Friday Thoughts Pre-Cisco Live

It’s weird to think that I’m headed out to Cisco Live for the first time since 2019. The in-person parts of Cisco Live have been sorely missed during the pandemic. I know it was necessary all around but I didn’t realize how much I enjoyed being around others and learning from the community until I wasn’t able to do it for an extended period of time.
Now we’re back in Las Vegas and ready to take part in something that has been missed. I’ve got a busy lineup of meetings with the CCIE Advisory Council and Tech Field Day Extra but that doesn’t mean I’m not going to try and have a little fun along the way. And yes, before you ask, I’m going to get the airbrush tattoo again if they brought the artist back. It’s a tradition as old as my CCIE at this point.
What else am I interested in?
- I’m curious to see how Cisco responds to their last disappointing quarter. Are they going to tell us that it was supply chain? Are they going to double down on the software transition? And how much of the purchasing that happened was pull through? Does that mean Continue reading
AAE-1 & SMW5 cable cuts impact millions of users across multiple countries


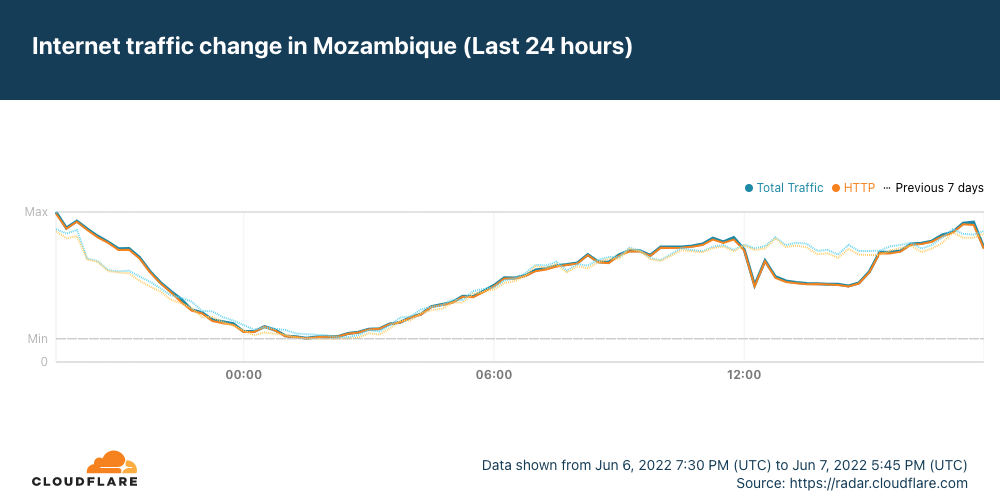
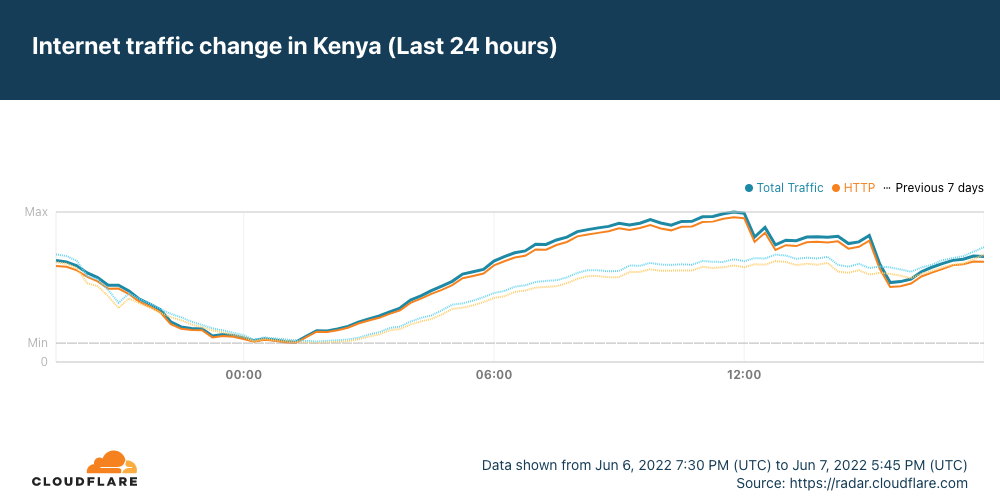
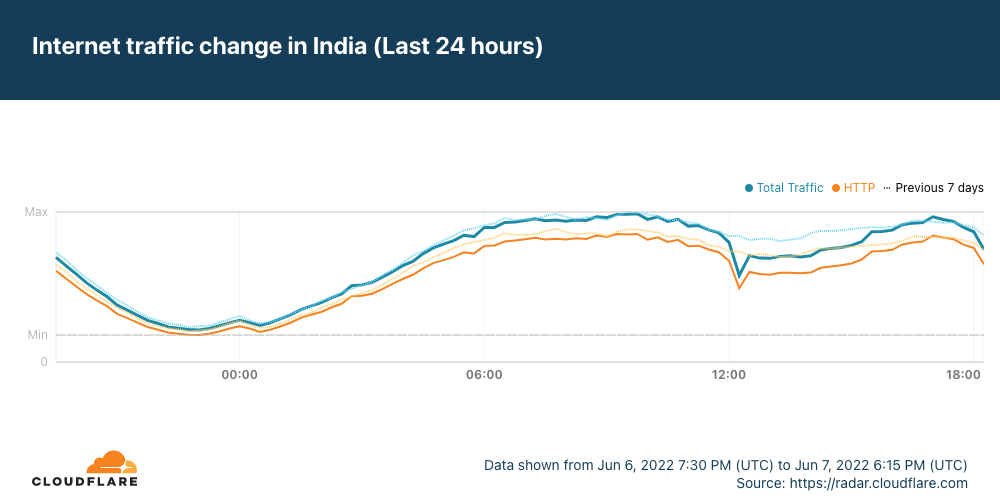
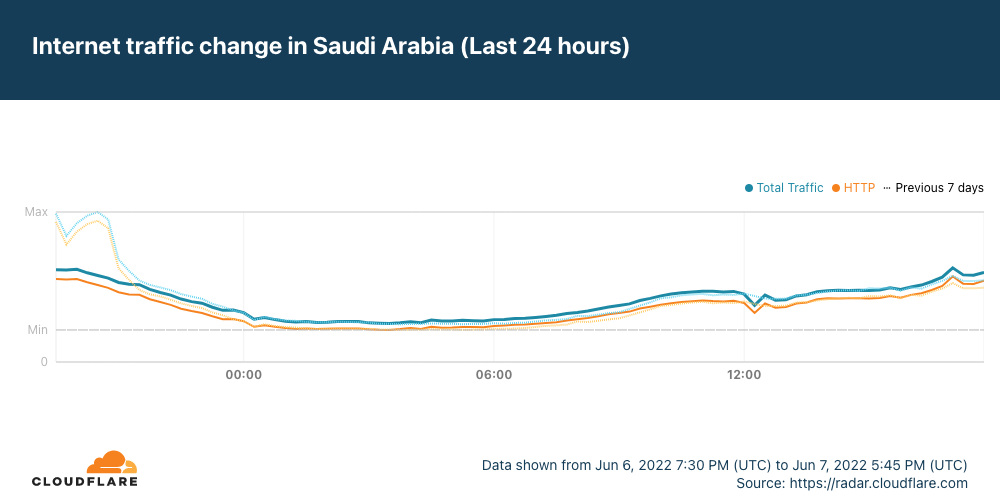
Just after 1200 UTC on Tuesday, June 7, the Africa-Asia-Europe-1 (AAE-1) and SEA-ME-WE-5 (SMW-5) submarine cables suffered cable cuts. The damage reportedly occurred in Egypt, and impacted Internet connectivity for millions of Internet users across multiple countries in the Middle East and Africa, as well as thousands of miles away in Asia. In addition, Google Cloud Platform and OVHcloud reported connectivity issues due to these cable cuts.
The impact
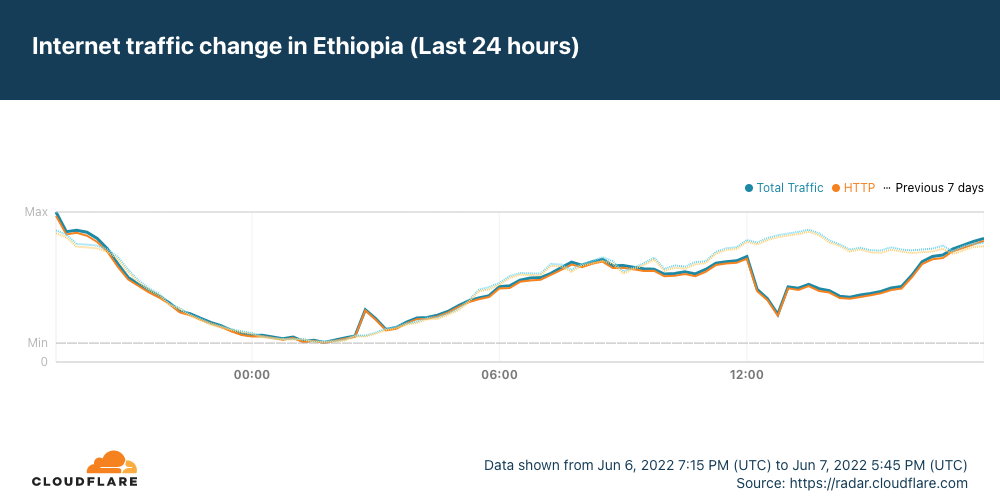
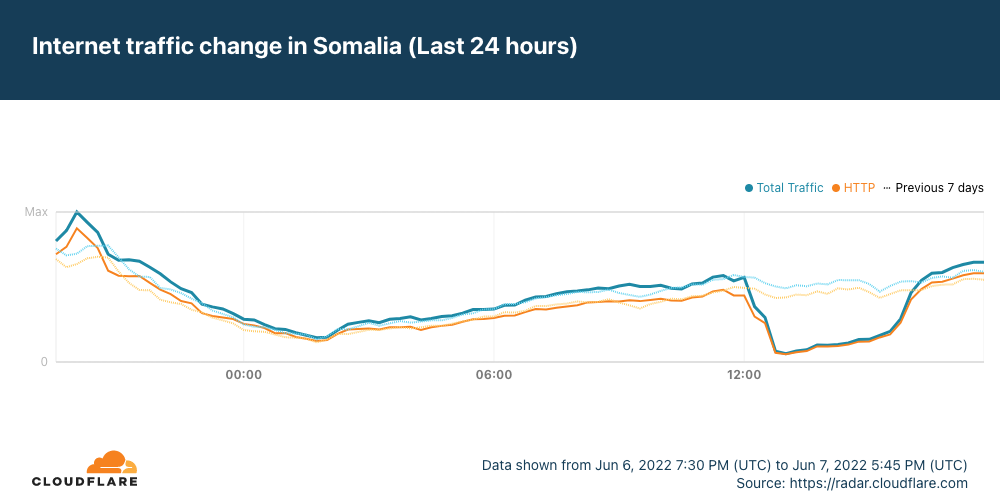
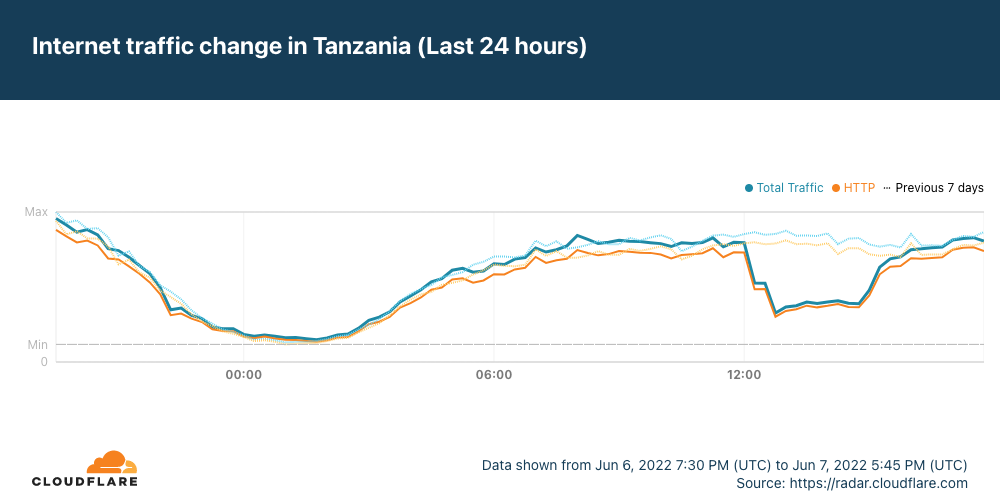
Data from Cloudflare Radar showed significant drops in traffic across the impacted countries as the cable damage occurred, recovering approximately four hours later as the cables were repaired.
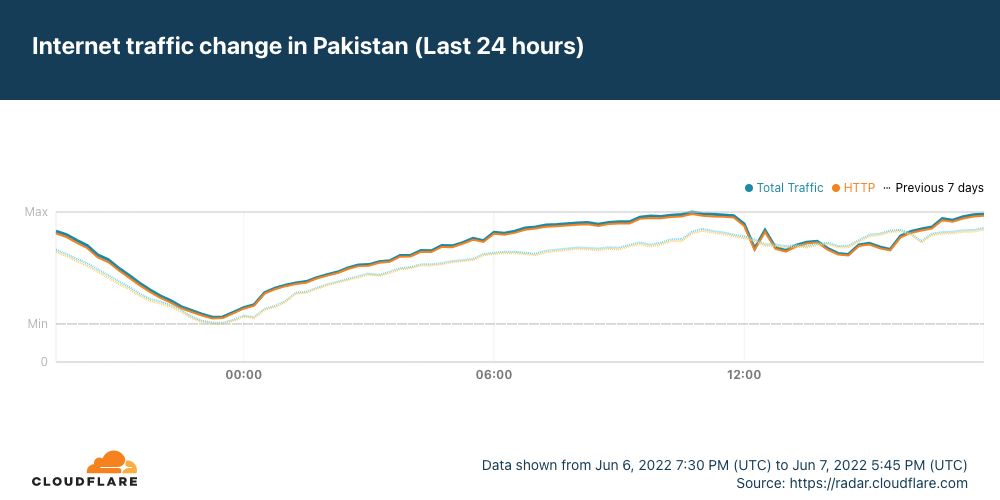
It appears that Saudi Arabia may have also been affected by the cable cut(s), but the impact was much less significant, and traffic recovered almost immediately.
In the graphs above, we show that Ethiopia was one of the impacted countries. However, as it is landlocked, there are obviously no submarine cable landing points within the country. The Afterfibre map from the Network Startup Resource Center (NSRC) shows that that fiber in Ethiopia connects to fiber in Somalia, which experienced an impact. In addition, Ethio Telecom also routes traffic through network providers in Kenya and Djibouti. Djibouti Telecom, one of these providers, in turn Continue reading
Video: Rogue IPv6 RA Challenges
IPv6 security-focused presentations were usually an awesome opportunity to lean back and enjoy another round of whack-a-mole, often starting with an attacker using IPv6 Router Advertisements to divert traffic (see also: getting bored at Brussels airport) .
Rogue IPv6 RA challenges and the corresponding countermeasures are thus a mandatory part of any IPv6 security training, and Christopher Werny did a great job describing them in IPv6 security webinar.
Video: Rogue IPv6 RA Challenges
IPv6 security-focused presentations were usually an awesome opportunity to lean back and enjoy another round of whack-a-mole, often starting with an attacker using IPv6 Router Advertisements to divert traffic (see also: getting bored at Brussels airport) .
Rogue IPv6 RA challenges and the corresponding countermeasures are thus a mandatory part of any IPv6 security training, and Christopher Werny did a great job describing them in IPv6 security webinar.
Key advantages of the Calico eBPF data plane
Project Calico and eBPF
Project Calico has offered a production-ready data plane based on eBPF since September 2020, and it’s been available for technical evaluation for even longer (since February 2020).


The pre-requisites and limitations are simple to review, it’s easy to enable, and it’s easy to validate your configuration. So, there’s never been a better time to start experiencing the benefits!
You do know what those are, don’t you? Don’t worry if not! That’s what this blog post is about. We’ve reached a point where the journey is easy to make, if you know why you want to get there.
Key advantages of using Calico with eBPF
Calico is already the most widely deployed Kubernetes network security solution. What can eBPF do to help our winning formula further? I’ll dive into the details, but let’s look at the highest possible level first.
These three key benefits apply across all supported environments:
- General performance
- Native Kubernetes service handling
- Source IP preservation and Direct Server Return, or DSR
- Each of these benefits is significant and worth discussing in more detail.
Performance
Calico’s eBPF data plane achieves high performance in several ways. Firstly, it achieves higher throughput and/or less CPU Continue reading
How Queen Elizabeth II’s Platinum Jubilee had an impact on the Internet

“I declare before you all that my whole life, whether it be long or short, shall be devoted to your service and the service of our great imperial family to which we all belong.”
— Queen Elizabeth II birthday speech, April 21, 1947

The rising and setting of the sun has an impact on human behaviour and on Internet trends, and events like this weekend's celebration of Queen Elizabeth II’s Platinum Jubilee also show up in Internet trends.
When Elizabeth II's reign started, on February 6, 1952 (the coronation was on June 2, 1953), the Turing machine had already been proposed (1936), and with that the basis for computer science. ARPANET, which became the technical foundation of the Internet, was still a dream that came to fruition in the late 60s — the World Wide Web is from 1989 and in 2014 we celebrated its Silver Jubilee. So, with that in mind, let’s answer the question: did the 2022 celebrations of the first British monarch with a 70th anniversary on the throne have an impact on the UK’s Internet traffic?
First, some details about the Platinum Jubilee. There was a four-day bank holiday (June 2-5) in the UK Continue reading
Using OpenSSL with Ed Harmoush 1/6 Generating Public & Private Keys – Video
Ethan Banks and Ed Harmoush kick off a six-part video series on using OpenSSL. The first video covers the generation of public and private keys in OpenSSL.
The post Using OpenSSL with Ed Harmoush 1/6 Generating Public & Private Keys – Video appeared first on Packet Pushers.
A new portal for Project Galileo participants

This post is also available in 日本語, Deutsch, Français, Español and Português.

Each anniversary of Project Galileo serves as an impetus for big-picture thinking among the Cloudflare team about where to take the initiative next. For this eighth anniversary, we want to help participants get the most out of their free security and performance services and simplify the onboarding process.
Organizations protected under Galileo are a diverse bunch, with 111 countries represented across 1,900+ web domains. Some of these organizations are very small and sometimes operated solely by volunteers. It is understandable that many do not have IT specialists or other employees with technical knowledge about security and performance capabilities. We strive to give them the tools and training to succeed, and we felt it was imperative to take this effort to a new level.
Introducing the Cloudflare Social Impact Projects Portal
To provide Galileo participants with one place to access resources, configuration tips, product explainers, and more, we built the Cloudflare Social Impact Projects Portal.
The crisis in Ukraine was a key source of inspiration for this endeavor. With overall applications for the project skyrocketing by 177% in March 2022, we were rushing to onboard new Continue reading
Cisco Live 2022 – Are you ready?
Soon, many of us will be on an airplane heading to Las Vegas for Cisco Live 2022. So I felt …
The post Cisco Live 2022 – Are you ready? first appeared on Fryguy's Blog.Kubernetes Unpacked 002: Tackling Container Management And Kubernetes Complexity
In this episode, Michael Levan chats with Neil Cresswell, CEO and Co-Founder of Portainer.io. They talk about the challenges of Kubernetes and how everyone is trying to navigate its complexities. They also dive into Kubernetes security, networking, and management.
The post Kubernetes Unpacked 002: Tackling Container Management And Kubernetes Complexity appeared first on Packet Pushers.
Kubernetes Unpacked 002: Tackling Container Management And Kubernetes Complexity
In this episode, Michael Levan chats with Neil Cresswell, CEO and Co-Founder of Portainer.io. They talk about the challenges of Kubernetes and how everyone is trying to navigate its complexities. They also dive into Kubernetes security, networking, and management.Using Custom Vagrant Boxes with netsim-tools
A friend of mine started using Vagrant with libvirt years ago (it was his enthusiasm that piqued my interest in this particular setup, eventually resulting in netsim-tools). Not surprisingly, he’s built Vagrant boxes for any device he ever encountered, created quite a collection that way, and would like to use them with netsim-tools.
While I didn’t think about this particular use case when programming the netsim-tools virtualization provider interface, I decided very early on that:
- Everything worth changing will be specified in the system defaults
- You will be able to change system defaults in topology file or user defaults.
Using Custom Vagrant Boxes with netlab
A friend of mine started using Vagrant with libvirt years ago (it was his enthusiasm that piqued my interest in this particular setup, eventually resulting in netlab). Not surprisingly, he’s built Vagrant boxes for any device he ever encountered, created quite a collection that way, and would like to use them with netlab.
While I didn’t think about this particular use case when programming the netlab virtualization provider interface, I decided very early on that:
- Everything worth changing will be specified in the system defaults
- You will be able to change system defaults in topology file or user defaults.