Forwarding BUM Frames in VXLAN Network With Multicast in Underlay
There are two main methods that can be used to forward broadcast, unknown unicast, and multicast (BUM) frames in a VXLAN network:
- Ingress replication.
- Multicast in underlay.
In this post, we take a detailed look at how multicast can be used to forward BUM frames by running multicast in the underlay. We are using the topology from my Building a VXLAN Lab Using Nexus9000v post. The Spine switches are configured using the Nexus feature Anycast RP. That is, no MSDP is used between the RPs. To be able to forward broadcast frames such as ARP in our topology, the following is required:
- The VTEPs must signal that they want to join the shared tree for 239.0.0.1 (to receive multicast) using a PIM Join.
- The VTEPs must signal that they intend to send multicast for 239.0.0.1 on the source tree using a PIM Register.
- The RPs must share information about the sources that they know of by forwarding PIM Register messages.
- The VTEP must encapsulate ARP packets in VXLAN and forward in the underlay using multicast.
The Leaf switches have the following configuration to enable multicast:
ip pim rp-address 192.0.2.255 group-list 224. Continue reading
Hedge 200: Automation with Ethan Banks
We’ve been on a long streak of discussions about automation, why it works, why it isn’t working, and what the networking industry can do about it. For this episode, we’re joined by the indubitable Ethan Banks. If you don’t think there’s anything left to say, you’ve not yet listened to Ethan!
Heavy Networking 707: Getting Real With Selector’s AIOps (Sponsored)
AI and machine learning are finally being applied to networking in meaningful ways. On today's sponsored show we talk with Selector about its AIOps platform, which ingests networking logs, flows, configurations, SNMP, and other telemetry to detect patterns, spot problems, and provide contextual insights to help network engineers do their jobs better. We speak with Selector about what it is, how it works, and concrete use cases.
The post Heavy Networking 707: Getting Real With Selector’s AIOps (Sponsored) appeared first on Packet Pushers.
HN707: Getting Real With Selector’s AIOps (Sponsored)
AI and machine learning are finally being applied to networking in meaningful ways. On today's sponsored show we talk with Selector about its AIOps platform, which ingests networking logs, flows, configurations, SNMP, and other telemetry to detect patterns, spot problems, and provide contextual insights to help network engineers do their jobs better. We speak with Selector about what it is, how it works, and concrete use cases.Early Data-Link Layer Addressing
After covering the theoretical part of network addressing (part 2, part 3), let’s go into some practical examples. I’ll start with data link layer and then move on to networking and higher layers.
The earliest data link implementations that were not point-to-point links were multi-drop links and I mentioned them in the networking challenges part of the webinar. Initially, we implemented multi-drop links with modems, but even today you can see multi-drop in satellite communications, Wi-Fi, or in cable modems.
Early Data-Link Layer Addressing
After covering the theoretical part of network addressing (part 2, part 3), let’s go into some practical examples. I’ll start with data link layer and then move on to networking and higher layers.
The earliest data link implementations that were not point-to-point links were multi-drop links and I mentioned them in the networking challenges part of the webinar. Initially, we implemented multi-drop links with modems, but even today you can see multi-drop in satellite communications, Wi-Fi, or in cable modems.
Top Questions for Wireless Operators Worldwide on Network Sunsettings
Plan to expand? Prepare for country-specific plans to sunset 2G and 3G nets for 5G to rise.Does Automation Require Reengineering?
During Networking Field Day 33 this week we had a great presentation from Graphiant around their solution. While the presentation was great you should definitely check out the videos linked above, Ali Shaikh said something in one of the sessions that resonated with me quite a bit:
Automation of an existing system doesn’t change the system.
Seems simple, right? It belies a major issue we’re seeing with automation. Making the existing stuff run faster doesn’t actually fix our issues. It just makes them less visible.
Rapid Rattletraps
Most systems don’t work according to plan. They’re an accumulation of years of work that doesn’t always fit well together. For instance, the classic XKCD comic:
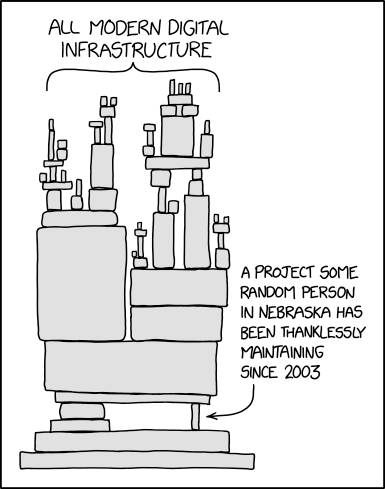
When it comes to automation, the idea is that we want to make things run faster and reduce the likelihood of error. What we don’t talk about is how each individual system has its own quirks and may not even be a good candidate for automation at any point. Automation is all about making things work without intervention. It’s also dependent on making sure the process you’re trying to automate is well-documented and repeatable in the first place.
How many times have you seen or heard of Continue reading
HS058 Are We Pausing the Technology Cycle
Today we debate its technoloyg is reaching a stable phase. Greg argues that we are in a period of stability, citing resistance to change and a slowdown in advancements. Johna believes that the rise of quantum computing and AI will lead to significant disruptions. They also discuss the future of AI and quantum computing, with Johna predicting a transformative impact by 2026, while Greg suggests a slower adoption due to existing heavy investments in technology.
The post HS058 Are We Pausing the Technology Cycle appeared first on Packet Pushers.
HS058: Are We Pausing The Technology Cycle?
Today we debate its technoloyg is reaching a stable phase. Greg argues that we are in a period of stability, citing resistance to change and a slowdown in advancements. Johna believes that the rise of quantum computing and AI will lead to significant disruptions. They also discuss the future of AI and quantum computing, with Johna predicting a transformative impact by 2026, while Greg suggests a slower adoption due to existing heavy investments in technology.Business-Optimized Networks Usher In A New Era For Networking Infrastructure
Networking success should be driven by great customer experience, not by a “bigger and faster” mindset.Introducing HAR Sanitizer: secure HAR sharing

On Wednesday, October 18th, 2023, Cloudflare’s Security Incident Response Team (SIRT) discovered an attack on our systems that originated from an authentication token stolen from one of Okta’s support systems. No Cloudflare customer information or systems were impacted by the incident, thanks to the real-time detection and rapid action of our Security Incident Response Team (SIRT) in tandem with our Zero Trust security posture and use of hardware keys. With that said, we’d rather not repeat the experience — and so we have built a new security tool that can help organizations render this type of attack obsolete for good.
The bad actor in the Okta breach compromised user sessions by capturing session tokens from administrators at Cloudflare and other impacted organizations. They did this by infiltrating Okta’s customer support system and stealing one of the most common mechanisms for troubleshooting — an HTTP Response Archive (HAR) file.
HAR files contain a record of a user’s browser session, a kind of step-by-step audit, that a user can share with someone like a help desk agent to diagnose an issue. However, the file can also contain sensitive information that can be used to launch an attack.
As a follow-up to the Continue reading
Email Routing subdomain support, new APIs and security protocols
It's been two years since we announced Email Routing, our solution to create custom email addresses for your domains and route incoming emails to your preferred mailbox. Since then, the team has worked hard to evolve the product and add more powerful features to meet our users' expectations. Examples include Route to Workers, which allows you to process your Emails programmatically using Workers scripts, Public APIs, Audit Logs, or DMARC Management.
We also made significant progress in supporting more email security extensions and protocols, protecting our customers from unwanted traffic, and keeping our IP space reputation for email egress impeccable to maximize our deliverability rates to whatever inbox upstream provider you chose.
Since leaving beta, Email Routing has grown into one of our most popular products; it’s used by more than one million different customer zones globally, and we forward around 20 million messages daily to every major email platform out there. Our product is mature, robust enough for general usage, and suitable for any production environment. And it keeps evolving: today, we announce three new features that will help make Email Routing more secure, flexible, and powerful than ever.
New security protocols
The SMTP email protocol Continue reading