SDxCentral Weekly News Roundup — September 2, 2016
 VMware and IBM released cloud services that enable organizations to move enterprise workloads to the cloud.
VMware and IBM released cloud services that enable organizations to move enterprise workloads to the cloud.
How R&D Helped Fuel Huawei’s Rise
 Huawei says it now has more than 50,000 patents.
Huawei says it now has more than 50,000 patents.
Worth Reading: Cisco, Arista, and shades of grey
The post Worth Reading: Cisco, Arista, and shades of grey appeared first on 'net work.
5 important reasons you should learn scripting
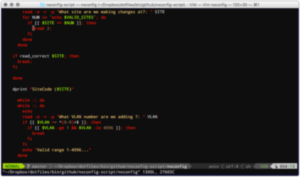 Today’s IT landscape if full of software defined marketecture, and lore of a dystopian future full of network engineers that do nothing but write code. But in reality, there are plenty of actual reasons you should be learning programming, or at least some basic scripting. For many network engineers programming is not new, we have all been hacking together shell, Perl and Python for a VERY long time. While the requirements in the future may change, today it is not necessary to become half network engineer half software engineer, but learning the basics now will keep you in the know. Learning the basics of logic and loop statements will not only help you speed up day to day tasks, but it will help you understand other languages as you expand your knowledge in the future. So, here are my top 10 reasons I think you need to learn scripting.
Today’s IT landscape if full of software defined marketecture, and lore of a dystopian future full of network engineers that do nothing but write code. But in reality, there are plenty of actual reasons you should be learning programming, or at least some basic scripting. For many network engineers programming is not new, we have all been hacking together shell, Perl and Python for a VERY long time. While the requirements in the future may change, today it is not necessary to become half network engineer half software engineer, but learning the basics now will keep you in the know. Learning the basics of logic and loop statements will not only help you speed up day to day tasks, but it will help you understand other languages as you expand your knowledge in the future. So, here are my top 10 reasons I think you need to learn scripting.
1: Automation can save you time
Writing a script for common / repetitive tasks can save you a staggering amount of time. Over the years I have written hundreds of scripts to aide in everything from Data Center VLAN/SVI management to banning/unbanning MAC addresses from multiple wireless lan controllers.
2: Continue reading
60% of Enterprise Workloads are Expected to Run in the Cloud by 2018
 IaaS is likely to see the highest growth over the next two years.
IaaS is likely to see the highest growth over the next two years.
Arista And Streaming Telemetry
On todays Weekly Show, we talk network telemetry with our sponsor, Arista Networks. Telemetry gives you deeper visibility into the network in near real time, and when combined with analytics can provide useful insights for operators. The post Show 304: Arista And The Brave New World Of Streaming Telemetry (Sponsored) appeared first on Packet Pushers.
SDN and NFV: Stepping Stones to the Telco Cloud
 Combine the flexibility of NFV with the network programmability offered by SDN.
Combine the flexibility of NFV with the network programmability offered by SDN.
Best practices for incident response in the age of cloud
This vendor-written tech primer has been edited by Network World to eliminate product promotion, but readers should note it will likely favor the submitter’s approach.
Most CISOs receive a rude awakening when they encounter their first major security issue in the cloud. If they identify a critical vulnerability that requires a patch, they may not have the authorization to tweak the cloud provider's pre-packaged stack. And if the customer does not own the network, there may not be a way to access details that are critical to investigating an incident.
In order to avoid a major security issue in the cloud, CISO’s must have an incident response plan. Here is how to build one:
To read this article in full or to leave a comment, please click here
