Hedge 195: DDoS Inflection with Barry Greene

DDoS attacks still play a major role in the global Internet, costing organizations tens (or hundreds) or millions of dollars each year. What are the current and future trends in DDoS attacks? Barry Greene, a global expert in DDoS mitigation, joins Russ White and Tom Ammon to discuss the future of DDoS.
Cloudflare Email Security now works with CrowdStrike Falcon LogScale


We are excited to announce an extended partnership between CrowdStrike and Cloudflare to bring together Cloudflare Email Security and CrowdStrike Falcon® LogScale. With this integration, joint customers who have both Falcon LogScale and Cloudflare Email Security can now send detection data to be ingested and displayed within their Falcon LogScale dashboard.
What is CrowdStrike Falcon LogScale?
CrowdStrike Falcon LogScale enables organizations to ingest, aggregate and analyze massive volumes of streaming log data from a wide array of sources at petabyte scale. It offers search and visualization capabilities, enabling users to easily query and explore their log data to gain valuable insights and identify security threats or anomalies.
Falcon LogScale helps customers by providing:
Log Ingestion It supports the collection of logs from diverse sources and can handle high volumes of log data in real time.
Real-Time Search Users can perform fast searches across their log data, enabling quick detection and investigation of security incidents or operational issues.
Dashboards and Visualizations Falcon LogScale offers customizable dashboards and visualizations to help teams gain insights from their log data.
All of these capabilities enable proactive threat hunting by leveraging advanced analytics. It helps security teams identify potential threats, detect anomalies, and quickly remediate Continue reading
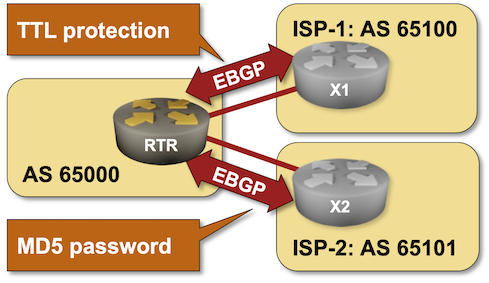
BGP Labs: Protect EBGP Sessions
I published another BGP labs exercise a few days ago. You can use it to practice EBGP session protection, including Generalized TTL Security Mechanism (GTSM) and TCP MD5 checksums1.

I would strongly recommend to run BGP labs with netlab, but if you like extra work, feel free to use any system you like including physical hardware.
-
I would love to add TCP-AO to the mix, but it’s not yet supported by the Linux kernel, and so cannot be used in Cumulus Linux or FRR containers. ↩︎
BGP Labs: Protect EBGP Sessions
I published another BGP labs exercise a few days ago. You can use it to practice EBGP session protection, including Generalized TTL Security Mechanism (GTSM) and TCP MD5 checksums1.
-
I would love to add TCP-AO to the mix, but it’s not yet supported by the Linux kernel, and so cannot be used in Cumulus Linux or FRR containers. ↩︎
Day Two Cloud 211: Cloud Security Acronym Soup With Jo Peterson
Today on Day Two Cloud we go deep on new areas of cloud security that you may not be familiar with. There are forces out there that are driving the rise of new security tools and processes, and we bring back guest Jo Peterson to help us make sense of it all.
The post Day Two Cloud 211: Cloud Security Acronym Soup With Jo Peterson appeared first on Packet Pushers.