Worth Reading: Where Are the Self-Driving Cars?
Gary Marcus wrote an interesting essay describing the failure of self-driving cars to face the unknown unknowns. The following gem from his conclusions applies to AI in general:
In a different world, less driven by money, and more by a desire to build AI that we could trust, we might pause and ask a very specific question: have we discovered the right technology to address edge cases that pervade our messy really world? And if we haven’t, shouldn’t we stop hammering a square peg into a round hole, and shift our focus towards developing new methodologies for coping with the endless array of edge cases?
Obviously that’s not going to happen, we’ll keep throwing more GPU power at the problem trying to solve it by brute force.
Worth Reading: Where Are the Self-Driving Cars?
Gary Marcus wrote an interesting essay describing the failure of self-driving cars to face the unknown unknowns. The following gem from his conclusions applies to AI in general:
In a different world, less driven by money, and more by a desire to build AI that we could trust, we might pause and ask a very specific question: have we discovered the right technology to address edge cases that pervade our messy really world? And if we haven’t, shouldn’t we stop hammering a square peg into a round hole, and shift our focus towards developing new methodologies for coping with the endless array of edge cases?
Obviously that’s not going to happen, we’ll keep throwing more GPU power at the problem trying to solve it by brute force.
DNS is the new BGP
One of the big changes within the Internet over the last decade or so has been the shift to replicated services. Service replication allows each individual service point to be positioned closer to clusters of users. The question now becomes who (and how) selects the "best" service point to use in response to each user's service request. It seems that in many cases the answer is the DNS, and not the BGP routing protocol.Transforming Container Network Security with Calico Container Firewall
In today’s cloud-driven landscape, containerized workloads are at the heart of modern applications, driving agility, scalability, and innovation. However, as these workloads become increasingly distributed across multi-cluster, multi-cloud, and hybrid environments, the challenge of securing them grows exponentially. Traditional network security measures designed for static network boundaries are ill-suited for the dynamic nature of containerized applications.
The Challenge: Protecting Cloud-Native Workloads
The rapid migration to the cloud has resulted in an explosion of cloud workloads, ranging from traditional applications with minimal cloud adaptation to cloud-native applications exploiting the cloud’s elasticity and scalability.
Cloud-native applications, in particular, rely on microservices architectures, ephemeral and highly elastic containers, and CI/CD automation through platforms like Kubernetes. These applications embrace the cloud’s dynamic nature but introduce unique security challenges. Unlike traditional workloads, cloud-native applications lack fixed network boundaries and are highly distributed across hybrid and multi-cloud environments. They demand a new approach to network security.
The Need for a Container Firewall in DevOps Flows:
The essence of DevOps is speed and automation. Containers and orchestration platforms like Kubernetes enable rapid software development and deployment. However, this agility brings heightened security concerns.
Traditional firewalls, rooted in perimeter defenses, struggle to secure dynamic containerized environments effectively.

Fig Continue reading
Day Two Cloud 210: Can Network Automation Catch Up To The Cloud?
On today's Day Two Cloud we discuss the state of network automation and whether and how it can catch up to automation in the public cloud. We look at network automation challenges, define boundaries with other elements of the infrastructure stack, the impact of cloud networking, whether AI and ML can help, and more. Our guests are Chris Grundemann and Scott Robohn, co-founders of the Network Automation Forum (NAF).
The post Day Two Cloud 210: Can Network Automation Catch Up To The Cloud? appeared first on Packet Pushers.
Day Two Cloud 210: Can Network Automation Catch Up To The Cloud?
On today's Day Two Cloud we discuss the state of network automation and whether and how it can catch up to automation in the public cloud. We look at network automation challenges, define boundaries with other elements of the infrastructure stack, the impact of cloud networking, whether AI and ML can help, and more. Our guests are Chris Grundemann and Scott Robohn, co-founders of the Network Automation Forum (NAF).How to Stay Up and Running When the Cloud Goes Down – and Avoid Lock-ins
The dominance of a small set of cloud providers means many businesses find themselves in ‘one-stop shops’ where vendor lock-in remains a huge issue, especially when outages occur.Building companies means building careers: why I joined Cloudflare as Chief People Officer

One piece of advice I received early in my career was to get into a transformative industry. Those words have followed me ever since, and it’s a goal I’ve encouraged many others to pursue.
For me, it meant first launching into biotechnology where I learned my passion for working with deeply technical and disruptive businesses doing things that hadn’t been done before.
I later joined Amazon at a time when it was best known as a retailer instead of a technology company as it is today. While there, I led HR for some of their most technical businesses from eCommerce to AWS. As all these businesses scaled over the next decade, I became increasingly focused, and then finally fully dedicated to, leading HR for AWS. During that time, I had the opportunity to serve as a thought partner to the AWS CEO and leadership team as the organization grew from 400 employees to 30,000.
It was at this point in my career that I realized my passion for scaling a company with practices that reinforce the mission and building programs with intention to nurture the culture. To have any impact, all this work must be in support of promoting a Continue reading
BGP Labs: Bidirectional Route Redistribution
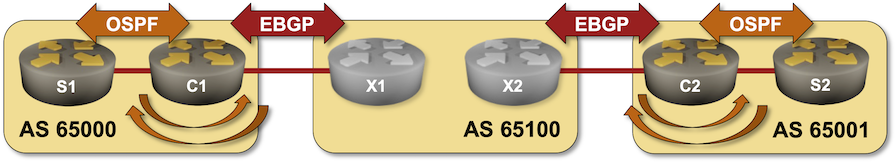
In the next BGP labs exercise you’ll build the customer part of an MPLS/VPN solution. You’ll use bidirectional OSPF-to-BGP route redistribution to connect two sites running OSPF over a Service Provider MPLS backbone.

I would strongly recommend to run labs with netlab, but if you like extra work, feel free to use any system you like including physical hardware.
BGP Labs: Bidirectional Route Redistribution
In the next BGP labs exercise, you’ll build the customer part of an MPLS/VPN solution. You’ll use bidirectional OSPF-to-BGP route redistribution to connect two sites running OSPF over a Service Provider MPLS backbone.
How to Minimize Multi-Cloud Complexity
Successfully juggling multiple clouds can sometimes feel like performing a circus act. Fortunately, a few simple tricks can keep the task from becoming a showstopper.Heavy Networking 700: Rethinking Networking and Security For The Campus And Branch With Fortinet (Sponsored)
On today's sponsored Heavy Networking we talk with Fortinet about how it converges network and security across the breadth of its portfolio. Fortinet is best known for its firewalls, but the company also offers campus and branch switches, has a wireless portfolio, offers SD-WAN and SASE, provides AI-supported operations, and more. We also talk about Fortinet's approach to the branch office that rethinks networking, security, and performance.
The post Heavy Networking 700: Rethinking Networking and Security For The Campus And Branch With Fortinet (Sponsored) appeared first on Packet Pushers.