Hedge 175: Mike B on Personal Superpowers
When the economy starts contracting, career advisors start talking about the importance of “soft skills.” What are “soft skills,” exactly—and why are they “soft?” Mike Bushong joins Tom Amman and Russ White to talk about why these skills are important, why they are not “soft,” and how we should talk about people skills instead. They are superpowers,” and there isn’t anything “soft” about them.
Leveraging security policy recommender to tighten your cluster’s security posture
We’ve noticed that many of our customers are currently undergoing a significant transformation in their application architecture, transitioning from legacy vertical applications to distributed microservices running on Kubernetes. This shift brings along a range of benefits, such as improved scalability, resilience, and agility. However, it also creates a larger attack surface that needs to be managed effectively.
To minimize the attack surface, it is crucial to have a clear understanding of how each microservice communicates microservices within, and outside, the cluster to implement robust network configuration and security policies. This can be challenging, especially when dealing with re-architected applications that can consist of hundreds of microservices.
To make the life of the security and DevOps teams easier, there are a few things that can be done. Firstly, providing them with access to detailed information on how microservices communicate within and outside the cluster. Secondly, having automated policy recommendations to improve their configuration and security. Finally, providing visibility and audit reports to help identify vulnerabilities in the system and prevent potential breaches.
In this blog, we will discuss how to leverage the security policy recommender to rapidly create security policies to minimize the attack surface and improve the security posture.
Gathering Continue reading
San Francisco Giants Deploy Fully Wi-Fi 6E-Ready Network With Comcast, Extreme Networks
Baseball team’s CIO Bill Schlough tells Network Computing that, with a network bandwidth of up to 100GB, the San Francisco Giants plan to improve the fan experience with augmented reality, easier streaming, and fast mobile ticket entry at Oracle Park.Taking a Slice Out of Private Wireless Networks
Network slicing and microslicing are two new approaches to ensuring QoS over enterprise private cellular networks, but they come with some distinct differences.ChatGPT Privacy: Understanding the Compliance Risks
Learn about the privacy risks associated with ChatGPT and how to ensure compliance with data protection regulations and avoid unethical biases when using it.Secure by default: recommendations from the CISA’s newest guide, and how Cloudflare follows these principles to keep you secure


When you buy a new house, you shouldn’t have to worry that everyone in the city can unlock your front door with a universal key before you change the lock. You also shouldn’t have to walk around the house with a screwdriver and tighten the window locks and back door so that intruders can’t pry them open. And you really shouldn’t have to take your alarm system offline every few months to apply critical software updates that the alarm vendor could have fixed with better software practices before they installed it.
Similarly, you shouldn’t have to worry that when you buy a network discovery tool it can be accessed by any attacker until you change the password, or that your expensive hardware-based firewalls can be recruited to launch DDoS attacks or run arbitrary code without the need to authenticate.
This “default secure” posture is the focus of a recently published guide jointly authored by the Cybersecurity and Infrastructure Agency (CISA), NSA, FBI, and six other international agencies representing the United Kingdom, Australia, Canada, Germany, Netherlands, and New Zealand. In the guide, the authors implore technology vendors to follow Secure-by-Design and Secure-by-Default principles, shifting the burden of security as much Continue reading
Oxy: Fish/Bumblebee/Splicer subsystems to improve reliability


At Cloudflare, we are building proxy applications on top of Oxy that must be able to handle a huge amount of traffic. Besides high performance requirements, the applications must also be resilient against crashes or reloads. As the framework evolves, the complexity also increases. While migrating WARP to support soft-unicast (Cloudflare servers don't own IPs anymore), we needed to add different functionalities to our proxy framework. Those additions increased not only the code size but also resource usage and states required to be preserved between process upgrades.
To address those issues, we opted to split a big proxy process into smaller, specialized services. Following the Unix philosophy, each service should have a single responsibility, and it must do it well. In this blog post, we will talk about how our proxy interacts with three different services - Splicer (which pipes data between sockets), Bumblebee (which upgrades an IP flow to a TCP socket), and Fish (which handles layer 3 egress using soft-unicast IPs). Those three services help us to improve system reliability and efficiency as we migrated WARP to support soft-unicast.
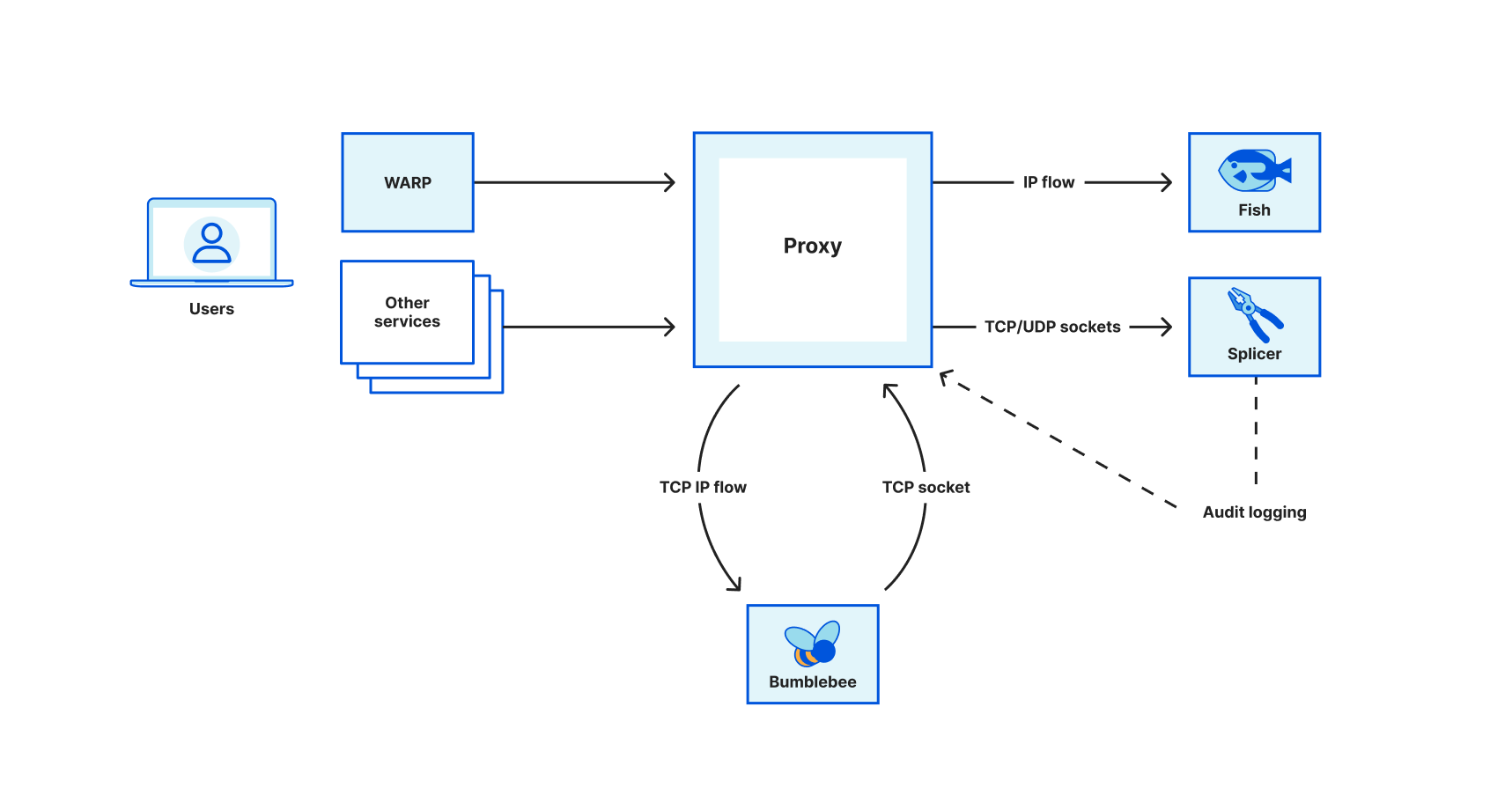
Splicer
Most transmission tunnels in our proxy forward packets without making any modifications. In other words, given Continue reading
Multi-Vendor EVPN Fabrics
Daniel left an interesting comment on my Studying EVPN to Prepare for a Job Interview blog post:
I also never build a VXLAN fabric with two vendors. So, is it possible now to build one large fabric consisting of multiple vendors?
TL&DR: Yes, but just because you could doesn’t mean that you should.
Multi-Vendor EVPN Fabrics
Daniel left an interesting comment on my Studying EVPN to Prepare for a Job Interview blog post:
I also never build a VXLAN fabric with two vendors. So, is it possible now to build one large fabric consisting of multiple vendors?
TL&DR: Yes, but just because you could doesn’t mean that you should.
Things Change. Some New content.
Once again it has been awhile. But I wanted to get some new content out. This year I was elected as a member of the board for WAA. Part of my time on the board will include writing articles for our membership. From the second I heard this I knew what I wanted to do. …Day Two Cloud 191: Modernizing Cloud Security And Optimizing Costs With Jo Peterson
Today's Day Two Cloud delves into cloud security and cloud cost optimization for SaaS and public clouds. Our guest is Jo Peterson. On the security front, we compare and contrast traditional on-prem and cloud security challenges, explore the shared responsibility model of cloud security, and more. For cost optimization we discuss the growing concern about cloud costs, why optimization tools still need humans, tips for tracking multicloud spending, and more.
The post Day Two Cloud 191: Modernizing Cloud Security And Optimizing Costs With Jo Peterson appeared first on Packet Pushers.
Day Two Cloud 191: Modernizing Cloud Security And Optimizing Costs With Jo Peterson
Today's Day Two Cloud delves into cloud security and cloud cost optimization for SaaS and public clouds. Our guest is Jo Peterson. On the security front, we compare and contrast traditional on-prem and cloud security challenges, explore the shared responsibility model of cloud security, and more. For cost optimization we discuss the growing concern about cloud costs, why optimization tools still need humans, tips for tracking multicloud spending, and more.New Zayo Submarine Cable Adds Faster, Redundant US–UK Route
Amid growing threats from bad actors, geopolitics, and climate change, Zayo Group announces a new submarine cable route between New York and Manchester.Where’s the Fish?
“Life is Good” has this great shirt I have a few of – “WTF: Where’s the Fish?” It is actually a question I get asked a lot. Where did I go? Where are my blogs? Where are my YouTubes? Where... Read More ›
The post Where’s the Fish? appeared first on Networking with FISH.
DDR4 memory organization and how it affects memory bandwidth
When shopping for DDR4 memory modules, we typically look at the memory density and memory speed. For example a 32GB DDR4-2666 memory module has 32GB of memory density, and the data rate transfer speed is 2666 mega transfers per second (MT/s).
If we take a closer look at the selection of DDR4 memories, we will then notice that there are several other parameters to choose from. One of them is rank x organization, for example 1Rx8, 2Rx4, 2Rx8 and so on. What are these and does memory module rank and organization have an effect on DDR4 module performance?
In this blog, we will study the concepts of memory rank and organization, and how memory rank and organization affect the memory bandwidth performance by reviewing some benchmarking test results.
Memory rank
Memory rank is a term that is used to describe how many sets of DRAM chips, or devices, exist on a memory module. A set of DDR4 DRAM chips is always 64-bit wide, or 72-bit wide if ECC is supported. Within a memory rank, all chips share the address, command and control signals.
The concept of memory rank is very similar to memory bank. Memory rank is a term used Continue reading