Seven New Spectre, Meltdown-Type Attacks Discovered
 Intel says not to worry and that the earlier patches it issued address these new security flaws as well as the older hardware bugs.
Intel says not to worry and that the earlier patches it issued address these new security flaws as well as the older hardware bugs.
Riverbed SD-WAN Gets Security, Enterprise-Routing Upgrade
 The vendor integrated SD-WAN, application acceleration, visibility, and security in a single device and says its SD-WAN now has more than 1,000 customers.
The vendor integrated SD-WAN, application acceleration, visibility, and security in a single device and says its SD-WAN now has more than 1,000 customers.
Germany Jumps on Huawei 5G Ban Plans, Says Report
 Government officials want to prevent German telecom operators from using equipment from Chinese firms to construct their 5G networks. This would be similar to moves made by the U.S. and Australia.
Government officials want to prevent German telecom operators from using equipment from Chinese firms to construct their 5G networks. This would be similar to moves made by the U.S. and Australia.
Inspecting Gadgets: Don’t Forget the Asterisk When Buying Smart Devices

As we approach the holiday buying season, excitement is building for all the new IoT gadgets – “smart” everything for the home, fitness/health trackers and a plethora of connected children’s toys. But this excitement should come with a giant asterisk:
* Are these products safe?
We’ve all seen the horror stories – hacked baby monitors, vulnerable door locks, robot vacuums turned into roving surveillance devices and connected toys pulled from shelves.
Clearly these gadgets need further inspection. This week the Internet Society has joined with Consumers International and Mozilla to advocate for a set of five minimum security and privacy standards IoT manufacturers should follow to improve the safety of their products. Mozilla has incorporated these into their evaluation of 70 products in the latest version of Privacy Not Included, their holiday IoT buyer’s guide. More detailed explanations of the guide and evaluation criteria are also available.
These minimum guidelines are great start to improve IoT security and privacy. They are a subset of our IoT Trust Framework, which comprehensively addresses key security, privacy and lifecycle principles that should be incorporated into IoT offerings. Manufacturers can use this list of principles to practice “trust by design,” resellers can Continue reading
Research Brief: Achieving Success in Modern Network Automation
 This new Research Brief from AvidThink is aimed at providing enterprises and service providers with a view of the challenges in modern networking, and detailed strategies on how to overcome them by laying the right foundation for network automation.
This new Research Brief from AvidThink is aimed at providing enterprises and service providers with a view of the challenges in modern networking, and detailed strategies on how to overcome them by laying the right foundation for network automation.
Related Stories
U.S. R&E Community Embraces Routing Security

The Internet Society participated in a Routing Security Workshop that was held during the Internet2 Technology Exchange 2018 on 15 October 2018 in Orlando, United States. The research and education networking community has been one of the key targets of the MANRS initiative that is promoting adoption of best practices to reduce threats to the global routing system, and this community workshop followed on from a previous engagement we had with Internet2 and a number of other R&E networks in the US earlier in the year.
Internet2 interconnects R&E institutes across the United States in conjunction with regional and state networks, so we see them as a key partner in raising awareness of the routing security issues, as well as encouraging the adoption of the four MANRS principles. Indeed, one of the aims of MANRS is for network operator communities to take ownership of this process by generating awareness and disseminating best practices, along with making recommendations for improvement. So this workshop was a fantastic step in this direction.
Another positive step was Internet2 formally becoming a MANRS participant shortly before the workshop, follow in the footsteps of ESnet, CAAREN, KanREN, George Washington University, Indiana University, and DePaul University. WiscNet Continue reading
Real URLs for AMP Cached Content Using Cloudflare Workers
Today, we’re excited to announce our solution for arguably the biggest issue affecting Accelerated Mobile Pages (AMP): the inability to use real origin URLs when serving AMP-cached content. To allow AMP caches to serve content under its origin URL, we implemented HTTP signed exchanges, which extend authenticity and integrity to content cached and served on behalf of a publisher. This logic lives on Cloudflare Workers, meaning that adding HTTP signed exchanges to your content is just a simple Workers application away. Publishers on Cloudflare can now take advantage of AMP performance and have AMP caches serve content with their origin URLs. We're thrilled to use Workers as a core component of this solution.
HTTP signed exchanges are a crucial component of the emerging Web Packaging standard, a set of protocols used to package websites for distribution through optimized delivery systems like Google AMP. This announcement comes just in time for Chrome Dev Summit 2018, where our colleague Rustam Lalkaka spoke about our efforts to advance the Web Packaging standard.
What is Web Packaging and Why Does it Matter?
You may already see the need for Web Packaging on a daily basis. On your smartphone, perhaps you’ve searched for Christmas Continue reading
Latest Security Unicorn Netskope Scores $168.7M Series F
 An IPO is on the horizon but being acquired is not. “We are fiercely independent,” Netskope CEO Sanjay Beri said.
An IPO is on the horizon but being acquired is not. “We are fiercely independent,” Netskope CEO Sanjay Beri said.
Disastrous Cloud Transformation? Change Management Could Be the Answer
 To be successful in the cloud world, there needs to be an organizational shift within companies to encompass both change management and skills management.
To be successful in the cloud world, there needs to be an organizational shift within companies to encompass both change management and skills management.
Cisco Combines SD-WAN and Security, Extends Intent-Based Networking to Wireless
 The new Cisco SD-WAN Security product combines Viptela’s technology with Meraki, Cisco’s cloud-managed IT service and wireless LAN product, plus Cisco security software.
The new Cisco SD-WAN Security product combines Viptela’s technology with Meraki, Cisco’s cloud-managed IT service and wireless LAN product, plus Cisco security software.
We Won’t Save the Internet by Breaking It

On the anniversary of the armistice ending the First World War, more than 40 countries stood together for security online by signing the Paris Call for Trust and Security in Cyberspace. The call, which sets out a list of challenges the world needs to tackle, seems to be promising on paper. From hacking to harming the public core – all of this needs to be addressed. And it needs to be addressed urgently.
Others signed the call too. The Internet Society signed because we believe it is a continuation of calls we have made before. It maintains that solutions to Internet issues must be developed together with other Internet stakeholders – each performing its role, and all working collaboratively.
This approach is what allows the Internet to thrive and is key to the ultimate success of this call. Open, decentralized, and distributed. It’s not the traditional multilateral way of doing things, but it is the Internet way – the only one that can work.
There are real and pressing Internet security concerns. It’s critical that signatories to the call do not imagine they can address the concerns alone. The Internet depends, as a technical fact, on cooperative voluntary action, so Continue reading
Michigan VC Firm Deploys Bigleaf SD-WAN to Its Car Dealerships
 As venture capital firm DP Fox began to migrate its business-critical applications to the cloud it needed a connectivity service that could keep up with its growing portfolio.
As venture capital firm DP Fox began to migrate its business-critical applications to the cloud it needed a connectivity service that could keep up with its growing portfolio.
The rise of multivector DDoS attacks
It's been a while since we last wrote about Layer 3/4 DDoS attacks on this blog. This is a good news - we've been quietly handling the daily onslaught of DDoS attacks. Since our last write-up, a handful of interesting L3/4 attacks have happened. Let's review them.
Gigantic SYN
In April, John tweeted about a gigantic 942Gbps SYN flood:
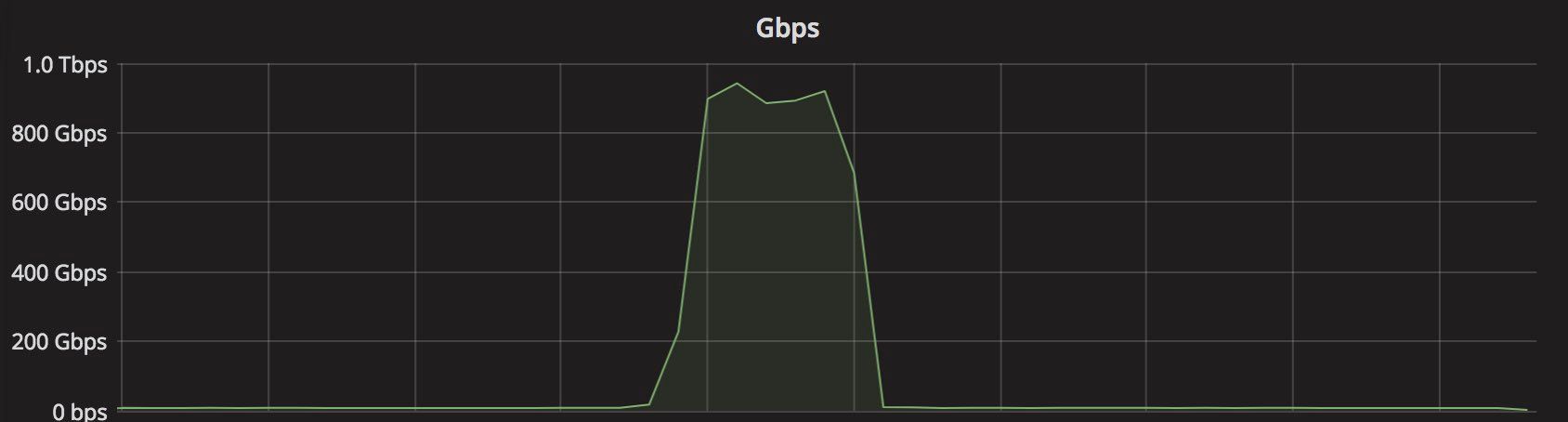
It was a notable event for a couple of reasons.
First, it was really large. Previously, we've seen only amplification / reflection attacks at terabit scale. In those cases, the attacker doesn't actually have too much capacity. They need to bounce the traffic off other servers to generate a substantial load. This is different from typical "direct" style attacks, like SYN floods. In the SYN flood mentioned by John, all 942Gbps were coming directly from attacker-controlled machines.
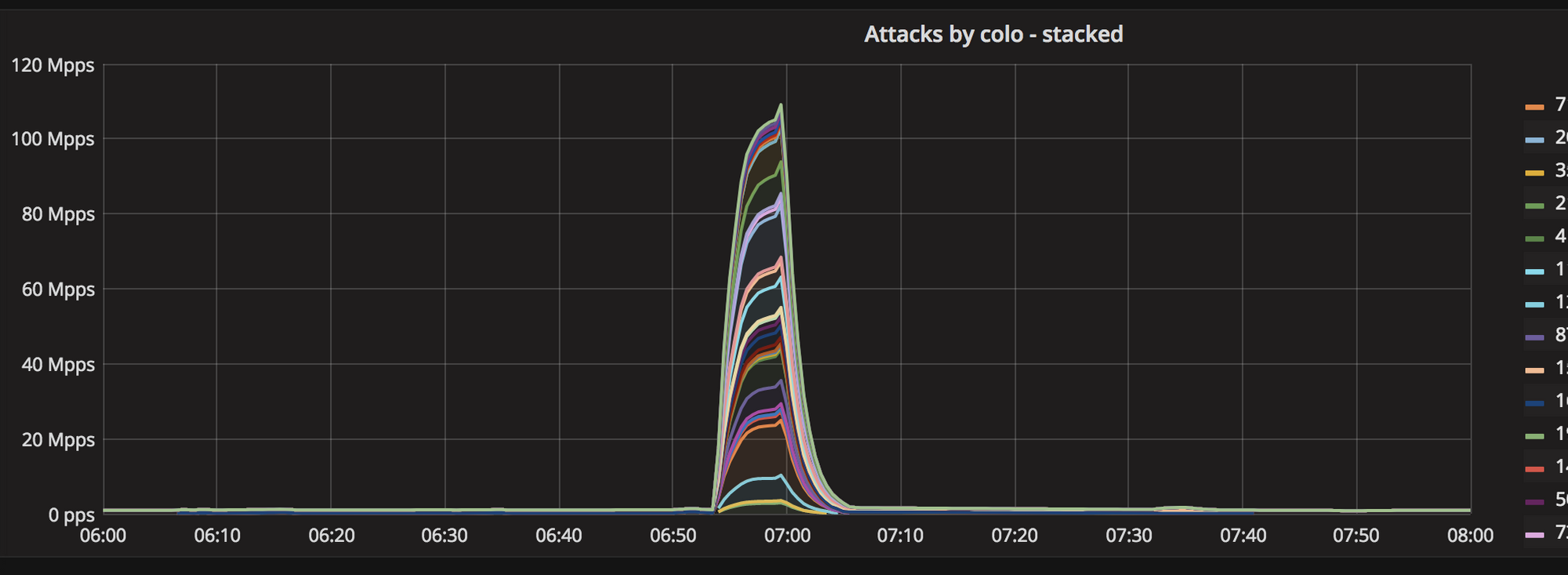
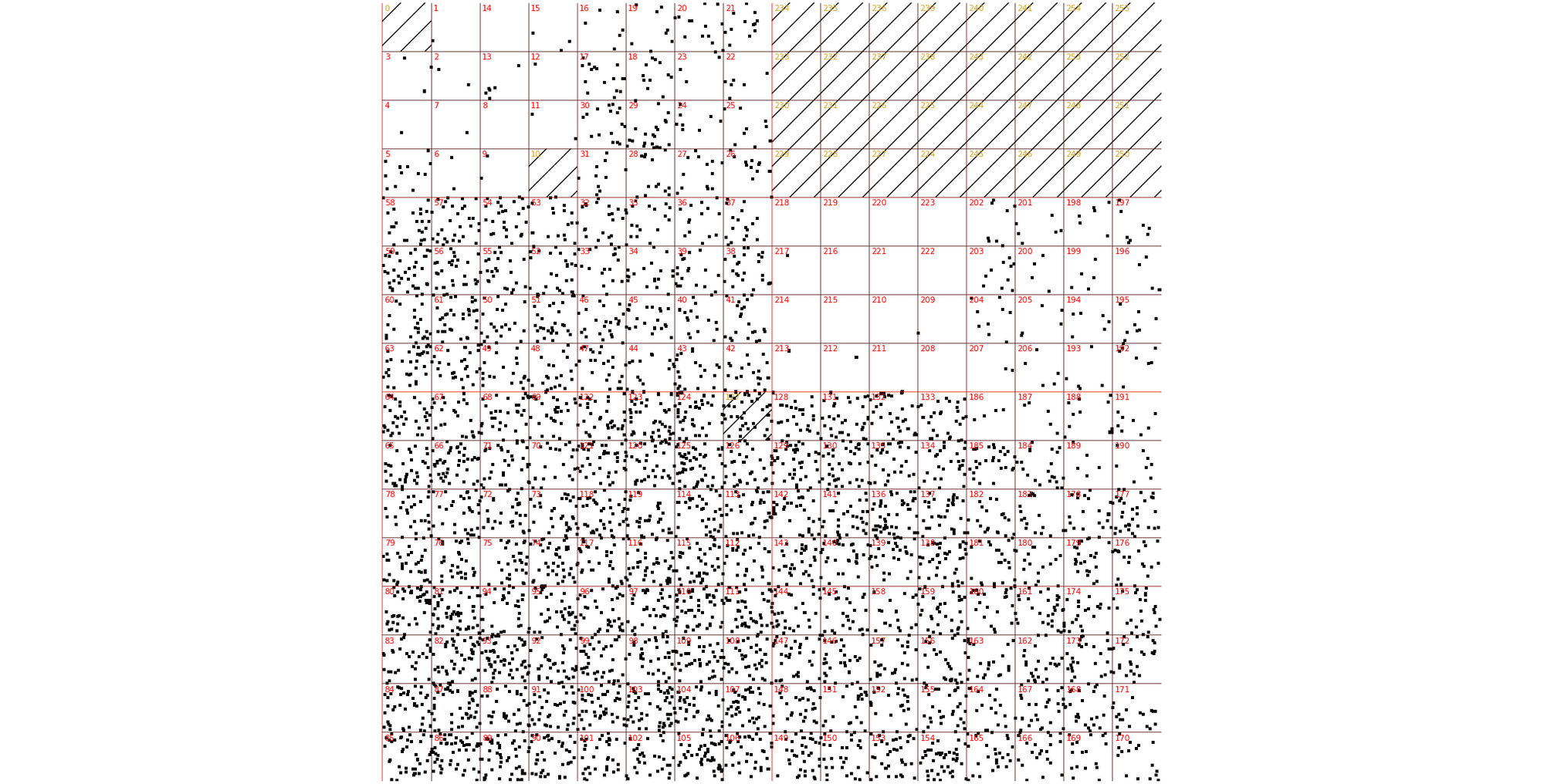
Secondly, this attack was truly distributed. Normal SYN floods come from a small number of geographical locations. This one, was all over the globe, hitting all Cloudflare data centers:
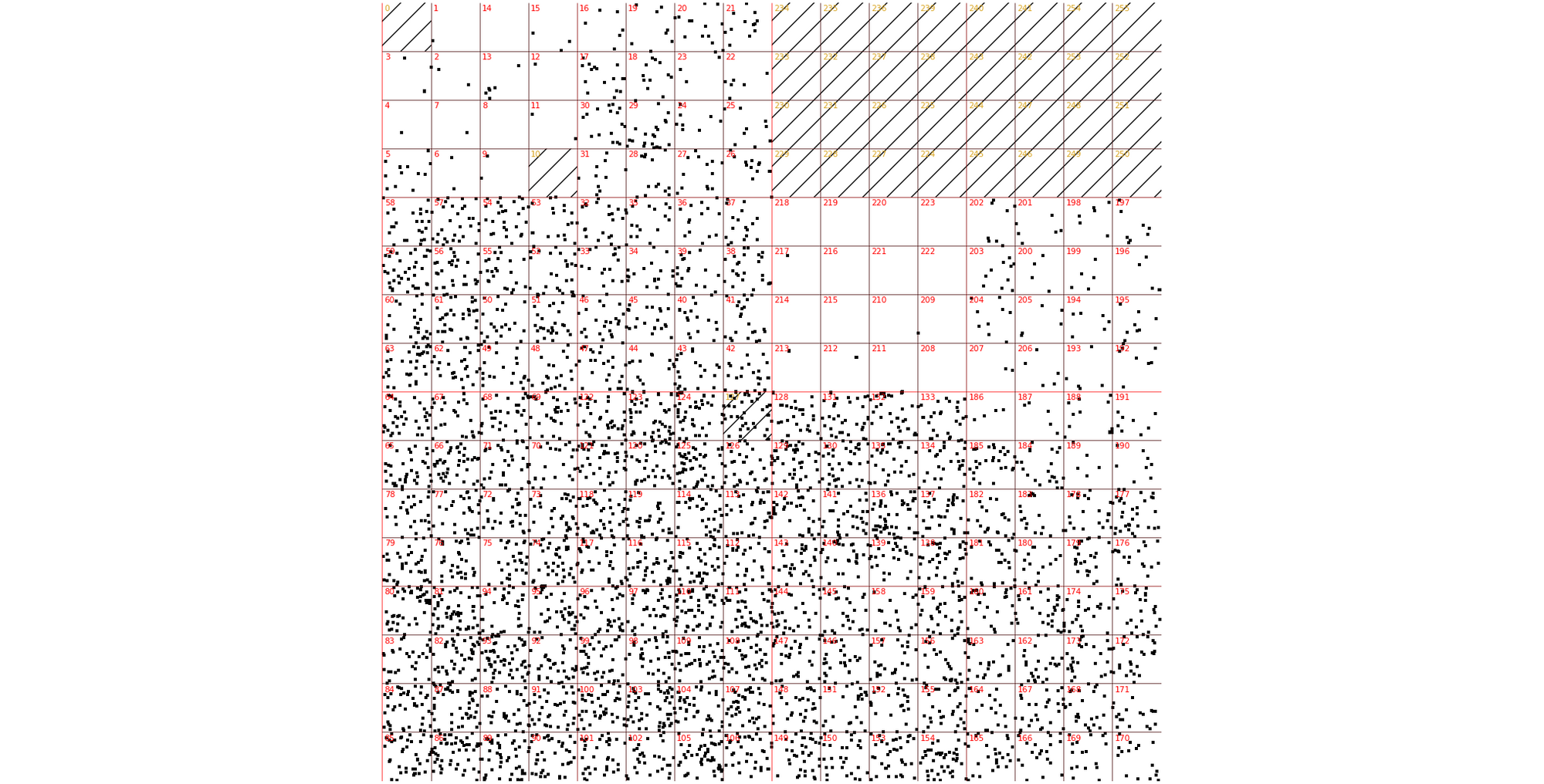
Thirdly, the attack seem to be partially spoofed. While our analysis was not conclusive, we saw random, spoofed source IP addresses in the largest internet exchanges. The above Hilbert curve shows the source IP Continue reading
How Network Automation Increases Security
This blog post was initially sent to subscribers of my SDN and Network Automation mailing list. Subscribe here.
After publishing the Manual Work Is a Bug blog post, I got this feedback from Michele Chubirka explaining why automating changes in your network also increases network security:
Read more ...Global Cybersecurity and the Internet Conundrum

Today marks the 100th anniversary of the armistice that ended the first World War. The 1918 ceasefire re-introduced a fragile peace that had collapsed when the world failed to defend common rules and international cooperation. International security and stability are as important now as they were a century ago.
That’s why French President Emmanuel Macron and leaders from around the world are about to gather in Paris for the first Paris Peace Forum. The forum will attempt to pave a way forward for a world that is shifting and changing faster than most of us can keep up with. That change and shift, and the speed of it is enabled by the Internet.
That is why the Internet Society is participating in the Forum.
I will be in Paris to speak on a panel about creating peace in cyberspace. Cybersecurity concerns across the world are real and justified and need to be addressed. We believe that the collaborative approach that helped to drive the growth of the Internet and allows it to thrive is essential for establishing cybersecurity.
The essence of a collaborative approach is that it allows stakeholders to create a shared vision for security.
The Shared Vision
At the Continue reading
ForeScout Buys SecurityMatters for $113 to Expand Network Protection
 The Netherlands-based startup provides device visibility, continuous network monitoring, and threat and anomaly detection specific to operational technology and industrial environments.
The Netherlands-based startup provides device visibility, continuous network monitoring, and threat and anomaly detection specific to operational technology and industrial environments.
Cisco Continues Kubernetes Kraze With AWS Hybrid Software
 While Cisco adds Kubernetes support across its portfolio, other vendors like VMware and IBM recently bought companies to boost their container cred.
While Cisco adds Kubernetes support across its portfolio, other vendors like VMware and IBM recently bought companies to boost their container cred.
Setting Up Addressing and Routing: FTDv Fun
In my previous blog (Fun in the Lab: FTDv & FMC – Install and Deploy) we deployed a FMC VM and a FTDv VM and ended the blog with the FTDv successfully added to the FMC.
Now? Now let’s add IP addressing for the FTDv and also set up routing protocol neighbor relationships. I learned what I am about to show you from my co-worker and friend, Keith Brister. So don’t thank me, thank Keith. 
I tossed together a ~29 minute YouTube. Obviously you can watch the entire thing. Or… here you go for the big sections.
- Overview – Start to 2:17 minutes
- Physical/Logical Mapping Overview – 2:18 to 9:25
- vSwitches, vmNICs and More in VMware – 9:26 to 16:20
- FTDv Configuring IP Adresses via FMC – 16:21 to 23:18
- FTDv Configuring IP Routing via FMC – 23:19 to 29:29
Done and Done. Easy Peasy!
Research Brief: Evolution of Security in Mobile Networks – Impact of 5G
 This new Research Brief from AvidThink delves into the evolution of the mobile network and explores new threats.
This new Research Brief from AvidThink delves into the evolution of the mobile network and explores new threats.
Related Stories
Fun in the Lab: FTDv & FMC – Install and Deploy
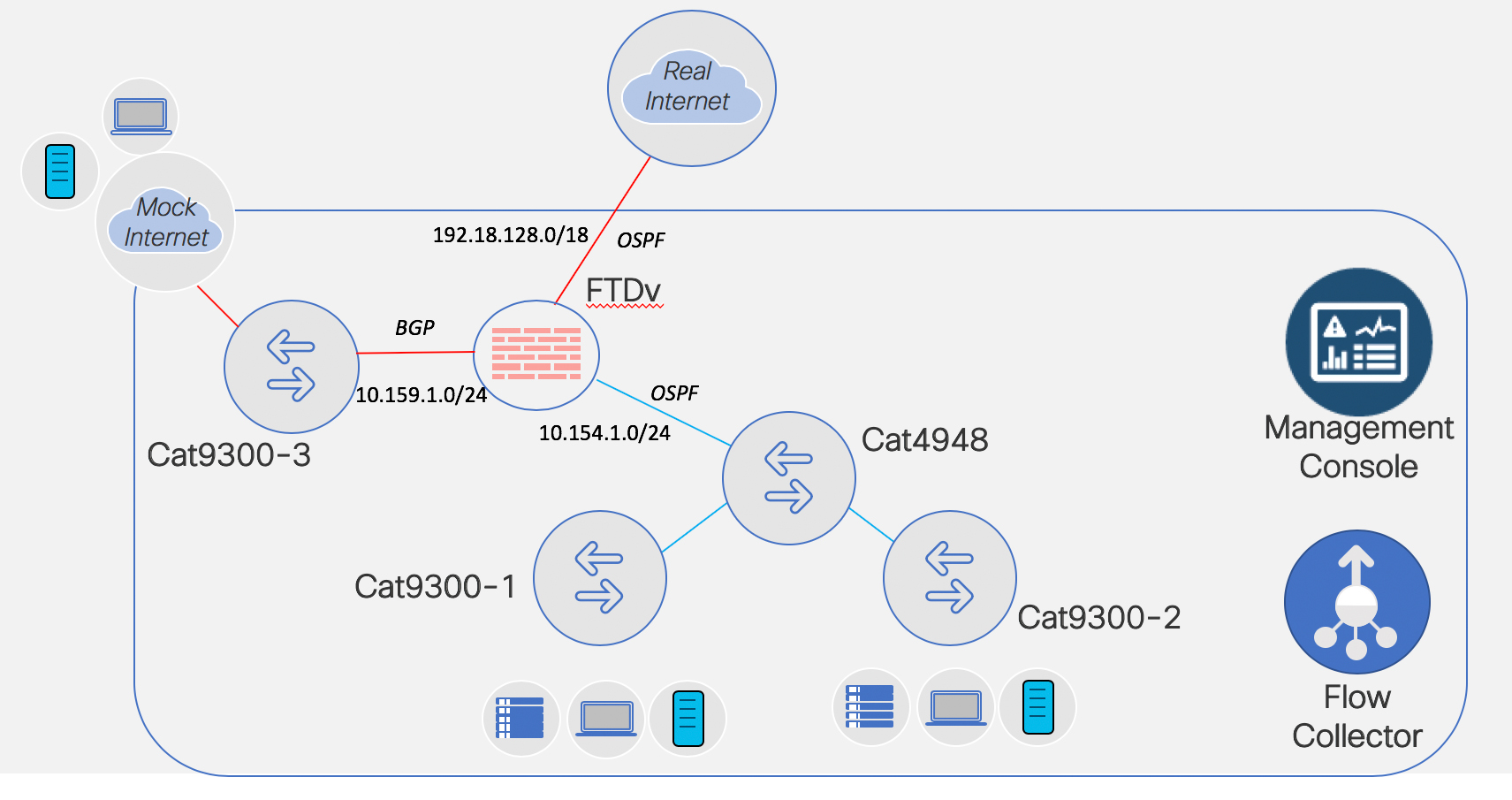
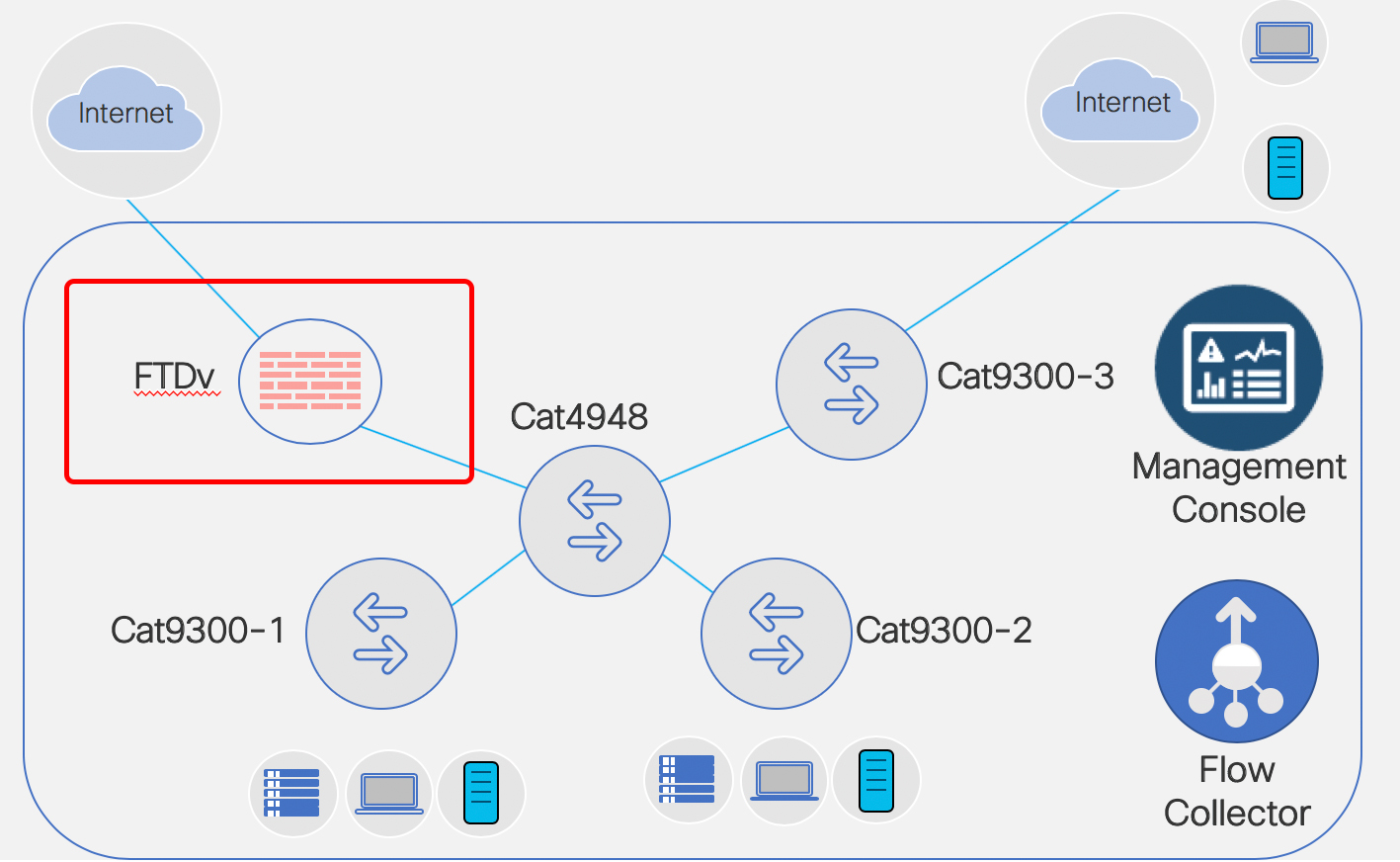
This is my Stealthwatch playground…. errrr… I mean … ahem… “work environment” for a Technical Solution Workshop I am working on for Stealthwatch.
Going to set up FTDv and FMC today. A co-worker and friend, Scott Barasch, helped me get jump started… so figure I’ll pass on what I just learned to you. 
What this blog will cover is
- DEPLOY
- Deploying the OVF for FTDv
- Deploying the OVF for FMC
- VMware settings
- Tweak for FTDv
- Tweak for FMC
- Prepping to Power On
- Snapshot Both Before Power On
- Power Both On
- Setup via Console
- FMC – console in and setup IP address
- FTDv – console in and step thru the prompts
- Test IP Connectivity
- Ping FMC and FTDv from the PC
- Notice Can’t ping FTDv
- Fix
- Ping
- Browse into FMC
- Change password
- Setup DNS
- Setup NTP
- Accept EULA
- Apply
- LICENSING
- License FMC
- FMC/FTDv: Make the Connection
- FTDv – Point FTDv to FMC
- FMC – bring the FTDv into the fold.

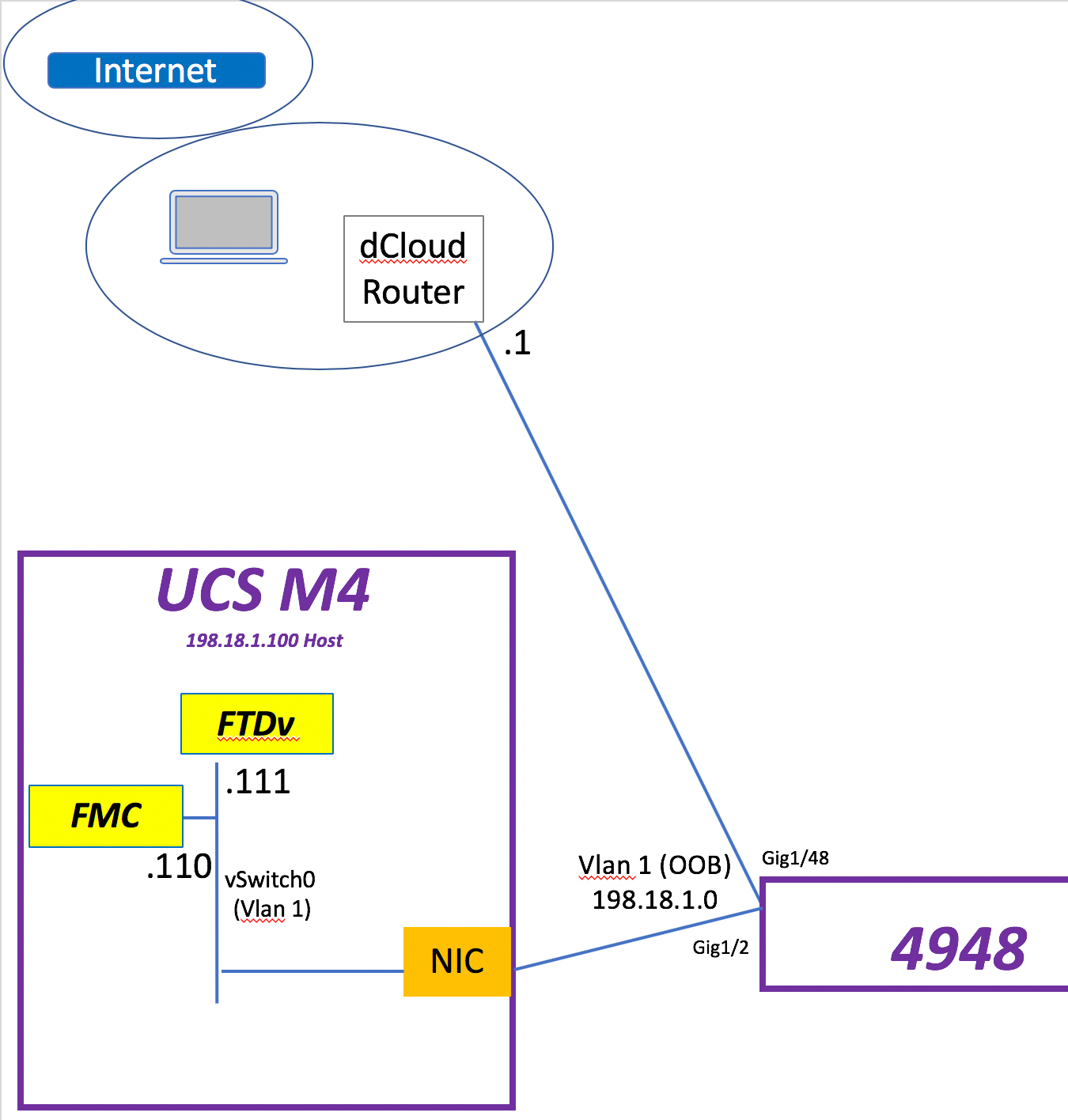
So let’s begin. What I have to host my FMC & FTDv VMs is a UCS M4 with a NIC connected to a Cat4948 in vlan 1. That NIC is tied to vSwitch0 in the UCS. Continue reading