GitLab Gets $100M Series D, Hits $1B Valuation
 The software repository used the news to take a swipe at rival GitHub, which Microsoft purchased for $7.5 billion.
The software repository used the news to take a swipe at rival GitHub, which Microsoft purchased for $7.5 billion.
Roughtime: Securing Time with Digital Signatures

When you visit a secure website, it offers you a TLS certificate that asserts its identity. Every certificate has an expiration date, and when it’s passed due, it is no longer valid. The idea is almost as old as the web itself: limiting the lifetime of certificates is meant to reduce the risk in case a TLS server’s secret key is compromised.
Certificates aren’t the only cryptographic artifacts that expire. When you visit a site protected by Cloudflare, we also tell you whether its certificate has been revoked (see our blog post on OCSP stapling) — for example, due to the secret key being compromised — and this value (a so-called OCSP staple) has an expiration date, too.
Thus, to determine if a certificate is valid and hasn’t been revoked, your system needs to know the current time. Indeed, time is crucial for the security of TLS and myriad other protocols. To help keep clocks in sync, we are announcing a free, high-availability, and low-latency authenticated time service called Roughtime, available at roughtime.cloudlare.com on port 2002.
Time is tricky
It may surprise you to learn that, in practice, clients’ clocks are heavily skewed. A recent study of Continue reading
Can NFV Help in Rolling Out DDoS Mitigation Services?
 Moving the security perimeter into the cloud helps companies that are struggling with the budget and talent needed to keep security in-house.
Moving the security perimeter into the cloud helps companies that are struggling with the budget and talent needed to keep security in-house.
Introducing the Cloudflare Onion Service
- When: a cold San Francisco summer afternoon
- Where: Room 305, Cloudflare
- Who: 2 from Cloudflare + 9 from the Tor Project
What could go wrong?
Bit of Background
Two years ago this week Cloudflare introduced Opportunistic Encryption, a feature that provided additional security and performance benefits to websites that had not yet moved to HTTPS. Indeed, back in the old days some websites only used HTTP --- weird, right? “Opportunistic” here meant that the server advertised support for HTTP/2 via an HTTP Alternative Service header in the hopes that any browser that recognized the protocol could take advantage of those benefits in subsequent requests to that domain.
Around the same time, CEO Matthew Prince wrote about the importance and challenges of privacy on the Internet and tasked us to find a solution that provides convenience, security, and anonymity.
From neutralizing fingerprinting vectors and everyday browser trackers that Privacy Badger feeds on, all the way to mitigating correlation attacks that only big actors are capable of, guaranteeing privacy is a complicated challenge. Fortunately, the Tor Project addresses this extensive adversary model in Tor Browser.
However, the Internet is full of bad actors, and distinguishing Continue reading
How do you explain the unreasonable effectiveness of cloud security?
With the enormous attack surface of cloud providers like AWS, Azure, and GCP, why aren't there more security problems? Data breaches and cyber attacks occur daily. How do you explain the unreasonable effectiveness of cloud security?
Google has an ebook on their security approach; Microsoft has some web pages. Both are the equivalent of that person who is disgustingly healthy and you ask them how they do it and they say "I don't know. I just eat right, exercise, and get plenty of sleep." Not all that useful. Most of us want a hack, a trick to good health. Who wants to eat right?
I'm sure Amazon also eats right, exercises, and gets plenty of sleep (probably not the people who work there), but AWS also has a secret that when that disgustingly healthy person starts talking about at a party, you just can't help leaning in and listening.
What's the trick to 6-pack security? Proving systems correct. Does your datacenter do that? I didn't think so. AWS does.
Dr. Byron Cook gave an enthusiastic talk on Formal Reasoning about the Security of Amazon Web Service. He's clearly excited about finally applying his research in a Continue reading
Trump and Peekaboo: Hackers Target Political Malware, Surveillance Software
 McAfee says Presidents Trump and Obama have malware campaigns named after them. Tenable discloses a flaw that could affect hundreds of thousands of security cameras globally.
McAfee says Presidents Trump and Obama have malware campaigns named after them. Tenable discloses a flaw that could affect hundreds of thousands of security cameras globally.
RPKI and BGP: our path to securing Internet Routing


This article will talk about our approach to network security using technologies like RPKI to sign Internet routes and protect our users and customers from route hijacks and misconfigurations. We are proud to announce we have started deploying active filtering by using RPKI for routing decisions and signing our routes.
Back in April, articles including our blog post on BGP and route-leaks were reported in the news, highlighting how IP addresses can be redirected maliciously or by mistake. While enormous, the underlying routing infrastructure, the bedrock of the Internet, has remained mostly unsecured.
At Cloudflare, we decided to secure our part of the Internet by protecting our customers and everyone using our services including our recursive resolver 1.1.1.1.
From BGP to RPKI, how do we Internet ?
A prefix is a range of IP addresses, for instance, 10.0.0.0/24, whose first address is 10.0.0.0 and the last one is 10.0.0.255. A computer or a server usually have one. A router creates a list of reachable prefixes called a routing table and uses this routing table to transport packets from a source to a destination.
On the Internet, network Continue reading
RPKI – The required cryptographic upgrade to BGP routing

We have talked about the BGP Internet routing protocol before. We have talked about how we build a more resilient network and how we can see outages at a country-level via BGP. We have even talked about the network community that is vital to the operation of the global Internet.
Today we need to talk about why existing operational practices for BGP routing and filtering have to significantly improve in order to finally stop route leaks and hijacks; which are sadly pervasive in today’s Internet routing world. In fact, the subtle art of running a BGP network and the various tools (both online and within your a networks subsystems) that are vital to making the Internet routing world a safe and reliable place to operate need to improve.
Internet routing and BGP and security along with its operational expertise must improve globally.

Nothing specific triggered today’s writing except the fact that Cloudflare has decided that it's high-time we took a leadership role to finally secure BGP routing. We believe that each and every network needs to change its mindset towards BGP security both on a day-by-day and a long-term basis.
It's time to stop Continue reading
VMware NSX-T Data Center in Evaluation for Common Criteria EAL4+ Certification
VMware NSX-T Data Center 2.x is now under evaluation for Common Criteria certification at Evaluation Assurance Level 4+ with BSI, Germany’s Federal Office for Information Security. Common Criteria is an internationally recognized standard (ISO-15408) that defines, validates, and assures security features and capabilities of IT security products. To see the evaluation status for VMware NSX-T 2.x, visit the German BSI certification website and reference certificate # BSI-DSZ-CC-1099.
VMware NSX-T was introduced to help organizations meet the stringent security demands of containerized workloads, multi-hypervisor, and multi-cloud. And this latest milestone for NSX-T 2.x reinforces VMware’s continuing commitment to deliver secure software to our customers. During the Common Criteria certification process, VMware NSX-T will undergo a thorough and rigorous evaluation methodology, with testing performed by a commercial Common Criteria Evaluation Facility under the oversight of the Certification Body. The Common Criteria certification acts as a seal of assurance for the federal government, its agencies, contractors and other organizations and assures that the product complies with strict security requirements specified within the designated level.
Within the VMware NSX portfolio, we have a long history of investing in certification efforts. For example, VMware NSX Data Center for vSphere 6.x also Continue reading
Intel’s Growing Chip Portfolio Stretches From Cloud to Edge
 Intel may be best known for its x86 server chips, but its growing silicon portfolio targets cloud and edge applications, as well as 5G.
Intel may be best known for its x86 server chips, but its growing silicon portfolio targets cloud and edge applications, as well as 5G.
ARM Supports Chip Makers in Servers, IoT, and 5G
 Instead of manufacturing chips, ARM provides its instruction set architecture to its customers — such as Qualcomm, Broadcom, NXP, and Marvell — and those companies manufacture the chips.
Instead of manufacturing chips, ARM provides its instruction set architecture to its customers — such as Qualcomm, Broadcom, NXP, and Marvell — and those companies manufacture the chips.
Interconnection Bandwidth Skyrockets With 5G as an ‘Amplifier,’ Equinix Says
 SDN and NFV are contributing to the growth of interconnection because these technologies make it easier for customers to consume more bandwidth.
SDN and NFV are contributing to the growth of interconnection because these technologies make it easier for customers to consume more bandwidth.
Solving Container Security Requires New Tools and Processes
 This eBrief from SDxCentral delves into the latest developments in container security and looks at the techniques companies are using to ensure their container environments are secure and not vulnerable to breaches.
This eBrief from SDxCentral delves into the latest developments in container security and looks at the techniques companies are using to ensure their container environments are secure and not vulnerable to breaches.
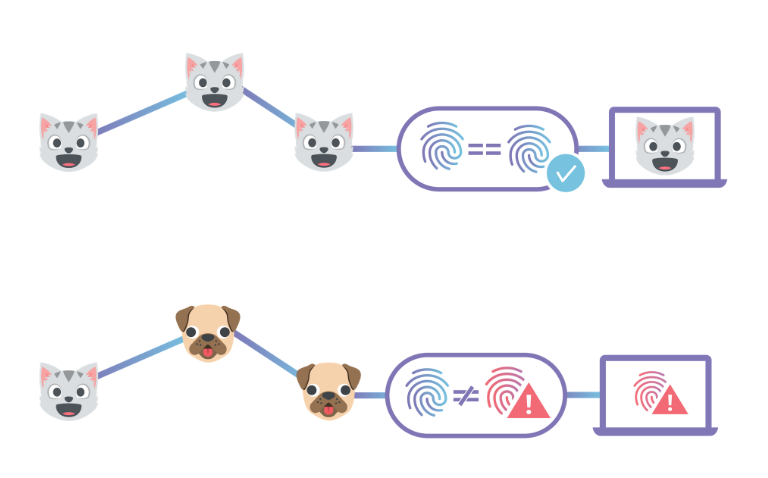
Expanding DNSSEC Adoption


Cloudflare first started talking about DNSSEC in 2014 and at the time, Nick Sullivan wrote: “DNSSEC is a valuable tool for improving the trust and integrity of DNS, the backbone of the modern Internet.”
Over the past four years, it has become an even more critical part of securing the internet. While HTTPS has gone a long way in preventing user sessions from being hijacked and maliciously (or innocuously) redirected, not all internet traffic is HTTPS. A safer Internet should secure every possible layer between a user and the origin they are intending to visit.
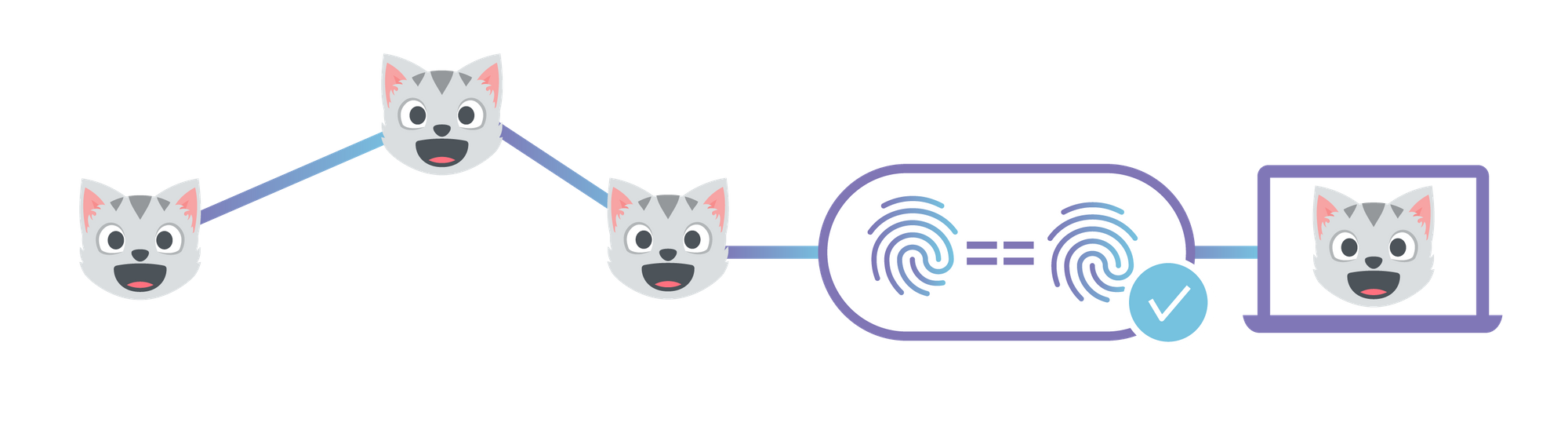
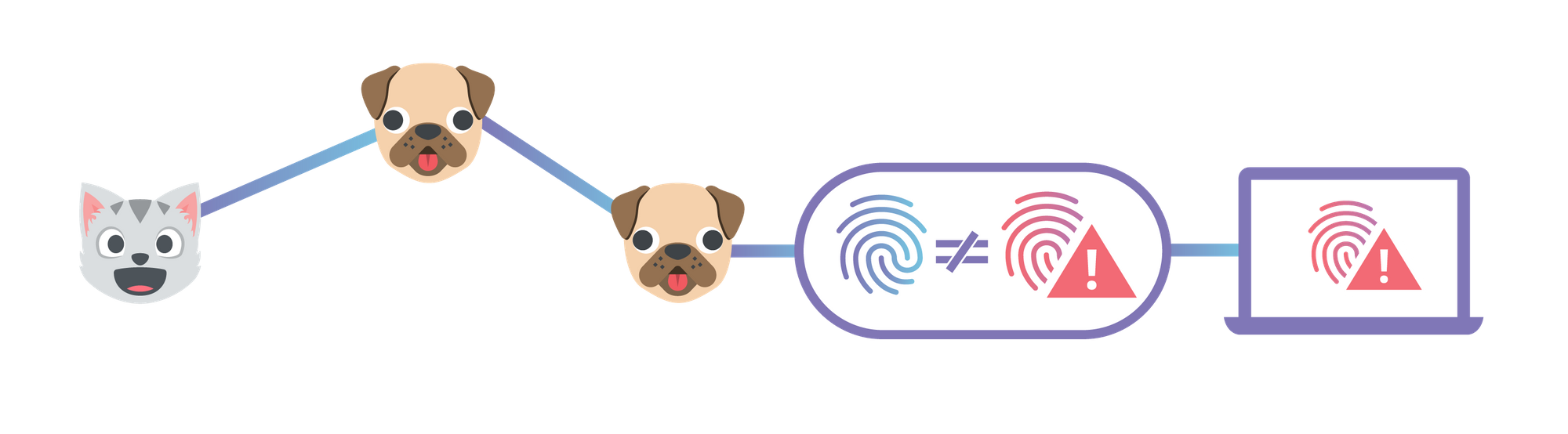
As a quick refresher, DNSSEC allows a user, application, or recursive resolver to trust that the answer to their DNS query is what the domain owner intends it to be. Put another way: DNSSEC proves authenticity and integrity (though not confidentiality) of a response from the authoritative nameserver. Doing so makes it much harder for a bad actor to inject malicious DNS records into the resolution path through BGP Leaks and cache poisoning. Trust in DNS matters even more when a domain is publishing record types that are used to declare trust for other systems. As a specific example, DNSSEC is helpful for preventing Continue reading
Juniper Brings Contrail to the Edge, Works Closely With Red Hat
 Distributed computing with Red Hat OpenStack Platform allows the Contrail Edge Cloud to remotely manage the lifecycle of compute nodes and virtual machines (VMs) from a centralized data center without requiring co-located OpenStack control plane functions in each of these remote edge sites.
Distributed computing with Red Hat OpenStack Platform allows the Contrail Edge Cloud to remotely manage the lifecycle of compute nodes and virtual machines (VMs) from a centralized data center without requiring co-located OpenStack control plane functions in each of these remote edge sites.
End-to-End Integrity with IPFS
This post describes how to use Cloudflare's IPFS gateway to set up a website which is end-to-end secure, while maintaining the performance and reliability benefits of being served from Cloudflare’s edge network. If you'd rather read an introduction to the concepts behind IPFS first, you can find that in our announcement. Alternatively, you could skip straight to the developer docs to learn how to set up your own website.
By 'end-to-end security', I mean that neither the site owner nor users have to trust Cloudflare to serve the correct documents, like they do now. This is similar to how using HTTPS means you don't have to trust your ISP to not modify or inspect traffic.
CNAME Setup with Universal SSL
The first step is to choose a domain name for your website. Websites should be given their own domain name, rather than served directly from the gateway by root hash, so that they are considered a distinct origin by the browser. This is primarily to prevent cache poisoning, but there are several functional advantages as well. It gives websites their own instance of localStorage and their own cookie jar which are sandboxed from inspection and manipulation by malicious third-party documents. Continue reading
Cloudflare goes InterPlanetary – Introducing Cloudflare’s IPFS Gateway


Today we’re excited to introduce Cloudflare’s IPFS Gateway, an easy way to access content from the InterPlanetary File System (IPFS) that doesn’t require installing and running any special software on your computer. We hope that our gateway, hosted at cloudflare-ipfs.com, will serve as the platform for many new highly-reliable and security-enhanced web applications. The IPFS Gateway is the first product to be released as part of our Distributed Web Gateway project, which will eventually encompass all of our efforts to support new distributed web technologies.
This post will provide a brief introduction to IPFS. We’ve also written an accompanying blog post describing what we’ve built on top of our gateway, as well as documentation on how to serve your own content through our gateway with your own custom hostname.
Quick Primer on IPFS
Usually, when you access a website from your browser, your browser tracks down the origin server (or servers) that are the ultimate, centralized repository for the website’s content. It then sends a request from your computer to that origin server, wherever it is in the world, and that server sends the content back to your computer. This system has served the Internet well for decades, Continue reading
Welcome to Crypto Week


The Internet is an amazing invention. We marvel at how it connects people, connects ideas, and makes the world smaller. But the Internet isn’t perfect. It was put together piecemeal through publicly funded research, private investment, and organic growth that has left us with an imperfect tapestry. It’s also evolving. People are constantly developing creative applications and finding new uses for existing Internet technology. Issues like privacy and security that were afterthoughts in the early days of the Internet are now supremely important. People are being tracked and monetized, websites and web services are being attacked in interesting new ways, and the fundamental system of trust the Internet is built on is showing signs of age. The Internet needs an upgrade, and one of the tools that can make things better, is cryptography.
Every day this week, Cloudflare will be announcing support for a new technology that uses cryptography to make the Internet better. Everything we are announcing this week is free to use and provides a meaningful step towards supporting a new capability or structural reinforcement. So why are we doing this? Because it’s good for the users and good for the Internet. Welcome to Crypto Week!
A more Continue reading
Trading Off Security And Performance Thanks To Spectre And Meltdown
The revelations by Google’s Project Zero team earlier this year of the Spectre and Meltdown speculative execution vulnerabilities in most of processors that have powered servers and PCs for the past couple of decades shook the industry as Intel and other chip makers scrambled to mitigate the risk of the threats in the short term and then implement plans to incorporate the mitigation techniques into future versions of the silicon. …
Trading Off Security And Performance Thanks To Spectre And Meltdown was written by Jeffrey Burt at .
From Idea to Action: Beyond the Net Selects 15 Amazing Chapter Projects!

The Beyond the Net Funding Programme is pleased to announce the results of our 2018 Grant Cycle. A total of 49 applications were received, and after a thorough reviewing process, 15 amazing projects were selected.
These projects are at the core of our mission, and will use the Internet to develop Community Networks in underserved areas, to empower women through ICT, as well as bringing awareness on Internet policies around the world.
This is the result of months of effort from our Chapter Community. Many discussions, numerous clarifications and proposals, updates, and revisions form the Beyond the Net Selection Committee. We are proud of you all.
Please join us in celebrating the following projects!
Developing community networks in the Northern region of Brazil – Brazil Chapter
Supporting and promoting the development of the Internet to enrich people’s lives, the project aim is to contribute to the growth and improvement of community networks policies and practices in Brazilian rural areas, in order to strengthen those who are marginalized. Instituto Nupef will work to develop a new network in the state of Maranhão as well as a developing a communications plan for the Babassu coconut breakers organizations and movements. Objectives include Continue reading