Fortinet Forges FortiAI Security Service
The service utilizes a "self-learning" deep neural network to automate rote security tasks to...
Daily Roundup: Cisco SecureX All-In on Cloud Native
Cisco went all-in on cloud-native security with SecureX; AT&T joined Open Cybersecurity...
Weathering Heights: Of Resolutions And Ensembles
In the past year or so, watching supercomputer maker Cray, which is now part of Hewlett Packard Enterprise, has been a bit like playing a country and western song backwards on the record player. …
Weathering Heights: Of Resolutions And Ensembles was written by Timothy Prickett Morgan at The Next Platform.
Seamless remote work with Cloudflare Access
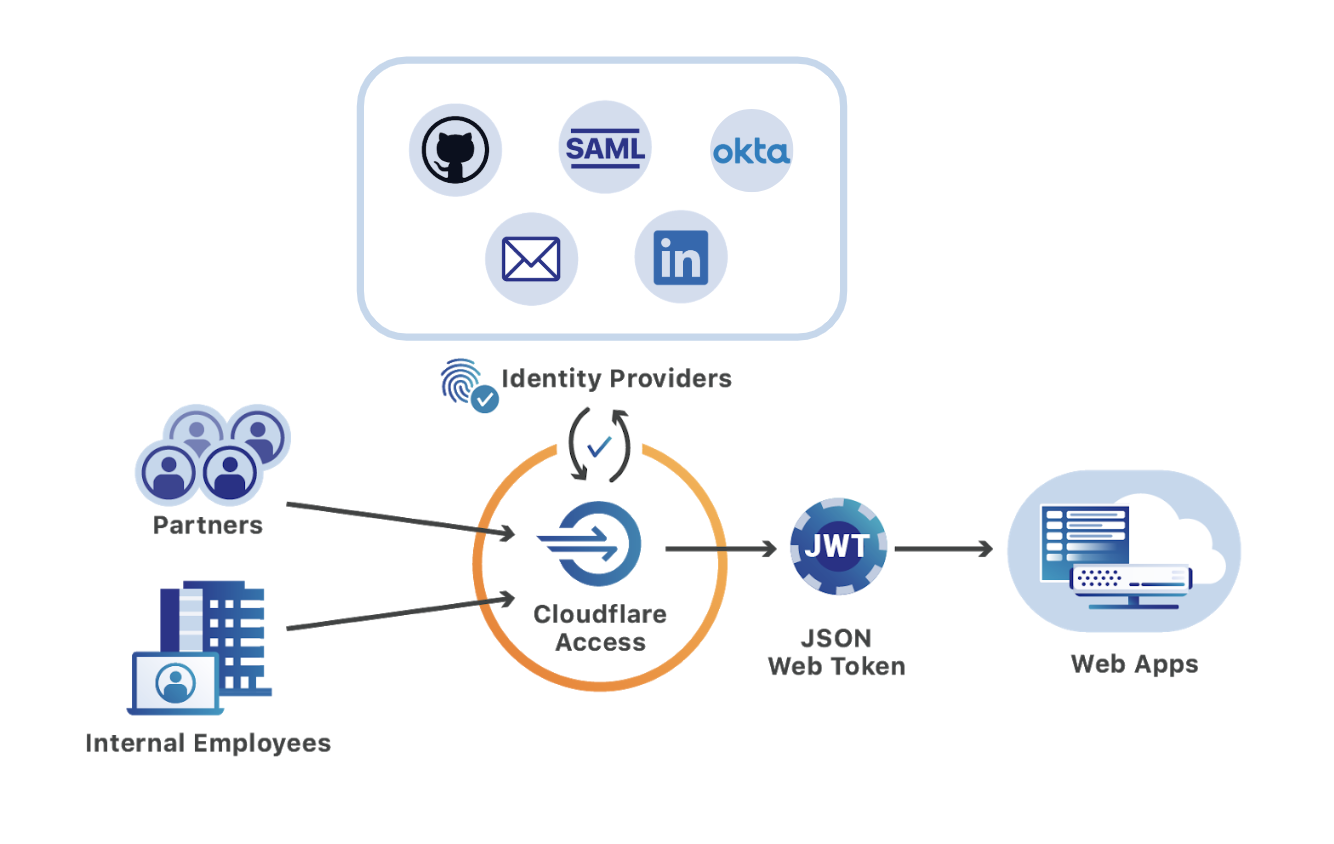
The novel coronavirus is actively changing how organizations work in real-time. According to Fortune, the virus has led to the “world’s largest work-from-home experiment.” As the epidemic crosses borders, employees are staying home and putting new stress on how companies manage remote work.
This is only accelerating an existing trend, however. Remote work has gained real traction in the last decade and Gartner projects that it will only continue. However, teams which are moving to a distributed model tend to do so slowly. When those timelines are accelerated, IT and security administrators need to be able to help their workforce respond without disrupting their team members.
Cloudflare Access can help teams migrate to a model that makes it seamless for users to work from any location, or any device, without the need for lengthy migrations or onboarding sessions. Cloudflare Access can be deployed in less than one hour and bring SaaS-like convenience and speed to the self-hosted applications that previously lived behind a VPN.
Leaving the castle-and-moat
When users share a physical space, working on a private network is easy. Users do not need clunky VPN clients to connect to the resources they need. Team members physically sit close Continue reading
Topology matters: how port-per-workload management strategies no longer hold up
In the beginning, there were switches. And connected to these switches were servers, routers and other pieces of gear. These devices ran one application, or at a stretch, multiple applications on the same operating system and thus IP stack. It was very much one-server-per-port; the SQL Server was always on port 0/8, and shutting down port 0/8 would affect only that machine.
This is no longer true, as network engineers well know. Physical hardware no longer dictates what, where, and how servers and other workloads exist. Cloud computing, multi-tenant virtual infrastructures and dynamically reallocated virtual resources mean that one port can cover 20 or 200 servers. Conversely, link aggregation and other forms of port density protocols mean that one server can have fault-tolerant aggregated links across one, five or 50 ports.
A new way of looking at switching—as a logical, rather than physical, topology—is required. In this view, switches aren’t so much pieces of the network architecture themselves, but simply ports that can be used to set up much more complex logical links. This article will focus on two main concepts: routing protocols (to allow better utilization of underutilized switching links) and switching protocols such as STP (those used to Continue reading
Tech Bytes: Getting A Full-Fidelity View Of Network Security With Riverbed (Sponsored)
On today's Tech Bytes we discuss the essential role that visibility plays in network security. Riverbed is our sponsor. We explore how Riverbed brings together logs, flow records, and packet capture to provide a full-fidelity view from multiple angles to help you respond to analyze security events. Our guests are Marco Di Benedetto, SVP and CTO; and Vincent Berk, VP and Chief Architect for Security at Riverbed.Tech Bytes: Getting A Full-Fidelity View Of Network Security With Riverbed (Sponsored)
On today's Tech Bytes we discuss the essential role that visibility plays in network security. Riverbed is our sponsor. We explore how Riverbed brings together logs, flow records, and packet capture to provide a full-fidelity view from multiple angles to help you respond to analyze security events. Our guests are Marco Di Benedetto, SVP and CTO; and Vincent Berk, VP and Chief Architect for Security at Riverbed.
The post Tech Bytes: Getting A Full-Fidelity View Of Network Security With Riverbed (Sponsored) appeared first on Packet Pushers.
Verizon Warns of Rising Enterprise Mobile Security Risk
The operator’s third annual survey on mobile security concluded that 43% of respondents believe...
Socratic vs. Euclidean Forms of API Documentation

I was emailing a service about their documentation and while their doc was good, about one particularly tricky concept they told me that once you use it for a while, that’s when you’ll understand it.
In other words: you’ll only understand it after you understand it.
I didn’t like that response. I want documentation that takes me from an unproductive newbie to a somewhat functioning journeyperson. Not an expert, but I want to get stuff done as soon as possible. And for that you need to understand the mental model behind the API. Otherwise, how do you know how to make anything happen?
I realize it’s hard to make good documentation. I spent a lot of time writing Explain the Cloud Like I'm 10 just to communicate the mental model behind the cloud. It’s not easy.
Then I read that something that showed me there are two different styles of documentation: Euclidean and Socratic:
Euclidean - state your axioms and let users derive the rest. Easiest for the API provider, but hardest on the user. This is the most common form of documentation. You see it all the time. Each entry point in the API is sort of Continue reading
Cisco SecureX Unifies Network, Cloud, Endpoint Security
Cisco’s 2020 CISO Benchmark Study found that 28% of security professionals say that managing a...
FPGA Inroads to Convolutional Neural Networks
At The Next FPGA Platform event in January there were several conversations about what roles reconfigurable hardware will play in the future of deep learning. …
FPGA Inroads to Convolutional Neural Networks was written by Josh Gibson at The Next Platform.
Network Break 272: Dell Technologies Sells RSA; Nubeva Cracks TLS 1.3 With Out-Of-Band Decryption
The latest Network Break podcast analyzes Dell Technologies' sale of its RSA business unit; what sponsor cancellations at the RSA Conference might mean for large tech events going forward; Arista Networks' financial results; new capabilities in products from ExtraHop, Nubeva, and Spirent; and more tech news.Network Break 272: Dell Technologies Sells RSA; Nubeva Cracks TLS 1.3 With Out-Of-Band Decryption
The latest Network Break podcast analyzes Dell Technologies' sale of its RSA business unit; what sponsor cancellations at the RSA Conference might mean for large tech events going forward; Arista Networks' financial results; new capabilities in products from ExtraHop, Nubeva, and Spirent; and more tech news.
The post Network Break 272: Dell Technologies Sells RSA; Nubeva Cracks TLS 1.3 With Out-Of-Band Decryption appeared first on Packet Pushers.
Leading Japan to a Better Future with KCME’s Hyungbae Kim
We hear from KCME's Hyungbae Kim on his work on mobile development to create a more sustainable and...
The Week in Internet News: ISPs Sue Maine Over New Privacy Law

Protesting privacy: Four ISP trade groups are suing the state of Maine for a privacy law that goes into effect this year, Ars Technica reports. Among other things, the law supposedly violates ISP free speech rights because it limits their ability to advertise to their customers and to offer discounts in exchange for customers’ personal information. The Maine law requires ISPs to get customers’ opt-in consent before using or sharing sensitive data.
DSL over fiber: The California Advanced Services Fund, a program launched in 2008 to connect all Californians to broadband, was an early success, but recent actions in the state legislature have encouraged slow speeds of 6 Mbps and eliminated the fund’s ability to serve public housing already served by slow DSL service, the EFF says in a blog post. “By establishing an abysmally low standard based on DSL technology that made its debut more than a decade ago, the state’s regulator is forced to conclude that basically everyone has useful broadband access today,” the EFF says. “This has kept the state from closing the digital divide.”
It’s getting better: Nigeria is making great strides in getting residents connected to the Internet, the BBC reports. More than Continue reading