The Technical Challenges of Building Cloudflare WARP
If you have seen our other post you know that we released WARP to the last members of our waiting list today. With WARP our goal was to secure and improve the connection between your mobile devices and the Internet. Along the way we ran into problems with phone and operating system versions, diverse networks, and our own infrastructure, all while working to meet the pent up demand of a waiting list nearly two million people long.
To understand all these problems and how we solved them we first need to give you some background on how the Cloudflare network works:
How Our Network Works
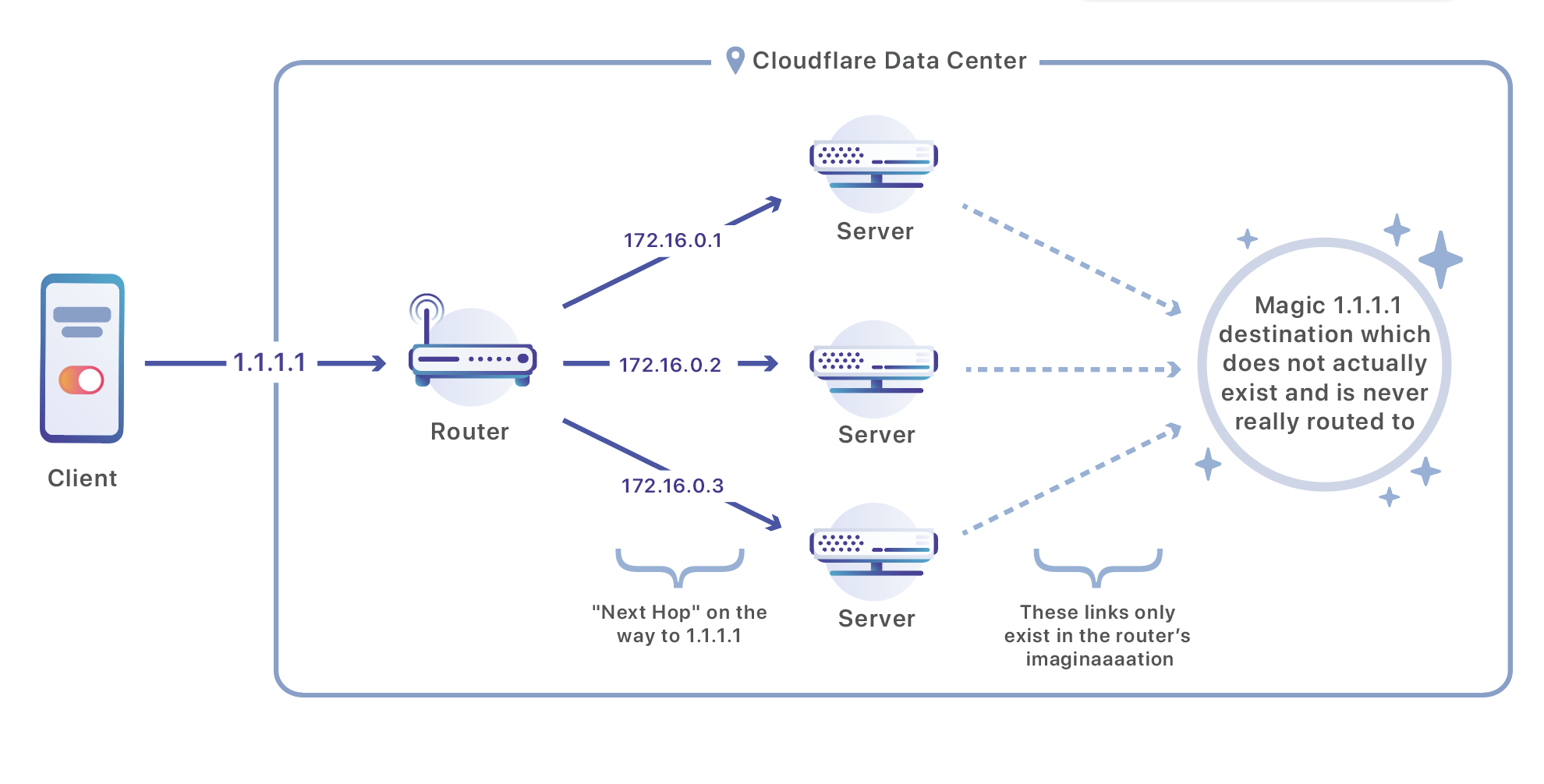
The Cloudflare network is composed of data centers located in 194 cities and in more than 90 countries. Every Cloudflare data center is composed of many servers that receive a continual flood of requests and has to distribute those requests between the servers that handle them. We use a set of routers to perform that operation:
Our routers listen on Anycast IP addresses which are advertised over the public Internet. If you have a site on Cloudflare, your site is available via two of these addresses. In this case, I am doing a DNS query Continue reading
Testing Open vSwitch-DPDK

In a previous tutorial we have built DPDK 18.11.2 and Open vSwitch 2.11.1 on Linux Debian 10.1 VM (buster). We have created a L3 Open vSwitch QEMU appliance that we will use to compare performance of Open vSwitch with enabled/disabled DPDK. A network topology is depicted on the Picture 1.
The lab is created as GNS3 project which consists of a single Debian Open vSwitch appliance. Two Linux Core 6.3 hosts PC1 and PC2 are connected to the switchports Ethernet0 and Ethernet1, respectively. Firstly, we are going to bind the both ports to DPDK-compatible driver and create a bridge with the DPDK ports attached to the bridge. As a last step, we will measure maximum achievable bandwidth with iPerf3 tool. The host PC1 will be be acting as a iPerf3 client connecting to the iPerf3 server running on the host PC2.
Note: Open vSwitch 2.11.1 appliance built on Debian 10 buster and DPDK 18.11.2 is available in Download-> Appliance Section. The Linux Core 6.3 image is available there, as well.

Picture 1 - Debian Open vSwitch/DPSK Appliance with Connected Host
1. GNS3 Configuration
Check GNS3 settings for Open Continue reading
Debian Open vSwitch Appliance with DPDK
Open vSwitch is a production quality, multilayer virtual switch licensed under the open source Apache 2.0 license. It is designed to enable massive network automation through programmatic extension, while still supporting standard management interfaces and protocols (e.g. NetFlow, sFlow, IPFIX, RSPAN, CLI, LACP, 802.1ag).
DPDK is the Data Plane Development Kit that consists of libraries to accelerate packet processing workloads running on a wide variety of CPU architectures.
Note: Open vSwitch images are customized with my after install script and they are ready for use in GNS3.
Username is debian with the password debian.
Debian Linux 10 (buster) VMDK Appliance with DPDK 18.11.2 and Open vSwitch 2.11.1 [997,2MB]
https://drive.google.com/file/d/1ZuVVP2POUnFjySt0YpFwPeSG5Rtw_6Gj/view?usp=sharing
Juniper JNCIE-CLOUD Announced
I know we all have our cloudy day (some of us more than others) yet if you are a cloud …
The post Juniper JNCIE-CLOUD Announced appeared first on Fryguy's Blog.
Automation Solution: Deploy BGP Routing with YANG Data Models
A while ago Ruben Tripiana tried to configure BGP on Cisco IOS using IETF YANG data models… and failed. In Spring 2019 Building Network Automation Solutions online course Chris Crook decided to deploy BGP routing on multiple platforms using YANG data models instead of configuration templates. Not only did he succeed, he also documented his work and the tools he used, and published the solution so you can replicate his efforts.
You can find many more network automation solutions created by the attendees of our automation course in solutions showcase.
Controlling Information Flow: NATS Subjects and Queues
Publish/subscribe messaging platforms like NATS allow us to build highly event-driven software systems, where we can build software to constantly listen for relevant messages and take action accordingly. This is what makes EDI projects like StackStorm (a project I’ve worked on and written about before) - and others like it- so powerful. Another advantage of pub/sub systems is that publishers don’t have to know or care if anyone is listening.Controlling Information Flow: NATS Subjects and Queues
Publish/subscribe messaging platforms like NATS allow us to build highly event-driven software systems, where we can build software to constantly listen for relevant messages and take action accordingly. This is what makes EDI projects like StackStorm (a project I’ve worked on and written about before) - and others like it- so powerful. Another advantage of pub/sub systems is that publishers don’t have to know or care if anyone is listening.Citrix Meshes Istio Service Mesh Into Its ADC Platform
The company is offering Istio in two ways: as an ingress gateway for north-south traffic into the...
Kubernetes Kills Containership’s Cruise
The company's founder and CTO explained that it was unable to adequately monetize its operations in...
Rubrik, NetApp Catapult Data Management to the Cloud
The partnership aims to simplify data management on cloud-scale architectures through policy-based...
Full Stack Journey 034: Choosing Your Own Adventure
If you've ever thought about working for yourself, catch this episode of the Full Stack Journey. Guest Ned Bellavance discusses his decision to leave a job as an IT consultant to become an independent content creator of tech training material. Ned shares real-world insights into his experience along with practical takeaways.
The post Full Stack Journey 034: Choosing Your Own Adventure appeared first on Packet Pushers.
Full Stack Journey 034: Choosing Your Own Adventure
If you've ever thought about working for yourself, catch this episode of the Full Stack Journey. Guest Ned Bellavance discusses his decision to leave a job as an IT consultant to become an independent content creator of tech training material. Ned shares real-world insights into his experience along with practical takeaways.NSX-T 2.5 What is new for Kubernetes
NSX-T 2.5 was released last week and now we also have the new NSX Container Plugin 2.5 on the market…. VMworld US 2019 is also over with announcements of huge innovations like NSX Intelligence, enhanced security, and improved operability and observability. You can find more information here! I would like to take this opportunity to specifically highlight the new containers capabilities we had been working on for this release.
What is new in NSX Container plugin (NCP)
Simplified UI (Policy API) support
With the introduction of the new intent-based Policy API and corresponding Simplified UI, administrators have seen that objects created by NCP for Kubernetes are not visible in the new UI. Instead they had to go to the Advanced Networking & Security tab that corresponds to the old imperative APIs. Furthermore, all related objects like T0, IP Block, IP Pool had to be created using the Advanced Networking & Security tab. I am happy to announce that from NCP 2.5+ we have a parameter in the NCP configmap (ncp.ini) policy_nsxapi that can be set to True. In that case, NCP will start calling the new intent-based API and all objects will be visible in the simplified UI. Continue reading
Aryaka’s HybridWAN Boasts Multi-Tenancy, Enhanced Firewalls
Its HybridWAN allows low-priority traffic to be routed over broadband or 4G LTE while running...
Verizon NG-PON2 Trial Hits 34 Gb/s Speed
The trial with network partner Calix used SDN to bond four multi-gig fiber optic channels.