Docker Networking – CoreOS Flannel
This blog is part of my ongoing series on Docker containers. In this blog, I will cover Flannel which is a CoreOS networking solution to connect containers across multiple hosts. Please refer to my first blog on CoreOS to understand CoreOS basics as well as how to setup CoreOS cluster. Flannel Overview: Flannel creates an … Continue reading Docker Networking – CoreOS FlannelCoreOS overview
This blog is part of my ongoing series on Docker containers. In this blog, I will cover basics of CoreOS and some hands-on stuff I tried with CoreOS. As mentioned in my other blog on Docker orchestration, CoreOS falls in the category of specialized Linux distributions that can host Containers and are suitable for massive server deployments. … Continue reading CoreOS overviewDocker Networking – Weave
This blog is part of my ongoing series on Docker containers. Weaveworks is developing a Docker Networking solution to connect Containers. I recently played around with their solution and in this blog, I will capture some of my thoughts. Following are some internals on their implementation as I understood: Weave creates a Weave bridge as well as … Continue reading Docker Networking – WeaveDocker Networking – Socketplane
This blog is part of my ongoing series on Docker containers. In my previous blogs 1 and 2, I covered basics of Docker Networking and also covered some of the limitations with the current solutions. In the next few blogs, I will cover Docker Networking solutions from Socketplane, Weaveworks, CoreOS. Socketplane is developing a Docker networking … Continue reading Docker Networking – SocketplaneWelcome to MovingPackets.NET!
Welcome to my new home! If you’ve come over here because you used to read my drivel on LameJournal, then thank you! If you’re a new visitor, you are very welcome and I hope you choose to subscribe by RSS or Email so you can get notified of new posts.
MovingPackets.net is the new name for LameJournal. All the networking and computer-related content from LameJournal has been duplicated here at MovingPackets, but the photography content is gone and I’ll attempt to stay focused on things related to moving packets around as I post here going forward.
I have a new site theme, and with the new name as well, things are still likely to change a bit here visually (I have no logo yet for example). Still, there’s no time like the present so I decided to launch the site and I’ll tweak things as we go along with the aim of making the content more easily accessible. I hope you like my new home; it’s going to take a while before it feels comfortable!
Thanks for stopping in at MovingPackets.
John.
If you liked this post, please do click through to the source at Welcome to MovingPackets.NET! and give me a share/like. Thank you!
MovingPackets.NET – The New Name for LameJournal
I’ve been quiet lately, mostly because I’ve been horribly busy but also in part because I’ve been thinking that it’s about time to rebrand LameJournal to something that better reflects the content. And to that end, MovingPackets.net has been born. All the … Continue reading
If you liked this post, please do click through to the source at MovingPackets.NET – The New Name for LameJournal and give me a share/like. Thank you!
QoS Design Notes for CCDE
Trying to get my CCDE studies going again. I’ve finished the End to End QoS Design book (relevant parts) and here are my notes on QoS design.
Basic QoS
Different applications require different treatment, the most important parameters are:
- Delay: The time it takes from the sending endpoint to reach the receiving endpoint
- Jitter: The variation in end to end delay between sequential packets
- Packet loss: The number of packets sent compared to the number of received as a percentage
Characteristics of voice traffic:
- Smooth
- Benign
- Drop sensitive
- Delay sensitive
- UDP priority
One-way requirements for voice:
- Latency ≤ 150 ms
- Jitter ≤ 30 ms
- Loss ≤ 1%
- Bandwidth (30-128Kbps)
Characteristics for video traffic:
- Bursty
- Greedy
- Drop sensitive
- Delay sensitive
- UDP priority
One-way requirements for video:
- Latency ≤ 200-400 ms
- Jitter ≤ 30-50 ms
- Loss ≤ 0.1-1%
- Bandwidth (384Kbps-20+ Mbps)
Characteristics for data traffic:
- Smooth/bursty
- Benign/greedy
- Drop insensitive
- Delay insensitive
- TCP retransmits
Quality of Service (QoS) – Managed unfairness, measured numerically in latency, jitter and packetloss
Quality of Experience (QoE) – End user perception of network performance, subjective and can’t be measured
Tools
Classification and marking tools: Session, or flows, are analyzed to determine what class the packets belong to Continue reading
NFD9 Prep: NetBeez
I’m reviewing the presenters for Network Field Day 9, in particular looking at those I’m not familiar with. NetBeez is one of those making their first Tech Field Day appearance.
NetBeez
We all know that our users and the applications they access are incredibly distributed. We don’t control all the network elements, but the network team still gets the blame if things go wrong. You need greater visibility to prove it’s not the network, but getting that visibility is tough. Current options for probes aren’t always cost-effective to deploy across many sites. Many sites don’t have any local server infrastructure.
That’s where NetBeez comes in. They have developed Raspberry Pi-based agents that can easily be deployed to many locations. Plug in power, plug in a network cable, and it phones home. Go to the NetBeez dashboard, and from there you can configure the tests you want the agent to run.
Since the devices are so small, they can easily be deployed to a range of small sites, and can simulate a range of user traffic. Tests include Ping, HTTP, Traceroute, DNS. A particularly nice feature is the ability to run an ad-hoc iPerf test with custom parameters.
The dashboard shows you how the Continue reading
It’s About Application Delivery, Not Networking
Send to Kindle@DrDust tweets: @packetpushers – at the beginning you appeared very Cisco centric. Now not so much. What do you guys “like” working on? Be warned, @DrDust. This is probably not the post you’re looking for. But it’s where my mind went after reading your question. ;-) On Early Cisco-centrism I don’t especially remember that […]CCDE Practical exam preparation – Podcast
Wouldn’t you want to listen the story from the guys who passed the CCDE exam ? What are their CCDE Recommended reading list ? Is there any CCDE Training which they suggest for CCDE Preparation? Which technologies they recommend for the CCDE candidates to focus ?
The post CCDE Practical exam preparation – Podcast appeared first on Network Design and Architecture.
PlexxiPulse—Interested in joining our team?
If you’ve been following our blog and/or keeping up with Plexxi on social media, you may have noticed that there is a lot going on here. We recently introduced new product starter kits, began construction on our new office expansion, are working on some exciting projects, and have grown by 20 percent in the past two months. Are you interested in being a part of the Plexxi team? If so, we would love to hear from you. Check out our careers page for more information.
Below you will find our top picks for stories in the networking space this week. Have a great weekend!
In this week’s PlexxiTube video of the week, Dan Backman explains how Plexxi’s datacenter transport fabric works with optical transport gear.
Light Reading: New Plexxi Chief Makes His Mark
By Mitch Wagner
As he enters his third month in the big chair, new Plexxi CEO Rich Napolitano is retooling the company’s messaging to focus more on the benefits of software networks — using Plexxi technology, of course — and less on the abstract benefits of SDN. Napolitano took over as CEO in November after 30 years in the technology industry, most recently at EMC Continue reading
Sizing up the three popular Internet TV streaming sticks
If you’re like most folks, the back of your home entertainment center is a hive of HDMI cables, USB cords and power adaptors, not to mention the HDMI switchers necessary to cope with this cornucopia of entertainment providers. Thankfully, there is a solution: The increasingly popular streaming stick.
These Internet TV streaming devices will be the savior of every gadget-obsessed, cable-cluttered geek out there. These chewing gum-sized streaming devices can pipe the whole wide, weird and wonderful Internet into your television, with a lot less of the cable mess than you’re dealing with now.
Currently available in one of three flavors—Roku's Stick ($50), Google's Chromecast ($35), and Amazon's Fire Stick ($39)— these three devices can deliver pretty much any online content you could wish for directly to your living room. Here's a look at what these sticks have to offer:
To read this article in full or to leave a comment, please click here
CCDE Practical Exam Blueprint
What is in the CCDE Practical exam blueprint ? If you passed CCDE Written ( 352-001 ) already, practical exam is the only barrier between you and certificate ! Below blueprint is the first step for your CCDE journey. You will know that what are the concepts which you need to be an expert !
The post CCDE Practical Exam Blueprint appeared first on Network Design and Architecture.
Cisco Certified Design Expert ( CCDE ) Written exam topics
You can see CCDE Written Exam ( 352-001 ) blueprint below. For those who want to start their CCDE journey , probably knowing the topics is the first step.
The post Cisco Certified Design Expert ( CCDE ) Written exam topics appeared first on Network Design and Architecture.
How can router decide so fast?
How does Internet work - We know what is networking
Cisco created all sorts of different magic inside their boxes that optimize forwarding processing of packets. Main router function is fairly self-explanatory. Router performs IP forwarding more often called IP routing. IP routing is process of deciding where to send the packet after it was received. IP Routing explained in detail Logic behind IP forwarding is listed in steps here with the assumption it will be an IPv4 packet that was received. This is process switching explained in 11 steps: A frame enters the one of router’s interface First thing that router does is to check frame
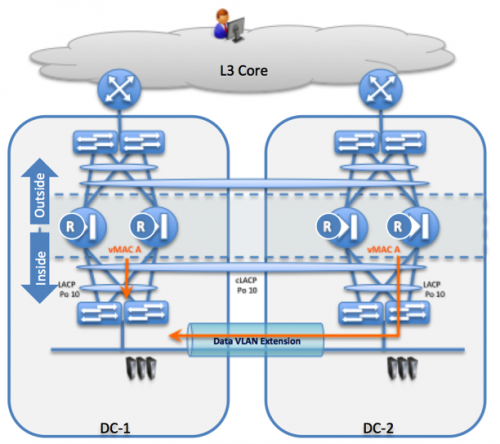
27 – Bis-Bis – Stateful Firewall devices and DCI challenges – Part 1 (cont)
Back to the recent comments on what is “officially” supported or not ?
First of all, let’s review the different Firewall forwarding mode officially supported
ASA cluster deployed inside a single data center:
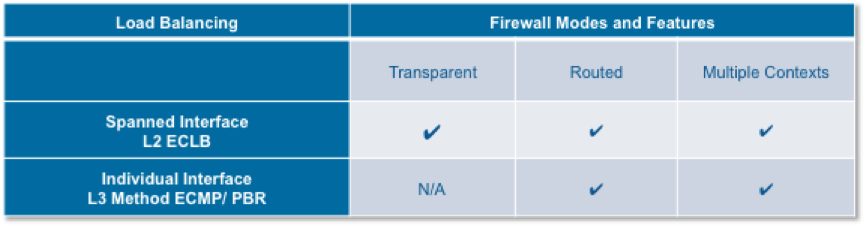 Fig.1 Firewall forwarding mode within a single DC. Please note the firewall routed mode supported with the Layer 2 load balancing (LACP) Spanned Interface mode.
Fig.1 Firewall forwarding mode within a single DC. Please note the firewall routed mode supported with the Layer 2 load balancing (LACP) Spanned Interface mode.
When configured in Routed mode (e.g. default gateway for the machines), the same ASA identifiers IP/MAC are distributed among all ASA members of the cluster. When the ASA cluster is stretched across different locations, the Layer 2 distribution mechanism facing the ASA devices is achieved locally using pair of switches (usually leveraged the a Multi-chassis EthernetChannel technique such as VSS or vPC).
Subsequently the same virtual MAC address (ASA vMAC) of the ASA cluster is duplicated on both sites and as the result it hits the upward switch from different interfaces.
Fig.2 ASA and duplicate vMAC address
When the ASA cluster runs the firewall routed mode with Spanned interface method, it breaks the Ethernet rules due to the duplicate MAC address, with risks of affecting the whole network operation. Consequently Continue reading
SDN Router @ Spotify on Software Gone Wild
Imagine you need a data center WAN edge router with multiple 10GE uplinks. You’d probably go for an ASR or a MX-series router, right? How about using a 2 Tbps ToR switch and an SDN solution to make it work with full Internet routing table?
If you happen to have iTunes on your computer, please spend 10 seconds rating the podcast before you start listening to it. Thank you!
Read more ...The Importance of Product Education
 I learned something new this afternoon. While other users of this product were already aware of it, I was not. This is something that is specific to the Wi-Fi community, but there is a larger point affecting all practitioners of technology that I will attempt to illustrate in this post.
I learned something new this afternoon. While other users of this product were already aware of it, I was not. This is something that is specific to the Wi-Fi community, but there is a larger point affecting all practitioners of technology that I will attempt to illustrate in this post.
The Problem
I have been doing a lot of wireless surveys lately. These particular surveys have been large enough to require two engineers to be on site. We’ll divide up the location by floors or sections in order to get the job done in less time. These particular surveys are in place assessments, so we aren’t putting survey AP’s up on poles and measuring signal strength, determining attenuation of walls, etc. We’re simply measuring the signal of all AP’s in place and making recommendations based on the requirements of the business(e.g. moving to support voice at 5GHz or location based services). In addition to using a survey tool, which in our case is Ekahau’s Site Survey, we are also doing spectrum analysis at various points within the given facility with Metageek’s Wi-Spy DBx hardware and Chanalyzer software.
The spectrum analysis portion is where my problem resided. I happen to have a pair Continue reading
Golang for Network Ops
I get asked quite often where the traditional network engineer / network ops should start if they want to broaden their horizons with better code hacking skills or they have spent the last 20 years using Perl scripts or more recently Python and need a change. The answer is easy, Golang. At Socketplane, we all ditched the past couple of ... The post Golang for Network Ops appeared first on NetworkStatic | Brent Salisbury's Blog....
Show 221 – Marriott, Wifi, + the FCC with Glenn Fleishman & Lee Badman
A funny thing happened on Twitter a week or so ago. I saw this message from Glenn Fleishman. If anyone wants me on a podcast to explain why Marriott wants the FCC to give it license to block personal hotspots, let’s talk. — Glenn Fleishman (@GlennF) January 2, 2015 I thought that the topic would be a […]
Author information
The post Show 221 – Marriott, Wifi, + the FCC with Glenn Fleishman & Lee Badman appeared first on Packet Pushers Podcast and was written by Ethan Banks.