Feedback: ipSpace.net Materials
Andy Lemin sent me such a wonderful review of ipSpace.net materials that I simply couldn’t resist publishing it ;)
ipSpace.net is probably my favorite networking resource out there. After spending years with other training content sites which are geared around certifications, ipspace.net provides a totally unique source of vendor neutral opinions, information, and anecdotes – the kind of information that is just not available anywhere else. And to top it off, is presented by a wonderful speaker who is passionate, smart and really knows his stuff!
The difference between an engineer who just has certs versus an engineer who has a rounded and wide view of the whole industry is massive. An engineer with certs can configure your network, but an engineer with all the knowledge this site provides, is someone who can question why and challenge how we can configure your network in a better way.
Feedback: ipSpace.net Materials
Andy Lemin sent me such a wonderful review of ipSpace.net materials that I simply couldn’t resist publishing it ;)
ipSpace.net is probably my favorite networking resource out there. After spending years with other training content sites which are geared around certifications, ipspace.net provides a totally unique source of vendor neutral opinions, information, and anecdotes – the kind of information that is just not available anywhere else. And to top it off, is presented by a wonderful speaker who is passionate, smart and really knows his stuff!
The difference between an engineer who just has certs versus an engineer who has a rounded and wide view of the whole industry is massive. An engineer with certs can configure your network, but an engineer with all the knowledge this site provides, is someone who can question why and challenge how we can configure your network in a better way.
CyberFlood: Test Duration, Load Specification and Default Starter Tests
Okay so ORIGINALLY the idea was to do a YouTube video to explain the interaction and relationship between the “Test Duration” of a CyberFlood test and the “Load Specification”. However, in order to best explain “load specification” though it is... Read More ›
The post CyberFlood: Test Duration, Load Specification and Default Starter Tests appeared first on Networking with FISH.
Rust Notes: Booleans
The boolean type in Rust is defined with the bool type annotation and can be either a true or false literal. Boolean Considerations false has a bit battern of 0x00 true has a bit battern of 0x01 Booleans cannot be used in arithmatic unless they are cast to a u8 continue reading
Interop LDP and Segment Routing with IP infusion and MikroTik
Introduction
During networking field day service provider 1 there was a ton of talk about segment routing (SR) and ethernet virtual private networks (EVPN). One of the biggest questions was “how do we get there?” and while we won’t examine EVPN in this post (it’s coming in a future post don’t worry) we will look at how you can take advantage of SR while still having large portions of LDP in your network.
The team here at IP architechs works on a lot of MikroTik and whitebox gear so we’ll focus on a deployment using MikroTik and IP infusion.
MPLS and IGP setup
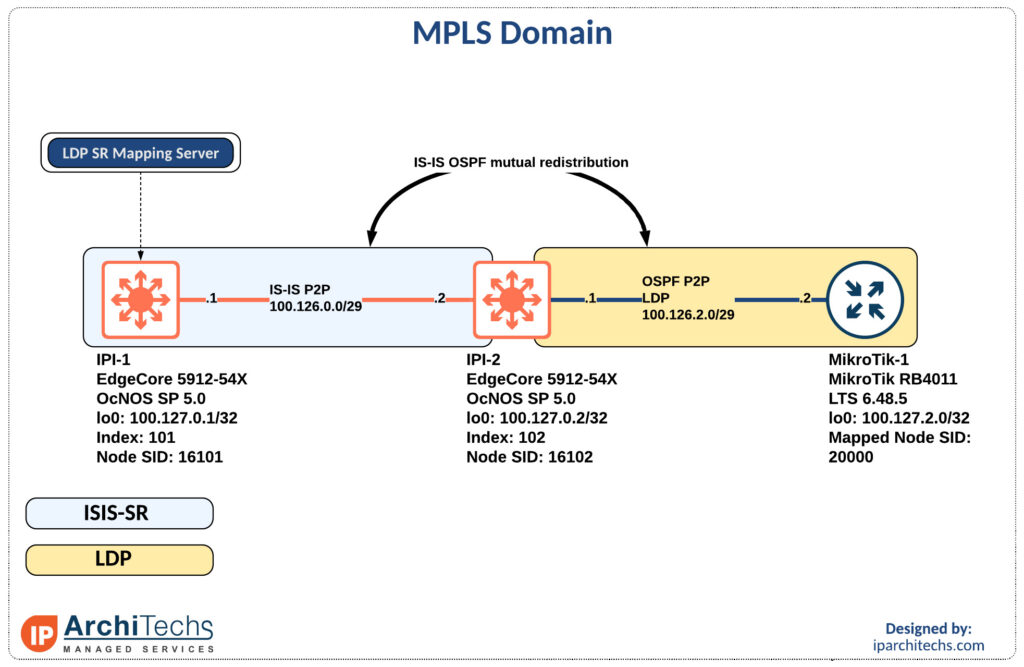
The first thing to accomplish is end to end reachability between the provider edge (PE) routers. MikroTik doesn’t support IS-IS so we will have to perform redistribution between the IS-IS segment and the OSPF segment as seen above.
MPLS only requires the /32s of the loopbacks for functionality so redistribution is limited to the /32 loopbacks of the PE routers.
ip prefix-list LDP-PE-LOOPBACKS
seq 10 permit 100.127.2.0/24 eq 32
!
ip prefix-list SR-PE-LOOPBACKS
seq 10 permit 100.127.0.0/24 eq 32
!
route-map REDIS-OSPF-TO-ISIS permit 10
match ip address prefix-list LDP-PE-LOOPBACKS
!
route-map REDIS-ISIS-TO-OSPF permit Continue readingWorth Reading: We’re a Decade Past Blade Server Market Peak
Stumbled upon a totally unexpected fun fact:
Every server vendor either peaked or hits the peak of maximum units sold per quarter in 2015. In the years that follow, the monthly averages drop.
Keep that in mind the next time Cisco sales team comes along with a UCS presentation.
Worth Reading: We’re a Decade Past Blade Server Market Peak
Stumbled upon a totally unexpected fun fact:
Every server vendor either peaked or hits the peak of maximum units sold per quarter in 2015. In the years that follow, the monthly averages drop.
Keep that in mind the next time Cisco sales team comes along with a UCS presentation.
Performance testing of Commercial BGP
1st Post Comparing Open Source BGP Stacks 2nd Post Follow-up Measuring BGP Stacks Performance 3rd Post Comparing Open Source BGP stacks with internet routes 4th Post Bird on Bird, Episode 4 of BGP Perf testing 5th Post BGP Performance 5 – 1000 full internet neighbors 6th Post BGP Performance testing...Juniper vQFX and Containerlab
In this post, we look at how Containerlab can be used to quickly spin up vQFX topologies for network validation and testing. We’ll walk through the entire process - how to build docker images from vQFX images, what happens behind the scenes when bringing these containers up and how to build/verify your topology.
Worth Reading: Non-Standard Standards, SRv6 Edition
Years ago, I compared EVPN to SIP – it has a gazillion options, and every vendor implements a different subset of them, making interoperability a nightmare.
According to Andrew Alston, SRv6 is no better (while being a security nightmare). No surprise there.
Worth Reading: Non-Standard Standards, SRv6 Edition
Years ago, I compared EVPN to SIP – it has a gazillion options, and every vendor implements a different subset of them, making interoperability a nightmare.
According to Andrew Alston, SRv6 is no better (while being a security nightmare). No surprise there.
Rust Notes: Integers and Floats
Integers Integers represent whole numbers. Rust has both unsigned integers and signed integers. unsigned integers cannot be negative, and have a higher positive range than signed integers, that can be negative, but have a lower postive range. The following table lists the integer...continue reading
What the Citrix Private Equity Deal Means for Enterprise Customers
The deal will combine Citrix with data management and machine learning giant Tibco, creating a software company that will compete with Microsoft and Amazon.Cloud Engineering For The Network Pro: Part 2 – Virtual Network Architecture (Video)
Part 2 of this cloud engineering series by Michael Levan digs into the basic network services available in Azure and AWS. You can subscribe to the Packet Pushers’ YouTube channel for more videos as they are published. It’s a diverse a mix of content from Ethan and Greg, plus selected videos from our events. It’s […]
The post Cloud Engineering For The Network Pro: Part 2 – Virtual Network Architecture (Video) appeared first on Packet Pushers.
Heavy Networking 616: Do We Need An SMTP Alternative? TMTP And MNM Are Here To Find Out
The SMTP protocol isn't broken, but email kinda is. Spam, phishing, and other unwanted messages are easy to deliver and harder to stop. On today's Heavy Networking we discuss TMTP and mnm, a proposed new protocol and client that aim to preserve the benefits of email while eliminating vulnerabilities and offering a better experience. Our guest is Liam Breck, creator of TMTP and mnm.
The post Heavy Networking 616: Do We Need An SMTP Alternative? TMTP And MNM Are Here To Find Out appeared first on Packet Pushers.
Heavy Networking 616: Do We Need An SMTP Alternative? TMTP And MNM Are Here To Find Out
The SMTP protocol isn't broken, but email kinda is. Spam, phishing, and other unwanted messages are easy to deliver and harder to stop. On today's Heavy Networking we discuss TMTP and mnm, a proposed new protocol and client that aim to preserve the benefits of email while eliminating vulnerabilities and offering a better experience. Our guest is Liam Breck, creator of TMTP and mnm.Could Open Base Station SoCs Unleash A New Era In Mobile Infrastructure?
This article was originally published in Packet Pushers Ignition on March 23, 2021. Just as nature abhors a vacuum and seeks to fill it with any available matter, business abhors a single-source solution to wide scale problems. Competitors rush to fill the vacuum of choice with alternative, interchangeable products. The IT market typically fosters competition […]
The post Could Open Base Station SoCs Unleash A New Era In Mobile Infrastructure? appeared first on Packet Pushers.
Backing Up the Dump Truck

Hello Ellen,
I have received a number of these spam messages over the past few weeks and I had hoped they would eventually taper off. However, it doesn’t appear that is the case. So I’ll take the direct approach.
I’m a member of the CCIE Advisory Council. Which means I am obligated to report any and all attempts to infringe upon the integrity of the exam. As you have seen fit to continue to email me to link to your site to promote your test dumps I think you should be aware that I will be reporting you to the CCIE team.
Good luck in your future endeavors after they shut you down for violating their exam terms and conditions. And do not email me again.
That’s an actual email that I sent TODAY to someone (who probably isn’t really named Ellen) that has been spamming me to link to their CCIE dump site. The spam is all the same. They really enjoy reading a random page on my site, usually some index page picked up by a crawler. They want me to insure a link to their site which is a brain dump site for CCIE Continue reading