Azure Route Server: Behind the Scenes
Last week I described the challenges Azure Route Server is supposed to solve. Now let’s dive deeper into how it’s implemented and what those implementation details mean for your design.
The whole thing looks relatively simple:
Cisco Live 2021 – Online
It is that time of year again, just not quite the same as it once was. Once again Cisco Live …
The post Cisco Live 2021 – Online first appeared on Fryguy's Blog.Worth Reading: Modules, Monoliths, and Microservices
If you want to grow beyond being a CLI (or Python) jockey, it’s worth trying to understand things work… not only how frames get from one end of the world to another, but also how applications work, and why they’re structured they way they are.
Daniel Dib recently pointed out another must-read article in this category: Modules, monoliths, and microservices by Avery Pennarun – a wonderful addition to my distributed systems resources.
Worth Reading: Modules, Monoliths, and Microservices
If you want to grow beyond being a CLI (or Python) jockey, it’s worth trying to understand things work… not only how frames get from one end of the world to another, but also how applications work, and why they’re structured they way they are.
Daniel Dib recently pointed out another must-read article in this category: Modules, monoliths, and microservices by Avery Pennarun – a wonderful addition to my distributed systems resources.
pygnmi 8. Securing the gNMI connectivity with self-signed certificates.
Hello my friend,
Continuing our explanation of the pyGNMI, we’ll take a loon into the security aspect of the tool. Namely, we will take a look how quickly and easily you can implement the encryption between your host running pyGNMI and the gNMI speaking network function.
2
3
4
5
retrieval system, or transmitted in any form or by any
means, electronic, mechanical or photocopying, recording,
or otherwise, for commercial purposes without the
prior permission of the author.
Where is the GNMI in the Network Automation?
The automation world (network and not only) can at a high level be split into text-based automation and model-driven automation. The text based automation is all about Linux systems, where we typically template the whole configuration files, put them in the corresponding folders and then restart daemons. The model driven approach is where we communicate with the network devices using the NETCONF, RESTCONF or gNMI based on the YANG modules. At the current moment, gNMI is most dynamically developing protocol. We not only teaches you how it works and when to use it, but we also created a Python library, Continue reading
Is 5G Vulnerable to New Cyberattacks Thanks to Edge Computing?
Service providers and their enterprise customers can take steps to improve security measures within the 5G infrastructure and the services deployed on it.Who Pays The Price of Redundancy?

No doubt by now you’ve seen the big fire that took out a portion of the OVHcloud data center earlier this week. These kinds of things are difficult to deal with on a good day. This is why data centers have reductant power feeds, fire suppression systems, and the ability to get back up to full capacity. Modern data centers are getting very good at ensuring they can stay up through most events that could impact an on-premises private data center.
One of the issues I saw that was ancillary to the OVHcloud outage was the small group of people that were frustrated that their systems went down when the fire knocked out the racks where their instances lived. More than a couple of comments mentioned that clouds should not go down like this or asked about credit for time spent being offline or some form of complaints about unavailability. By and large, most of those complaining were running non-critical systems or were using the cheapest possible instances for their hosts.
Aside from the myopia that “cloud shouldn’t go down”, how do we deal with this idea that cloud redundancy doesn’t always translate to single instance availability? I think we Continue reading
Heavy Networking 566: Inside Intel’s Strategy To Unlock Data Center Performance (Sponsored)
On today's Heavy Networking we dive into Intel's portfolio---including Tofino, SmartNICs, P4, and more---to understand how it unlocks the compute power of your data center. Our guest is Mike Zeile, Data Center Group Vice President and General Manager of End-to-End Network Applications at Intel. Intel is our sponsor.Heavy Networking 566: Inside Intel’s Strategy To Unlock Data Center Performance (Sponsored)
On today's Heavy Networking we dive into Intel's portfolio---including Tofino, SmartNICs, P4, and more---to understand how it unlocks the compute power of your data center. Our guest is Mike Zeile, Data Center Group Vice President and General Manager of End-to-End Network Applications at Intel. Intel is our sponsor.
The post Heavy Networking 566: Inside Intel’s Strategy To Unlock Data Center Performance (Sponsored) appeared first on Packet Pushers.
In Macedonia, Strengthening IXP.mk’s Peering Infrastructure

The Internet Society has been supporting the development of the Internet in Macedonia by collaborating with the Faculty of Computer Science and Engineering (FCSE) of the Saints Cyril and Methodius University in Macedonia on its IXP.mk project. IXPs play a critical role in bringing faster and more affordable Internet, and the Macedonian IXP (IXP.mk) had been established in June 2018 with technical support from a number of stakeholders.
Switch and MUX to Strengthen Infrastructure
As traffic grew, IXP.mk needed to increase its peering capacity with improved switching capabilities and space for data racks that would allow it to attract new participants to the exchange. In 2020, the Internet Society provided IXP.mk with a switch and two Fiber Optic Multiplexers (Fiber Mux) that enabled an additional peering location to be established in the Telesmart Telekom data center, thereby making it easier for other major networks and Content Distribution Networks to peer with each other. The Fiber Muxes support the transmission of multiple data channels over a single fiber that has been donated by an existing member of IXP.mk.
Critical Service Provider
With a strong peering infrastructure, IXP.mk is now a critical service provider to Continue reading
Lessons Learned from Scaling Up Cloudflare’s Anomaly Detection Platform
Introduction to Anomaly Detection for Bot Management
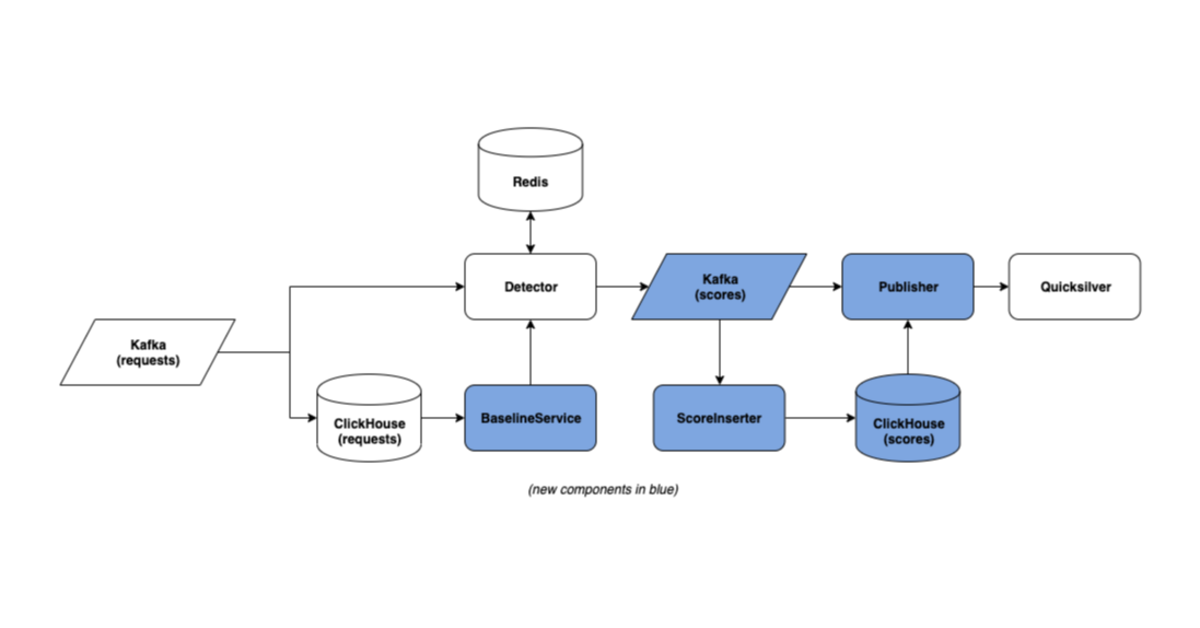
Cloudflare’s Bot Management platform follows a “defense in depth” model. Although each layer of Bot Management has its own strengths and weaknesses, the combination of many different detection systems — including Machine Learning, rule-based heuristics, JavaScript challenges, and more — makes for a robust platform in which different detection systems compensate for each other’s weaknesses.
One of these systems is Anomaly Detection, a platform motivated by a simple idea: because bots are made to accomplish specific goals, such as credential stuffing or content scraping, they interact with websites in distinct and difficult-to-disguise ways. Over time, the actions of a bot are likely to differ from those of a real user. Anomaly detection aims to model the characteristics of legitimate user traffic as a healthy baseline. Then, when automated bot traffic is set against this baseline, the bots appear as outlying anomalies that can be targeted for mitigation.
An anomaly detection approach is:
- Resilient against bots that try to circumvent protections by spoofing request metadata (e.g., user agents)
- Able to catch previously unseen bots without being explicitly trained against them.
So, how well does this work?
Today, Anomaly Detection processes more than Continue reading
Video: Cisco SD-WAN Routing Design
After reviewing Cisco SD-WAN policies, it’s time to dig into the routing design. In this section, David Penaloza enumerated several possible topologies, types of transport, their advantages and drawbacks, considerations for tunnel count and regional presence, and what you should consider beforehand when designing the solution from the control plane’s perspective.
Video: Cisco SD-WAN Routing Design
After reviewing Cisco SD-WAN policies, it’s time to dig into the routing design. In this section, David Penaloza enumerated several possible topologies, types of transport, their advantages and drawbacks, considerations for tunnel count and regional presence, and what you should consider beforehand when designing the solution from the control plane’s perspective.