MTN Consulting Names AWS’ Infrastructure Vendors
 In addition to using vendors, AWS manufactures a range of equipment from routers, chips, network interface cards, and network gear for high-speed data transfers.
In addition to using vendors, AWS manufactures a range of equipment from routers, chips, network interface cards, and network gear for high-speed data transfers.
Flexible deployment options for NSX-T Data Center Edge VM
Each datacenter is unique and is designed to serve the specific business needs. To serve these business needs, you could have a small or a large ESXi/KVM footprint. NSX-T Data Center can be leveraged to provide networking and security benefits regardless of the size of your datacenter. This blog focusses on a critical infrastructure component of the NSX-T Data Center i.e. NSX-T Edge node. Refer to my previous blogs, where I have discussed how the centralized components of a logical router are hosted on Edge nodes and also, provide centralized services like N-S routing, NAT, DHCP, Load balancing, VPN etc. To consume these services, traffic from compute nodes must go to the Edge node.
These NSX-T Edge nodes could be hosted in a dedicated Edge cluster or a collapsed Management and Edge cluster as discussed in the NSX-T Reference design guide. NSX-T Edge nodes could also be hosted in Compute Cluster in small Datacenter topologies, making it a Collapsed Compute and Edge Cluster design. Please refer to NSX-T Reference design guide to understand the pros/cons of using a dedicated cluster vs a shared cluster.
In this blog, I will cover various deployment options of NSX-T VM form factor Continue reading
How Telemedicine Is Impacting Healthcare in Rural Nepal
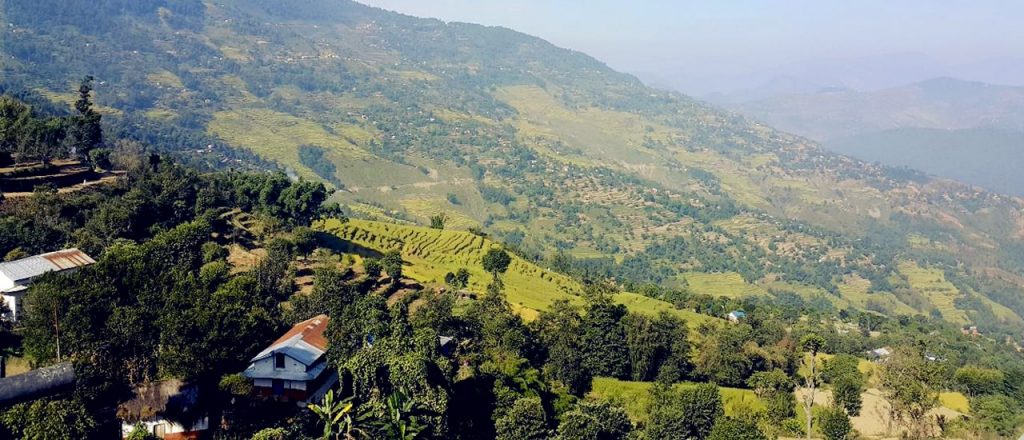
Lack of an affordable and accessible community healthcare is a challenge in rural communities across the globe, and an obstacle in ensuring a healthy population in remote indigenous communities across rural Nepal. Broadband connectivity is opening the door to more accessible and cost-effective patient care by speeding up electronic health records and digital images and increasing mobility with wireless monitoring devices.
This story takes place in Dullu, a place extremely difficult to reach, located in the Dailekh District in mid-western Nepal. In order to reach the area, you need to fly from Kathmandu to Surkhet via a domestic flight and then take an off-road, four-wheel drive across approximately 80 kilometers, many of which are through a mountainous dirt road that remains challenging for both visitors and locals. Despite being fertile land filled with culture and history, Dullu is far behind in the development process and it is still struggling in terms of infrastructure development, including road access, robust communication, and proper health and education services.
The town’s solitary hospital is perpetually understaffed. Budget cuts, inhospitable winters, and lack of medical resources have perennially plagued medical service deliveries to the approximately 45,000 residents who depend on a distant health center.
The Continue reading
IBM’s Acquisition of Red Hat Hinges on Integration
 Red Hat is viewed as an open source software beacon and some worry a heavy-handed integration from IBM could snuff out that light.
Red Hat is viewed as an open source software beacon and some worry a heavy-handed integration from IBM could snuff out that light.
Ciena Optimizes Its Packet Optical Networks With Analytics Service
 The offering is sold as a subscription service in three tiers to provide different levels of visibility and data analysis based on an organization’s needs.
The offering is sold as a subscription service in three tiers to provide different levels of visibility and data analysis based on an organization’s needs.
Google Does Good While Other Cloud Providers Battle for JEDI
 It’s not all rainbows and flowers at Google. Hundreds of employees are planning a walkout following a report that the cloud giant rewarded a top exec accused of sexual misconduct.
It’s not all rainbows and flowers at Google. Hundreds of employees are planning a walkout following a report that the cloud giant rewarded a top exec accused of sexual misconduct.
MEF Releases SD-WAN Technical Specification to Its Members
 MEF aims for its SD-WAN service standardization to accelerate sales of SD-WAN products and services like MEF accomplished with Carrier Ethernet service standardization.
MEF aims for its SD-WAN service standardization to accelerate sales of SD-WAN products and services like MEF accomplished with Carrier Ethernet service standardization.
Russia Will Launch 5G in 2020, GSMA Says
 Mobile broadband is expected to be the first use case for 5G in Russia. Specifically, operators are looking at ways to ease network congestion in urban areas.
Mobile broadband is expected to be the first use case for 5G in Russia. Specifically, operators are looking at ways to ease network congestion in urban areas.
Deploying Secure Kubernetes Containers in Production: Thwarting the Threats
 Once you have containers in production certain security measures must be put in place to cover network filtering, container inspection, and host security.
Once you have containers in production certain security measures must be put in place to cover network filtering, container inspection, and host security.
Oracle Cloud Tech Seems Solid. But Is It Too Late?
 The company’s got about a year to turn around its Oracle cloud business if it’s going to meet its lofty goals.
The company’s got about a year to turn around its Oracle cloud business if it’s going to meet its lofty goals.
The Benefits of Flexible Multi-Cloud and Multi-Region Networking
A report recently published by 451 Research shows that almost 70% of all enterprises will be using a multi-cloud or hybrid IT infrastructure in a year’s time. As more and more enterprises are swayed into the cloud, companies who have already adopted the cloud are now choosing to go with multi-cloud infrastructure or hybrid architecture for their IT requirements.
The report also showcased that about 60% of all workloads are expected to run using a form of hosted cloud service by 2019. This is an increase of about 45% from 2017. This marks an impressive change from DIY owned and operated services to a cloud or third-party hosted IT services. Therefore, the future of IT services is clearly hybrid and multi-cloud.
Here we explore some of the reasons multi-cloud is a fantastic idea for enterprises when they consider security, flexibility, reliability, and cost-effectiveness.
Reduce Security Risks Like a DDoS Attack
A Distributed Denial of Service or DDoS attack is when a number of different computer systems attack a server, website, network resource or a cloud hosting unit. A DDoS attack can be executed by an individual as well as a federal government.
In a scenario that your company’s website is Continue reading