The Languages Which Almost Became CSS
This was adapted from a post which originally appeared on the Eager blog. Eager has now become the new Cloudflare Apps.
In fact, it has been a constant source of delight for me over the past year to get to continually tell hordes (literally) of people who want to – strap yourselves in, here it comes – control what their documents look like in ways that would be trivial in TeX, Microsoft Word, and every other common text processing environment: “Sorry, you’re screwed.”
— Marc Andreessen
1994
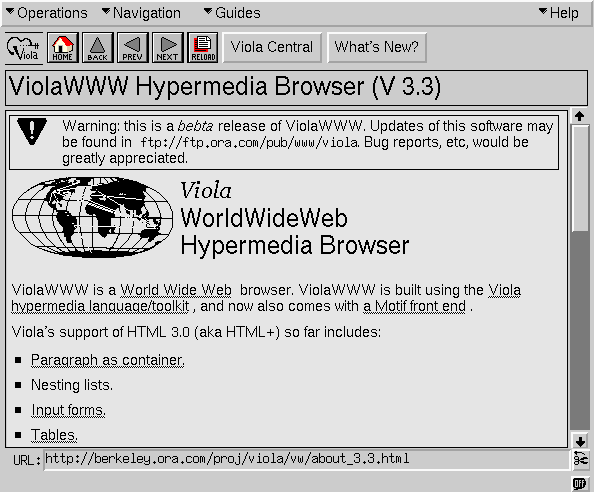
When Tim Berners-Lee announced HTML in 1991 there was no method of styling pages. How a given HTML tag was rendered was determined by the browser, often with significant input from the user’s preferences. To Continue reading











 SVP David Goeckeler will oversee the Viptela business.
SVP David Goeckeler will oversee the Viptela business. Bitnami hopes to add more functionality and provide a unifying experience.
Bitnami hopes to add more functionality and provide a unifying experience.