BGP design options for EVPN in Data Center Fabrics
Ivan Pepelnjak described his views regarding BGP design options for EVPN-based Data Center Fabrics in this article. In comments to following blog post we briefly discussed sanity of eBGP underlay + iBGP overlay design option and come to conclusion that we disagree on this subject. In this blog post I try to summarize my thoughts about this design options.
Let’s start with the basics – what’s the idea behind underlay/overlay design? It’s quite simple – this is logical separation of duties of “underlying infrastructure” (providing simple IP transport in case of DC fabrics) and some “service” overlayed on top of it (be it L3VPN or EVPN or any hypervisor-based SDN solution). The key word in previous sentence – “separation”. In good design overlay and underlay should be as separate and independent from each other as possible. This provides a lot of benefits – most important of which is the ability to implement “smart edge – simple core” network design, where your core devices (= spines in DC fabric case) doesn’t need to understand all complex VPN-related protocols and hold customer-related state.
We use this design option for a long time – OSPF for underlay and iBGP for overlay is de-facto Continue reading
BiB 027: Juniper Networks At NFD17 – A Platform Emerges
Juniper Networks presented for a second day at Network Field Day 17, this time focusing on Appformix for analytics & automation; and PeerBot, a BGP configuration application.
The post BiB 027: Juniper Networks At NFD17 – A Platform Emerges appeared first on Packet Pushers.
SEO Performance in 2018 Using Cloudflare
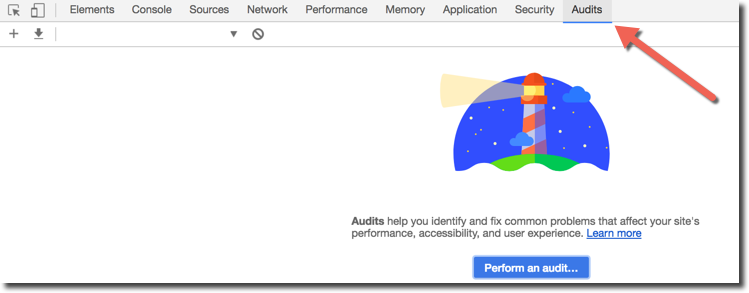
For some businesses SEO is a bad word, and for good reason. Google and other search engines keep their algorithms a well-guarded secret making SEO implementation not unlike playing a game where the referee won’t tell you all the rules. While SEO experts exist, the ambiguity around search creates an opening for grandiose claims and misinformation by unscrupulous profiteers claiming expertise.
If you’ve done SEO research, you may have come across an admixture of legitimate SEO practices, outdated optimizations, and misguided advice. You might have read that using the keyword meta tag in your HTML will help your SEO (it won’t), that there’s a specific number of instances a keyword should occur on a webpage (there isn’t), or that buying links will improve your rankings (it likely won’t and will get the site penalized). Let’s sift through the noise and highlight some dos and don’ts for performance-based SEO in 2018.
SEO is dead, long live SEO!
Nearly every year since its inception, SEO is declared dead. It is true that the scope of best practices for search engines has narrowed over the years as search engines have become smarter, and much of the benefit Continue reading
The Lazy Person’s Guide to Better Online Privacy
I consider myself a high-functioning lazy person. I do my laundry regularly, but leave clean clothes in a pile on the floor. I make it to work on time, but have to set my alarm for an hour earlier than I’d like because I hit the snooze button so many times. I will wear a blazer to my business casual office, but only to cover up my terribly wrinkled shirts… which I pick up off my bedroom floor each morning.
At the Internet Society, I work primarily on topics related to security and privacy. Through my work, I have the pleasure of learning about new vulnerabilities or computer viruses, how different apps and devices can or already are spying on me and selling my data, and all other manner of scary online threats. As you can imagine I’ve become increasingly paranoid about my online privacy.
Yet, when it comes to online privacy, lazy and paranoid is a terrible combination.
I know what I should be doing to better protect my online privacy. I know I should update my devices regularly. I know I should be using two factor authentication when its available. But, like the clothes I know I should be folding, I Continue reading
List of EVPN and DC-related RFCs
In this post I try to collect links to all interesting RFCs and drafts related to DC, EVPN and network overlays.
Some of this documents are complete industry standards, some are drafts aiming to become such standarts, and others are just informational documents, often already outdated and forgotten, but despite this still interesting and useful. So don’t forget to pay attention to time frame each particular document was created and updated.
RFC 7209 – Requirements for Ethernet VPN (EVPN)
This document specifies the requirements for an Ethernet VPN (EVPN) solution, which addresses various VPLS issues.
RFC 7432 – BGP MPLS-Based Ethernet VPN
This document describes procedures for BGP MPLS-based Ethernet VPNs (EVPN-MPLS).
RFC 7938 – Use of BGP for Routing in Large-Scale Data Centers
This document summarizes operational experience in designing and operating large-scale data centers using BGP as the only routing protocol.
RFC 7348 – Virtual eXtensible Local Area Network (VXLAN)
This document describes Virtual eXtensible Local Area Network (VXLAN), which is used to address the need for overlay networks within virtualized data centers accommodating multiple tenants.
RFC 7364 – Problem Statement: Overlays for Network Virtualization
This document describes issues associated with providing multi-tenancy Continue reading
Don’t focus on trivia…
Found this great quote in Algorithms to Live By: The Computer Science of Human Decisions - a must-read for all nerds:
Depend upon it there comes a time when for every addition of knowledge you forget something that you knew before. It is of the highest importance, therefore, not to have useless facts elbowing out the useful ones.
Sherlock Holmes
Now you know why you should focus on how things work instead of memorizing commands ;)
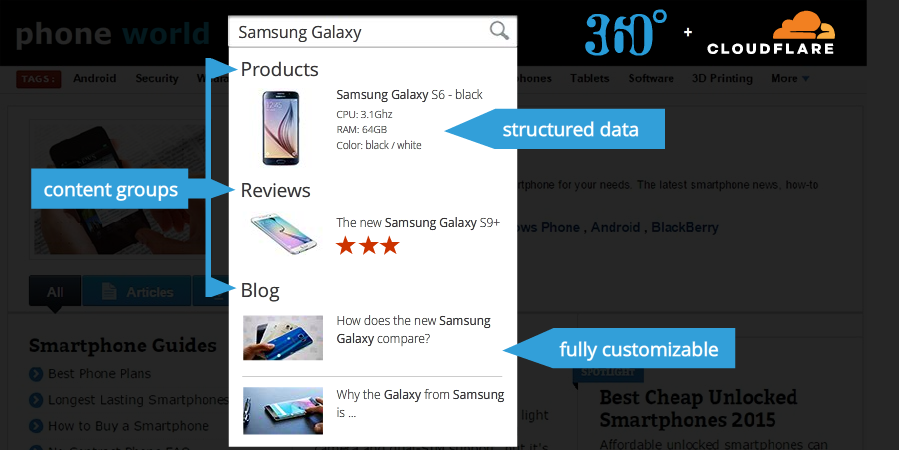
Lessons learned from adapting Site Search 360 for Cloudflare Apps

This is a guest post by David Urbansky, CEO and Co-Founder of SEMKNOX and Site Search 360. David is a search enthusiast having built natural language search experiences for e-commerce sites and recipe search engines.
As a startup founder, there are always key product decisions to be made when Site Search 360, our key product, is embedded in one context versus another. I’d like to share some experiences, choices, and challenges in our process packaging Site Search 360 for Cloudflare Apps.
What is Site Search 360?
Site Search 360 is a search solution for websites. Offering a search bar on a website improves user experience tremendously if the site has more than just a handful of pages. According to a eConsultancy study, up to 30% of web visitors use the search feature on e-commerce sites and searchers sometimes make up 40% of the revenue. Additionally, Nielsen Group found that 51% of people who did not find what they were looking for with the first query, gave up without refining the search - the search had better work very well then.
Why use the Cloudflare App?
Considering these facts, almost every website should have a search feature. However, implementing Continue reading
Networking Field Day 17 (NFD17) Redux
As I write this it’s Friday afternoon in Silicon Valley, Networking Field Day 17 (NFD17) is over, and I am truly exhausted after a week of presentations covering topics like Ethernet switch hardware, testing/simulation and network operating system (Mellanox, Ixia, Cumulus), Field Area Networks (Cisco), visibility and automation (Juniper AppFormix), distributed network monitoring (Thousand Eyes) and much more.
I will be posting in the coming weeks about some of the individual presentations, but while I dry off from the information firehose I thought I’d briefly summarize some of my personal highlights from the week.
Themes
One recurring theme throughout the week was automation. Cisco for example, spoke about the capabilities for Zero Touch Provisioning (ZTP) in IOS XR. Juniper presented the OpenContrail platform which, impressively, appears to have a new and very positive sense of direction after (in my opinion) floating around somewhat aimlessly for a while. Extreme Networks spoke about Workflow Composer, and its ability to integrate with tools like Splunk to auto-remediate detected issues. VMware demonstrated the impressive capabilities of NSX to configure distributed firewalling and microsegmentation down to the container level, while VeloCloud from VMware demonstrated another facet of automation, that of the software defined WAN.
Another Continue reading
China Mobile and China Unicom Deploy Huawei’s Cloud Fabric
 Huawei says it has no expectations of doing business with the U.S. government.
Huawei says it has no expectations of doing business with the U.S. government.
Weekend Reads 012618: Mostly Security and Legal Stuff
If it were not for the insatiable bandwidth needs of the twenty major hyperscalers and cloud builders, it is safe to say that the innovation necessary to get Ethernet switching and routing up to 200 Gb/sec or 400 Gb/sec might not have been done at the fast pace that the industry as been able to pull off. —Timothy Prickett Morgan @The Continue reading
Cavium Network Interface Cards Power HPE, VMware, and Microsoft HCI
 Cavium plans to continue expanding into the popular HCI sector.
Cavium plans to continue expanding into the popular HCI sector.
Watch the “State of the Net 2018” Live on Monday, January 29
Internet governance, blockchain, algorithms, free speech, net neutrality, IoT, cybersecurity, fragmentation … and so much more! On Monday, January 29, 2018, the State of the Net 2018 conference will be streaming live out of the Newseum in Washington DC. You can watch starting at 9:00am US EST (UTC-5) Monday morning at:
http://www.stateofthenet.org/live/
The SOTN 2018 agenda is packed with many of the leading voices in US Internet policy, including Senators, Representatives, and even an FCC Commissioner. Global organizations and corporations will be represented, too, among the many speakers.
At 11:00am EST, our own Sally Shipman Wentworth, VP of Global Policy Development, will participate in a panel, Internet Governance: Are We In A Post Multi-Stakeholder World?, along with Larry Strickling. Larry is perhaps best known recently for the IANA transition work but has been working with us on efforts to expand the use of the multistakeholder model for Internet governance. Others panelists will be Dr. Jovan Kurbalija from our partner the DiploFoundation; Steve DelBianco of NetChoice; and the Hon. Robert Strayer of the US State Department. The session will be moderated by Shane Tews from the Internet Education Foundation. The abstract is:
It will have been Continue reading
Intranet DDoS attacks
As on a Darkling Plain: Network Survival in an Age of Pervasive DDoS talk by Steinthor Bjarnason at the recent NANOG 71 conference. The talk discusses the threat that the proliferation of network connected devices in enterprises create when they are used to launch denial of service attacks. Last year's Mirai attacks are described, demonstrating the threat posed by mixed mode attacks where a compromised host is used to infect large numbers devices on the corporate network.The first slide from the talk shows a denial attack launched against an external target, launched from infected video surveillance cameras scattered throughout the the enterprise network. The large volume of traffic fills up external WAN link and overwhelms stateful firewalls.
The second slide shows an attack targeting critical internal services that can have been identified by reconnaissance from the compromised devices. In addition, scanning activity associated with reconnaissance for additional devices can itself overload internal resources and cause outages.
In both cases, most of the critical activity occurs behind the corporate firewall, making it extremely challenging to detect and mitigate these threats.
The talk discusses a number of techniques that service providers use to secure their networks that enterprises will need to adopt Continue reading
Free 5-Part Webcast Series on NSX

Mark your calendars now for this free VMware NSX: Things You Need to Know webcast series presented by VMware Education Services. Each 60-minute session is delivered by VMware Certified Instructors and offered at 3 different times so you can choose what works for your schedule.
- Feb 1: Simplify Network Provisioning with Logical Routing and Switching using VMware NSX
- Feb 22: Automate Your Network Services Deployments with VMware NSX and vRealize Automation
- Mar 8: Design Multi-Layered Security in the Software-Defined Datacenter using VMware vSphere 6.5 and VMware NSX 6.4
- Mar 29: Advanced VMware NSX: Demystifying the VTEP, MAC, and ARP Tables
- Apr 19: That Firewall Did What? Advanced Troubleshooting for the VMware NSX Distributed Firewall
RSVP for one or all five here. (See below for more info.)
Feb 1:
Simplify Network Provisioning with Logical Routing and Switching using VMware NSX
Did you know it’s possible to extend LANs beyond their previous boundaries and optimize routing in the data center? Or decouple virtual networkoperations from your physical environment to literally eliminate potential network disruptions for future deployments? Join us to learn how VMware NSX can make these a reality. We’ll also cover the networking components of NSX to Continue reading
Cisco Acquires Secure Hyperconvergence Startup
Skyport Systems deal bolsters Cisco's hybrid cloud security expertise.
SDxCentral’s Weekly Roundup — January 26, 2018
 Nokia opens a multi-cloud design center; VMware releases AWS Greengrass on vSphere; Qualcomm starts a 5G Initiative in China.
Nokia opens a multi-cloud design center; VMware releases AWS Greengrass on vSphere; Qualcomm starts a 5G Initiative in China.