Getting Started with Packet Pushers Community Podcasting
We wrote this introductory guide to help those considering Packet Pushers community podcasting understand what is required. This is not a detailed list of everything you will need to know. Rather, this guide shares enough information to get you started. You'll still have to do a bit of Googling, research, and decision making of your own. We hope this helps. Happy podcasting!
The post Getting Started with Packet Pushers Community Podcasting appeared first on Packet Pushers.
iPexpert’s Newest “CCIE Wall of Fame” Additions 10/16/2015
Please join us in congratulating the following iPexpert students who have passed their CCIE lab!
A Look at the New WordPress Brute Force Amplification Attack
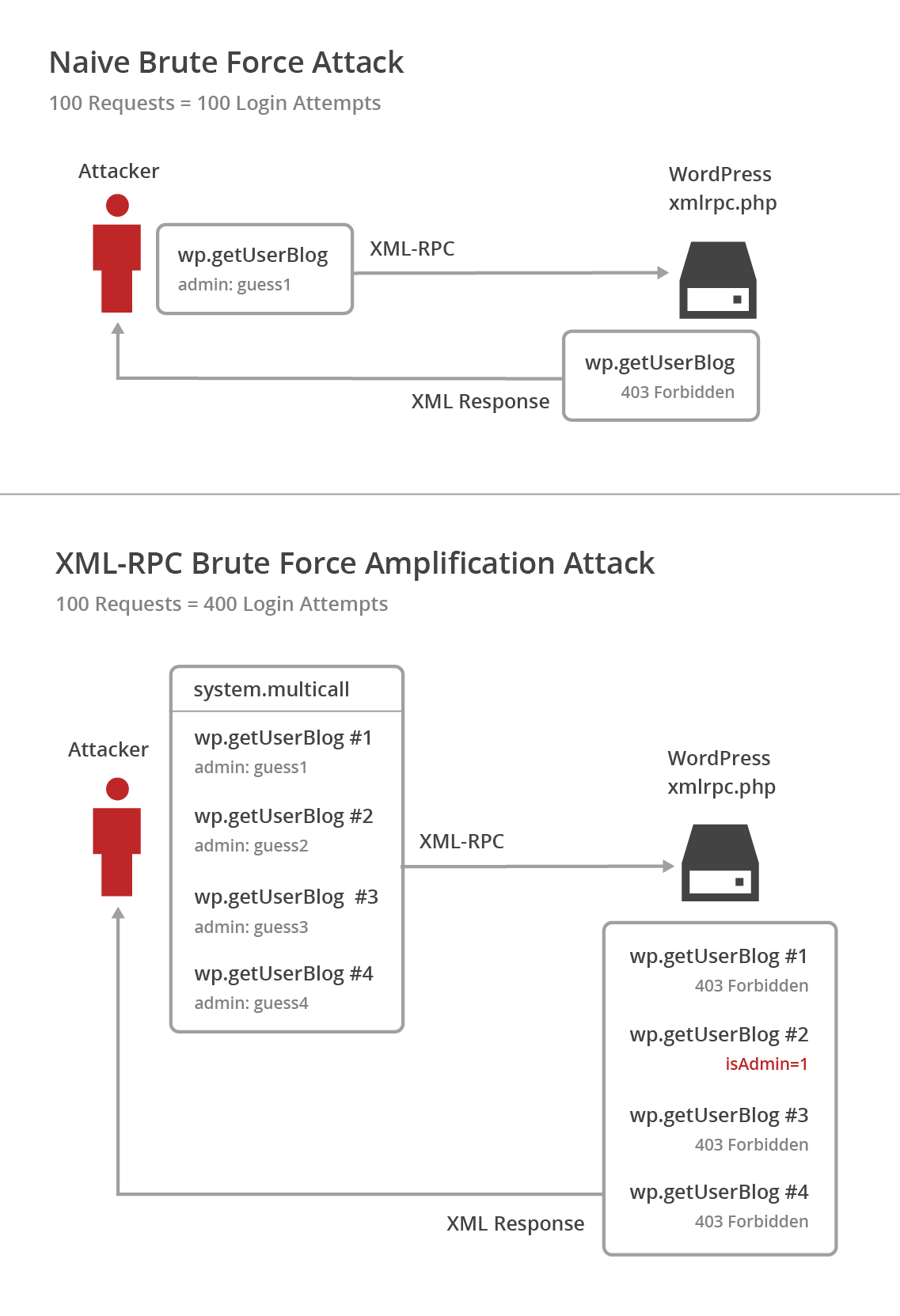
Recently, a new brute force attack method for WordPress instances was identified by Sucuri. This latest technique allows attackers to try a large number of WordPress username and password login combinations in a single HTTP request.
The vulnerability can easily be abused by a simple script to try a significant number of username and password combinations with a relatively small number of HTTP requests. The following diagram shows a 4-fold increase in login attempts to HTTP requests, but this can trivially be expanded to a thousand logins.
This form of brute force attack is harder to detect, since you won’t necessarily see a flood of requests. Fortunately, all CloudFlare paid customers have the option to enable a Web Application Firewall ruleset to stop this new attack method.
What is XML-RPC?
To understand the vulnerability, it’s important to understand the basics of the XML remote procedure protocol (XML-RPC).
XML-RPC uses XML encoding over HTTP to provide a remote procedure call protocol. It’s commonly used to execute various functions in a WordPress instance for APIs and other automated tasks. Requests that modify, manipulate, or view data using XML-RPC require user credentials with sufficient permissions.
Here is an example that requests a list Continue reading
Before adding solid-state drives, right-size your infrastructure using workload profiling
This vendor-written tech primer has been edited by Network World to eliminate product promotion, but readers should note it will likely favor the submitter’s approach.
If you’re looking to add Solid-State Drives to your storage environment you want to avoid under-provisioning to ensure performance and scalability, but to meet cost goals and avoid unnecessary spending you need to avoid over-provisioning. Workload profiling can help you achieve the critical balance.
A recent survey of 115 Global 500 companies by GatePoint Research and sponsored by Load DynamiX showed that 65% of storage architects say they are doing some sort of pre-deployment testing before making their investment decision. Alarmingly, only 36% understand their application workload I/O profiles and performance requirements. They don’t know what workload profiling is and how it can be used to accurately evaluate vendors against the actual applications that will be running over their particular storage infrastructure.
To read this article in full or to leave a comment, please click here
Radisys Integrates FlowEngine With Sanctum’s SDN Controller
 Radisys and Sanctum target CSPs with a blended SDN platform.
Radisys and Sanctum target CSPs with a blended SDN platform.
Musings on Datanauts #9
I listened to episode 9 of the excellent Datanauts podcast with Ethan Banks and Chris Wahl recently.Great job with this one, guys. I can tell how engaged I am in a podcast by how often I want to interrupt you :)
For this episode, that was lots of times!
Since I couldn't engage during the podcast, I'm going to have a one-sided discussion here, about the topics that grabbed my attention.
RARP?
Chris explained that the 'notify switches' feature of an ESXi vSwitch serves to update the L2 filtering table on upstream physical switches. This is necessary any time a VM moves from one physical link (or host) to another.
Updating the tables in all of the physical switches in the broadcast domain can be accomplished with any frame that meets the following criteria:
- Sourced from the VM's MAC address
- Destined for an L2 address that will flood throughout the broadcast domain
- Specifies an Ethertype that the L2 switches are willing to forward
Brocade DemoFriday Q&A + Video: Building a Real-World OpenStack NFV Deployment with L4-7 Services
 After its live presentation on how to build a real-world OpenStack NFV deployment with Layer 4-7 services, our DemoFriday presenters took questions from the audience. Read the full Q&A here!
After its live presentation on how to build a real-world OpenStack NFV deployment with Layer 4-7 services, our DemoFriday presenters took questions from the audience. Read the full Q&A here!
QOTW: Knowledge

Knowledge depends on the direction given to our passions and on our moral habits. To calm our passions is to awaken in ourselves the sense of the universal; to correct ourselves is to bring out the sense of the true.
Sertillanges, The Intellectual Life
The post QOTW: Knowledge appeared first on 'net work.
Defining SDN Down

If a WAN product that uses software to control the flow of traffic is an SD-WAN, and a data center than uses software to build a virtual topology is an SD-DC, and a storage product that uses software to emulate traditional hardware storage products is SD storage, and a network where the control plane has been pulled into some sort of controller an SDN, aren’t my profile on LinkedIn, and my twitter username @rtggeek software defined people (SDP)? A related question — if there are already IoT vendors, and the IoT already has a market, can we declare the hype cycle dead and move on with our lives? Or is hype too useful to marketing folks to let it go that easily? One thing we do poorly in the networking world is define things. We’re rather sloppy about the language we use — and it shows.
Back on topic, but still to the point — maybe it’s time to rethink the way we use the phrase software defined. Does SD mean one thing emulating another? Does SD mean centralized control? Does SD mean software controlled? Does SD mean separating the control plane from the data plane? Does SD mean OpenFlow?
IPv6 Implementation Guide: It’s Go Time
The time is now to deploy IPv6. Our guide covers protocol basics, IPv6 benefits, how to plan a dual-stack deployment, potential security issues and how to learn more.SDN Internet Router Is in Production on Software Gone Wild
You might remember the great idea David Barroso had last autumn – turn an Arista switch into an Internet edge router (SDN Internet Router – SIR). In the meantime, he implemented that solution in production environment serving high-speed links at multiple Internet exchange points. It was obviously time for another podcast on the same topic.
Read more ...