Tech Notes: Difference Between OS1 and OS2 Fibre Optic Cable
These are two standards for single mode fibre optic cabling from a total of five types of fibre that are generically used today known of “OF types” (OM1, OM2, OM3 for multimode and OS1,OS2 for single mode.) OS1 is for indoor use i.e. Campus, Data Centre. Cabling is is tight buffered (i.e. manufactured into solid […]
The post Tech Notes: Difference Between OS1 and OS2 Fibre Optic Cable appeared first on EtherealMind.
5 ways to tell a cloud poser from a cloud pro
Who would you trust more to fix your car, a licensed mechanic or a guy who once saw someone do an oil change? The choice should be simple. But surprisingly, the debate over trusting an expert versus someone who claims to be an expert happens every day across all industries, so it shouldn’t be shocking that the debate rages in the cloud, too.
Cloud computing enables people and companies to access applications from any computer. But the cloud has created a new group of cloud posers -- inexperienced software developers who make bold (and often untrue) claims about the performance of the cloud-based applications they manage. While on the surface they may seem like a good choice to support your business, once you start asking smart questions, a cloud poser’s true colors (and lack of expertise) will quickly be revealed.
To read this article in full or to leave a comment, please click here
What to consider when negotiating a hybrid cloud SLA
Service Level Agreements (SLA) serve as a roadmap and a warranty for cloud services offerings. All cloud providers offer standard, one-size-fits-all SLAs that cover availably, performance, security, disaster recovery, response times, compliance and termination. This may be adequate for pure cloud applications, however standard SLAs fall short when it comes to hybrid cloud deployments.
There is nothing standard about hybrid deployments. Each one is different and inherently includes a higher level of involvement from IT. SLAs need to establish clear guidelines of engagement for both the enterprise and service provider. Unfortunately, not all cloud service providers are open or equipped to customize SLAs.
To read this article in full or to leave a comment, please click here
Transactional Thoughts on a Stormy Night
It was a dark stormy autumn night and three networking engineers had nothing better to do than ponder the heavy topics of transactional consistency in a distributed SDN environment in Episode 16 of Software Gone Wild podcast.
Here are a few of the topics that crossed our minds:
Read more ...Cisco Champion.
Woke up to a very nice email today.
I have been selected as a Cisco Champion for 2015! – Now i get to see what all the fuzz is about and hopefully be able to contribute something.
Wizards are also for, well, wizards
I always enjoy reading the IPspace blog and as Ivan has stated about our blog, I don’t always agree with his opinion, but they are informative and cover just about everything networking. So this may come as a surprise, but in response to his “Do we have too many knobs” post from about a week ago I have one simple response: “Amen”.
Networking is unnecessarily complicated. We have written several blogs on this topic and related items. I used to run the sustaining organization for all data products at my previous company and when you do the analysis of the customer reported issues that come in to the support organization, you find that a very large percentage stem from configuration mistakes.
Many of those mistakes are not typos. We like to refer to fat fingered configurations often as a reason to move to a more automated configuration and provisioning environment, but most of the configuration mistakes that are made are simply because we have made it so difficult to configure these devices. Type something in the wrong order and it may not work right or behave slightly differently. Simple checks across configurations that could avoid many problems are Continue reading
Riding the SD-WAN Wave
Software Defined Networking has changed the way that organizations think about their network infrastructure. Companies are looking at increasing automation of mundane tasks, orchestration of policy, and even using white box switches with the help of new unbound operating systems. A new class of technologies that is coming to market hopes to reduce complexity and cost for the Achilles Heel of many enterprises: the Wide Area Network (WAN).
Do You WANt To Build A Snowman?
The WAN has always been a sore spot for enterprise networks. It’s necessary to connect your organization to the world. If you have remote sites or branch locations, it is critical for daily operations. If you have an e-commerce footprint your WAN connection needs to be able to handle the generated traffic. But good WAN connectivity costs money. Lots of money.
WAN protocols are constantly being refined to come up with the fastest possible transmission and the highest possible uptime. Frame Relay, Asynchronous Transfer Mode (ATM) and Multi-Protocol Label Switching (MPLS) are a succession of technologies that have shaped enterprise WAN connectivity for over a decade. They have their strengths and weaknesses. But it is difficult to build an enterprise WAN Continue reading
PQ Show 36 – ENIGMA NMS – Network Management – The Engineers Monitoring System from NETSAS Australia
Network management and monitoring is at the heart of every network but not every product is based on client requests. Enigma NMS has been built by engineers for engineers to use. That's why the interface will be totally familiar to you and has the features you expect to be in the product.
Author information
The post PQ Show 36 – ENIGMA NMS – Network Management – The Engineers Monitoring System from NETSAS Australia appeared first on Packet Pushers Podcast and was written by Greg Ferro.
Recent Networking Opensource projects – OPNFV, Openconfig, ONOS
I came across few recent Opensource projects which I found them to be interesting. In this blog, I will cover some details on OPNFV, Openconfig, ONOS. There is no relation between the 3 projects, the common thing is all the 3 projects are focussed on Networking and Cloud and all are relatively new. OPNFV OPNFV … Continue reading Recent Networking Opensource projects – OPNFV, Openconfig, ONOSWhy don’t all companies take a customer centric approach to service?
Why don't all companies take a customer-centric approach to service?
by Srikanth Sandru, Technical Support Engineer - November 24, 2014
Being part of the Packet Design Customer Care department and specifically the Technical Support group, I constantly ask: What more can we do to better serve our customers? My own recent experiences as a customer of various consumer products revealed some things that I can correlate to my job and Packet Design’s customer centric approach.
A Tale of Two ISPs
I use two different Internet service providers and experienced issues with both recently. The first, which I will call “ISP1,” is a wired service provider. One day my service was disconnected, as my subscription had expired. I called them to ask for a renewal at 10:00 a.m., and the customer care executive confirmed a collection agent would arrive shortly. (They have a door-to-door bill collection staff, and they turn your service on immediately upon payment). The agent did show up to renew my service.
At 4:00 p.m. (six hours after I had already renewed the service), I received a call from the same ISP1 asking if I would like to renew, since my Continue reading
Wireshark tid-bit: Packets larger than the MTU size.. why, how?
Ever so often when I was doing some packet analysis I would come across systems that were sending packets larger the Ethernet MTU of the segment. Or so I thought those packets were getting transmitted, eventually I finally figured out why I was seeing packets with an increased packet size. The answer was large segment/send […]Schuberg Philis Deploys VMware NSX
• Application Roll Out Reduced from Weeks to Minutes
• VMware NSX Enables Better Agility, Flexibility and Security
Recently I had the opportunity to speak with the team at Schuberg Philis about their successful, production deployment of VMware NSX. As background, Schuberg Philis is an innovative business technology company and an important player in the field of mission critical outsourcing services. The company serves customers across financial services, retail suppliers and utilities, and therefore must comply with the highest international risk management and corporate governance standards, while remaining flexible to evolving customer needs.
The adoption of VMware NSX based network virtualization has transformed the way Schuberg Philis runs its IT. In order to provide 100 percent functional up time of its customers’ critical applications, Schuberg Philis continuously optimizes its infrastructure and processes. However, the company increasingly saw its network as a barrier to increasing business agility.
To solve this challenge and to accelerate application roll out, the Schuberg Philis implemented a software-defined data center environment, and deployed VMware NSX. Schuberg Philis is taking advantage of the VMware NSX platform’s flexibility, security and agility to accelerate the deployment of applications to customers. Schuberg Philis customers now have easy access to Continue reading
FECs, LDP and BGP in the MPLS World
After discussing the basics of MPLS and LDP in our Tech Talks chat, Seamus Gilchrist and myself focused on a concept that perplexes many networking engineers entering the MPLS world: the relationship between Forward Equivalence Classes (FEC), LDP and BGP.
Generating SSH keys to use for CoreOS host connectivity
While this is likely widely known, I figured this was worth documenting for someone that might not have done this before. If you’ve looked at CoreOS at all you know that in order to connect to a CoreOS server it needs to be configured with your machines SSH key. This is done through the cloud-config file which we’ll cover in much greater detail in a later post. So let’s quickly walk through how to generate these keys on the three different operating systems I’m using for testing…
CentOS
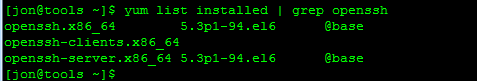
You’ll need to have OpenSSH installed on the CentOS host you’re using in order for this to work. Check to see if it’s installed…
Now let’s check to make sure that we don’t already have a key generated…
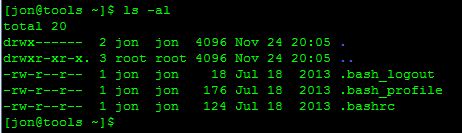
There’s no .ssh folder listed in our home directory so let’s move on to generating the key.
Note: If there was a .ssh folder already present, there’s a good chance you already have a key generated. If you want to use this existing key, skip ahead to after we generate the new key.
Since there isn’t a .ssh folder present, let’s create a new key. Continue reading
Outsourcing Mistakes
Outsourcing is complex, and there are lots of ways it can go wrong, or simply fail to deliver. I’ve put together a list of things that I see going wrong with outsourcing arrangements. Of course it’s not exclusive!
There’s a few different types of outsourcing. It might mean procuring a commodity service – e.g. IaaS, or it might mean handing over your existing environment and staff to a third party. There’s also a whole range of levels in between, but the usual deal is: Some part of your environment gets managed or delivered by someone else, according to the terms of a fixed agreement.
Here’s a few things I’ve learnt to watch out for (nb not all these items apply to all types of agreements):
Not keeping up to date
If your outsourcer is managing your software, the contract usually covers applying security patches and bug fixes. But what gets missed is larger upgrades – e.g. ESXi 4.1 to 5.x. Everything goes OK for a while…and then your version goes End of Support.
It then becomes a major drama to get the upgrades sorted out. For financial purposes, you may not be able to do major Continue reading
Facebook Fabric Networking Deconstructed
Facebook engineering has recently introduced their next-generation data center network architecture planned to be operational in the new Altoona facility. Introducing data center fabric, the next-generation Facebook data center network
In this post we are going to look at the design proposed and break down some of the reasons why this design was necessary although maybe still not ideal.
Facebook, the killer app.. literally
Within Facebook’s data center the network is a critical component driving this social networks ever increasing appetite to connect people together. The challenges unfold on two axis, the first being the explosive growth in the user population and its increasing demand and access bolstered by modern mobile devices and the second related to the exponential growth of machine to machine traffic required to aggregate and compose information which we all know and love. Due to the nature of Facebook applications, machine to machine communications is “several orders of magnitude larger than what goes out the Internet”
The need to parallelize work becomes a daunting task in this environment requiring an enormous communication fabric for internal processing.
the rate of our machine-to-machine traffic growth remains exponential, and the volume has been doubling at an interval of less Continue reading
Eight CCIEs. Need I say Moore?
A long time student of INE, Neil Moore has done it again, last time becoming the worlds first 7x CCIE, and this time becoming the worlds first and only 8x CCIE. And no, he doesn’t work for Cisco.
As a side note, INE has been experiencing phenomenal growth, and tremendous passing rates for people that have been sitting our R&S, Data Center and Collaboration bootcamps. In fact, of just the bootcamps we’ve held this year, nearly all of our students have reported back to us a pass in the 3-4 weeks following their bootcamp experience. Now mind you, these folks come to us studied up and prepared for the bootcamp, but they all credit us as being the deciding factor in their pass.
We’re also adding new content all the time, including Python scripting, Openstack and SDN such as OVS. Check out our Black Friday deals and grab an All Access Pass or sign up for a bootcamp and check out what’s new!
Scaling SDN: Is OpenFlow Ready for Prime Time?
Pica8 Says ‘Yes’ and Challenges the FUD
Up to this point, OpenFlow has mostly been deployed in research and higher-education environments. These early trials have shed some light on interesting use cases, what OpenFlow is good for, and of course, what OpenFlow might not be so good for.
This is important because OpenFlow and SDN adoption is only going to grow. It’s imperative that we understand these limitations – specifically, what’s real and what’s FUD.
One of these is scale.
If you’ve kicked the tires on OpenFlow, one question you may have heard is “How many flows does that switch support?” However, this question is only part of the story. It’s like asking only about a car’s top speed when what you should be thinking other things too – such as fuel efficiency and maintenance. So to figure out the right questions, we first need to go over a bit of background.
In its most basic terms, any network traffic, whether it’s Layer 2, Layer 3, or something else, is governed by a of forwarding rules as defined by a series of protocols. If it’s this MAC, do this. If it’s that IP, go Continue reading
The Alternative Guide to installing GNS3 on Linux using Chris Welsh’s script.
Hello Windows, MAC and Linux pros! Based on comments from a previous release of the Getting Started Guide for Linux, it becameThe onePK office prank
 You know those times when you paste innocuous config to a router and it just freezes up on you? Even if you know you’ve done nothing wrong it can be a few scary seconds until the router starts to respond again. While reading up on onePK I was trying to come up with a use case. Though I eventually thought about some other things that would actually be useful. The very first thing that came to mind was something to test just for fun.
You know those times when you paste innocuous config to a router and it just freezes up on you? Even if you know you’ve done nothing wrong it can be a few scary seconds until the router starts to respond again. While reading up on onePK I was trying to come up with a use case. Though I eventually thought about some other things that would actually be useful. The very first thing that came to mind was something to test just for fun.
The prank
Picture this; You ask a co-worker to login to a router and shutdown an interface which won’t be used anymore. Your colleague logs into the device and disables the interface and the session hangs. Only it doesn’t just hang, it’s dead and apparently your colleague can’t ping the device now. At this point it can be a good idea to ask your co-worker about what exactly he changed.
Continue reading

