Don’t miss a day full of SDN, security, microsegmentation and hands-on NSX
Gabi Gerber (with a bit of help from my side) is organizing another set of SDN events in Zurich (Switzerland) in early June.
In the morning of June 7th we’ll talk about software-defined security:
Read more ...Enable nested virtualization on supported hardware. (Fixing WARNING KVM acceleration not available, using ‘qemu’ issue)
 |
| Source: http://samadhisoft.com/wp-content/uploads/2009/05/nested-boxes.jpg |
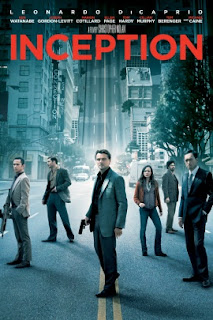 |
| © Warner Bros |
Wholesale Voice Carriers Examine NFV
 This wholesale work tends to be forgotten.
This wholesale work tends to be forgotten.
Label Switched Multicast — Q&A
This post is the last one I'm planning in this series on Label Switched Multicast (LSM). The questions & answers below are meant to expand on topics from the previous posts or address topics that weren't mentioned in the previous posts at all.
If you're not familiar with LSM yet then this Q&A likely won't make much sense to you and I recommend you go back and read through the previous posts.
Please post a comment if one of the answers isn't clear or you have additional questions!
Survey: Should The Packet Pushers Host A Conference?
Deep inside the virtual ideas lab at Packet Pushers, we’ve been debating the merits of organizing a two-day Packet Pushers conference. We love live events because there’s no better way to strengthen a community and share ideas. And because at a live event there’s no fast-forward button–we can lock the conference doors so that you […]
The post Survey: Should The Packet Pushers Host A Conference? appeared first on Packet Pushers.
Survey: Should The Packet Pushers Host A Conference?
Deep inside the virtual ideas lab at Packet Pushers, we’ve been debating the merits of organizing a two-day Packet Pushers conference. We love live events because there’s no better way to strengthen a community and share ideas. And because at a live event there’s no fast-forward button–we can lock the conference doors so that you […]
The post Survey: Should The Packet Pushers Host A Conference? appeared first on Packet Pushers.
ONUG Hopes to Nudge Networks Toward Real Interoperability
 ONUG plans to give standards bodies a push.
ONUG plans to give standards bodies a push.