Day Two Cloud 208: HashiCorp Licensing Changes And The Day Two Cloud-Chaos Lever Crossover
Today on Day Two Cloud we dive into the implications of licensing changes that HashiCorp has made to its popular Terraform software. In short, the company has switched from an open source to a business source license. HashiCorp says it felt compelled to make the change to ensure that some other business entity doesn't take the open-source software and turn it into a competing product (looking at you, AWS). Will the licensing change have a significant impact? For 99% of users probably not, but there are caveats and concerns to discuss. Today's show is a crossover with Chaos Lever, a weekly podcast co-hosted by Ned Bellavance and Chris Hayner that covers IT news.
The post Day Two Cloud 208: HashiCorp Licensing Changes And The Day Two Cloud-Chaos Lever Crossover appeared first on Packet Pushers.
Day Two Cloud 208: HashiCorp Licensing Changes And The Day Two Cloud-Chaos Lever Crossover
Today on Day Two Cloud we dive into the implications of licensing changes that HashiCorp has made to its popular Terraform software. In short, the company has switched from an open source to a business source license. HashiCorp says it felt compelled to make the change to ensure that some other business entity doesn't take the open-source software and turn it into a competing product (looking at you, AWS). Will the licensing change have a significant impact? For 99% of users probably not, but there are caveats and concerns to discuss. Today's show is a crossover with Chaos Lever, a weekly podcast co-hosted by Ned Bellavance and Chris Hayner that covers IT news.ARP and Static Routes
A few days ago, I described how ARP behaves when the source- and destination IP addresses are not on the same subnet (TL&DR: it doesn’t care). Now, let’s see how routers use ARP to get the destination MAC address for various entries in the IP routing table. To keep things simple, we’ll use static routes to insert entries in the IP routing table.
We’ll run our tests in a small virtual lab with two Linux hosts and an Arista vEOS switch. The link between H1 and RTR is a regular subnet. H2 has an IP address on the Ethernet interface, but RTR uses an unnumbered interface.
ARP and Static Routes
A few days ago, I described how ARP behaves when the source- and destination IP addresses are not on the same subnet (TL&DR: it doesn’t care). Now, let’s see how routers use ARP to get the destination MAC address for various entries in the IP routing table. To keep things simple, we’ll use static routes to insert entries in the IP routing table.
We’ll run our tests in a small virtual lab with two Linux hosts and an Arista vEOS switch. The link between H1 and RTR is a regular subnet. H2 has an IP address on the Ethernet interface, but RTR uses an unnumbered interface.
The Top 10 Benefits of SD-WAN: Advantages of SD-WAN Explained
SD-WAN gives enterprises a wide array of services to build and enhance their networks to meet today’s ever-changing business needs.HS054 Matching IT and Corporate Culture
Are you interested in learning more about aligning technology choices with organizational goals? Our podcast has got you covered! Listen now to explore the importance of technology alignment with business objectives.
The post HS054 Matching IT and Corporate Culture appeared first on Packet Pushers.
HS054: Matching IT and Corporate Culture
Are you interested in learning more about aligning technology choices with organizational goals? Our podcast has got you covered! Listen now to explore the importance of technology alignment with business objectives.Campus Switch Sales Forecast: 2023 Looks Strong; 2024 Maybe Not
Backlog orders and more expensive equipment are expected to drive up campus switch sales in 2023, but a correction may loom on the horizon.
The post Campus Switch Sales Forecast: 2023 Looks Strong; 2024 Maybe Not appeared first on Packet Pushers.
Private 5G: Not As Scary As You Think
When one thinks of 5G, it’s easy to associate the technology with complex carrier deployments, but enterprise-focused companies, like VMware, have designed products for corporate environments.Cloudflare’s tenant platform in action: Meter deploys DNS filtering at scale
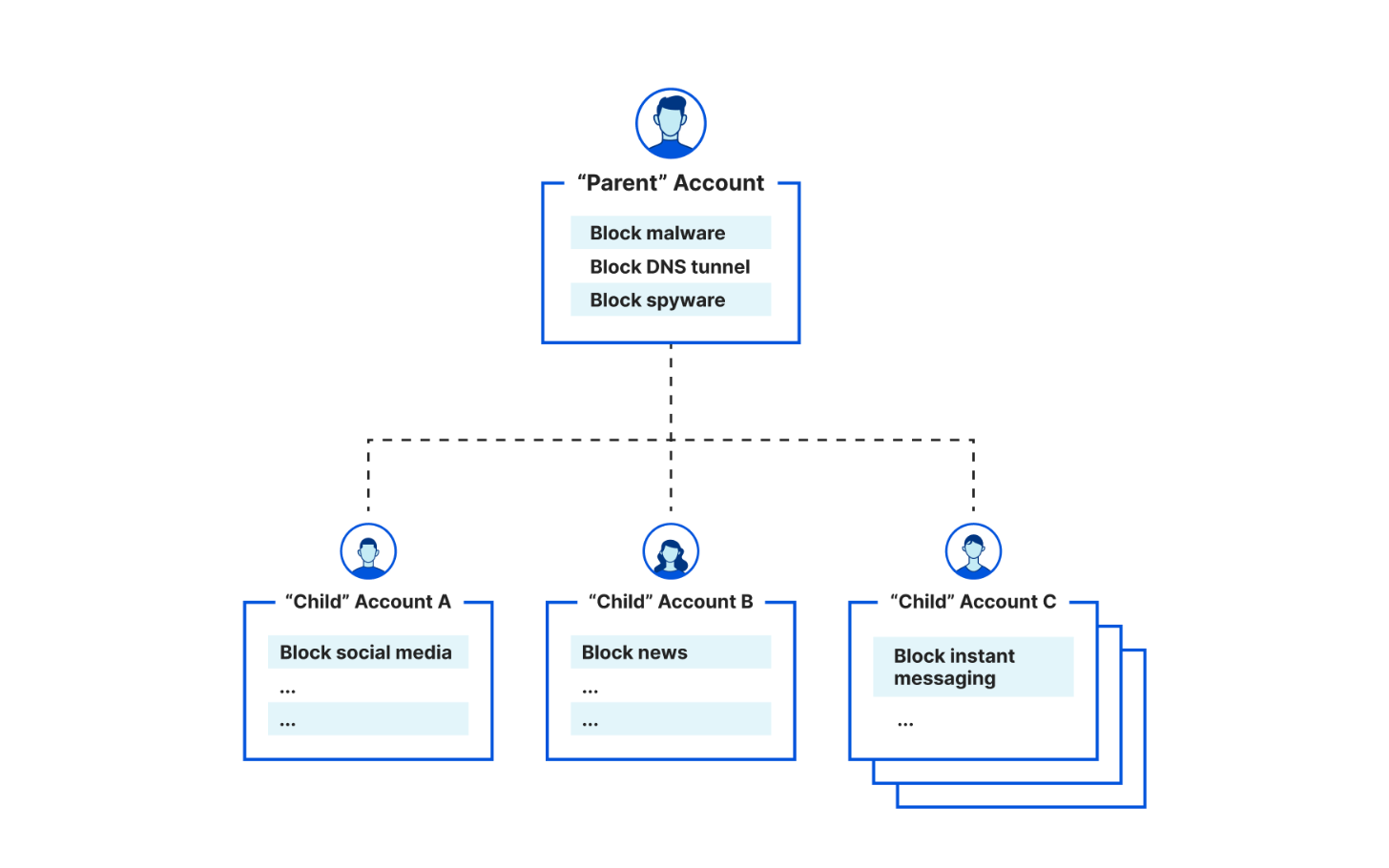
In January 2023, we announced support for Managed Service Providers (MSPs) and other businesses to create 'parent-child' and account-level policy configurations when deploying Cloudflare for DNS filtering. Specifically, organizations leverage the integration between our Tenant API and Cloudflare Gateway, our Secure Web Gateway (SWG) to protect their remote or office end users with web filtering and inspection. Already, customers like the US federal government, MalwareBytes, and a large global ISP take advantage of this integration to enable simpler, more flexible policy management across larger deployments across their end customers
Today, we're excited to showcase another similar story: Meter, a provider of Internet infrastructure, is leveraging the Tenant API integration for DNS filtering to help their clients enforce acceptable Internet use policies.
How Meter deploys Cloudflare to secure Internet browsing
Meter, headquartered in San Francisco and founded in 2015, provides Internet infrastructure that includes routing, switching, wireless, and applications. They help deliver faster, more efficient, more secure networking experiences for a diverse range of corporate spaces, including offices, warehouses, retail, manufacturing, biotech, and education institutions.
Meter integrates with the Cloudflare Tenant API to provide DNS filtering to their customers. With the Meter dashboard, Meter customers can set policies to Continue reading