The Week in Internet News: Testing 1, 2, 3

This is a test: Amazon has asked the U.S. Federal Communications Commission for permission to test a new wireless Internet service using the 3.5 MHz spectrum band, Cord Cutters News reports. The test, in Sunnyvale, California, would run from mid-August to mid-February. The test is in addition to Amazon’s plans to launch 3,236 satellites for a new home Internet service.
Billions for broadband: U.S. presidential candidate Elizabeth Warren, a Democratic senator from Massachusetts, wants to spend $85 billion to expand rural broadband in the country, CNet reports. She also wants to override states trying to prevent local municipalities from building their own broadband networks.
Russian hackers vs. the IoT: Microsoft has accused a Russian hacking group of targeting Internet of Things devices, including a voice over IP phone and office printer, Security Today reports. The Russian group known as Fancy Bear was allegedly involved in the hack of the Democratic National Committee before the 2016 U.S. elections.
Lawsuit recognition: Facebook users can sue the social networking site for its facial recognition photo tagging service, a U.S. court has ruled. Illinois users have claimed the tagging service violates a state privacy law, NPR reports. “Once a Continue reading
Why You Can’t Fix a System from the Inside
Stumbled upon an interesting article describing numerous examples of how it's impossible to fix a system from the inside because the good guys always lose to the more aggressive (and less scrupulous) individuals.
It's amazing how well the same ideas apply to TCP-versus-UDP, P2P traffic versus everything else (this one has been fixed after a lot of pressure from the outside), latency- versus drop-based TCP congestion management and $vendor marketing.
Money Moves: July 2019
Here are some of the most prominent venture capital and merger and acquisition news items from...
GKE with VPN – Networking options
While working on a recent hybrid GCP plus on-premise customer architecture, we had a need to connect GKE cluster running in GCP to a service running in on-premise through a VPN. There were few unique requirements like needing to expose only a small IP range to the on-premise and having full control over the IP … Continue reading GKE with VPN – Networking optionsWeekly Top Posts: 2019-08-11
- Dynatrace Scores $544M IPO, Cloudflare to Follow Suit
- Cisco Pays $8.6M in First-Ever Security Software Whistleblower Payout
- Lanner and GTT Leverage uCPE to Bolster SD-WAN Performance
- IBM Packs Red Hat OpenShift Into Cloud Paks
- Cohesity Adds Security Capabilities With CyberScan
The TOGAF ADM – Part I
In my last post we briefly looked at the TOGAF ADM. We won’t be able to fit it all into a single blog post but we will start to explore the ADM from a high level. ADM stands for Architecture Development Method and it organized in 10x different phases. These different phases are designed to […]GitHub’s CI/CD Expansion Set to Change Workflows
“It will be interesting to see how the continuous integration players react. These vendors...
DNS Query Privacy
In this article we'll look at DNS Query Name Minimisation in some detail and present the results of our measurement of the current level of use of this resolver query technique in today's Internet.The Serverlist: Building out the SHAMstack

Check out our seventh edition of The Serverlist below. Get the latest scoop on the serverless space, get your hands dirty with new developer tutorials, engage in conversations with other serverless developers, and find upcoming meetups and conferences to attend.
Sign up below to have The Serverlist sent directly to your mailbox.
Heavy Networking 464: Provocative Statements With Tom Hollingsworth
Today's Heavy Networking is a conversation with Tom Hollingsworth that ranges over a variety of provocative statements about the networking and technology industries, including "certifications are dead," "enterprise networking is dying," "BGP as a kitchen sink protocol is a bad idea," and more. Tom responds and discussions ensue.
The post Heavy Networking 464: Provocative Statements With Tom Hollingsworth appeared first on Packet Pushers.
Fast Friday- Black Hat USA 2019
I just got back from my first Black Hat and it was an interesting experience. It was crazy to see three completely different security-focused events going on in town all at once. There was Black Hat, B-Sides Las Vegas, and DEFCON all within the space of a day or so of each other. People were flowing back and forth between them all and it was quite amazing.
A wanted to share a few quick thoughts about the event from my perspective being a first timer.
- The show floor wasn’t as bit as VMworld or Cisco Live, but it was as big as it needed to be. Lots of companies that I’ve heard of, but several more that were new to me. That’s usually a good sign of lots of investment in the security space.
- Speaking of which, I talked to quite a few companies about a variety of analytics, telemetry, and insider threat monitoring solutions. And almost all of them had a founder from Israel or someone that was involved in the cybersecurity areas of the IDF. That’s a pretty good track record for where the investment is going.
- The Vegas booth gimmicks never change. I think I’ve spent too Continue reading
Ulukhaktok: Community Networking in the (Far) North

In June of this year, I had the great privilege of traveling to Ulukhaktok, NWT, Canada to talk to community members about the possibility of building a new, local Internet service network. As a result of these meetings, and the incredibly driven individuals I met with in Ulu, this time next year, Ulukhaktok will be the proud owner of the far-most Northern community network in the world.
I left Washington, D.C. in the throes of summer – upper 80-degree weather and so humid you’d feel wet the second you stepped outside. Two days and five planes later I was in Ulukhaktok, a community of about 400 people on the 70th parallel. Summer there is a little different, and I explored the community amidst summer snow and 24-hour days.
I spent four days getting to know the community, and it wasn’t hard to understand the deep sense of community pride right away. Ulu is a beautiful, U-shaped town on the edge of the Arctic Ocean. It’s filled with people who will stop when they see a stranger, smile, and ask who you are and what you’re doing. And every time someone stopped, I told them about the Internet Society, Continue reading
Using Automation vs Making Automation

First published in Packet Pushers Human Infrastructure Magazine 58 – you can subscribe here Another side of the debate around programming, automation and orchestration. Are you a user or a maker ? Platforms are 80/20 For the last 20 or 30 years, network management software has followed an 80/20 approach to customisation. On the first […]
The post Using Automation vs Making Automation appeared first on EtherealMind.
Innovations in CBD And Hemp
Cannabidiol (CBD) and hemp have been known to be used in health supplements for humans and animals, as well as in various beauty products. Since the legalization of marijuana in many U.S. states, innovations in CBD and hemp products have become an acceptable and highly effective alternative to synthetic drugs for the treatment of many conditions including:
- Chronic pain
- Anxiety and depression
- PTSD
- Arthritis
- Sleep issues
While more studies need to be done, it is believed since CBD and hemp oil may help reduce inflammation in the body that it may help serve as treatment and preventions for such health issues as heart disease and diabetes.
Innovative in CBD and hemp products for the treatment of dogs, specifically, may help to:
- Reduce aggression
- Relieve pain
- Improve skin and coat appearance
- Help reduce seizures
When CBD and hemp products do not offer a miracle cure, they have shown great promise in helping people who do not respond well to traditional drugs or who may simply not like the negative side effects for prescription drugs in treating certain medical conditions.
Keep in mind that most of the innovations in CBD and hemp are not designed to make you high, Continue reading
Introducing Certificate Transparency Monitoring


Today we’re launching Certificate Transparency Monitoring (my summer project as an intern!) to help customers spot malicious certificates. If you opt into CT Monitoring, we’ll send you an email whenever a certificate is issued for one of your domains. We crawl all public logs to find these certificates quickly. CT Monitoring is available now in public beta and can be enabled in the Crypto Tab of the Cloudflare dashboard.
Background
Most web browsers include a lock icon in the address bar. This icon is actually a button — if you’re a security advocate or a compulsive clicker (I’m both), you’ve probably clicked it before! Here’s what happens when you do just that in Google Chrome:
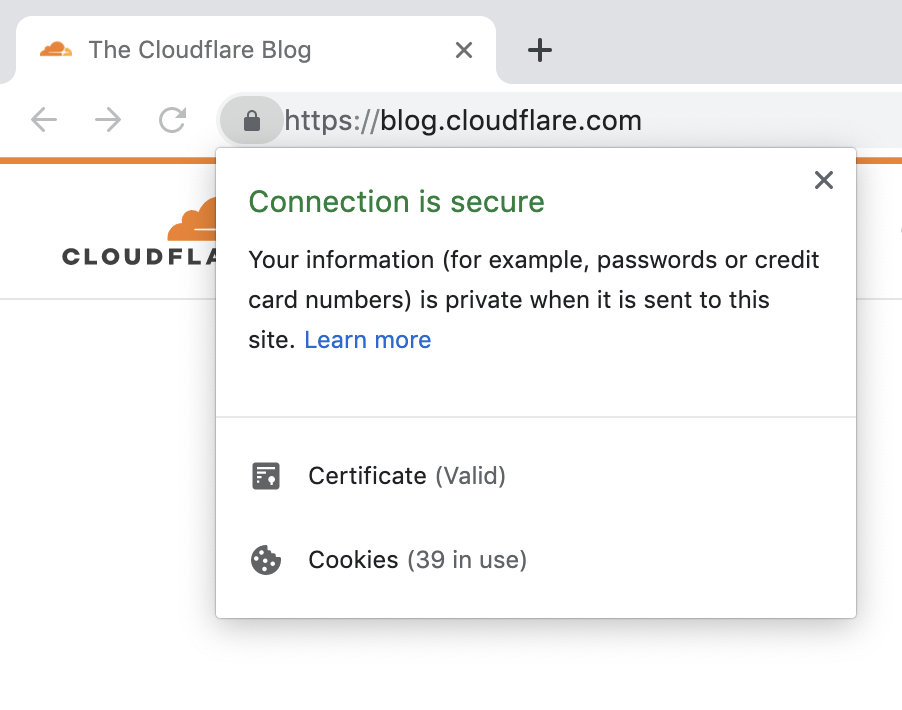
This seems like good news. The Cloudflare blog has presented a valid certificate, your data is private, and everything is secure. But what does this actually mean?
Certificates
Your browser is performing some behind-the-scenes work to keep you safe. When you request a website (say, cloudflare.com), the website should present a certificate that proves its identity. This certificate is like a stamp of approval: it says that your connection is secure. In other words, the certificate proves that content was not intercepted or Continue reading