DNS over TLS: experience from the Go6lab
After the experiment with DPRIVE at IETF99, we thought we’d try to implement it in the Go6lab and see how this actually works in day-to-day reality.
The first step was to take a look at https://dnsprivacy.org/wiki/ as we had a feeling this might be the best source for information around this topic. There’s a ton of info about DNS over TLS, but what we were really looking for was simple instructions on how to setup a recursive DNS server to serve DNS responses over TLS (port 853), as well as how to setup a local client on our device that could talk to the server and accept local DNS queries over TLS, thereby protecting our DNS communications over the Internet.
We decided that running a TLS proxy was not the way to do it, so we used CentOS 7 VPS with Unbound installed. After some time and with extensive help from Willem Toorop from NLnet Labs (thanks Willem!!!) we managed to navigate the setup process for server and client.
Firstly, we installed the default Unbound from the CentOS7 default yum repositories, which turned out not to be a very good idea, as this version is 1.4.20 Continue reading
Worth Reading: Malware in your screen
The post Worth Reading: Malware in your screen appeared first on rule 11 reader.
Cross Links in a Spine and Leaf
The post Cross Links in a Spine and Leaf appeared first on rule 11 reader.
Hey Alexa, Turn my lab on!
TL/DR Put together a custom Alexa Skill so I can turn switches and routers off in my lab as shown in the video here. Feels pretty great.
As most of my twitter followers have noticed, I’ve been doing a lot of Home Automation, mostly with Apple #homeKit. But I also picked up an Amazon Dot because… well why not?
One of the great things abut the digital voice assistance from Amazon, is that they have created an extensible framework that enables those with a little bit of coding skills to add to Mrs. A’s already already impressive impressive array of abilities.
The Amazon Alexa developer page is pretty impressive. There’s a ton of information and tutorials there, as well as an SDK and code examples in Node.js. I’m almost exclusively a python coder at this point, so I decided to look for something a little more familiar and came upon this.
Flask-Ask
Flask-Ask is a Flask extension that makes building Alexa skills for the Amazon Echo easier and much more fun.
Essentially, John Wheeler took the flask WSGI ( web) framework and made it super easy to be able to create Amazon Alexa skills using this familiar library. Continue reading
Worth Reading: It’s okay to forget what you read
The post Worth Reading: It’s okay to forget what you read appeared first on rule 11 reader.
SDxCentral’s Top 10 Articles — August 2017
 NetApp brags about its HCI; Top 10 security startups; VMware scores big with Vodafone.
NetApp brags about its HCI; Top 10 security startups; VMware scores big with Vodafone.
Upcoming Events and Webinars
You might have noticed the “upcoming webinars” blog widget is gone and I’ll write a blog post every two weeks or so to keep you updated on upcoming webinars and other events.
Here’s what’s coming in September and October 2017:
- Does Docker (and containers) make sense with Cumulus Networks on September 21st in Zurich;
- Docker workshop on September 21st in Zurich;
- DevOps and Security for Enterprise Environments on September 28th;
- Second part of Network Visibility with Flow Data webinar on October 5th;
- Network automation workshop in Rome on October 18th.
Istanbul/Turkey Onsite CCDE Training – 50% OFF until Sep-15, 2017
Istanbul/Turkey Onsite CCDE Training will be held between October 30 – November 4. Course will be in English as usual, everyday will be between 9am – 6pm, 9 hours. I am going to extend my CCDE Materials for this course as there was new scenarios and the technologies after August 29, 2017 CCDE […]
The post Istanbul/Turkey Onsite CCDE Training – 50% OFF until Sep-15, 2017 appeared first on Cisco Network Design and Architecture | CCDE Bootcamp | orhanergun.net.
Docker Networking Tip – Load balancing options in Docker
I had promised earlier that I will continue my Docker Networking Tip series. This is second in that series. The first one on Macvlan driver can be found here. In this presentation, I have covered different load balance options with Docker. Following topics are covered in this presentation: Overview of Service Discovery and Load balancing … Continue reading Docker Networking Tip – Load balancing options in DockerChange VM Hardware Version
The VM hardware version designates the virtual hardware functions supported by a virtual machine, which relates to the hardware on the host server. A VMware product will not be able to power on a VM with a hardware version higher than what it supports.
Deutsche Telekom, Huawei Launch 5G Test Network in Europe
 The network is getting 2 Gb/s speeds and less than 3 milliseconds of latency.
The network is getting 2 Gb/s speeds and less than 3 milliseconds of latency.
OCP Hardware Could Lay Foundation for Open Edge Computing
 SDxCentral just published new research on MEC.
SDxCentral just published new research on MEC.
The 2017 SDxCentral SD-WAN and vCPE Survey is Here!
 Take survey and enter to win one of two $300 Gift Cards redeemable at various retailers including Amazon, Target, Visa Virtual Card, etc.
Take survey and enter to win one of two $300 Gift Cards redeemable at various retailers including Amazon, Target, Visa Virtual Card, etc.
SIDH in Go for quantum-resistant TLS 1.3
The Quantum Threat
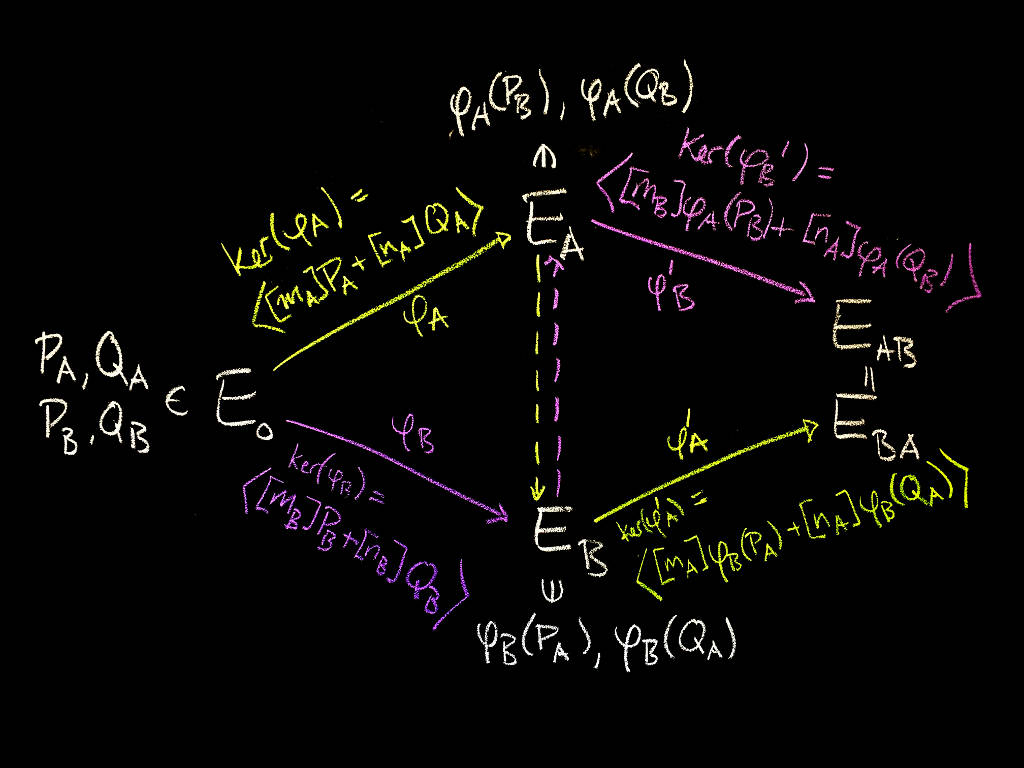
Most of today's cryptography is designed to be secure against an adversary with enormous amounts of computational power. This means estimating how much work certain computations (such as factoring a number, or finding a discrete logarithm) require, and choosing cryptographic parameters based on our best estimate of how much work would be required to break the system.
If it were possible to build a large-scale quantum computer, many of the problems whose difficulty we rely on for security would no longer be difficult to solve. While it remains unknown whether large-scale quantum computers are possible (see this article for a good overview), it's a sufficient risk that there's wide interest in developing quantum-resistant (or post-quantum) cryptography: cryptography that works on ordinary computers we have today, but which is secure against a possible quantum computer.
At Cloudflare, our biggest use of cryptography is TLS, which we use both for serving our customers' websites (all Cloudflare sites get free HTTPS), as well as for internal inter-datacenter communication on our backend.
In the TLS context, we want to create a secure connection between a client and a server. There are basically three cryptographic problems here:
Authenticity: the server Continue reading
New Study: Understanding MANRS’ Potential for Enterprises and Service Providers
Mutually Agreed Norms for Routing Security, or MANRS, was founded with the ambitious goal of improving the security and reliability of the global Internet routing system, based on collaboration among participants and shared responsibility for Internet infrastructure. These are undoubtedly essential pillars supporting the Internet’s tremendous growth and success, but we must better articulate the incentives of contributing to global security and resilience to grow MANRS participation and reach our goals.
To do so, we engaged 451 Research to understand the attitudes and perceptions of Internet service providers and the broader enterprise community around MANRS and how it relates to their organizations. The results of the study are documented in the report: https://www.routingmanifesto.org/resources/research/.
The study results demonstrate considerable unrealized potential for MANRS, showing that enterprises are interested in security and their interest should be a strong incentive for more service providers to participate. Market education could be particularly effective in overcoming the operational inertia that many providers face.
The key points from the study are:
- While MANRS itself is not well known by enterprises, its attributes are highly valued.
- Enterprises have high expectations for MANRS efforts.
- Enterprise perceptions of MANRS can translate into increased revenue for service Continue reading
Time Synchronization, Security, and Trust
Time is something that is often overlooked or taken for granted, but the accuracy and reliability of time is critical to our lives and must be protected. Time is a core concept underlying nearly all physical and virtual systems. Distributed computer systems, key to many functions inherent in our daily lives, rely on accurate and reliable time, yet we rarely stop and think about how that time is constructed and represented. Accurate and reliable time is needed to determine when an event occurs, in what order a particular sequence of events occurs, or when to schedule an event that is to occur at a particular time in the future. Finally, and of particular interest to our trust agenda here at the Internet Society, quality reliable time is required for many of the security technologies that help provide trust for the Internet. It is a vital and often overlooked part of the Internet infrastructure.
Some specific examples where accurate reliable secure time information is vital include:
- The finance sector where there are high demands on the time synchronization of business clocks in trading systems. This is especially true in the high frequency trading where a new EU legislation called Markets Continue reading
Worth Reading: Wave System’s DPU architecture
The post Worth Reading: Wave System’s DPU architecture appeared first on rule 11 reader.
Dictionary: Blame THeater
What is Blame Theater ?
The post Dictionary: Blame THeater appeared first on EtherealMind.
HPE Closes $8.8B Software Spinoff Deal with Micro Focus
 Micro Focus is now the seventh largest pure-play enterprise software company in the world.
Micro Focus is now the seventh largest pure-play enterprise software company in the world.
Microsoft Amps Container Support with Jenkins Plugin
 The company was unable to find required support from Jenkins to Kubernetes.
The company was unable to find required support from Jenkins to Kubernetes.