Australia Bans Carriers from Using Huawei and ZTE Equipment for 5G
 The government argues that 5G blurs the line between the core network and the edge network, making security more challenging.
The government argues that 5G blurs the line between the core network and the edge network, making security more challenging.
Announcing the Online Trust Audit & Honor Roll Methodology for 2018
The Online Trust Alliance (OTA) is an Internet Society initiative that aims to enhance online trust, user empowerment, and innovation through convening multistakeholder initiatives and developing and promoting best practices, ethical privacy practices, and data stewardship. One of OTA’s major activities is the Online Trust Audit & Honor Roll, which promotes responsible online privacy and data security practices and recognizes leaders in the public and private sectors who have embraced them. This morning, we released the methodology we’ll use for this year’s audit.
The report will analyze more than 1,000 websites on consumer protection, site security, and responsible privacy practices. Based on a composite weighted analysis, sites that score 80 percent or better overall, without failing in any one category, will be recognized in the Honor Roll.
Building largely on past criteria, this year’s updates include GDPR compliance and other security and privacy standards and practices, as well as adding a healthcare sector. From the press release:
Key changes to this year’s Audit include:
- Consumer Protection (email authentication, domain security and anti-phishing technologies) – more granular assessment of Domain-based Message Authentication, Reporting and Conformance (DMARC) support, and increased weight for use of opportunistic Transport Layer Security (TLS), which Continue reading
There’s a Techlash. The G20 Should Listen.
The Internet is at risk. Once thought of as the global equalizer, opening doors for communication, work opportunities, commerce and more – the Internet is now increasingly viewed with skepticism and wariness. We are witnessing a trend where people fare feeling let down by the technology they use. Fueled by unease and uncertainty about the growing scope of threats to security and privacy that come with an always-on, tech-driven world, people are now looking for ways to disconnect and are placing greater emphasis on values and human interaction.
The way we live our lives is now inextricably linked to the Internet – which is estimated to contribute US$6.6 trillion a year, or 7.1 percent of total GDP in the G20 countries by 2020. In developing nations, that digital economy is growing steadily by 15 to 25 percent a year. Yet the Internet essentially is under attack. Large scale data breaches, uncertainties about how our data is being used and monetized, cybercrime, surveillance and other online threats are impacting Internet users’ trust. We are at an important crossroads for the Internet and its healthy development is at stake.
It is our collective duty to find a response to the Continue reading
Enabling SDN Based Multi-Access Edge Computing Systems
 While MEC is set to address the data demand of 5G networks, adding network programmability to MEC ameliorates the overall MEC solution.
While MEC is set to address the data demand of 5G networks, adding network programmability to MEC ameliorates the overall MEC solution.
Cisco Talos Smells a RAT
 The company selling the software claims it will only sell it for legal uses. But the RAT gives buyers everything they need to build a botnet.
The company selling the software claims it will only sell it for legal uses. But the RAT gives buyers everything they need to build a botnet.
Getting To The Root Of Security With Trusted Silicon
The increasingly distributed nature of computing and the rapid growth in the number of the small connected devices that make up the Internet of Things (IoT) are combining with trends like the rise of silicon-level vulnerabilities highlighted by Spectre, Meltdown, and more recent variants to create an expanding and fluid security landscape that’s difficult for enterprises to navigate. …
Getting To The Root Of Security With Trusted Silicon was written by Jeffrey Burt at .
Cohesity’s Helios Uses Machine Learning to Manage Secondary Data
 The cloud service gives companies visibility and mobility across all of their secondary data and applications from a single dashboard. It also uses machine learning and analytics to power a bunch of new infrastructure management features.
The cloud service gives companies visibility and mobility across all of their secondary data and applications from a single dashboard. It also uses machine learning and analytics to power a bunch of new infrastructure management features.
Foundries.io Tightens Edge, IoT Integration to Boost Security
 The firm sees constant and long-term updates as key to maintaining edge and IoT security.
The firm sees constant and long-term updates as key to maintaining edge and IoT security.
Arista Taps VMware, Zscaler to Create Consistent Cloud Security
 VMware’s software will bring common security policy enforcement to virtual and physical workloads. Zscaler brings its north-south traffic security.
VMware’s software will bring common security policy enforcement to virtual and physical workloads. Zscaler brings its north-south traffic security.
Microsoft Foils Russian Security Threat, Seizes Fake Political Websites
 Microsoft said it has used this approach 12 times in two years to shut down 84 fake websites associated with the state-sponsored hacking group called Fancy Bear.
Microsoft said it has used this approach 12 times in two years to shut down 84 fake websites associated with the state-sponsored hacking group called Fancy Bear.
DeGrasse Tyson: Make Truth Great Again
Neil deGrasse Tyson tweets the following:I’m okay with a US Space Force. But what we need most is a Truth Force — one that defends against all enemies of accurate information, both foreign & domestic.— Neil deGrasse Tyson (@neiltyson) August 20, 2018
A good start: The National Academy of Sciences, which “…provides objective, science-based advice on critical issues affecting the nation."— Neil deGrasse Tyson (@neiltyson) August 20, 2018
Truth vs. "Truth"
Securing The Server, Inside And Out
Computing is hard enough, but the sophistication and proliferation of attacks on IT infrastructure, from the firewall moat surrounding the corporate network all the way down into the guts of the operating system kernel and deep into the speculative execution units on the physical processor, make the task of computing – with confidence – doubly difficult. …
Securing The Server, Inside And Out was written by Timothy Prickett Morgan at .
How Cloudflare protects customers from cache poisoning
A few days ago, Cloudflare — along with the rest of the world — learned of a "practical" cache poisoning attack. In this post I’ll walk through the attack and explain how Cloudflare mitigated it for our customers. While any web cache is vulnerable to this attack, Cloudflare is uniquely able to take proactive steps to defend millions of customers.
In addition to the steps we’ve taken, we strongly recommend that customers update their origin web servers to mitigate vulnerabilities. Some popular vendors have applied patches that can be installed right away, including Drupal, Symfony, and Zend.
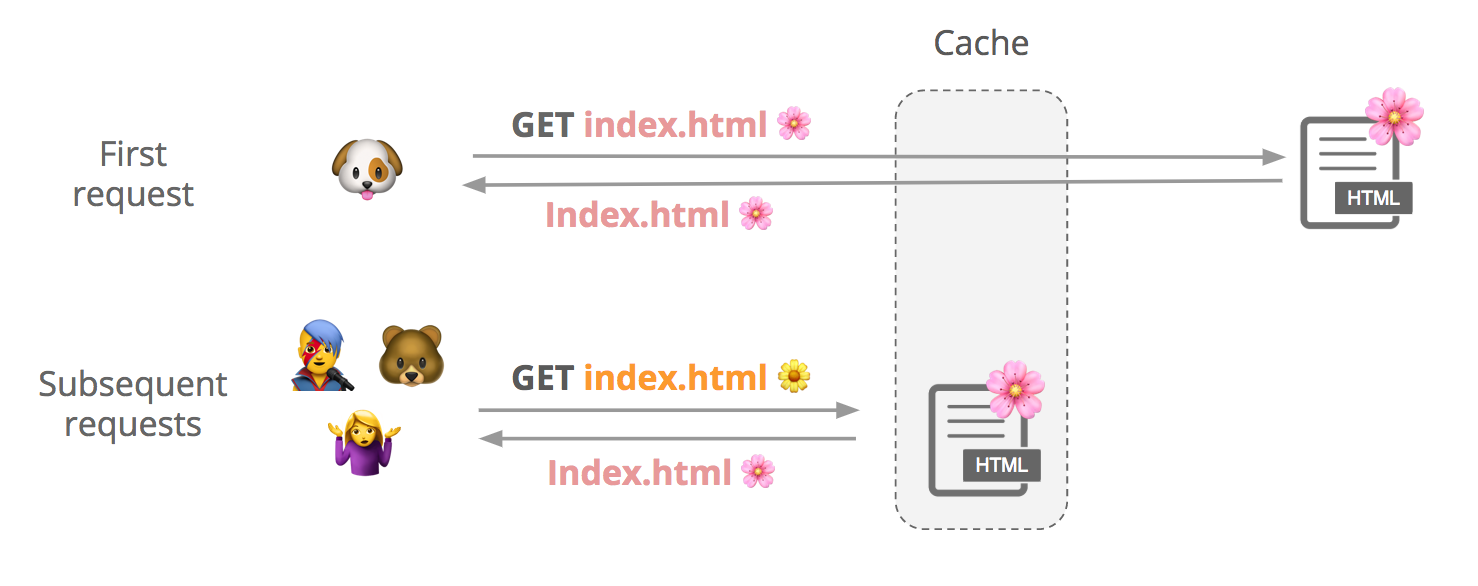
How a shared web cache works
Say a user requests a cacheable file, index.html. We first check if it’s in cache, and if it’s not not, we fetch it from the origin and store it. Subsequent users can request that file from our cache until it expires or gets evicted.
Although contents of a response can vary slightly between requests, customers may want to cache a single version of the file to improve performance:
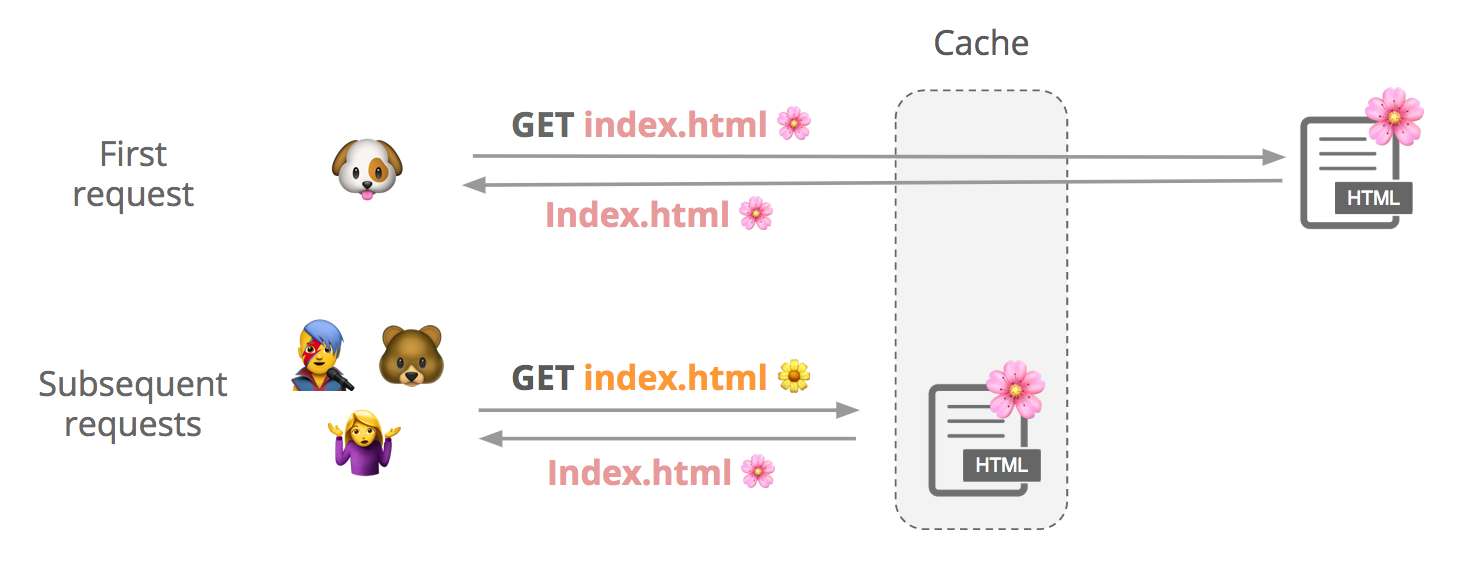
(See this support page for more info about how to cache HTML with Cloudflare.)
How do we know it’s the same file? We create something Continue reading
Security in the New World of Containers and Serverless
 This eBrief from SDxCentral takes a look at some of the security issues facing serverless and containers and delves into some of the tools and methodologies available to overcome these challenges.
This eBrief from SDxCentral takes a look at some of the security issues facing serverless and containers and delves into some of the tools and methodologies available to overcome these challenges.
VMware Cloud on AWS: Advanced Networking and Security with NSX-T SDDC
Announced in AWS Summit in New York last month and also briefly mentioned on the prior blog, Announcing General Availability of VMware NSX-T Data Center 2.2.0, NSX-T networking and security is now available in Preview Mode for new SDDC deployments on VMware Cloud on AWS. Please reach out to your sales/SE contact for more information. In this blog post, I give an overview of the advanced networking and security functionality provided by NSX-T within VMware Cloud on AWS. Continue reading
Classic Rock and Cloud-Native Attacks Collide at Black Hat
 Leading cloud access security broker (CASB) vendors McAfee and Bitglass talk security and cloud-native attacks at Black Hat.
Leading cloud access security broker (CASB) vendors McAfee and Bitglass talk security and cloud-native attacks at Black Hat.
Alibaba Cloud Eyes Expansion Into Southeast Asia With New Products, Partners
 At the Alibaba Cloud Summit this week, the cloud provider launched a wide breadth of products that span serverless, data, search and analytics, IoT, and machine learning.
At the Alibaba Cloud Summit this week, the cloud provider launched a wide breadth of products that span serverless, data, search and analytics, IoT, and machine learning.
Cisco’s Security Business, Service Provider Wins Propel Fiscal 4Q Results
 The company’s service provider business was up 6 percent year over year. But 5G isn’t the reason for the turnaround.
The company’s service provider business was up 6 percent year over year. But 5G isn’t the reason for the turnaround.
IoT Attacks Doubled in Two Months, Check Point Says
 While IoT malware made its top-three debut in July, cryptomining malware remained the top two offenders, according to the monthly report.
While IoT malware made its top-three debut in July, cryptomining malware remained the top two offenders, according to the monthly report.
Three new ways teams are using Cloudflare Access
Since leaving beta three weeks ago, Cloudflare Access has become our fastest-growing subscription service. Every day, more teams are using Access to leave their VPN behind and connect to applications quickly and securely from anywhere in the world.
We’ve heard from a number of teams about how they’re using Access. Each team has unique needs to consider as they move away from a VPN and to a zero trust model. In a zero trust framework, each request has to prove that a given application should trust its attempt to reach a secure tool. In this post, we’re highlighting some of the solutions that groups are using to transition to Cloudflare Access.
Solution 1: Collaborate with External Partners
Cloudflare Access integrates with popular identity providers (IdPs) so that your team can reach internal applications without adding more credentials. However, teams rarely work in isolation. They frequently rely on external partners who also need to reach shared tools.
How to grant and manage permissions with external partners poses a security risk. Just because you are working with a third-party doesn’t mean they should have credentials to your IdP. They typically need access to a handful of tools, not all of your internal Continue reading