Organizations Left Grappling for Solutions Amid Alarming Cloud Security Gaps
The convergence of a Zero Trust framework with enhanced collaboration between security and development teams is foundational to a robust cloud security posture.HW020: How We Got to Wi-Fi 7 and Where We Go From Here
To understand the newest standard, Wi-Fi 7, it helps to look back at Wi-Fi 5 and 6, and even forward to Wi-Fi 8. What’s the reasoning behind the updates? How have they been experienced at the ground level? Who should make the change and when? Host Keith Parsons and Wi-Fi expert Srikanth Subramanian touch on... Read more »BGP Labs: Use Multiple AS Numbers on the Same Router
Can you use BGP to connect to the global Internet without having a public BGP AS number? Of course, assuming your Internet Service Provider is willing to run BGP with a network using a private AS number. But what happens if you want to connect to two ISPs? It’s ridiculous to expect you’ll be able to persuade them to use the same private AS number.
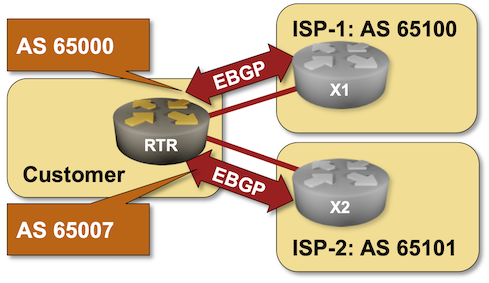
That’s one of the many use cases for the local-as functionality available in most BGP implementations. You can practice it in the Use Multiple AS Numbers on the Same Router lab exercise.
BGP Labs: Use Multiple AS Numbers on the Same Router
Can you use BGP to connect to the global Internet without having a public BGP AS number? Of course, assuming your Internet Service Provider is willing to run BGP with a network using a private AS number. But what happens if you want to connect to two ISPs? It’s ridiculous to expect you’ll be able to persuade them to use the same private AS number.
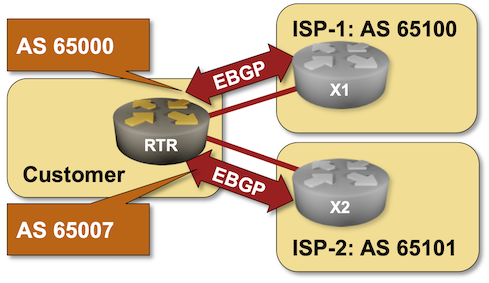
That’s one of the many use cases for the local-as functionality available in most BGP implementations. You can practice it in the Use Multiple AS Numbers on the Same Router lab exercise.
On Writing Complexity

I’ve been on a bit of a writer’s break after finishing the CCST book, but it’s time to rekindle my “thousand words a day” habit. As always, one part of this is thinking about how I write—is there anything I need to change? Tools, perhaps, or style?
What about the grade level complexity of my writing? I’ve never really paid attention to this, but I’m working on contributing to a site regularly that does. So maybe I should.
I tend to write to the tenth or eleventh-grade level, even when writing “popular material,” like blog posts. The recommended level is around the eighth-grade level. Is this something I need to change?
It seems the average person considers anything above the eighth-grade reading level “too hard” to read, so they give up. Every reading level calculation I’ve looked at essentially uses word and sentence length as proxies for complexity. Long words and sentences intimidate people.
On the other hand, measuring the reading grade level can seem futile. There are plenty of complex concepts described by one- and two-syllable words. Short sentences can still have lots of meaning.
Further, the reading grade level does not tell you if the sentence makes sense. Continue reading
Tech Bytes: Breaking Through The Noise With Wi-Fi 7 (Sponsored)
Wi-Fi 7 is the latest iteration of the wireless standard from the Wi-Fi Alliance. Wi-Fi 6 brought significant increases in throughput and performance. Wi-Fi 6e made the 6Ghz spectrum available (at least in the US). What does Wi-FI 7 bring to the table, and is it worth going through an upgrade? Our guest is Chris... Read more »IT Teams Are Not Prepared for 90-Day Digital Certifications
90-day digital certificates are a fast-approaching reality. While they will bring security benefits for businesses and help ensure digital trust across the web, they will also be a burden for unprepared IT managers.NB465: Dell Terminates VMware Resale Deal; Return-To-Office Orders Backfire Says Study
This week on Network Break we discuss Dell terminating its resale agreement of VMware as Broadcom looks to streamline OEM agreements, a new Wi-Fi AP and cloud-managed switches from Extreme, and the fits and starts in US chip manufacturing. A new study finds Return-To-Office (RTO) mandates don’t improve productivity or company performance, but do drive... Read more »5G RedCap Promises Nirvana for IoT Deployments Globally. But Can it Deliver?
Keeping IT’s attention as 5G Reduced Capacity (RedCap) services emerge will require rising above competitive solutions.HN719: Meet SuzieQ, The Network Observability Application
Guest Dinesh Dutt introduces his newest creation, SuzieQ. It’s a network observability platform application that has both a free, open source version and an enterprise version. Lightweight, fast, and platform-agnostic, SuzieQ’s use cases include network documentation, troubleshooting, fabric-wide visibility, network refresh and redesign, low/no code validation, audits and compliance, and proactive health checks. Hosts Ethan... Read more »Join Us For Packet Protector, A New Cybersecurity Podcast
Hi, I’m Jennifer Minella and I’m excited to finally share with you all that I’ll be co-hosting a new podcast on the Packet Pushers network. It’s called Pocket Protector, a podcast exploring the intersection of networking and security. Each week, we’re drilling into topics, from wired and wireless network security to access control and zero... Read more »5 Things You Can’t Automate In Your Data Center
Data center automation is a hot topic, but some key areas still require a human touch. Find out which data center operations are resistant to automation – for now.Segment Routing IPv6 (SRv6) with VyOS
In this post we take a look at configuring Segment Routing IPv6 (SRv6) using VyOS. For those unfamiliar, VyOS is an open-source routing platform built on top of Debian Linux and features a commit-based configuration system similar to Juniper’s JUNOS. It originated as a fork of Vyatta Core in late 2013 after Brocade stopped development. If you are new to VyOS, it is recommended to read the quick start guide before continuing.Hedge 211: Learning About Learning
How much have you thought about the way you learn–or how to effectively teach beginners? There is a surprising amount of research into how humans learn, and how best to create material to teach them. In this roundtable episode, Tom, Eyvonne, and Russ discuss a recent paper from the Communications of the ACM, 10 Things Software Developers Should Learn about Learning.
Evaluating the 2024 Cybersecurity Landscape
Looking ahead after emerging from 2023, 2024 is the year of the business understanding security and security starting to understand the business.Thanksgiving 2023 security incident
On Thanksgiving Day, November 23, 2023, Cloudflare detected a threat actor on our self-hosted Atlassian server. Our security team immediately began an investigation, cut off the threat actor’s access, and on Sunday, November 26, we brought in CrowdStrike’s Forensic team to perform their own independent analysis.
Yesterday, CrowdStrike completed its investigation, and we are publishing this blog post to talk about the details of this security incident.
We want to emphasize to our customers that no Cloudflare customer data or systems were impacted by this event. Because of our access controls, firewall rules, and use of hard security keys enforced using our own Zero Trust tools, the threat actor’s ability to move laterally was limited. No services were implicated, and no changes were made to our global network systems or configuration. This is the promise of a Zero Trust architecture: it’s like bulkheads in a ship where a compromise in one system is limited from compromising the whole organization.
From November 14 to 17, a threat actor did reconnaissance and then accessed our internal wiki (which uses Atlassian Confluence) and our bug database (Atlassian Jira). On November 20 and 21, we saw additional access indicating they may have come back Continue reading
KU047: Back to the Basics: Network Engineering for Platform Engineers
Network engineering is foundational to platform engineering. Michael and Kristina chat with Marino Wijay about tinkering with their home labs to brush up on networking skills and get hands-on practice. The three talk about how in a cloud-based world, it can be easy to forget about the networking nuts and bolts that connect workloads and... Read more »Appreciation of automated IX Quarantine LAN testing
Appreciation of automated IX Quarantine LAN testing
Something that bgp.tools (my company) does a great deal is joining internet exchanges.