Watch Out Networking, the Service Mesh Will Rock Your World
 Service meshes could displace many L4-7 networking functions. But will they?
Service meshes could displace many L4-7 networking functions. But will they?
Banking-Grade Credential Stuffing: The Futility of Partial Password Validation

Recently when logging into one of my credit card providers, I was greeted by a familiar screen. After entering in my username, the service asked me to supply 3 random characters from my password to validate ownership of my account.
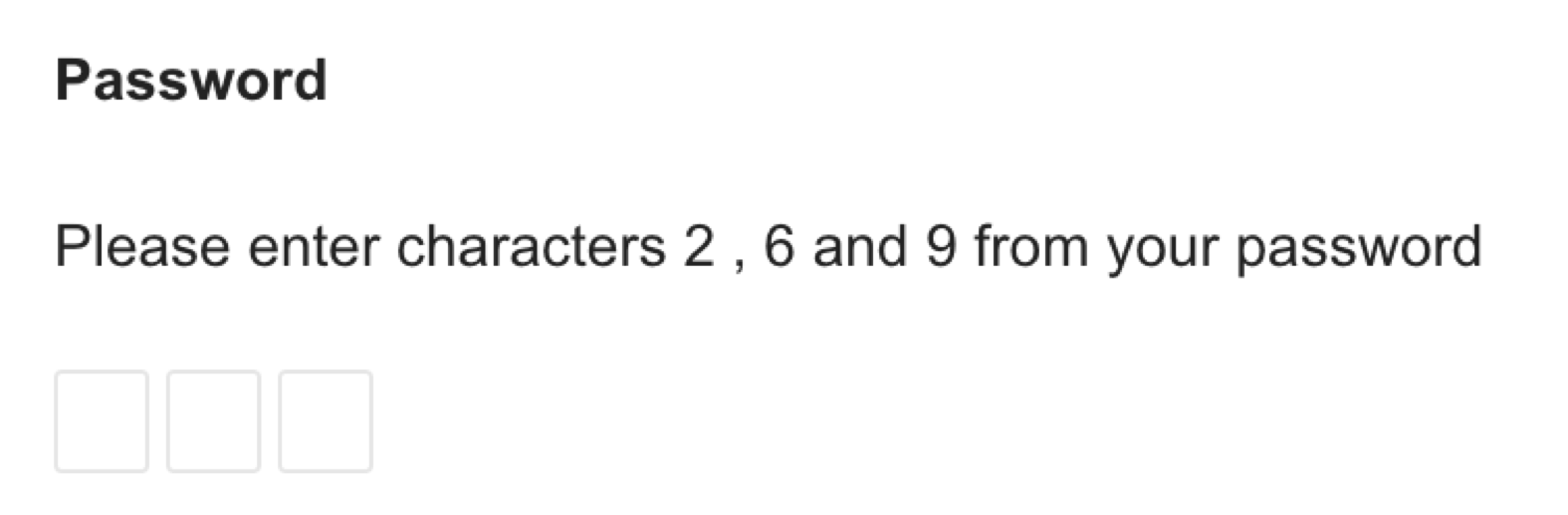
It is increasingly common knowledge in the InfoSec community that this practice is the antithesis of, what we now understand to be, secure password management.
For starters; sites prompting you for Partial Password Validation cannot store your passwords securely using algorithms like BCrypt or Argon2. If the service provider is ever breached, such plain-text passwords can be used to login to other sites where the account holder uses the same password (known as a Credential Stuffing attack).
Increased difficulty using long, randomly-generated passwords from Password Managers, leads to users favouring their memory over securely generated unique passwords. Those using Password Managers must extract their password from their vault, paste it somewhere else and then calculate the correct characters to put in. With this increased complexity, it further incentivises users to (re-)use simple passwords they can remember and count off on their fingers (and likely repeatedly use on other sites).
This is not to distinct thinking that originally bought us complex Continue reading
Ensuring Security Posture In A Multi Cloud World: A NSX(mas) Carol
Holidays are a great time of year to take a moment and reflect. In 2018 at VMware Networking & Security, we’ve had yet another exciting year for us—we’re very proud of many achievements. For example, NSX now being deployed by 82% of Fortune 100 companies is a substantial industry adoption data point. But rather than focus on those numbers, I wanted to take a moment to highlight one of our biggest accomplishments this year (in my opinion). Oh, and in case you missed some of those 2018 highlights, you can catch a replay of Tom Gillis’ keynote Building the Network of the Future with the Virtual Cloud Network from VMWorld US 2018.
NSX Past

Earlier this year (the end of April to be precise), at Dell Technologies World, we had our external launch of the Virtual Cloud Network. The problem statement was simple: our customers were embarking on a digital transformation journey in their respective lines of business and with those efforts came challenges around a new level of networking complexity. Their goal within their organizations was to move from centralized data centers to hyper-distributed centers of applications and data, typically spanning multiple locations, multiple geos, Continue reading
IoT Security Startup Phosphorus Builds Agentless ‘Update-All’ Button
 IoT devices have two types of update mechanisms: an API call or user-initiated update. Phosphorus covers all that with its update-all button for IoT.
IoT devices have two types of update mechanisms: an API call or user-initiated update. Phosphorus covers all that with its update-all button for IoT.
Kubernetes Security Flaw Expected, Won’t Be the Last
 The latest flaw was coincidentally announced on the same day as the latest version of Kubernetes was released. Project members said security concerns do not impact the release cycle.
The latest flaw was coincidentally announced on the same day as the latest version of Kubernetes was released. Project members said security concerns do not impact the release cycle.
T-Mobile and Sprint Get Nod of Approval From U.S. Gov Agencies
 According to reports, the deal was cleared after Deutsche Telekom and SoftBank offered to stop using Huawei equipment.
According to reports, the deal was cleared after Deutsche Telekom and SoftBank offered to stop using Huawei equipment.
CenturyLink Combines Managed Palo Alto Networks Firewalls, Threat Detection, and Visibility
 The managed firewall, integrated with CenturyLink’s Security Log Monitoring platform, gives companies better threat intelligence capabilities and visibility across their hybrid network environments.
The managed firewall, integrated with CenturyLink’s Security Log Monitoring platform, gives companies better threat intelligence capabilities and visibility across their hybrid network environments.
Packet and Netronome Team Up on Microservers Built for Edge Workloads
 The networking-focused hardware is built for the Open19 Foundation infrastructure platform.
The networking-focused hardware is built for the Open19 Foundation infrastructure platform.
Industrial Internet and OpenFog Consortiums Merge to Create Industrial IoT Powerhouse
 The two groups will combine memberships to develop industry guidance and best practices for Industrial IoT as well as fog and edge computing.
The two groups will combine memberships to develop industry guidance and best practices for Industrial IoT as well as fog and edge computing.
VMware Helps Make-a-Wish Foundation Save Millions on IT
 On average, it takes $10,500 for a wish. And the Foundation must balance the need to grant wishes with the need to update its IT infrastructure.
On average, it takes $10,500 for a wish. And the Foundation must balance the need to grant wishes with the need to update its IT infrastructure.
Notes on Build Hardening
I thought I'd comment on a paper about "build safety" in consumer products, describing how software is built to harden it against hackers trying to exploit bugs.What is build safety?
However, C/C++ is "unsafe", and is the most popular language for building stuff that interacts with the network. In other cases, while the language itself may be safe, it'll use underlying infrastructure ("libraries") written in C/C++. When we are talking about hardening builds, making them safe or security, we are talking about C/C++.
Some Random Thoughts From Security Field Day
I’m spending the week in some great company at Security Field Day with awesome people. They’re really making me think about security in some different ways. Between our conversations going to the presentations and the discussions we’re having after hours, I’m starting to see some things that I didn’t notice before.
- Security is a hard thing to get into because it’s so different everywhere. Where everyone just sees one big security community, it is in fact a large collection of small communities. Thinking that there is just one security community would be much more like thinking enterprise networking, wireless networking, and service provider networking are the same space. They may all deal with packets flying across the wires but they are very different under the hood. Security is a lot of various communities with the name in common.
- Security isn’t about tools. It’s not about software or hardware or a product you can buy. It’s about thinking differently. It’s about looking at the world through a different lens. How to protect something. How to attack something. How to figure all of that out. That’s not something you learn from a book or a course. It’s a way of adjusting your Continue reading
VMware Cloud on AWS with NSX-T SDDC – Connectivity, Security, and Port Mirroring Demo
VMware Cloud on AWS with NSX-T SDDC – Networking and Security
Watch the embedded demo below or view on the NSX YouTube channel here to see several cool NSX-T networking and security capabilities within VMware Cloud on AWS. The demo shows connectivity from VMware Cloud on AWS SDDC to on-prem via AWS Direct Connect Private VIF. Access to native AWS services from VMware Cloud on AWS SDDC is also shown. Additionally, Edge security policies, distributed firewall/micro-segmentation, and port mirroring are demonstrated. Continue reading
Webinar: Can Consumers Trust Retailers’ Email? Findings from OTA’s Email Marketing & Unsubscribe Audit

Masergy’s New CEO Is Tasked to Grow Its SDN-Based Offerings
 The company was pretty revolutionary with its idea to layer SDN on top of multiple third-party transport before all the SD-WAN vendors conceived of this.
The company was pretty revolutionary with its idea to layer SDN on top of multiple third-party transport before all the SD-WAN vendors conceived of this.
Comcast Is Working on a uCPE That Runs Multiple VNFs With Its SD-WAN
 The service provider is hoping to launch a cost-effective uCPE platform that supports more VNFs along with its SD-WAN early next year.
The service provider is hoping to launch a cost-effective uCPE platform that supports more VNFs along with its SD-WAN early next year.
DPDK — One API to Rule Them All?
 DPDK has extended its reach beyond packet processing and could be a universal API for other acceleration functions needed for effective NFV.
DPDK has extended its reach beyond packet processing and could be a universal API for other acceleration functions needed for effective NFV.
Napatech and Intel Partner on FPGA Technology for Standard Servers
 The big hyperscalers use field programmable gate array technology on standard servers in their data centers. But there’s a trend for other enterprises to emulate these hyperscalers.
The big hyperscalers use field programmable gate array technology on standard servers in their data centers. But there’s a trend for other enterprises to emulate these hyperscalers.
Notes about hacking with drop tools
In this report, Kasperky found Eastern European banks hacked with Raspberry Pis and "Bash Bunnies" (DarkVishnya). I thought I'd write up some more detailed notes on this.Drop tools
A common hacking/pen-testing technique is to drop a box physically on the local network. On this blog, there are articles going back 10 years discussing this. In the old days, this was done with $200 "netbook" (cheap notebook computers). These days, it can be done with $50 "Raspberry Pi" computers, or even $25 consumer devices reflashed with Linux.A "Raspberry Pi" is a $35 single board computer, for which you'll need to add about another $15 worth of stuff to get it running (power supply, flash drive, and cables). These are extremely popular hobbyist computers that are used everywhere from home servers, robotics, and hacking. They have spawned a large number of clones, like the ODROID, Orange Pi, NanoPi, and so on. With a quad-core, 1.4 GHz, single-issue processor, 2 gigs of RAM, and typically at least 8 gigs of flash, these are pretty powerful computers.
Typically what you'd do is install Kali Linux. This is a Linux "distro" that contains all the tools hackers want to Continue reading
Pivot3 Adds Encryption, Key Management to HCI Stack
 Adding these policy-based security capabilities to the Pivot3 Intelligence Engine enables customers to integrate data encryption and key management into the same workflow for managing applications and storage.
Adding these policy-based security capabilities to the Pivot3 Intelligence Engine enables customers to integrate data encryption and key management into the same workflow for managing applications and storage.
