Stopping Drupal’s SA-CORE-2019-003 Vulnerability
On the 20th February 2019, Drupal announced that they had discovered a severe vulnerability and that they would be releasing a patch for it the next day. Drupal is a Content Management System used by many of our customers, which made it important that our WAF protect against the vulnerability as quickly as possible.
As soon as Drupal released their patch, we analysed it to establish what kind of payloads could be used against it and created rules to mitigate these. By analysing the patch we were able to put together WAF rules to protect cloudflare customers running Drupal.
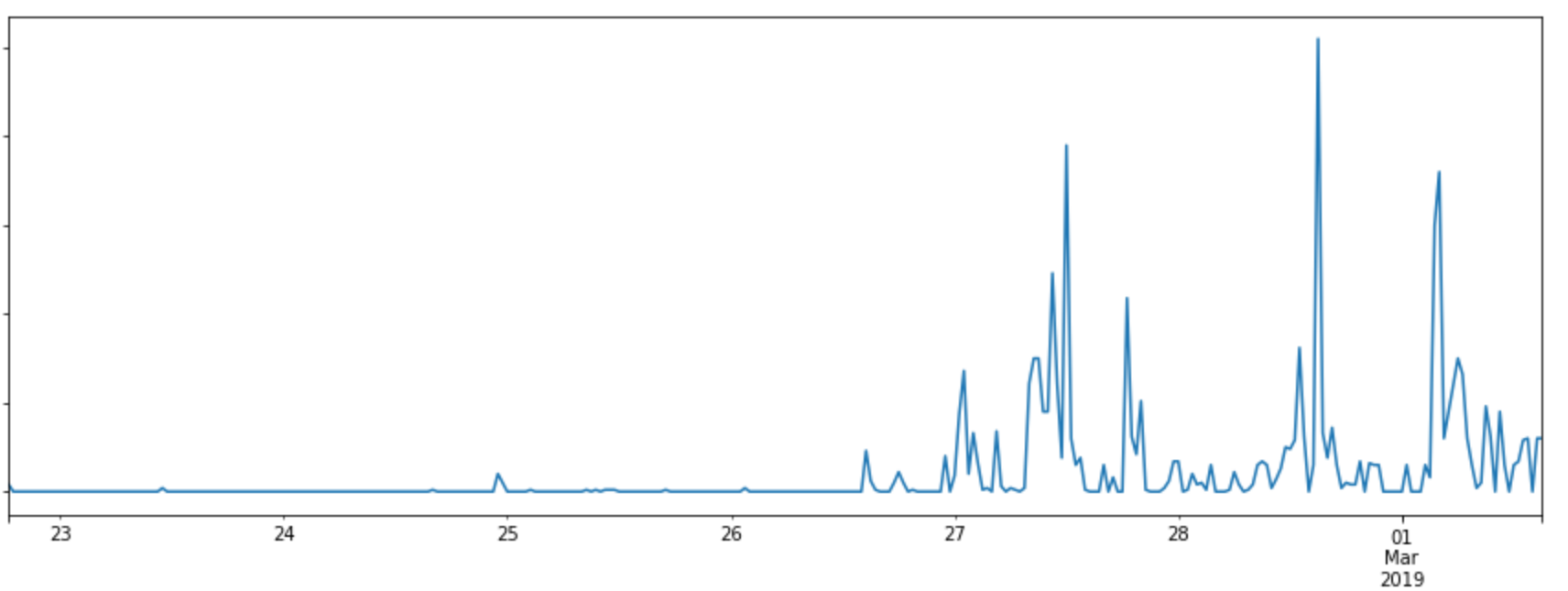
We identified the type of vulnerability we were dealing within 15 minutes. From here, we were able to deploy rules to block the exploit well before any real attacks were seen.
The exploit
As Drupal's release announcement explains, a site is affected if:
From looking at the patch we very quickly realised the exploit would be based on deserialization. The option ['allowed_classes' Continue reading
 The security landscape is essentially AI versus AI. May the best man, err, machine win.
The security landscape is essentially AI versus AI. May the best man, err, machine win.
 The Chicago-based regional carrier plans to begin offering 5G services by the end of this year.
The Chicago-based regional carrier plans to begin offering 5G services by the end of this year. Archer is a governance, risk management, and compliance platform. NetWitness is a threat detection...
Archer is a governance, risk management, and compliance platform. NetWitness is a threat detection...
 The attacks occurred after security research firm Pen Test Partners posted a blog containing...
The attacks occurred after security research firm Pen Test Partners posted a blog containing... The service uses Nokia’s Nuage Networks for SD-WAN, Fortinet for virtual security services,...
The service uses Nokia’s Nuage Networks for SD-WAN, Fortinet for virtual security services,... Huawei is losing no time in building on its momentum from the show as today it opened a Cyber...
Huawei is losing no time in building on its momentum from the show as today it opened a Cyber...