Reverse Proxy + Cache for Minecraft
Reverse Proxy + Cache for Minecraft
One of the things that I like to play from time to time is Minecraft, however one of things ( at least with me this is ) is that Minecraft is best played with other people, This however means you have to go throu
Nested Virtualization
A typical Network Virtualization demo is difficult as you need quite some hypervisor hosts to run some VMs on and interconnect them using Overlays. I solve this using nested virtualization. This means that I run a hypervisor running on another. This gives me the flexibility that my physical nodes, or “hypervisor underlay” if you will, can scale easily and I’m independent of them.
My physical cluster consists of 2 nodes running ESXi with vCenter. On top of that I’m running 4 other ESXi hosts divided in 2 “virtual” clusters and 4 KVM hosts as Contrail Compute Nodes.
How does this work?
This technology works using Intel’s VT-x (which is hardware assisted virtualization) and EPT (to virtualise memory allocations). This combination works since the “Nehalem” arch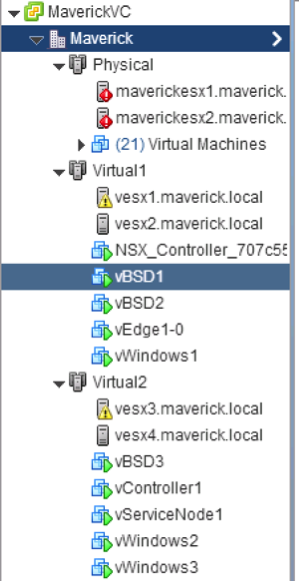 itecture (released 2008). The technology is ported to the more “Desktop” oriented CPU’s as well, so there is a good chance your notebook supports it as well. Since the Haswell architecture the nested virtualization works even better as Intel now supports VMCS Shadowing for nested VMs, which creates a data structure in memory per VM (and now supports nested VMs as well, which used to be a software effort).
itecture (released 2008). The technology is ported to the more “Desktop” oriented CPU’s as well, so there is a good chance your notebook supports it as well. Since the Haswell architecture the nested virtualization works even better as Intel now supports VMCS Shadowing for nested VMs, which creates a data structure in memory per VM (and now supports nested VMs as well, which used to be a software effort).
Memory is the biggest burden in these Continue reading
Notes from NANOG 63
This is a selected summary of the recent NANOG 63 meeting, held in early February, with some personal views and opinions thrown in.Cisco Live in San Diego – Will You Make It?
“Make it” was one of the first singles released by the the band Aerosmith. Since then these guys have been rocking away for about 40 years. What does this have to do with Cisco Live? Aerosmith will be the band playing at the Customer Appreciation Event (CAE). A good time is pretty much guaranteed. Aerosmith knows how to entertain a crowd.
The CAE will take place at Petco Park, the home of the San Diego Padres. This photo shows the arena in the evening, looks quite spectacular to me.
Cisco Live is much more than just having fun though. If you want to make it in the IT industry, there is a lot to gain by going to Cisco Live. Here are some of my reason why I want to go:
- Stay on top of new technologies – Where is ACI going?
- Dip my toes into other technologies that I find interesting
- Gain deep level knowledge of platforms or features that will benefit me and my customers
- Go to sessions that will aid me on my certification path
- Connect with people!
- Learn a lot while having fun at the same time!
- Learn from the experience of others
When you are Continue reading
Unified/Seamless MPLS
In this post I would like to highlight a relative new (to me) application of MPLS called Unified MPLS.
The goal of Unified MPLS is to separate your network into individual segments of IGP’s in order to keep your core network as simple as possible while still maintaining an end-to-end LSP for regular MPLS applications such as L3 VPN’s.
What we are doing is simply to put Route Reflectors into the forwarding path and changing the next-hop’s along the way, essentially stiching together the final LSP.
Along with that we are using BGP to signal a label value to maintain the LSP from one end of the network to the other without the use of LDP between IGP’s.
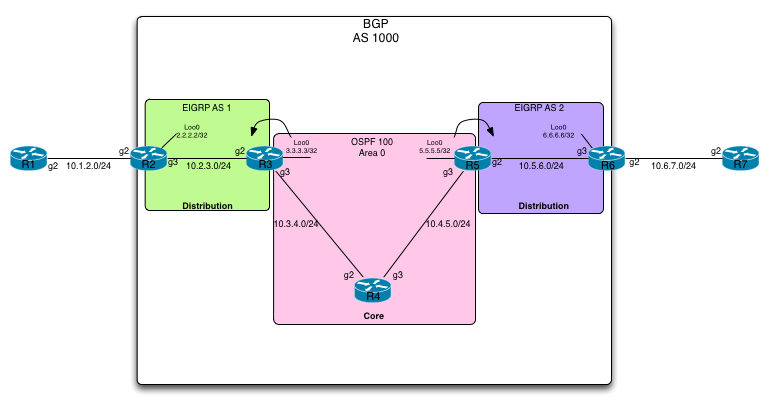
Take a look at the topology that we will be using to demonstrate this feature:
In this topology we have a simplified layout of a service provider. We have a core network consisting of R3, R4 and R5 along with distribution networks on the right and left of the core. R2 and R3 is in the left distribution and R5 and R6 is in the right hand side one.
We have an MPLS L3VPN customer connected consisting of R1 in one site Continue reading
STP Notes for CCDE
These are my study notes for CCDE based on “CCIE Routing and Switching v5.0 Official Cert Guide, Volume 1, Fifth Edition” and “Designing Cisco Network Service Architectures (ARCH) Foundation Learning Guide: (CCDP ARCH 642-874), Third Edition“, “INE – Understanding MSTP” and “Spanning Tree Design Guidelines for Cisco NX-OS Software and Virtual PortChannels“. This post is not meant to cover STP and all its aspects, it’s a summary of key concepts and design aspects of running STP.
STP
STP was originally defined in IEEE 802.1D and improvements were defined in amendments to the standard. RSTP was defined in amendment 802.1w and MSTP was defined in 802.1s. The latest 802.1D-2004 standard does not include “legacy STP”, it covers RSTP. MSTP was integrated into 802.1Q-2005 and later revisions.
STP has two types of BPDUs: Configuration BPDUs and Topology Change Notification BPDUs. To handle topology change, there are two flags in the Configuration BPDU: Topology Change Acknowledgment flag and Topology Change flag.
MessageAge is an estimation of the age of BPDU since it was generated by root, root sends it with an age of 0 and other switches increment this Continue reading
Away from WordPress to Jekyll on Github
Recently I seriously considered shutting down the blog. I wasn't writing as often as I wanted. It was costing money to keep up, the free services...[[ Summary content only, you can read everything now, just visit the site for full story ]]
IT Security Skills Anyone Can and Should Learn
I’ve been teaching IT security awareness for several years and I try to get those in attendance of the classes to learn some basic IT security skills. These basic skills build on each other and there is some cross over, but ultimately this blended set of security skills can help anyone stay safe online. As with any sport you always start by learning the fundamentals, and while no one skill can get you into the game or keep you safe online, they can definitely make you ready for either.
Physical Security
With free Wi-Fi available in coffee shops and many fast food restaurants I constantly see people leaving their devices unattended and this lapse can allow someone to walk off with the device unnoticed. Think about your device and the amount of data it may contain. The device may have your whole world stored on it! If someone takes your laptop, tablet, or phone it is so much more than having the device stolen, but the data it contains. Besides this Wi-Fi example other scenarios to pay attention to your device is when going through airport security or leaving the device in plain site while stored in the car. Continue reading
Finding Older Articles While The Blog is Migrated
If you hadn't noticed, the Revolution Wi-Fi website was recently migrated from Blogger to Squarespace. While I like the new look on the website, some of the features on the old site aren't yet replicated on the new site. Additionally, cached web search results still point to old URLs causing "webpage not found" errors from Google and others.
If you're looking for older blog posts or pages, you have two options:
- Go to the old website still at http://www.revolutionwifi.blogspot.com
OR - Add the "/revolutionwifi/" directory into URL address for any blog post
Example:
http://revolutionwifi.net/2013/05/apple-ios-fast-roaming-with-aerohive-wi.html
Becomes:
http://revolutionwifi.net/revolutionwifi/2013/05/apple-ios-fast-roaming-with-aerohive-wi.html
Additionally, all of the categorized article topics are available on the old website at http://revolutionwifi.net/revolutionwifi/p/article-archives-by-topic.html
Finally, I've fixed all of the old URL links embedded within blog posts that were broken right after the blog migration due to the different directory structure. Ugh! But I've fixed this now... so all good there :)
I will also be adding Search and Categories to the new website once I have time. Thanks for your patience while I complete this work!
Cheers,
Andrew von Nagy
Away from WordPress to Jekyll on Github
My move from Wordpress self hosted to Jekyll on Github[[ Summary content only, you can read everything now, just visit the site for full story ]]
Away from WordPress to Jekyll on Github
Recently I seriously considered shutting down the blog. I wasn’t writing as often as I wanted. It was costing money to keep up, the free services are really sub-par from what I’ve experienced. It...[[ Summary content only, you can read everything now, just visit the site for full story ]]
Away from WordPress to Jekyll on Github
Recently I seriously considered shutting down the blog. I wasn’t writing as often as I wanted. It was costing money to keep up, the free services are really sub-par from what I’ve experienced. It...[[ Summary content only, you can read everything now, just visit the site for full story ]]
Use Rate-Limiting to Alleviate Link Saturation
At some point in time you may come across a scenario in which you notice a WAN link at a branch site is being saturated. You then have to weigh your options to mitigate the saturation because it can cause intermittent network outages and other issues. In this scenario we will use rate-limiting on the […]
Author information
The post Use Rate-Limiting to Alleviate Link Saturation appeared first on Packet Pushers Podcast and was written by Korey Rebello.
Cisco Live 2015 – Customer Appreciation Event Featuring Aerosmith!!
Yes, you heard me right. Aerosmith!

One of the most looked forward to social events for Cisco Live has always been the Customer Appreciation Events (CAE). Cisco rarely let’s us down when throwing this shindig, and has amazed us in the past with renting out resorts, baseball stadiums, and even Universal Studios.
This year, the CAE will be held on Wednesday June 10th at 7:30 inside Petco Park which is just a short walk from the convention center. With Aerosmith headlining this event it is sure to be huge! So if you haven’t already registered for CLUS15, be sure to do so NOW!!!
In other news, it seems that CDW is sponsering a new outdoor social media area for us to connect and hang out by the waterfront. Currently I believe this to be in addition to the normal social media hub that Cisco has been providing us since 2012.
This rendering of the area seems to indicate that it is located behind the convention center, probably in this area…
If you have any questions about this years event please reach out to @CiscoLive on twitter, or on Facebook!
The post Cisco Live 2015 – Customer Appreciation Event Continue reading
Cisco Live 2015 – Announcements – I Don’t Want to Miss a Thing
In case the above video has not given it away, the CAE band on Wednesday June 10th @ 7:30 at Petco Park for Cisco Live 2015 is none other than Aerosmith! We have had some great bands over the years (KISS, Lenny Kravitz, Imagine Dragons, OK GO, just to name a few) and I suspect that this […]
The post Cisco Live 2015 – Announcements – I Don’t Want to Miss a Thing appeared first on Fryguy's Blog.
iPexpert’s Newest “CCIE Wall of Fame” Additions 2/06/2015
Please join us in congratulating the following iPexpert client’s who have passed their CCIE lab!
This Week’s CCIE Success Stories
- Shawn Wilson, CCIE #46739 (Collaboration)
- Gaurav Sharma, CCIE #44785 (Data Center)
- Theogene Nishimwe, CCIE #44776 (Collaboration)
- Rakesh Jain, CCIE #44775 (Collaboration)
We Want to Hear From You!
Have you passed your CCIE lab exam and used any of iPexpert’s self-study products, or attended a CCIE Bootcamp? If so, we’d like to add you to our CCIE Wall of Fame!
Plexxi Pulse – Big Data is Driving Datacenter Infrastructure Development
You may have seen last week that we partnered with Cloudera, certifying the Plexxi Switch on Cloudera’s Enterprise 5 platform.
This partnership, while exciting for us and our partners, plays a larger role in the IT landscape as a whole. According to an article this week by Arthur Cole of Enterprise Networking Planet, this move embodies Cole’s belief that networking infrastructure development is increasingly being driven by Big Data applications. He cites the key challenge as not finding somewhere to store all the data (e.g. storage) but rather how to make it available to “diverse and disparate sets of resources quickly and at a relatively low cost.”
He closes out with his piece by admitting that there’s still progress to be made with this technology. Nevertheless, we’re proud to be leading the charge.
Below please find a few of our top picks for our favorite news articles of the week. Enjoy!
InformationAge: Converged infrastructure: a networking panacea or just another nice idea?
By Ben Rossi
It’s a real-time, data-heavy, multimedia world. Legacy networks with their siloed environments are simply not designed to deliver today’s enterprise demands, which are focused more and more on delivering applications Continue reading
Does Infinite Bandwidth Mean You Don’t Need SDN?
Interestingly, this question was asked during a discussion I had at the Open Server Summit last November with an Industry Analyst with, andMusing: Could We Replace PCIe Bus With Ethernet Switch ?
I've been thinking about how a data centre architecture would look if we replaced the PCIe bus in servers with an Ethernet fabric. It's more doable than most people think.
The post Musing: Could We Replace PCIe Bus With Ethernet Switch ? appeared first on EtherealMind.
Forming a Local User Group
I just read a short post by Lindsay Hill titled Doing Community Programs Right. I think the points made are accurate and well-founded. Prior to working for Cisco, I was part of the “CLN Designated VIP Program”. I had the opportunity to connect with others in and around the industry. I think these online communities are great and there is a wealth of knowledge sharing that happens. During key conferences many of our paths cross and even more interesting conversations happen.
I’d personally like to bring some of those concepts into the local communities I work in. I think many of the same tenants would be important. I wouldn’t want a local group to be about any single vendor (even Cisco) or partner. It would be really interesting to just get a bunch of people together that wanted to share their technology challenges and how they are addressing them.
If you have started such a group, I’d love to hear what worked and what didn’t. Were you able to get attendance even in smaller or rural communities? Maybe you are located in Central Kentucky or East Tennessee and would like to work together in such an effort? If so, reach out to Continue reading