IPv4 Address Transfer Prices Down?
Last year I wrote about the IPv4 Address Transfer Process. Recently I was involved in another IPv4 transfer. I was surprised to see that IPv4 prices have fallen in the last year. I have done some rudimentary analysis of the APNIC transfer statistics to try to figure out why.
APNIC publishes statistics on transfers at ftp.apnic.net/public/transfers/apnic. These text files list all resource transfers that have taken place – the to & from organisation, the resource type, the date, etc. I am very interested in looking at the trends. How many transactions take place each month, and how many addresses are being transferred?
I wrote a simple Python script to do this analysis for me. It retrieves the latest statistics, and converts them into a Google chart:
(If you’re reading this via RSS, and the chart doesn’t display, you may need to click here to see the web version).
Note this does not do live updates. It is a point in time, generated using the current data at the time the script is run. If you would like to update the code to do live updates, fork it from Github here. I’d also love to update the script to Continue reading
Replacing Central Router with a Next-Generation Firewall?
One of my readers sent me this question:
After reading this blog post and a lot of blog posts about zero trust mode versus security zones, what do you think about replacing L3 Data Center core switches by High Speed Next Generation Firewalls?
Long story short: just because someone writes about an idea doesn’t mean it makes sense. Some things are better left in PowerPoint.
Read more ...Walking with Packets: Traceroute Through MPLS Cloud
Think about this for a minute: An MPLS network with a two Provider Edge (PE) routers and some Provider (P) routers. The P routers have no VRFs configured on them and therefore have no routes whatsoever for any of the customer networks. A customer then does a traceroute from one of their sites, across the MPLS cloud, and into one of their other sites. The traceroute output shows the P routers as hops along the path.
How is it possible for the P routers to reply to the traceroute if they don't have routes back to the customer network?
Decapsulation ERSPAN Traffic With Open Source Tools
Cisco Encapsulated Remote SPAN (ERSPAN) feature allows to monitor traffic on one or more ports and send the monitored traffic to one orDecapsulation ERSPAN Traffic With Open Source Tools
Cisco Encapsulated Remote SPAN (ERSPAN) feature allows to monitor traffic on one or more ports and send the monitored traffic to one or more destination ports. Traffic is encapsulated into GRE tunnel and routed via network to ERSPAN destination. Any device that supports ERSPAN can be used as ERSPAN destination. It might be another Cisco device or Linux with installed software that can decapsulate GRE traffic.
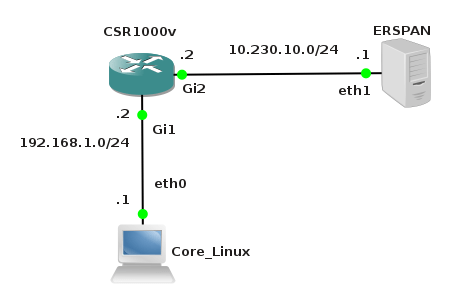
The goal of this article is to show methods and tools for decapsulation of ERSPAN traffic. For this purpose I have built simple lab that consists of a Cisco CSR 1000v router and two Linux boxes. Core Linux represents a network host and generates network traffic (ICMP) that is going to be monitored. It is connected to the port GigabitEthernet1 of the Cisco router. The router is configured to monitor traffic on the port Gi1 and it sends traffic encapsulated in GRE tunneling protocol to IP address 10.230.10.1. It is the IP address of the ERSPAN destination configured on Linux Security Union. Security Onion is a unique Linux distro for intrusion detection, network security monitoring, and log management based on Ubuntu however any other Linux distro can be used.
Picture 1 - ERSPAN Lab Topology
Below is an example of ERSPAN Continue reading
MPLS VPN
Thought I would put this on here, makes use of an MPLS backbone which allows for multiple VRF's to exist.Original blog post which covers50 000 Page views of orhanergun.net between March-May 2015
This blog received 50 000 page views between 1 of March and 1 th of May.I shared you couple more metrics from the site stats in addition to Pageviews. Since at the same time two classes I teach ( Pre-CCDE and CCDE ) in addition to my other jobs, I couldn’t update the blog since… Read More »
The post 50 000 Page views of orhanergun.net between March-May 2015 appeared first on Network Design and Architecture.