Storage Spending On The Rise
451 Research finds that companies plan to spend more on public cloud storage as they prioritize disaster recovery and backup.
Configure the Brocade NOS REST API to use HTTPS
Brocade VDX switches have REST and NETCONF interfaces. The REST API uses the built-in HTTP server. By default, this uses plain-text HTTP. As of NOS 6.0, you can (and should!) use HTTPS. If NOS has a certificate configured, it will automatically use HTTPS. Here’s how to configure it.
Pre-Change Tests
Let’s just do a couple of quick checks before we begin. Check that the switch is only listening on port 80, and that it responds to simple API queries:
Lindsays-MacBook:~ lhill$ nmap -p80,443 10.254.4.125 Starting Nmap 7.00 ( https://nmap.org ) at 2016-02-05 18:56 NZDT Nmap scan report for 10.254.4.125 Host is up (0.14s latency). PORT STATE SERVICE 80/tcp open http 443/tcp closed https Nmap done: 1 IP address (1 host up) scanned in 0.52 seconds Lindsays-MacBook:~ lhill$ curl -u admin:password -d "<activate-status></activate-status>" http://10.254.4.125/rest/operational-state/activate-status <output xmlns='urn:brocade.com:mgmt:brocade-firmware'> <overall-status>0</overall-status> <activate-entries> <rbridge-id>1</rbridge-id> <status>0</status> </activate-entries> </output> Lindsays-MacBook:~ lhill$ ssh [email protected] [email protected]'s password: Welcome to the Brocade Network Operating System Software admin connected from 10.252.131.4 using ssh on Leaf-203025 Leaf-203025# show http server status rbridge-id 1: Status: HTTP Enabled and HTTPS Continue reading
Introduction to BGP-LS and PCEP
Julian Lucek did a fantastic job describing how NorthStar controller uses BGP-LS and PCEP, so I asked him whether he’d be willing to do a deep dive on these two topics. He gracefully agreed, and the results are already online.
Read more ...CoreOS Aims rkt 1.0 at Improving Container Security
 It's about security, not about challenging Docker, CoreOS says.
It's about security, not about challenging Docker, CoreOS says.
BT Taps Its Own Cisco Routers for SD-WAN
 BT will manage the SD-WAN services.
BT will manage the SD-WAN services.
Docker 1.10: New Compose file, improved security, networking and much more!
We’re pleased to announce Docker 1.10, jam-packed with stuff you’ve been asking for. It’s now much easier to define and run complex distributed apps with Docker Compose. The power that Compose brought to orchestrating containers is now available for setting … ContinuedDocker 1.10: New Compose file, improved security, networking and much more!
We’re pleased to announce Docker 1.10, jam-packed with stuff you’ve been asking for. It’s now much easier to define and run complex distributed apps with Docker Compose. The power that Compose brought to orchestrating containers is now available for setting … ContinuedCollege students need food, sleep… and Wi-Fi. [VIDEO]
How important is Wi-Fi to education? When it comes to earning a college degree, reliable Wi-Fi is essential. Students want to be connected anywhere, any time in classrooms, dorm rooms, student centers, stadiums, or just walking across the quad. Reliable...SDN? I Still Don’t kNow what it is…

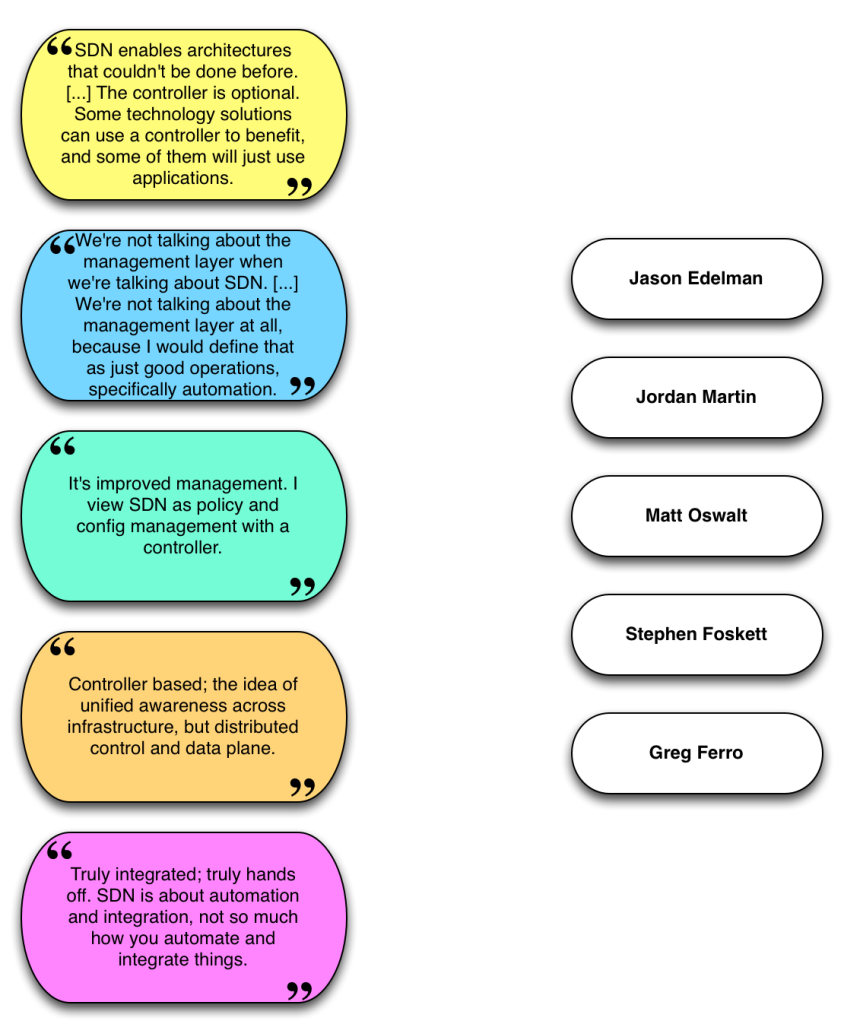
Today you get to play the SDN Definition Game: match the definition of Software Defined Neworking with the person who said it at the Networking Field Day 11 Delegate Roundtable. I’d make this exercise “drag and drop” but that sounds a bit complicated, so instead you’re on your honor not to cheat. Click on the image to see the answers in a new window.
SDN, Whatever That Is
I should note that the quotes I used were taken from conversation, so if I mis-transcribed anything or used it too far out of context I apologize to the speaker concerned. In actual fact though, who said what in this case doesn’t really matter. I shared the quotes to demonstrate that even when defined by a group of smart people like these, there doesn’t seem to be one definition of SDN that everybody can agree on. That has opened the door for marketing departments everywhere to use the SDN tag on anything and everything (aka “SDN Washing”) in the hopes that it sounds impressive and thus presumably increases sales. As a result, many people – both vendors and customers – believe that SDN is becoming a four letter word.
Buy the Solution, Continue reading
Six Practices Of A Great Manager
These six essential practices can help you become a better manager.
The post Six Practices Of A Great Manager appeared first on Packet Pushers.
Six Practices Of A Great Manager
These six essential practices can help you become a better manager.
The post Six Practices Of A Great Manager appeared first on Packet Pushers.
Machine to Machine Networking & IOT
The future of networking, and IT Infrastructure more generally, will be driven by machine to machine interactions.
The post Machine to Machine Networking & IOT appeared first on EtherealMind.
For Those Who Think Differently
A week ago Plexxi’s founder and CTO, Dave Husak presented at the Boston area networking Meetup called BOSNOG. This week Plexxi celebrates our five-year founding anniversary. I was at the Meetup with the Plexxi team and during the Q&A segment a question was asked that provoked some reflection on my part. The question was “what has been the biggest barrier to adoption for Plexxi?” A simple question, but the answer is not so simple.
The biggest barrier to Plexxi has been the ingrained acceptance of networking complexity and singular design to all networking requirements. Over the past five years, many companies brought to market solutions that added to this complexity with little if any underlying changes to the traditional network architecture. The past five years in networking has been witness to a multitude of technical attempts to change networking through the façade of automation, but none have tried to make it simpler and better. During these five years entire product lines from our competitors have achieved full cradle to end-of-life cycle in an attempt to “…harness the intelligent network through programmability and abstraction across multiple layers, offering a choice of protocols, industry standards, and usage-based deployment models” with the goal to Continue reading