute video! Good luck! Have fun!
Raspberry Pi and AWS IOT – First steps
Hi All,
I have slightly changed this to networking, but the intention and my current use is to measure the water level of a sump, since that deviates from the network blog writing, i have extended the same to a Router.
Purpose – Have a Router and also a Syslog Server which monitors my internal network (This can easily be extended to a Car / Moisture Sensor or a Temperature/Humidity Sensor), what we want to do is to make sure if any anomaly is seen in Log Messages, it logs to IOT service. We can then take this up as a Part-2 writing to perform a specific action / automated on what action can be taken to mitigate
Discussion about configuring a Linux device is out of scope, so lets think that we all have that setup. What happens next ?
Lets quickly see our python script, which parses for a anomaly, in this lets say when someone runs a ping command, well its not a anomaly but will do for our use-case.
logparse.py is our program, so i have imported it into the readily available sample program provided by AWSIOT Kit, so you dont have to know Continue reading
Fun: Playing Battleships over BGP
BGP is the kitchen-sink of networking protocols, right? Whatever control-plane information you need to transport around, you can do it with BGP… including the battleship coordinates carried in BGP communities.
On the more serious front, it's nice to see at least some ISPs still care enough about the stability of the global Internet to use BGP route flap dampening.
Recover a RAID5 Array on Linux with healthy disks
Intel Atom failures I know the title sounds a bit weird and you may ask why would you need to recover a RAID5 array when all your disks are healthy, right? To understand what is going on, my DS1515+ has an Intel Atom C2538. (source: Synology CPU / NAS Type). It recently caused a lot of issues in the IT industry. (remember the Cisco clock issue? ? ) The Errata AVR54 of the C2000 Specifications update clearly states the following: “system may experience inability to boot or may cease operation”. My NAS was starting to have regular reboots and it completely crashed before I could back up the last delta of data. In the first instance, Synology denied any abnormal failure rate on this specific [Read More...]
The post Recover a RAID5 Array on Linux with healthy disks appeared first on VPackets.net.
NetDevOpEd: Disaggregation is key to software vulnerability management
One critical decision that executives need to make when assessing their data center architecture is their approach to software vulnerability management across all network components. Vulnerability management primarily revolves around selecting an efficient and modern software management strategy. There are several ways to execute on a software management strategy, and I believe disaggregation is a critical first step in doing it right.
In this post, I want to take a minute to first share my thoughts on the vulnerability management trends I’ve noticed. I will argue that a) you need to prioritize the network in how you manage vulnerabilities and b) disaggregation is the only way to do it properly. We’ll also take a look at the reasons why I think we never had the right framework to manage software delivery, making vulnerability management a challenge on platforms that are closed in nature.
Operations at the core of vulnerability management
Three weeks ago, I joined 40,000 security professionals in San Francisco to attend the biggest gathering of security conscious professionals — RSA Conference. While there were several presentations and moments from the event that stood out, one that caught my eye was a presentation that discussed challenges in the industry Continue reading