AT&T Slams ‘Pre-Standard’ 5G Specs, Forms Group To Speed Standards
 Operator is “in talks” with global operators to accelerate 3GPP Standard.
Operator is “in talks” with global operators to accelerate 3GPP Standard.
Self-Improvement Through Time Travel
There are some days I wish I could travel back in time and “fix” the time I wasted through an hour, a day, or a week working on something that really wasn’t worth my time, or just wandering through links on the Internet, looking at things I don’t really (ultimately) care about. My time management skills are, honestly, often lacking. There doesn’t seem to be a way, does there, though?
 Or maybe there is. Let’s twist our brains a little and think about it this way. Tomorrow is going to be the day we wish we could travel into from the day after tomorrow to fix, right? So what if we did reverse time travel and fix tomorrow today? Sure, sounds nice, but how? The answer might seem a little trivial, but it’s only apparently trivial, rather than trivial in real life.
Or maybe there is. Let’s twist our brains a little and think about it this way. Tomorrow is going to be the day we wish we could travel into from the day after tomorrow to fix, right? So what if we did reverse time travel and fix tomorrow today? Sure, sounds nice, but how? The answer might seem a little trivial, but it’s only apparently trivial, rather than trivial in real life.
Once answer is the humble todo list. I know, you’ve made one of these before—in fact, you probably already have one, don’t you? And it’s never really helped, right? Well, let’s see if we can figure out how to supercharge to make it a bit more effective. To begin, we have to try to understand how a todo Continue reading
New Webinar: Docker Networking Fundamentals
After the fantastic Docker 101 webinar by Matt Oswalt a few people approached me saying “that was great, but we’d need something more on Docker networking”, and during one of my frequent chats with Dinesh Dutt he mentioned that he already had the slides covering that topic.
Problem solved… and Dinesh decided to do it as a free webinar (thank you!), so all you have to do is register. Hurry up, there are only 1000 places left ;)
Bandwidth Costs Around the World
CloudFlare protects over 4 million websites using our global network which spans 86 cities across 45 countries. Running this network give us a unique vantage point to track the evolving cost of bandwidth around the world.
 CC BY-SA 2.0 image by Quinn Dombrowski
CC BY-SA 2.0 image by Quinn Dombrowski
Recap
Two years ago, we previewed the relative cost of bandwidth that we see in different parts of the world. Bandwidth is the largest recurring cost of providing our service. Compared with Europe and North America, there were considerably higher Internet costs in Australia, Asia and Latin America. Even while bandwidth costs tend to trend down over time, driven by competition and decreases in the costs of underlying hardware, we thought it might be interesting to provide an update.
Since August 2014, we have tripled the number of our data centers from 28 to 86, with more to come. CloudFlare hardware is also deployed in new regions such as the Middle East and Africa. Our network spans multiple countries in each continent, and, sometimes, multiple cities in each country.
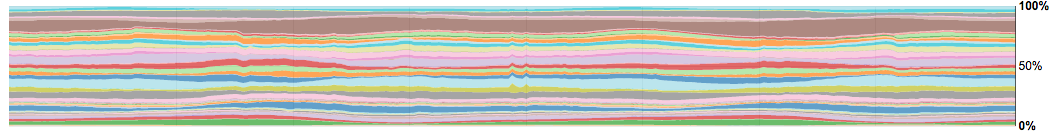
There are approximately thirteen networks called “Tier 1 networks” (e.g., Telia, GTT, Tata, Cogent) who Continue reading