Response: I am not a supplier
 Open source software owes you nothing. You owe it.
Open source software owes you nothing. You owe it.
Gigabyte Spins Off Server Division To Chase Datacenter Business
Gigabyte Technology’s enterprise server division has been spun off under a new logo: Giga Computing. …
Gigabyte Spins Off Server Division To Chase Datacenter Business was written by Tobias Mann at The Next Platform.
The Interesting Years Ahead For Servers
By every measure we can get our hands on, 2022 was a bumper year for server shipments and server spending, which is good indicator for the appetite for new kinds of applications and the expansion of existing applications in the world at large. …
The Interesting Years Ahead For Servers was written by Timothy Prickett Morgan at The Next Platform.
Hedge 160: Avishai Ish-Shalom and Jurassic Cloud

Cloud might seem shiny and new—but that’s just the way it looks on the outside. Most cloud services are still built on decades old technology, from networking to file access. Avishai Ish-Shalom joins Tom Ammon and Russ White to discuss the impact of changes in hardware on the design of operating systems, and think through how things will need to change to continue the drive for more performance.
The New Branch Office and the Role of Zero Trust Network Access
Zero Trust Network Access is designed to give users access over the internet to just the applications and services they need to have access to.How Cloudflare can help stop malware before it reaches your app


Let’s assume you manage a job advert site. On a daily basis job-seekers will be uploading their CVs, cover letters and other supplementary documents to your servers. What if someone tried to upload malware instead?
Today we’re making your security team job easier by providing a file content scanning engine integrated with our Web Application Firewall (WAF), so that malicious files being uploaded by end users get blocked before they reach application servers.
Enter WAF Content Scanning.
If you are an enterprise customer, reach out to your account team to get access.
Making content scanning easy
At Cloudflare, we pride ourselves on making our products very easy to use. WAF Content Scanning was built with that goal in mind. The main requirement to use the Cloudflare WAF is that application traffic is proxying via the Cloudflare network. Once that is done, turning on Content Scanning requires a single API call.
Once on, the WAF will automatically detect any content being uploaded, and when found, scan it and provide the results for you to use when writing WAF Custom Rules or reviewing security analytics dashboards.
The entire process runs inline with your HTTP traffic and requires no change to your Continue reading
Rust Binary and Docker Releases Using Github Actions
https://codingpackets.com/blog/rust-binary-and-docker-releases-using-github-actions
Supermicro Throws Its Weight Behind Arm Servers
Supermicro has become the latest of the big OEMs to add Arm-based systems to its portfolio, with the launch of its Mt. …
Supermicro Throws Its Weight Behind Arm Servers was written by Tobias Mann at The Next Platform.
Basic Step-Functions Input and Output and Lambda— Passing Data From one to another
With so much focus on serverless in Re-Invent 2022 and the advantages of Step Functions, I have started to transform some of my code from Lambda to Step Functions.
Step-Function was hard until I figured out how data values can be mapped for input and how data can be passed and transformed between Lambda functions. I have made a small attempt for someone who is starting in step functions for understanding the various steps involved.
Basically, Step Functions can be used to construct business logic and Lambda can be used to transform the data instead of transporting with Lambda-Invokes from Lambda Functions.
Let’s take the following example
I have step_function_1 which has the requirement to invoke another lambda if my_var is 1 else do not do anything.
This is a simple if-else logic followed by the lambda-invoke function
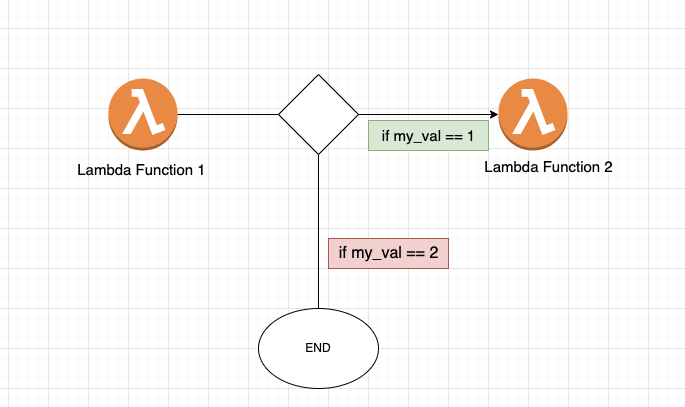
Now, the power of step-functions will come into play to write these conditional and also pass data from Lambda to Other making it super scalable for editing in future and all of the code will seem very logical and pictorial, best part is this can be designed instead of learning Amazon’s State Language.
let’s try to do Continue reading
Asking Meaningful Questions: How To Break Negative Patterns
Unconscious patterns of behavior can impede our professional progress. For example, you might watch others capitalize on ideas you have but don’t act on. Or your abrupt delivery of “the facts” alienates your colleagues and creates friction that can be detrimental. As I’ve recognized patterns in my own life and career, I’ve developed ways to […]
The post Asking Meaningful Questions: How To Break Negative Patterns appeared first on Packet Pushers.
Why the Industry Needs SASE Standards
MEF recently published the industry’s first standard for SASE, which defines common terminology, attributes of the service, and a service framework, along with a Zero Trust frameworkAzure Host-Based SDN: Part 1 – VFP Introduction
Azure Virtual Filtering Platform (VFP) is Microsoft’s cloud-scale virtual switch operating as a virtual forwarding extension within a Hyper-V basic vSwitch. Figure 1-1 illustrates an overview of VFP building blocks and relationships with basic vSwitch. Let’s start the examination from the VM vm-nwkt-1 perspective. Its vNIC vm-cafe154 has a synthetic interface eth0 using a NetVSC driver (Network Virtual Service Client). The Hyper-V vSwitch on the Parent Partition is a Network Virtual Service Provider (NetVSP) with VM-facing vPorts. Vm-cafe154 is connected to vPort4 over the logical inter-partition communication channel VMBus. VFP sits in the data path between VM-facing vPorts and default vPort associated with physical NIC. VFP uses port-specific Layers for filtering traffic to and from VMs. A VFP Layer is a Match Action Table (MAT) having a set of policy Rules. Rules consist of Conditions and Actions and are divided into Groups. Each layer is programmed by independent, centralized Controllers without cross-controller dependencies.
Let’s take a concrete example of Layer/Group/Rule object relationship and management by examining the Network Security Group (NSG) in the ACL Layer. Each NSG has a default group for Infrastructure rules, which allows Intra-VNet traffic, outbound Internet connection, and load balancer communication (health check, etc.). We Continue reading
DoS Attack Using Spanning Tree Protocol
The Spanning Tree Protocol (STP) is a network protocol that builds a loop-free logical topology […]
The post DoS Attack Using Spanning Tree Protocol first appeared on Brezular's Blog.