5 Reasons to Switch to the Calico Ingress Gateway (and How to Migrate Smoothly)
The End of Ingress NGINX Controller is Coming: What Comes Next?
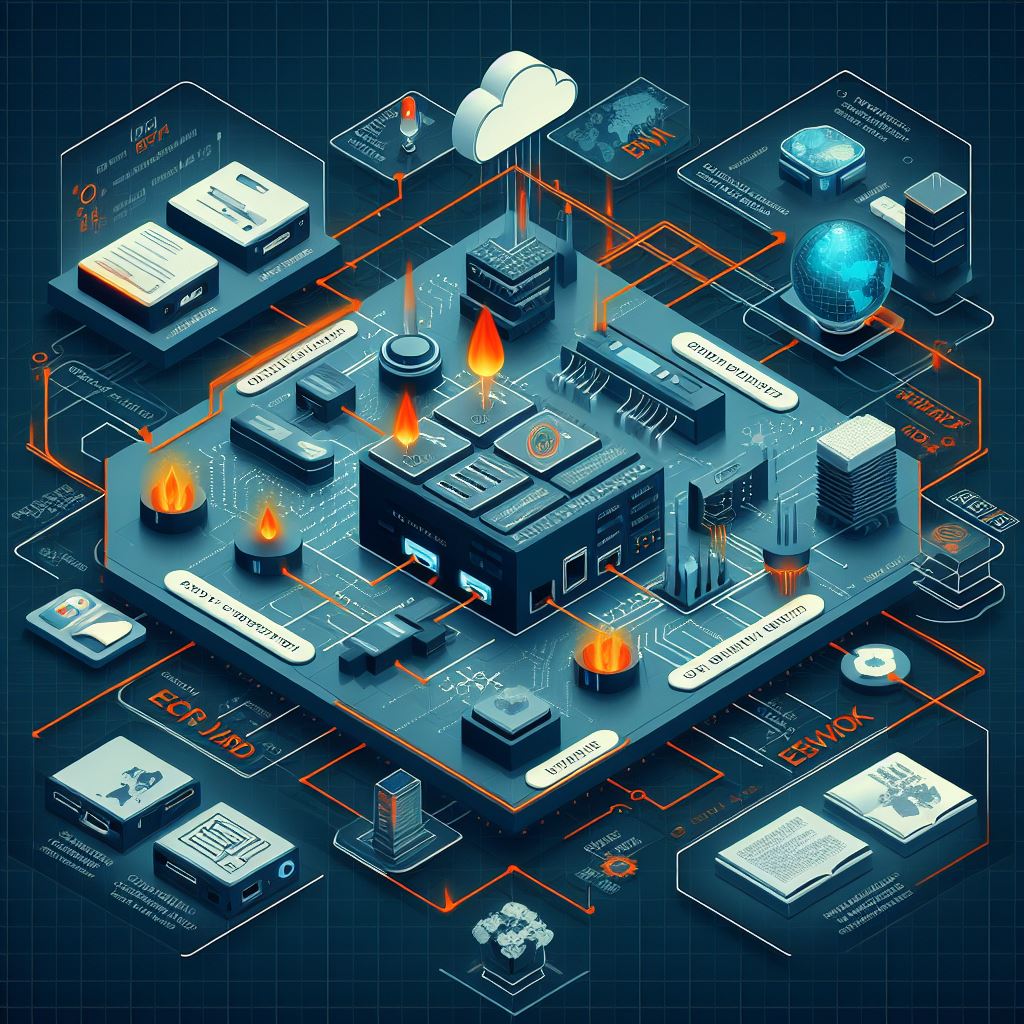
The Ingress NGINX Controller is approaching retirement, which has pushed many teams to evaluate their long-term ingress strategy. The familiar Ingress resource has served well, but it comes with clear limits: annotations that differ by vendor, limited extensibility, and few options for separating operator and developer responsibilities.
The Gateway API addresses these challenges with a more expressive, standardized, and portable model for service networking. For organizations migrating off Ingress NGINX, the Calico Ingress Gateway, a production-hardened, 100% upstream distribution of Envoy Gateway, provides the most seamless and secure path forward.
If you’re evaluating your options, here are the five biggest reasons teams are switching now followed by a step-by-step migration guide to help you make the move with confidence.
Reason 1: The Future Is Gateway API and Ingress Is Being Left Behind
Ingress NGINX is entering retirement. Maintaining it will become increasingly difficult as ecosystem support slows. The Gateway API is the replacement for Ingress and provides:
- A portable and standardized configuration model
- Consistent behaviour across vendors
- Cleaner separation of roles
- More expressive routing
- Support for multiple protocols
Calico implements the Gateway API directly and gives you an Continue reading
UET Data Transfer Operation: Work Request Entity and Semantic Sublayer
Work Request Entity (WRE)
[SES part updated 7-Decembr 2025: text and figure]
The UET provider constructs a Work Request Entity (WRE) from a fi_write RMA operation that has been validated and passed by the libfabric core. The WRE is a software-level representation of the requested transfer and semantically describes both the source memory (local buffer) and the target memory (remote buffer) for the operation. Using the WRE, the UET provider constructs the Semantic Sublayer (SES) header and the Packet Delivery Context (PDC) header.
From the local memory perspective, the WRE specifies the address of the data in registered local memory, the length of the data, and the local memory key (lkey). This information allows the NIC to fetch the data directly from local memory when performing the transmission.
From the target memory perspective, the WRE describes the Resource Index (RI) table, which contains information about the destination memory region, including its base address and the offset within that region where the data should be written. The RI table also defines the allowed operations on the region. Because an RI table may contain multiple entries, the actual memory region is selected using the rkey, which is also included in the WRE. Continue reading
NB553: Palo Alto Networks Acquires Chronosphere; New Agentic AI Products for Orchestration and Networking
Take a Network Break! We start with a relative path traversal vulnerability in Fortinet’s FortiWeb. We’ll move on to an acquisition by Palo Alto Networks, another hiccup from our friends at Cloudflare, some AI announcements by Itential and Gluware, and finish with first quarter 2026 fiscal results from Palo Alto Networks. AdSpot Sponsor: Itential ... Read more »Tech Bytes: How IBM SevOne Delivers App-Centric Network Observability (Sponsored)
A lot of network monitoring tools allow you to say, “It’s not the network,” but a more useful tool would not only tell you that it’s not the network, but also what the problem actually is. Today our guest is Brandon Hale, CTO at IBM SevOne. He is here to give us an overview of... Read more »Get better visibility for the WAF with payload logging
As the surface area for attacks on the web increases, Cloudflare’s Web Application Firewall (WAF) provides a myriad of solutions to mitigate these attacks. This is great for our customers, but the cardinality in the workloads of the millions of requests we service means that generating false positives is inevitable. This means that the default configuration we have for our customers has to be fine-tuned.
Fine-tuning isn’t an opaque process: customers have to get some data points and then decide what works for them. This post explains the technologies we offer to enable customers to see why the WAF takes certain actions — and the improvements that have been made to reduce noise and increase signal.
Cloudflare’s WAF protects origin servers from different kinds of layer 7 attacks, which are attacks that target the application layer. Protection is provided with various tools like:
Managed rules, which security analysts at Cloudflare write to address common vulnerabilities and exposures (CVE), OWASP security risks, and vulnerabilities like Log4Shell.
Custom rules, where customers can write rules with the expressive Rules language.
Rate limiting rules, malicious uploads detection Continue reading
IOS/XR Route Redistribution Configuration Mess
One would hope that the developers of a network operating system wouldn’t feel the irresistible urge to reinvent what should have been a common configuration feature for every routing protocol. Alas, the IOS/XR developers failed to get that memo.
I decided to implement route redistribution (known as route import in netlab) for OSPFv2/OSPFv3, IS-IS, and BGP on IOS/XR (Cisco 8000v running IOS/XR release 24.4.1) and found that each routing protocol uses a different syntax for the source routing protocol part of the redistribute command.
Hedge 289: Containerlab
If you are struggling with building labs on lighter weight systems–or if you’re just interested in what Containerlab is and does–join Rick, Roman, and Russ for this discussion of what Containerlab is, what it does, and where its going.
TNO050: Resiliency and Transparency with Andy Lapteff
Today Scott interviews Andy Lapteff. He opens up about his non-linear career path, starting from a working class background and his physical jobs in telecom to becoming a senior product marketing manager and podcaster. Join us as Andy shares candid stories of how he developed his resilience and the heartwarming origin story for the Art... Read more »HN806: Let’s Get NUTS!
Unit testing is a software development practice for checking that an individual component of code works before integrating that unit with other components in a larger program. A new open source project called Network Unit Testing System, or NUTS, brings the same concept to network automation. The big idea is that by incorporating unit tests into... Read more »Public Videos: Bridging with EVPN
The EVPN in the Data Center and Bridging with EVPN parts of the EVPN webinar, featuring Dinesh Dutt, are now available without a valid ipSpace.net account. Enjoy!
IPB188: IPv6 Adoption for an Entire Country
What does it take for an entire country to adopt IPv6? Our guest today is Tenanoia (Noia) Simona, CEO of Tuvalu Telecommunications Corporation, the country’s sole telecommunications provider. She’s here to walk us through the difficulties of connecting the many islands of Tuvalu and their journey to achieving one of the world’s highest IPv6 adoption... Read more »N4N043: Redundancy vs. High Availability Part 1
In today’s chat, Holly and Ethan consider a question from listener Douglas who asks, “How do you approach designing a network for high availability and redundancy?” They start by defining differences between redundancy and high availability, and talk about Holly’s experience with her own customers. Then they share examples of how to achieve redundancy in... Read more »Building VXLAN/EVPN Data Center Lab with netlab
Dmitry Klepcha published an excellent document describing how you can use netlab to build a series of data center fabric labs, starting from a simple IP network (without routing) and finishing with a complex EVPN/VXLAN network using symmetric IRB and MLAG toward hosts.
But wait, there’s more: all the lab topologies he used in his exercises are available on GitHub, which means that you could just clone the repo and start using them (I also “borrowed” some of his ideas as future netlab improvements).
Finally, thanks a million to Roman Pomazanov for bringing Dmitry’s work to my attention (and for the quote at the end of his post ;).
D2DO287: Leveling Up in Data Science
Ever wonder what it takes to level up your career in data science? Senior Data Scientist Darya Petrashka joins Ned and Kyler to share her personal journey from management and linguistics into data science, the real difference between a junior and a senior role, and helps us get under the “data science umbrella” to see... Read more »Interesting: an MCP Agent for Link-State Routing Protocols
Vadim Semenov created a nice demo that allows you to use an LLM to query the collected link-state graphs through an MCP agent (SuzieQ would probably be faster and easier to deploy, but hey, AI).
If you want to kick the tires, you’ll find the source code on GitHub (Network AI assistant, MCP server for Topolograph service). You’ll also need Vadim’s previous projects: Topolograph and OSPF watcher or IS-IS watcher.