Meraki-CLI – Command Line Utility for the Meraki Dashboard
Meraki changed the industry years ago as one of the first platforms to use a cloud portal for all configuration; forgoing the typical local CLI/GUI administration of network appliances. One of the first things a traditional network engineer (like myself) may notice about Meraki equipment is their complete lack of a command-line interface. For the […]
The post Meraki-CLI – Command Line Utility for the Meraki Dashboard appeared first on Packet Pushers.
Kubernetes Observability Challenges: The Need for an AI-Driven Solution
Kubernetes provides abstraction and simplicity with a declarative model to program complex deployments. However, this abstraction and simplicity create complexity when debugging microservices in this abstract layer. The following four vectors make it challenging to troubleshoot microservices.
- The first vector is the Kubernetes microservices architecture, where tens to hundreds of microservices communicate. Debugging such a componentized application is challenging and requires specialized tools.
- The second vector is the distributed infrastructure spread across heterogeneous on-premises and cloud environments.
- The third vector of complexity is the dynamic nature of Kubernetes infrastructure. The platform spins up required resources and provides an ephemeral infrastructure environment to scale the application based on demand.
- Lastly, in such a distributed environment, Kubernetes deployments need fine-grained security and an observability model with defense-in-depth to keep them secure. While modern security controls effectively protect your workloads, they can have unintended consequences by preventing applications from running smoothly and creating an additional layer of complexity when debugging applications.
Today, DevOps and SRE teams must stitch together an enormous amount of data from multiple, disparate systems that monitor infrastructure and services layers in order to troubleshoot Kubernetes microservices issues. Not only is it overwhelming to stitch this data, but troubleshooting using Continue reading
Fence Rail Transposition and Caesar Ciphers in Python
Recently I wrote simple encryption and decryption programs in Python to practice my coding skills. The first cipher_encrypt utility takes the clear_text.txt file as input. It first capitalizes all letters and then encrypts the text with the Rail fence cipher. The number of rows can be set using the variable k. The result of the […]Continue reading...
Worth Reading: AAA Deep Dive on Cisco Devices
Decades ago I understood the intricacies of AAA on Cisco IOS. These days I wing it and keep throwing spaghetti at the virtual wall until something sticks and I can log in (after all, it’s all in a lab, and I’m interested in routing protocols not interactions with TACACS+ server).
If you’re experiencing similar challenges you might appreciate AAA Deep Dive on Cisco Devices by the one and only Daniel Dib.
Worth Reading: AAA Deep Dive on Cisco Devices
Decades ago I understood the intricacies of AAA on Cisco IOS. These days I wing it and keep throwing spaghetti at the virtual wall until something sticks and I can log in (after all, it’s all in a lab, and I’m interested in routing protocols not interactions with TACACS+ server).
If you’re experiencing similar challenges you might appreciate AAA Deep Dive on Cisco Devices by the one and only Daniel Dib.
Modernize Network Security With Palo Alto Networks Prisma Access
Prisma Access, from Palo Alto Networks, combines security and access capabilities including CASB, FWaaS, and Zero Trust into a single, cloud-delivered service. Prisma Access can help enterprises provide a secure, high-performance experience for their remote workforces.
The post Modernize Network Security With Palo Alto Networks Prisma Access appeared first on Packet Pushers.
Hedge #66: Tyler McDaniel and BGP Peer Locking
Tyler McDaniel joins Eyvonne, Tom, and Russ to discuss a study on BGP peerlocking, which is designed to prevent route leaks in the global Internet. From the study abstract:
Holistic web protection: industry recognition for a prolific 2020
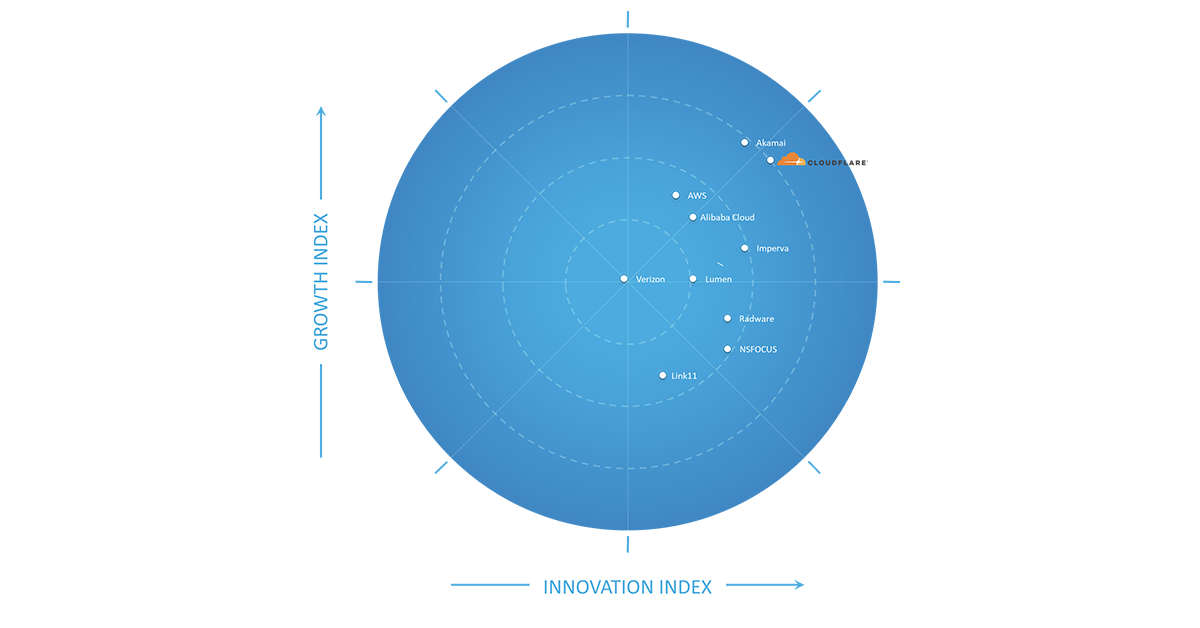
I love building products that solve real problems for our customers. These days I don’t get to do so as much directly with our Engineering teams. Instead, about half my time is spent with customers listening to and learning from their security challenges, while the other half of my time is spent with other Cloudflare Product Managers (PMs) helping them solve these customer challenges as simply and elegantly as possible. While I miss the deeply technical engineering discussions, I am proud to have the opportunity to look back every year on all that we’ve shipped across our application security teams.
Taking the time to reflect on what we’ve delivered also helps to reinforce my belief in the Cloudflare approach to shipping product: release early, stay close to customers for feedback, and iterate quickly to deliver incremental value. To borrow a term from the investment world, this approach brings the benefits of compounded returns to our customers: we put new products that solve real-world problems into their hands as quickly as possible, and then reinvest the proceeds of our shared learnings immediately back into the product.
It is these sustained investments that allow us to release a flurry of small improvements Continue reading
Soar: Simulation for Observability, reliAbility, and secuRity
Serving more than approximately 25 million Internet properties is not an easy thing, and neither is serving 20 million requests per second on average. At Cloudflare, we achieve this by running a homogeneous edge environment: almost every Cloudflare server runs all Cloudflare products.
As we offer more and more products and enjoy the benefit of horizontal scalability, our edge stack continues to grow in complexity. Originally, we only operated at the application layer with our CDN service and DoS protection. Then we launched transport layer products, such as Spectrum and Argo. Now we have further expanded our footprint into the IP layer and physical link with Magic Transit. They all run on every machine we have. The work of our engineers enables our products to evolve at a fast pace, and to serve our customers better.
However, such software complexity presents a sheer challenge to operation: the more changes you make, the more likely it is that something is going to break. Continue reading
Automation Win: Chatops-Based Security
It’s amazing how quickly you can deploy new functionality once you have a solid foundation in place. In his latest blog post Adrian Giacometti described how he implemented a security solution that allows network operators to block source IP addresses (identified by security tools) across dozens of firewalls using a bot listening to a Slack channel.
Would you be surprised if I told you we covered similar topics in our automation course? ?
Automation Win: Chatops-Based Security
It’s amazing how quickly you can deploy new functionality once you have a solid foundation in place. In his latest blog post Adrian Giacometti described how he implemented a security solution that allows network operators to block source IP addresses (identified by security tools) across dozens of firewalls using a bot listening to a Slack channel.
Would you be surprised if I told you we covered similar topics in our automation course? 😇
Building Backdoors and Fixing Malfeasance

You might have seen the recent news this week that there is an exploitable backdoor in Zyxel hardware that has been discovered and is being exploited. The backdoor admin account with the clever name ‘zyfwp’ is not something that has been present in the devices forever. The account was put in during firmware version 4.60, which was released in Q4 2020.
Zyxel is rushing to patch the devices and remove the backdoor account. Users are being advised to disable remote administration until the accounts can be deactivated and proven to be removed. However, the bigger question in my mind relates to the addition of the user account in the first place. Why would you knowingly install a backdoor?
Hello, Joshua
Backdoors are nothing new in the computer world. I’d argue the most famous backdoor account in the history of computer hacking belongs to Joshua, the dormant login for the War Operations Programmed Response (WOPR) computer system in the 1983 movie Wargames. Joshua was an old login for the creator to access the system outside of the military chain of command. When the developer was removed from the project the account was forgotten about until a kid discovered it and Continue reading
Considerations for Host-based Firewalls (Part 2)
This is a guest blog post by Matthias Luft, Principal Platform Security Engineer @ Salesforce, and a regular ipSpace.net guest speaker.
A couple of months ago I had the pleasure to publish my first guest post here and, as to be expected from ipspace.net, it triggered some great discussion.
With this input and some open thoughts from the last post, I want to dive into a few more topics.
Application Engineering vs. (?) Network Engineering
One trigger for the initial post was the question whether host-based firewalls (HBFs), potentially combined with solutions to learn rulesets based on flows, are intrinsically better than central firewalls. While we discussed the mileage around that already, comments and questions emphasized how often we have to handle a “software engineering vs. network engineering” mentality – which should not involve any blame in either direction as this mindset is usually enforced by organizational structures.
For whatever it is worth, I can only stress the point that a strong collaboration between software and network engineering will resolve way more issues than any technology. I award myself a “Thanks, Captain Obvious” here, but I still want to make the point to try Continue reading
Considerations for Host-based Firewalls (Part 2)
This is a guest blog post by Matthias Luft, Principal Platform Security Engineer @ Salesforce, and a regular ipSpace.net guest speaker.
A couple of months ago I had the pleasure to publish my first guest post here and, as to be expected from ipspace.net, it triggered some great discussion.
With this input and some open thoughts from the last post, I want to dive into a few more topics.
Playing with Python Ransomware
I recently came across the Python script pokus.py which implements a ransomware function. The code is written for demonstration purposes only, so it completely lacks obfuscation techniques. The goal is to identify the vulnerability that is intentionally implemented in the code so we can restore the attached file - private.gif.rsw (the file is compressed by […]Continue reading...
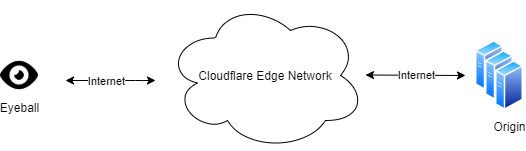
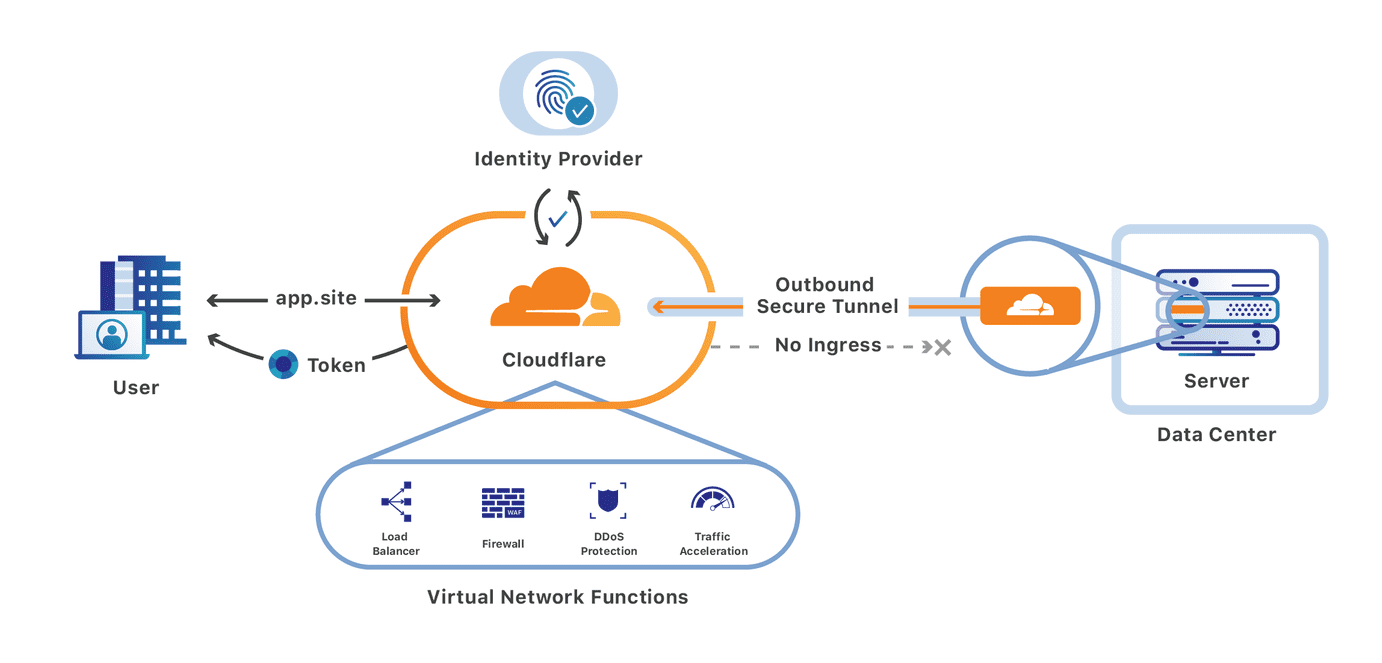
Integrating Cloudflare Gateway and Access
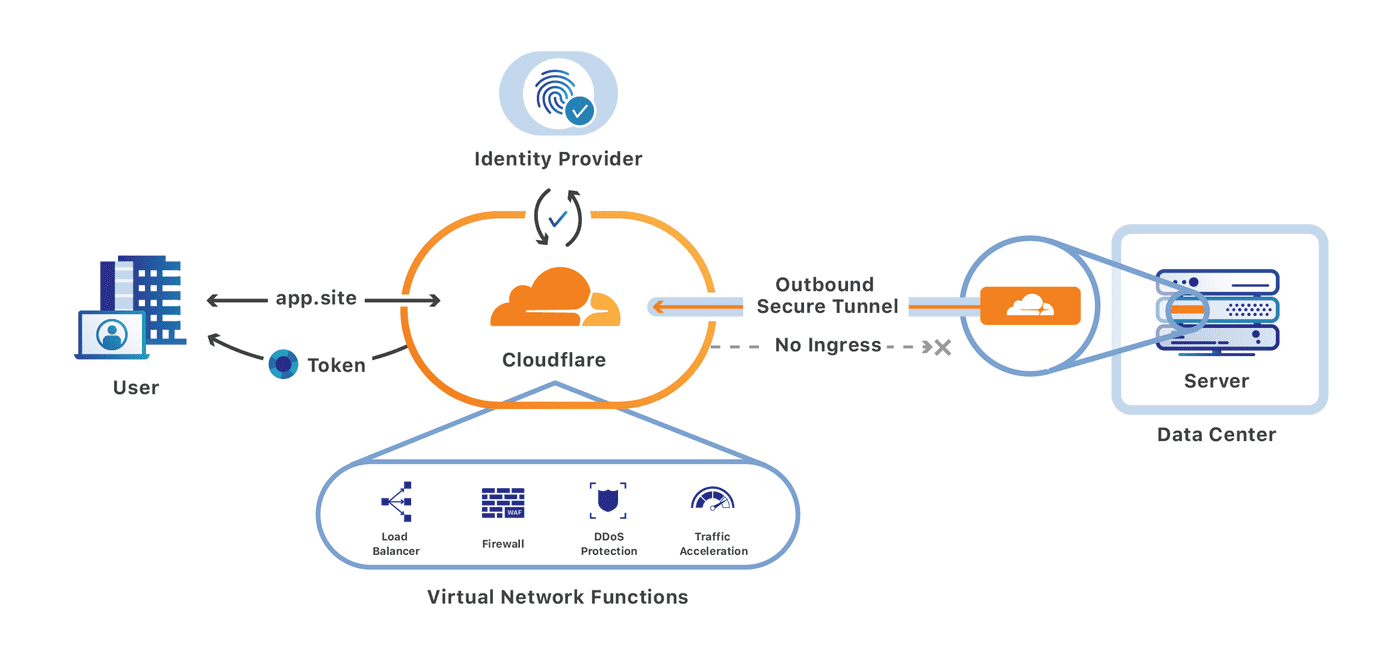
We’re excited to announce that you can now set up your Access policies to require that all user traffic to your application is filtered by Cloudflare Gateway. This ensures that all of the traffic to your self-hosted and SaaS applications is secured and centrally logged. You can also use this integration to build rules that determine which users can connect to certain parts of your SaaS applications, even if the application does not support those rules on its own.
Stop threats from returning to your applications and data
We built Cloudflare Access as an internal project to replace our own VPN. Unlike a traditional private network, Access follows a Zero Trust model. Cloudflare’s edge checks every request to protected resources for identity and other signals like device posture (i.e., information about a user’s machine, like Operating system version, if antivirus is running, etc.).
By deploying Cloudflare Access, our security and IT teams could build granular rules for each application and log every request and event. Cloudflare’s network accelerated how users connected. We launched Access as a product for our customers in 2018 to share those improvements with teams of any size.
Over the last two years, we Continue reading