Bash Script for Converting Video To MP3 Audio
I like listening to video training on my smartphone while walking to work. To save the space on the memory card I convert videos to MP3 audio in advance. For this purpose I wrote a Bash script video_to_mp3.sh which helps me to manage a conversion job. The script uses ffmpeg for conversion and it creates parallel conversion tasks to speed up the conversion process. The script checks the CPU load and it creates a new background process only if the CPU load is under a particular limit entered by a user.
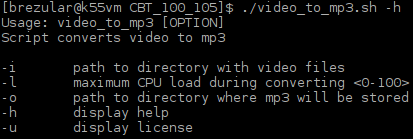
Picture 1 - Script Usage
Below is the output from the conversion process.
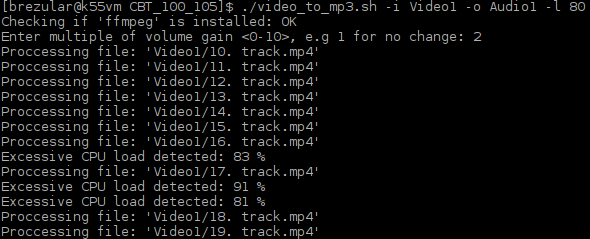
Picture 2 - Output From Conversion Process
The script creates a log file displaying info about the result of all conversion tasks. If the conversion fails for a particular video file, the script displays a return value of ffmpeg utility and the name of the file which is not successfully converted.
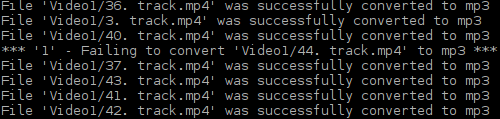
Picture 2 - Output from Log File
End.
Arista Reports Solid Q3 2016 Earnings
 It’s focused on meeting demand for its products.
It’s focused on meeting demand for its products.
OpenStack Summit Barcelona 2016: Current State
It’s October in the UK and blimey charlie, it’s a bit chilly. Good news then that the OpenStack Summit is in Barcelona! In comparison to Canada or Japan, it’s on my doorstep! Spain being the home of English holiday makers, the smell of sun cream, sangria and chicken nugget dinners awaits.
It Felt Different
Needless to say, I play investigator at these summits. Whether it’s the SDN congress, OpenStack or other networking events, the cynical grump hat is donned. Before I even managed to investigate anything, I felt something different. The hype lever was set to average and this show felt almost corporate. Good news or bad news? Something I’ve struggled to quantify all week and even now as I sit on the home bound flight to Blighty, I continue to ponder.
Big bang news was lacking like previous shows. Realistic use cases, real commentary and on-stage demos made this feel different. One of the demos made me both cringe and chuckle as Mark Collier played real life chaos monkey, pulling fibres and eventually even cutting through them during an EPC demo which included OPNFV Doctor and Vitrage. This demoed OpenStack’s capability to integrate with monitoring and life cycle tooling. Continue reading
FireEye Stock Climbs After Q3, Defying Security’s Slump
 Q3 revenues grew, and losses could have been worse.
Q3 revenues grew, and losses could have been worse.
Headcount: The Latest in Hirings, Firings And Retirings for October 2016
 Our monthly summary of executive moves and changes.
Our monthly summary of executive moves and changes.
CoreOS Creates ‘Operators’ for Stateful Apps in Containers
 It's more than Puppet/Chef for containers, CoreOS says.
It's more than Puppet/Chef for containers, CoreOS says.