Arista EOS MPLS P/PE-router Behavior
Something didn’t feel right as I tried to check whether the IPv4 ECMP I observed in the latest version of Arista cEOS containers works with my MPLS/anycast scenario. The forwarding tables seemed OK, but I wasn’t getting MPLS labels in the ICMP replies (see RFC 4950 for details), even though I know Arista EOS can generate them.
I decided to go down that rabbit hole and built the simplest possible BGP-free core (the addition of BGP will become evident in a few seconds) to investigate PE/P-router behavior:
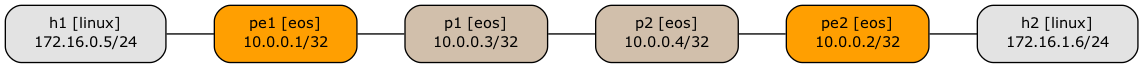
Lab topology
What Your EKS Flow Logs Aren’t Telling You
If you’re running workloads on Amazon EKS, there’s a good chance you already have some form of network observability in place. VPC Flow Logs have been a staple of AWS networking for years, and AWS has since introduced Container Network Observability, a newer set of capabilities built on Amazon CloudWatch Network Flow Monitor, that adds pod-level visibility and a service map directly in the EKS console.
It’s a reasonable assumption that between these tools, you have solid visibility into what’s happening on your cluster’s network. But for teams focused on Kubernetes security and policy enforcement, there’s a significant gap — and it’s not the one you might expect.
In this post, we’ll break down exactly what EKS native observability gives you, where it falls short for security-focused use cases, and what Calico’s observability tools, Goldmane and Whisker, provide that you simply cannot get from AWS alone.
What EKS Gives You Out of the Box
AWS offers two main sources of network observability for EKS clusters:
VPC Flow Logs capture IP traffic at the network interface level across your VPC. For each flow, you get source and destination IP addresses, ports, protocol, and whether traffic was accepted or rejected at Continue reading
NAN116: From NSoT to Operational Automation: Fast Time-to-Value with Nautobot Cloud (Sponsored)
Building a Network Source of Truth (NSoT) is only step one in an automation effort — turning it into operational automation is where outcomes happen. In this sponsored episode by Network to Code, Eric Fetty, a self-taught network engineer who literally automated his way through his CCIE lab, shares how he’s doing exactly that at... Read more »D2DO297: The Future of Open-Source Contributions in the AI Age
Kyler and Ned sit down with Liz Fong-Jones, Technical Fellow at Honeycomb, to discuss the impact of AI on open-source contributions. Liz proposes shifting the script from code patch contributions to detailed bug reports. They also break down the distinction between programming and software engineering, and the critical role of OpenTelemetry in ensuring the observability... Read more »TCG071: Cloud Cloning and Portability – Why Multi-Cloud Freedom Still Requires Translation (Sponsored)
In this sponsored episode, FluidCloud co-founders Sharad Kumar and Harshit Omar sit down with William and Eyvonne to discuss how FluidCloud tackles multi-cloud portability. They detail how FluidCloud acts as a cloning platform that scans an existing cloud or VMware environment, extracts complex infrastructure configurations (including compute and storage, as well as firewall rules and... Read more »Introducing Custom Regions for precision data control
A key part of our mission to help build a better Internet is giving our customers the tools they need to operate securely and efficiently, no matter their compliance requirements. Our Regional Services product helps customers do just that, allowing them to meet data sovereignty legal obligations using the power of Cloudflare’s global network.
Today, we're taking two major steps forward: First, we’re expanding the pre-defined regions for Regional Services to include Turkey, the United Arab Emirates (UAE), IRAP (Australian compliance) and ISMAP (Japanese compliance). Second, we’re introducing the next evolution of our platform: Custom Regions.
Before we dive into what’s new, let’s revisit how Regional Services provides the best of both worlds: local compliance and global-scale security. Our approach is fundamentally different from many sovereign cloud providers. Instead of isolating your traffic to a single geography (and a smaller capacity for attack mitigation), we leverage the full scale of our global network for protection and only inspect your data where you tell us to.
Here’s an overview of how it works:
Global ingestion & L3/L4 DDoS defense: Traffic is ingested at the closest Cloudflare data center, wherever in the world that Continue reading
What Your EKS Flow Logs Aren’t Telling You
If you’re running workloads on Amazon EKS, there’s a good chance you already have some form of network observability in place. VPC Flow Logs have been a staple of AWS networking for years, and AWS has since introduced Container Network Observability, a newer set of capabilities built on Amazon CloudWatch Network Flow Monitor, that adds pod-level visibility and a service map directly in the EKS console.
It’s a reasonable assumption that between these tools, you have solid visibility into what’s happening on your cluster’s network. But for teams focused on Kubernetes security and policy enforcement, there’s a significant gap — and it’s not the one you might expect.
In this post, we’ll break down exactly what EKS native observability gives you, where it falls short for security-focused use cases, and what Calico’s observability tools, Goldmane and Whisker, provide that you simply cannot get from AWS alone.
What EKS Gives You Out of the Box
AWS offers two main sources of network observability for EKS clusters:
VPC Flow Logs capture IP traffic at the network interface level across your VPC. For each flow, you get source and destination IP addresses, ports, protocol, and whether traffic was accepted or rejected at Continue reading
BGP Labs: Goodbye, Cumulus Linux
When I started the Online BGP Labs project in mid-2023, Cumulus Linux still seemed like a good platform to use. You could run devices as virtual machines (we were still supporting VirtualBox) or in containers (containerlab was improving with every release), and it looked more polished than bare-bones FRRouting.
Things only went downhill from there (from the perspective of offering a free and easy-to-use solution with a CLI resembling commonly-used devices):
HW073: OpenIntent: A Collaborative Effort for Wi-Fi Interoperability
OpenIntent is an open-source, collaborative effort by network operators to develop a standard schema to describe the necessary information needed to deploy network equipment. Keith sits down with Jake Snyder, the developer behind OpenIntent. They discuss why he developed OpenIntent, the building blocks of the schema, and his vision for seamless Wi-Fi design interoperability. AdSpot... Read more »PP101: Hackers Tap Intune to Wipe Windows Devices; Tricksters Trump E2E Encryption
On today’s news roundup we assess the White House’s new US cyber strategy (bellicose, bombastic, and boiler-plate), discuss a cyberattack attributed to Iran that used Windows to wipe thousands of devices, and dig into a Microsoft update on Entra passkeys. JJ isn’t impressed with new research that bypasses Wi-Fi client isolation, corporate spyware gets a... Read more »The Value of Concise Communication

When I first started working at Tech Field Day, one of the things that I struggled with was writing. Sure, I’d been writing blog posts for almost three years at that point. But what I really had issues with was my communication style through email. Every message became a small blog post unto itself. I spent more time answering every possible question and providing way more information than was needed. Luckily, Stephen Foskett helped me figure out that concise communication was critical. That lesson has grown on me through the current day.
Working With a Watch
I want you to think back to an interaction that you’ve had recently where you were talking to someone. Maybe you were asking them a question or looking for them to provide an opinion about something. How much did they talk? Was it a short pointed answer? Or did it feel as if it was going on forever? It’s something I’ve noticed recently with people I talk to in real life. The discussions aren’t short and focused. Instead they carry a lot of extra information and exposition that makes things take far too long.
Yes, I know the irony of that statement for Continue reading
HS127: You’re Not Thinking About Your Network the Way You Should (Sponsored)
Mav Turner, Chief Product Officer at Kentik, joins John Burke and Drew Conry-Murray for an in-depth conversation on the importance of deep visibility into enterprise networks. As networks grow more complex and stretch from on-prem and WAN to multi-cloud and edge locations, this sponsored discussion explores how good visibility supports everything from daily operations to... Read more »MANRS for Enterprise Customers
In October 2023, I was talking about Internet routing security at the DEEP conference in Zadar, Croatia. After explaining the (obvious) challenges and the initiatives aimed at making Internet routing more secure (MANRS), I made my usual recommendation: vote with your wallet. However, if you’re a company in Croatia (or Slovenia, or a number of other countries), you’re stuck.
While ISPs in Croatia might be doing a great job, none of them is a MANRS participant1, so we don’t know how good they are. The situation is not much better in Slovenia; the only ISPs claiming to serve Slovenia are Anexia (a cloud provider) and Go6 Institute, the small network operated by my good friend (and True Believer in IPv6 and MANRS) Jan Žorž. Moving further north, there are decent choices in Austria, and tons of options in Germany or Switzerland. I must be living in a truly thrifty part of Europe.
NB566: Google Spins Out Fiber Business; HPE Networking Revenue Soars in Q1
Take a Network Break! We begin with listener follow-up on Cisco SD-WAN vulnerabilities and a report that Nvidia is investing billions to develop open-source AI models. In our Red Alert section we warn of multiple vulnerabilities in Veeam’s backup software for Windows and a couple of Chrome zero-days. We cover new features in Fortinet’s FortiOS... Read more »Standing up for the open Internet: why we appealed Italy’s “Piracy Shield” fine
At Cloudflare, our mission is to help build a better Internet. Usually, that means rolling out new services to our millions of users or defending the web against the world’s largest cyber attacks. But sometimes, building a better Internet requires us to stand up against laws or regulations that threaten its fundamental architecture.
Last week, Cloudflare continued its legal battle against "Piracy Shield,” a misguided Italian regulatory scheme designed to protect large rightsholder interests at the expense of the broader Internet. After Cloudflare resisted registering for Piracy Shield and challenged it in court, the Italian communications regulator, AGCOM, fined Cloudflare a staggering €14 million (~$17 million). We appealed that fine on March 8, and we continue to challenge the legality of Piracy Shield itself.
While the fine is significant, the principles at stake are even larger. This case isn't just about a single penalty; it’s about whether a handful of private entities can prioritize their own economic interests over those of Internet users by forcing global infrastructure providers to block large swaths of the Internet without oversight, transparency, or due process.
To understand why we are fighting this, it’s necessary to take a step back Continue reading
netlab Graphs with Multi-Access Links
A netlab user wanted to create a nice-looking topology graph from a simple topology connecting a few devices to a broadcast (multi-access) link. I don’t have his exact topology, so we’ll use this one (skipping the details like setting device types)
nodes: [ r1, r2, h1, h2 ]
links:
- r1-r2
- interfaces: [ r1, r2, h1, h2 ]
This is what GraphViz generates based on netlab’s description of the lab topology:
Profil Wu Jingyu, Atlet Taekwondo Tiongkok Paling Dominan di Olimpiade
Daftar Pustaka
Wu Jingyu dikenal sebagai atlet taekwondo Tiongkok paling sukses sepanjang sejarah. Ia membangun reputasi global melalui kecepatan, ketepatan, dan mental juara. Selain itu, Wu Jingyu menginspirasi generasi muda lewat dedikasi dan konsistensi. Oleh karena itu, namanya selalu muncul dalam pembahasan taekwondo dunia.
Sejak awal karier, Wu Jingyu menunjukkan bakat luar biasa. Ia berlatih keras dan fokus pada detail teknik. Dengan demikian, ia mampu bersaing di level internasional. Bahkan, ia mendominasi kelas -49 kg putri selama bertahun-tahun.
Profil Singkat Wu Jingyu
Wu Jingyu lahir di Jingdezhen, Jiangxi, pada 23 Maret 1987. Ia mulai mengenal taekwondo sejak usia remaja. Selanjutnya, ia bergabung dengan sistem pelatnas Tiongkok. Di sana, ia menempa kemampuan fisik dan mental secara intensif.
Sebagai atlet, Wu Jingyu terkenal disiplin. Ia menjaga kondisi fisik, pola makan, dan fokus mental. Oleh sebab itu, performanya tetap stabil dalam tekanan tinggi. Selain itu, ia selalu mempelajari gaya lawan sebelum bertanding.
Perjalanan Karier Internasional
Karier internasional Wu Jingyu berkembang pesat. Ia meraih gelar dunia dan Olimpiade secara konsisten. Dengan kata lain, Continue reading
Honda Prelude: Coupe Legendaris dengan Performa dan Desain Ikonik
Daftar Pustaka
Honda Prelude merupakan coupe legendaris yang mencerminkan inovasi, performa, dan karakter sporty khas Honda. Sejak awal kemunculannya, mobil ini langsung menarik perhatian penggemar otomotif dunia. Selain itu, Honda Prelude menghadirkan keseimbangan antara kenyamanan, teknologi, dan pengendalian presisi. Oleh karena itu, banyak kolektor hingga pecinta JDM masih memburunya hingga sekarang.
Sejarah Honda Prelude yang Menginspirasi
Honda pertama kali memperkenalkan Honda Prelude pada tahun 1978. Saat itu, Honda ingin menciptakan coupe sporty dengan teknologi modern. Selanjutnya, Prelude berkembang melalui lima generasi berbeda. Setiap generasi membawa peningkatan desain, mesin lebih bertenaga, dan fitur canggih.
Selain itu, Prelude menjadi pelopor teknologi four wheel steering pada era 1980-an. Teknologi ini meningkatkan stabilitas saat menikung. Oleh sebab itu, Honda Prelude dikenal sebagai mobil yang menyenangkan untuk dikendarai. Bahkan, banyak jurnalis otomotif memuji keseimbangan sasisnya.
Desain Eksterior yang Sporty dan Elegan
Dari segi visual, Honda Prelude selalu tampil menawan. Garis bodinya terlihat aerodinamis dan tegas. Selain itu, lampu depan pop-up pada Continue reading