Network Break 171: Cisco Issues Critical Patches; Vendors Launch New Products
Today's Network Break dives into Cisco security patches and discusses new products from Talari, ExtraHop & Apstra, plus more tech news. The post Network Break 171: Cisco Issues Critical Patches; Vendors Launch New Products appeared first on Packet Pushers.Why hiring the ‘best’ people produces the least creative results — Quartz
 The complexity of modern problems often precludes any one person from fully understanding them. Factors contributing to rising obesity levels, for example, include transportation systems and infrastructure, media, convenience foods, changing social norms, human biology and psychological factors. Designing an aircraft carrier, to take another example, requires knowledge of nuclear engineering, naval architecture, metallurgy, hydrodynamics, […]
The complexity of modern problems often precludes any one person from fully understanding them. Factors contributing to rising obesity levels, for example, include transportation systems and infrastructure, media, convenience foods, changing social norms, human biology and psychological factors. Designing an aircraft carrier, to take another example, requires knowledge of nuclear engineering, naval architecture, metallurgy, hydrodynamics, […]Context-Aware Micro-segmentation – Remote Desktop Session Host Enhancements for VMware Horizon
In a previous post my colleague, Stijn, discussed the enhancements to how NSX for vSphere 6.4 handles Remote Desktop Session Host, RDSH, systems with the Identity-based Firewall and Context-Aware Micro-segmentation.
Remote Desktop Services is an underlying technology from Microsoft that many vendors take advantage of to provide overlay management and application deployment technologies for. In this post, we’re going to discuss how NSX for vSphere 6.4 allows customers to run RDS hosts with granular security for VMware Horizon systems.
VMware Horizon can provide multiple users the ability to connect to a single system to access their applications using the RDSH technology. These users can be of the same type, for example all HR users, or of multiple types, HR and Engineering users. In previous versions of NSX, it was not possible to individually secure user sessions and create Distributed Firewall (DFW) rule sets according to the user session logged into an RDSH server. This meant less flexibility in controlling what users could access data center application servers without isolating one set of users to one RDSH server. This model created a very rigid architecture for Horizon customers to follow.
Horizon allows customers Continue reading
6 Ways to Transform Legacy Data Storage Infrastructure
Learn how to maximize your existing data storage investments.
Automation Win: MPLS/VPN Service Deployment
I always encourage the students attending the Building Network Automation Solutions online course to create solutions for problems they’re facing in their networks instead of wasting time with vanilla hands-on assignments.
Francois Herbet took the advice literally and decided to create a solution that would configure PE-routers and create full-blown device configurations for CE-routers.
Read more ...The Blind Men and the Elephant
 Bufferbloat is responsible for much of the poor performance seen in the Internet today and causes latency (called “lag” by gamers), triggered even by your own routine web browsing and video playing.
Bufferbloat is responsible for much of the poor performance seen in the Internet today and causes latency (called “lag” by gamers), triggered even by your own routine web browsing and video playing.
But bufferbloat’s causes and solutions remind me of the old parable:
It was six men of Indostan, to learning much inclined,
who went to see the elephant (Though all of them were blind),
that each by observation, might satisfy his mind.
……. (six stanzas elided)
And so these men of Indostan, disputed loud and long,
each in his own opinion, exceeding stiff and strong,
Though each was partly in the right, and all were in the wrong!
So, oft in theologic wars, the disputants, I ween,
tread on in utter ignorance, of what each other mean,
and prate about the elephant, not one of them has seen!
John Godfrey Saxe
Most technologists are not truly wise: we are usually like the blind men of Indostan. The TCP experts, network operators, telecom operators, router makers, Internet service operators, router vendors and users have all had a grip *only* on their piece of the elephant.
The TCP experts look at TCP and think “if only TCP were Continue reading
NASA Social OA-4 Tours and Launch
In December 2015 I had the distinct honor to be selected to attend a NASA Social event that coincided with the OA-4 launch, an ISS resupply mission. NASA runs these events occasionally to give the world some insight into what goes on at various locations pertaining to the space industry. There’s a lot of really cool work going on, and I’m happy to finally have a chance to publish my experience on this amazing trip.Home network traffic analysis with a Raspberry Pi 3, a NetGear Switch and Ntop
I had the Raspberry Pi laying around for some time without doing any major function and so was a the NetGear switch [1]. So, I decided to do a weekend project to implement traffic analysis on my home network. I have a PPPoE connection to my ISP that connects to my home router [2]. The … Continue reading Home network traffic analysis with a Raspberry Pi 3, a NetGear Switch and NtopDipping my toes in the IoT pool: Microsoft DevKit IoT Board
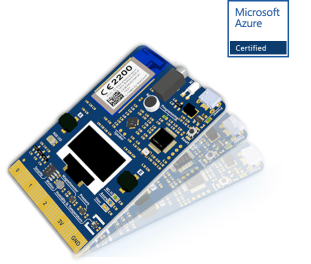
In my personal life, I’ve jumped in the SmartHome head first, but I’ve been really reluctant to blur the lines into my professional life. Recently, I saw something that changed all that. The Microsoft IoT DevKit board.
What is it?
This is Microsoft hardware product that allows developers to jump into the IoT pool. Specifically, the Microsoft Azure IoT hub pool. This is a very capable board with multiple sensors.
What sensors you ask?
- Humidity:
- Air Pressure
- Temperature
- Magnetometer
- Motion
- Microphone
Basically, it’s a really good sensor that can grab the majority of the physical measurements that we want to look at in the IoT world.
What do I do with it?
Right now, this is really just a tech toy for me. I have no specific projects that I’m trying to achieve. Rather this is a device that I’m using to try and really understand HOW the IoT ecosystem works and ensure my employability in years to come. So I don’t have any specific goals, but that’s really ok because Microsoft has been wonderful enough to supply us with the Microsoft IoT DevKit page over at Github which has a few different projects that allow me to grow Continue reading
Automation won’t cost you your job — it could save it
If you’re a regular reader of our blog, you probably do a lot of professional work with networking, manage an enterprise data center or play around with networks as a hobby (if you don’t, close your eyes for just a moment and imagine yourself in a well air-conditioned data center). You also likely know about the day-to-day tasks that maintaining a network requires, and how much time they take out of the day. Or, perhaps you’re a director that’s trying to resolve the issues your networking team keeps having. Has it ever occurred to you that there might be a better way to tackle these daily problems? Sure, what you’re doing now works, but there’s so much else you could be doing if the management of these tasks were optimized. That’s where network automation solutions can step in and give you more free time than you could have dreamed of. Why automation? Well, let’s get into what problems it eliminates and the benefits it brings — you can thank us later!
Problem: A manually configured and operated network
A day in the life of a network engineer includes three layers of regular tasks. At the top, we have troubleshooting operation Continue reading
Building a Sustainable Community Network in Sarantaporo Greece
For over a year now we in the Sarantaporo.gr Non Profit Organization have been in contact with Internet Society in meetings, over online interactions, and through in-person collaboration with people of the organization who visited our village last summer. From the beginning we saw that Internet Society is an organization which we share a lot of common elements with in terms of vision, and that its network is a natural space for our Community Network to be a part of.
In September 2017 we applied for the Internet Society Beyond the Net Funding Programme to approach the organization more closely and pursue funding to finance our Community Network. We are very happy to announce that our proposal was successful and will be funded with $30,000 USD through 2018 and 2019. This grant arrives very timely, in a period of transformation for our Community Network.
Continuously growing since 2010 to expand from Sarantaporo to even more villages in the region, today Sarantaporo.gr Community Network has reached a point where it is no longer possible to keep growing under the previous model, which was heavily dependent on the volunteering work of the nonprofit’s core team. Local inhabitants need to step in and Continue reading
Worth Reading: Networking Really Runs on Rainbows
From the fantastic Lines, Radios and Cables (a MUST READ if you’re even remotely interested in this thing called latency):
When we put different colours of light, or wavelengths, onto a single fibre, we call it Wave Division Multiplexing (WDM) which is a complicated way of saying a pretty rainbow […] International trading is powered by rainbows, literally.