AWS Direct Connect Site-Link — A very excellent service
< MEDIUM: https://raaki-88.medium.com/aws-direct-connect-site-link-a-very-excellent-service-10c13a389c8d >
Site-link is really a nice extension to the DX Gateway’s offering. Let me simplify it.
Reference: https://aws.amazon.com/blogs/networking-and-content-delivery/introducing-aws-direct-connect-sitelink/ — I Can’t Recommend this more, this is a very very nice read.
Few Important Points
- AWS Direct Connect Site Link is a private connection between your on-premises network and your AWS Direct Connect location.
- Site Link provides high bandwidth and low latency connection between your on-premises network and AWS.
- Site Link uses industry standard 802.1q VLANs to provide a secure connection between your on-premises network and AWS.
- Site Link is available in 1 Gbps and 10 Gbps speeds.
- You can use Site Link to connect to multiple AWS Direct Connect locations.
- The site Link is available in all AWS Regions.
Problem — I want to connect my two Data-Centres to Direct Connect Gateway through AWS Backbone.
Let’s see a reference Architecture
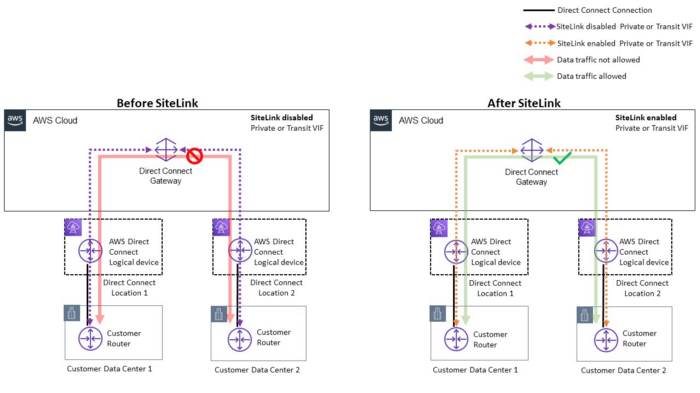
Replicating the above scenario
Few important aspects
- Connect DC1-DC2 via AWS Global Backbone Network
- If both DCs use the same BGP ASN 65001 in this case, use allowas-in to allow looping in AS-PATH
- When you enable site-link BGP session won’t flap but it Continue reading
Using EVPN/VXLAN with MLAG Clusters
There’s no better way to start this blog post than with a widespread myth: we don’t need MLAG now that most vendors have implemented EVPN multihoming.
TL&DR: This myth is close to the not even wrong category.
As we discussed in the MLAG System Overview blog post, every MLAG implementation needs at least three functional components:
Using EVPN/VXLAN with MLAG Clusters
There’s no better way to start this blog post than with a widespread myth: we don’t need MLAG now that most vendors have implemented EVPN multihoming.
TL&DR: This myth is close to the not even wrong category.
As we discussed in the MLAG System Overview blog post, every MLAG implementation needs at least three functional components:
3 container security best practices to strengthen your overall security posture
Container environments are highly dynamic and require continuous monitoring, observability, and security. Since container security is a continuous practice, it should be fully integrated into the entire development and deployment cycle. Implementing security as an integral part of this cycle allows you to mitigate risk and reduce the number of vulnerabilities across the dynamic and complex attack surface containers present.
Let’s take a look at three best practices for ensuring containers remain secure during build, deployment, and runtime.
Securing container deployments
Securing containers during the build and deployment stages is all about vulnerability management. It’s important to continuously scan for vulnerabilities and misconfigurations in software before deployment, and block deployments that fail to meet security requirements. Assess container and registry image vulnerabilities by scanning first- and third-party images for vulnerabilities and misconfigurations, and using a tool that scans multiple registries to identify vulnerabilities from databases such as NVD. You also need to continuously monitor images, workloads, and infrastructure against common configuration security standards (e.g. CIS Benchmarks). This enables you to meet internal and external compliance standards, and also quickly detect and remediate misconfigurations in your environment, thereby eliminating potential attack vectors.
Securing containers at runtime
Containerized workloads require a Continue reading
Four Elements for Disruption-Free Security Powered by Hardware
The industry has made major advancements over the last five years in mitigating security risk by harnessing the power of hardware.SRv6 as a Host-to-Host Overlay
During the discussion of the On Applicability of MPLS Segment Routing (SR-MPLS) blog post on LinkedIn someone made an off-the-cuff remark that…
SRv6 as an host2host overlay - in some cases not a bad idea
It’s probably just my myopic view, but I fail to see the above idea as anything else but another tiny chapter in the “Solution in Search of a Problem” SRv6 saga1.
SRv6 as a Host-to-Host Overlay
During the discussion of the On Applicability of MPLS Segment Routing (SR-MPLS) blog post on LinkedIn someone made an off-the-cuff remark that…
SRv6 as an host2host overlay - in some cases not a bad idea
It’s probably just my myopic view, but I fail to see the above idea as anything else but another tiny chapter in the “Solution in Search of a Problem” SRv6 saga1.
Viewing palo statistics
Useful commands to see general information on the firewall resources been used, interface and traffic statistics, and traffic counters.
Announcing Networking and Advanced Security Enhancement in NSX 4.0.1.1
We’re thrilled to announce the general availability of VMware NSX 4.0.1.1, another exciting release with updates in networking, security, and operations for private, public, and multi-clouds.
With this release, VMware NSX customers will be able to leverage accelerated NSX networking and security performance, enhanced network observability, and new network monitoring and troubleshooting features for increased flexibility.
NSX 4.0.1.1 will also deliver enhanced threat detection and prevention capabilities, helping customers bolster network defenses to block advanced threats from moving laterally across multi-cloud environments.
Read on to get the details on our latest NSX release.
Distributed Malware Prevention
The NSX Distributed Firewall has added malware detection and prevention support for Linux guest endpoints (VMs). Linux has become the most common operating system across multi-cloud environments, powering more than 78% of the most popular websites. With the recent emergence of more Linux-specific threats, and current malware countermeasures being mostly focused on addressing Windows-based threats, there is an imperative to address the specific security needs of Linux machines. Adding Linux to our prevention solution enables the NSX Distributed Firewall to provide more effective prevention coverage and fewer false positives across multi-cloud environments.
In addition, we expanded the Continue reading
Enhanced NSX Edge and Networking Services in NSX 4.0.1.1
VMware NSX 4.0.1.1 introduces exciting new capabilities and enhancements for virtualized networking and security for private, public, and multi-clouds. Check out the release blog for an overview of the new features.
Among these new features is NSX Gateway Stateful Active/Active Services. This feature delivers a key security enhancement, giving you the full power of the NSX Edge cluster for your services without worrying about bandwidth and CPU limitations. In this blog post, we’ll cover all the terminology you need to know for this new feature, as well as configuration and architecture, and design considerations.
Stateful Active/Active Services
Prior to VMware NSX 4.0.1.0, configuring NSX using any of the variety of NSX services offered by VMware required you to set up NSX Edge Gateways in Active/Standby High Availability mode. Under this configuration, traffic is forwarded through a single (Active) NSX Edge Node. So, when designing the architecture, you needed to be aware of the limits imposed by the Active/Standby mode on the bandwidth and CPU (Central Processing Unit) utilization of the node.
With the NSX 4.0.1.0 release of NSX Stateful Active/Active Services, this consideration no longer applies. This new feature makes it Continue reading
Tech Bytes: Why SASE Is An Architecture, Not A Product (Sponsored)
Today on the Tech Bytes podcast, we’ll be investigating Secure Access Service Edge, or SASE, including the current state of the market and how SASE is evolving. We’ll also look at how sponsor Juniper Networks is moving into the SASE space. Our guest is Kate Adam, Sr. Director of Security Product Marketing at Juniper Networks.
The post Tech Bytes: Why SASE Is An Architecture, Not A Product (Sponsored) appeared first on Packet Pushers.