Connection Types with Network Automation and Ansible
Ansible is a great platform for network automation, but one of its quirks is its sometimes obtuse errors. I was running a playbook which logs into various Arista leafs and spines and does some tests. I’m using SSH to issue the commands (versus eAPI). I got this error:
fatal: [spine1]: FAILED! => {"changed": false, "msg": "Connection type ssh is not valid for this module"}One of the little things that trips me up when doing Ansible with network automation is the connection type.
When you’re automating servers (Ansible’s original use case) the connection type is assumed to be SSH, so the Ansible control node will log in to the node and perform some functions. The default connection type is “ssh”.
It’s a little counter-intuative, but even if you’re using SSH to get into network device, most network-centric modules won’t work. You need to use another connection type such as network_cli, which is part of the netcommon module collection. When you use network_cli, you also might have to specify a few other options such as network_os, become, and become_method.
ansible_connection: network_cli
ansible_network_os: eos
ansible_become: yes
ansible_become_method: enableIf your device has some sort of API, you can use httpapi as the Continue reading
Heavy Networking 670: The Challenges And Satisfactions Of Building And Running A Mastodon Instance
On today’s Heavy Networking I talk with two people who have built and are running Hachyderm, a Mastodon instance which orients itself towards technical-minded folks. What started as a cool project in the basement suddenly grew to tens of thousands of users. I talk with Hachyderm's founders on how they scaled, problems they encountered, how they solved problems, and how they grappled with technical and human challenges.
The post Heavy Networking 670: The Challenges And Satisfactions Of Building And Running A Mastodon Instance appeared first on Packet Pushers.
Heavy Networking 670: The Challenges And Satisfactions Of Building And Running A Mastodon Instance
On today’s Heavy Networking I talk with two people who have built and are running Hachyderm, a Mastodon instance which orients itself towards technical-minded folks. What started as a cool project in the basement suddenly grew to tens of thousands of users. I talk with Hachyderm's founders on how they scaled, problems they encountered, how they solved problems, and how they grappled with technical and human challenges.VyOS with Host sFlow agent
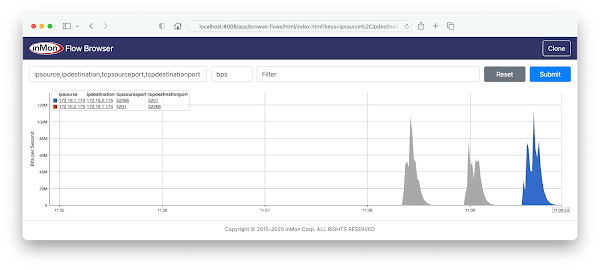
VyOS described deficiencies with the embedded sFlow implementation in the open source VyOS router operating system and suggested that the open source Host sFlow agent be installed as an alternative. The VyOS developer community embraced the suggestion and has been incredibly responsive, integrating, and releasing a version of VyOS with Host sFlow support within a week.vyos@vyos:~$ show versionVerify that the version of of VyOS is VyOS 1.4-rolling-202303170317 or later
Version: VyOS 1.4-rolling-202303170317
Release train: current
Built by: [email protected]
Built on: Fri 17 Mar 2023 03:17 UTC
Build UUID: 45391302-1240-4cc7-95a8-da8ee6390765
Build commit ID: e887f582cfd7de
Architecture: x86_64
Boot via: installed image
System type: guest
Hardware vendor: innotek GmbH
Hardware model: VirtualBox
Hardware S/N: 0
Hardware UUID: 871dd0f0-c4ec-f147-b1a7-ed536511f141
Copyright: VyOS maintainers and contributors
set system sflow interface eth0The above commands configure sFlow export in the VyOS CLI using the embedded Host sFlow agent.
set system sflow interface eth1
set system sflow interface eth2
set system sflow polling 30
set system sflow sampling-rate 1000
set system sflow server 10.0.0.30 port 6343
docker run --name sflow-rt -p 8008:8008 -p 6343:6343/udp -d sflow/prometheusA quick way to experiment with sFlow is to run the pre-built sflow/prometheus image Continue reading
Why SASE Shouldn’t Be Siloed
Hybrid networks aren’t going away, and by implementing an integrated SASE architecture, organizations can extend the convergence of networking and security from the edge to remote users.Cloudflare Access is the fastest Zero Trust proxy


During every Innovation Week, Cloudflare looks at our network’s performance versus our competitors. In past weeks, we’ve focused on how much faster we are compared to reverse proxies like Akamai, or platforms that sell serverless compute that compares to our Supercloud, like Fastly and AWS. This week, we’d like to provide an update on how we compare to other reverse proxies as well as an update to our application services security product comparison against Zscaler and Netskope. This product is part of our Zero Trust platform, which helps secure applications and Internet experiences out to the public Internet, as opposed to our reverse proxy which protects your websites from outside users.
In addition to our previous post showing how our Zero Trust platform compared against Zscaler, we also have previously shared extensive network benchmarking results for reverse proxies from 3,000 last mile networks around the world. It’s been a while since we’ve shown you our progress towards being #1 in every last mile network. We want to show that data as well as revisiting our series of tests comparing Cloudflare Access to Zscaler Private Access and Netskope Private Access. For our overall network tests, Cloudflare is #1 in Continue reading
Stop brand impersonation with Cloudflare DMARC Management


At the end of 2021 Cloudflare launched Security Center, a unified solution that brings together our suite of security products and unique Internet intelligence. It enables security teams to quickly identify potential security risks and threats to their organizations, map their attack surface and mitigate these risks with just a few clicks. While Security Center initially focused on application security, we are now adding crucial zero trust insights to further enhance its capabilities.
When your brand is loved and trusted, customers and prospects are looking forward to the emails you send them. Now picture them receiving an email from you: it has your brand, the subject is exciting, it has a link to register for something unique — how can they resist that opportunity?
But what if that email didn’t come from you? What if clicking on that link is a scam that takes them down the path of fraud or identity theft? And what if they think you did it? The truth is, even security minded people occasionally fall for well crafted spoof emails.
That poses a risk to your business and reputation. A risk you don’t want to take - no one does. Brand impersonation is a Continue reading
How we built DMARC Management using Cloudflare Workers

What are DMARC reports

DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It's an email authentication protocol that helps protect against email phishing and spoofing.
When an email is sent, DMARC allows the domain owner to set up a DNS record that specifies which authentication methods, such as SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail), are used to verify the email's authenticity. When the email fails these authentication checks DMARC instructs the recipient's email provider on how to handle the message, either by quarantining it or rejecting it outright.
DMARC has become increasingly important in today's Internet, where email phishing and spoofing attacks are becoming more sophisticated and prevalent. By implementing DMARC, domain owners can protect their brand and their customers from the negative impacts of these attacks, including loss of trust, reputation damage, and financial loss.
In addition to protecting against phishing and spoofing attacks, DMARC also provides reporting capabilities. Domain owners can receive reports on email authentication activity, including which messages passed and failed DMARC checks, as well as where these messages originated from.
DMARC management involves the configuration and maintenance of DMARC policies for a domain. Effective DMARC management requires ongoing monitoring and analysis Continue reading
Cloudflare partners with KnowBe4 to equip organizations with real-time security coaching to avoid phishing attacks


Today, we are very excited to announce that Cloudflare’s cloud email security solution, Area 1, now integrates with KnowBe4, a leading security awareness training and simulated phishing platform. This integration allows mutual customers to offer real-time coaching to their employees when a phishing campaign is detected by Cloudflare’s email security solution.
We are all aware that phishing attacks often use email as a vector to deliver the fraudulent message. Cybercriminals use a range of tactics, such as posing as a trustworthy organization, using urgent or threatening language, or creating a sense of urgency to entice the recipient to click on a link or download an attachment.
Despite the increasing sophistication of these attacks and the solutions to stop them, human error remains the weakest link in this chain of events. This is because humans can be easily manipulated or deceived, especially when they are distracted or rushed. For example, an employee might accidentally click on a link in an email that looks legitimate but is actually a phishing attempt, or they might enter their password into a fake login page without realizing it. According to the 2021 Verizon Data Breach Investigations Report, phishing was the most common form of social Continue reading
Introducing custom pages for Cloudflare Access


Over 10,000 organizations rely on Cloudflare Access to connect their employees, partners, and contractors to the applications they need. From small teams on our free plan to some of the world’s largest enterprises, Cloudflare Access is the Zero Trust front door to how they work together. As more users start their day with Cloudflare Access, we’re excited to announce new options to customize how those users experience our industry-leading Zero Trust solution. We’re excited to announce customizable Cloudflare Access pages including login, blocks and the application launcher.
Where does Cloudflare Access fit in a user’s workflow today?
Most teams we work with start their Zero Trust journey by replacing their existing virtual private network (VPN) with Cloudflare Access. The reasons vary. For some teams, their existing VPN allows too much trust by default and Access allows them to quickly build segmentation based on identity, device posture, and other factors. Other organizations deploy Cloudflare Access because they are exhausted from trying to maintain their VPN and dealing with end user complaints.
When those administrators begin setting up Cloudflare Access, they connect the resources they need to protect to Cloudflare’s network. They can deploy a Cloudflare Tunnel to create a secure, outbound-only, Continue reading
Case Study: Site Local NGINX
A while ago I rolled out an important change to the IPng Networks design: I inserted a bunch of [Centec MPLS] and IPv4/IPv6 capable switches underneath [AS8298], which gave me two specific advantages:
-
The entire IPng network is now capable of delivering L2VPN services, taking the form of MPLS point-to-point ethernet, and VPLS, as shown in a previous [deep dive], in addition to IPv4 and IPv6 transit provided by VPP in an elaborate and elegant [BGP Routing Policy].
-
A new internal private network becomes available to any device connected IPng switches, with addressing in 198.19.0.0/16 and 2001:678:d78:500::/56. This network is completely isolated from the Internet, with access controlled via N+2 redundant gateways/firewalls, described in more detail in a previous [deep dive] as well.
Overview

After rolling out this spiffy BGP Free [MPLS Core], I wanted to take a look at maybe conserving a few IP addresses here and there, as well as tightening access and protecting the more important machines that IPng Networks runs. You see, most enterprise networks will include a bunch of internal services, like databases, network attached storage, backup servers, network monitoring, Continue reading
Video: vPC Fabric Peering with EVPN Multihoming
After implementing MLAG functionality with EVPN and having a VXLAN-like fabric transport path between MLAG members, it becomes possible to get rid of the MLAG peer link.
Not surprisingly, most implementations of virtual MLAG peer link remain proprietary. Lukas Krattiger described the details of Cisco’s vPC Fabric Peering implementation in the EVPN Deep Dive webinar.
Video: vPC Fabric Peering with EVPN Multihoming
After implementing MLAG functionality with EVPN and having a VXLAN-like fabric transport path between MLAG members, it becomes possible to get rid of the MLAG peer link.
Not surprisingly, most implementations of virtual MLAG peer link remain proprietary. Lukas Krattiger described the details of Cisco’s vPC Fabric Peering implementation in the EVPN Deep Dive webinar.
Critical Thinking: The Overlooked IT Management Skill
Have you given much thought to critical thinking? It’s a talent that can make you a stronger, more effective leaderWAF is woefully insufficient in today’s container-based applications: Here’s why
According to the Cloud Security Alliance, the average large enterprise has 946 custom applications deployed. Traditionally, organizations deployed Web Application Firewalls (WAF), which provide visibility and enforce security controls on external traffic that passes through them, at the perimeter to protect these applications against external attacks.
However, WAF-secured container-based applications have a high likelihood of being breached, as the concept of a perimeter does not exist in these architectures. A new approach is needed to address both external threats and threats from lateral movement inside the cluster. In a world where successful exploits may be inevitable, relying on a perimeter WAF for application security leaves your entire environment vulnerable unless adequate security tools and policies are implemented at the workload level.
WAF’s weak security
Security techniques for traditional container-based application architectures are analogous to medieval castles, where everything important to running an application is consolidated within castle walls. In this analogy, WAF played the role of the wall and gate, only letting in friendly traffic.
WAF provides additional capabilities in these traditional architectures. It actively parses through valid requests and threats and provides alerts when it receives suspicious log requests. These alerts keep the security team apprised of threats Continue reading
Kubernetes Unpacked 021: Catching Up With Windows Containers On Kubernetes
On today's Kubernetes Unpacked, Michael and guests explore Windows containers. A few years ago there was a lot of hype around Nano, which then morphed into Nano Server. We look at the current state of containerized Windows, using Windows containers with Kubernetes, customer scenarios for container adoption, and Microsoft's approach to the container space.
The post Kubernetes Unpacked 021: Catching Up With Windows Containers On Kubernetes appeared first on Packet Pushers.
Kubernetes Unpacked 021: Catching Up With Windows Containers On Kubernetes
On today's Kubernetes Unpacked, Michael and guests explore Windows containers. A few years ago there was a lot of hype around Nano, which then morphed into Nano Server. We look at the current state of containerized Windows, using Windows containers with Kubernetes, customer scenarios for container adoption, and Microsoft's approach to the container space.Post-quantum crypto should be free, so we’re including it for free, forever


At Cloudflare, helping to build a better Internet is not just a catchy saying. We are committed to the long-term process of standards development. We love the work of pushing the fundamental technology of the Internet forward in ways that are accessible to everyone. Today we are adding even more substance to that commitment. One of our core beliefs is that privacy is a human right. We believe that to achieve that right the most advanced cryptography needs to be available to everyone, free of charge, forever. Today, we are announcing that our implementations of post-quantum cryptography will meet that standard: available to everyone, and included free of charge, forever.
We have a proud history of taking paid encryption products and launching it to the Internet at scale for Free. Even at the cost of short and long-term revenue because it’s the right thing to do. In 2014, we made SSL free for every Cloudflare customer with Universal SSL. As we make our implementations of post-quantum cryptography free forever today, we do it in the spirit of that first major announcement:
“Having cutting-edge encryption may not seem important to a small blog, but it is critical to advancing the encrypted-by-default Continue reading