Outburst: Can SONiC become the Linux of Network Operating Systems? – YouTube
 Useful business primer on why and what of SONIC
Useful business primer on why and what of SONIC
Who is Right About Edge Computing?
Edge will ultimately succeed (or fail) based on its ability to address the operational experience of those tasked with deploying and operating the its workloads.Creating MPLS/VPN Labs With netsim-tools
Two week ago I described how to create a simple VRF Lite lab with netsim-tools VRF configuration module. Adding MPLS/VPN to the mix and creating a full-blown MPLS/VPN lab is a piece of cake. In this blog post we’ll build a simple topology with two VRFs (red and blue) and two PE-routers:
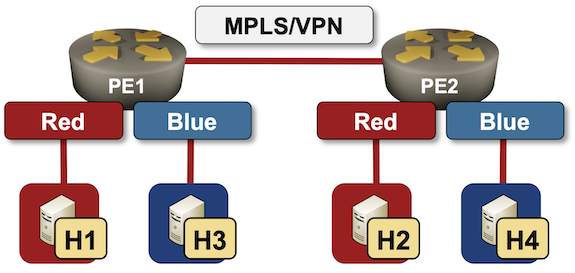
Lab topology
Creating MPLS/VPN Labs With netlab
Two week ago I described how to create a simple VRF Lite lab with netlab VRF configuration module. Adding MPLS/VPN to the mix and creating a full-blown MPLS/VPN lab is a piece of cake. In this blog post we’ll build a simple topology with two VRFs (red and blue) and two PE-routers:
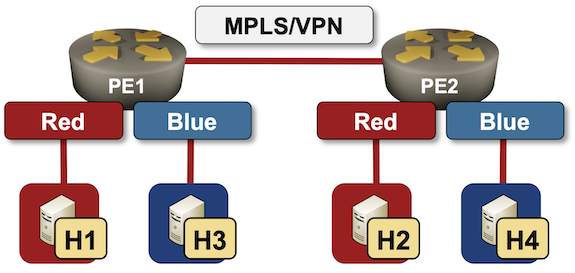
Lab topology
Using LEOs and GEOs
Once you head off the main roads your Internet connectivity options are often pretty limited. However, things are improving, and in Australia you can use an Internet service based on a connection through a geostationary satellite connection or you could sign up for Starlink, a Low Earth Orbit service. Both services offer decent capacity, but there are some some other critical differences going on here. Let's look at these services using a custom test rig to put them through their paces.EVPN-VXLAN Explainer 2 – The BGP Session
In this second post I will look at Ethernet VPN (EVPN), what is it and how to configure a BGP EVPN session on Aruba devices.
Please note, this post will focus on the establishment of the BGP EVPN session between peers, and thus will not present a fully functioning EVPN network. I aim to build the configuration up in stages to enable the reader to confidently understand the different pieces of EVPN-VXLAN as a technology.
Ethernet VPN - the VPLS successor seen about campus
Reading through EVPN RFCs one gets an impression of its convoluted development, or rather, the evolving area of focus for its application.
To summarize, it started life as a service-provider focused VPLS successor, then jumped over to the control plane for virtualized data centres, now gaining a foothold in campus networks.
I put together an overview of the various RFCs here.
EVPN - what is it used for?
In the first post in this series, I explained the VXLAN forwarding process, that relies upon flood and learn.
- VXLAN is a data plane technology, concerned with the forwarding of packets and what headers to add to data.
- EVPN is a control plane technology, concerned with building a Continue reading
Protecting The Hybrid Workforce With Palo Alto Networks Secure, Flexible SASE Solution
Palo Alto Networks announces new innovations for Prisma SASE for protecting the hybrid workforce, including the general availability of Prisma SD-WAN bandwidth licensing on-demand and Okyo Garde Enterprise Edition.
The post Protecting The Hybrid Workforce With Palo Alto Networks Secure, Flexible SASE Solution appeared first on Packet Pushers.
Day Two Cloud 144: The State Of IPv6 In Public Cloud
Today's Day Two Cloud explores the vastness of IPv6 and public cloud. IPv6 provides so much address space that you can use an address once for one connection and never use it again, and it isn't wasteful. The abundance of IPv6 may influence how you approach cloud applications and networks.How to Make Friends as an Adult
Making friends as an adult can seem daunting, but it doesn’t have to be. There are many ways to meet new people and build lasting relationships.
Ways to Find Friends as an Adult
Making friends as an adult can be challenging, but it can also be rewarding. With a little effort, you can develop lasting relationships with the people around you. Here are a few tips to get you started:
Join a club or group that aligns with your interests
One of the best ways to meet new friends is by joining a club or group that aligns with your interests. This could be anything from a book club to a hiking group to a cooking class. Not only will you have something in common with the other members, but you’ll also have the opportunity to bond over shared activities.
Attend local events and festivals
Another great way to meet new people is by attending local events and festivals. These are usually great occasions for socializing, and you never know who you might meet. You might even make some new friends that live right in your own neighborhood.
Volunteer for a cause that’s important to you
If you’re looking Continue reading
Cloudflare blocks 15M rps HTTPS DDoS attack
Earlier this month, Cloudflare’s systems automatically detected and mitigated a 15.3 million request-per-second (rps) DDoS attack — one of the largest HTTPS DDoS attacks on record.
While this isn’t the largest application-layer attack we’ve seen, it is the largest we’ve seen over HTTPS. HTTPS DDoS attacks are more expensive in terms of required computational resources because of the higher cost of establishing a secure TLS encrypted connection. Therefore it costs the attacker more to launch the attack, and for the victim to mitigate it. We’ve seen very large attacks in the past over (unencrypted) HTTP, but this attack stands out because of the resources it required at its scale.
The attack, lasting less than 15 seconds, targeted a Cloudflare customer on the Professional (Pro) plan operating a crypto launchpad. Crypto launchpads are used to surface Decentralized Finance projects to potential investors. The attack was launched by a botnet that we’ve been observing — we’ve already seen large attacks as high as 10M rps matching the same attack fingerprint.
Cloudflare customers are protected against this botnet and do not need to take any action.
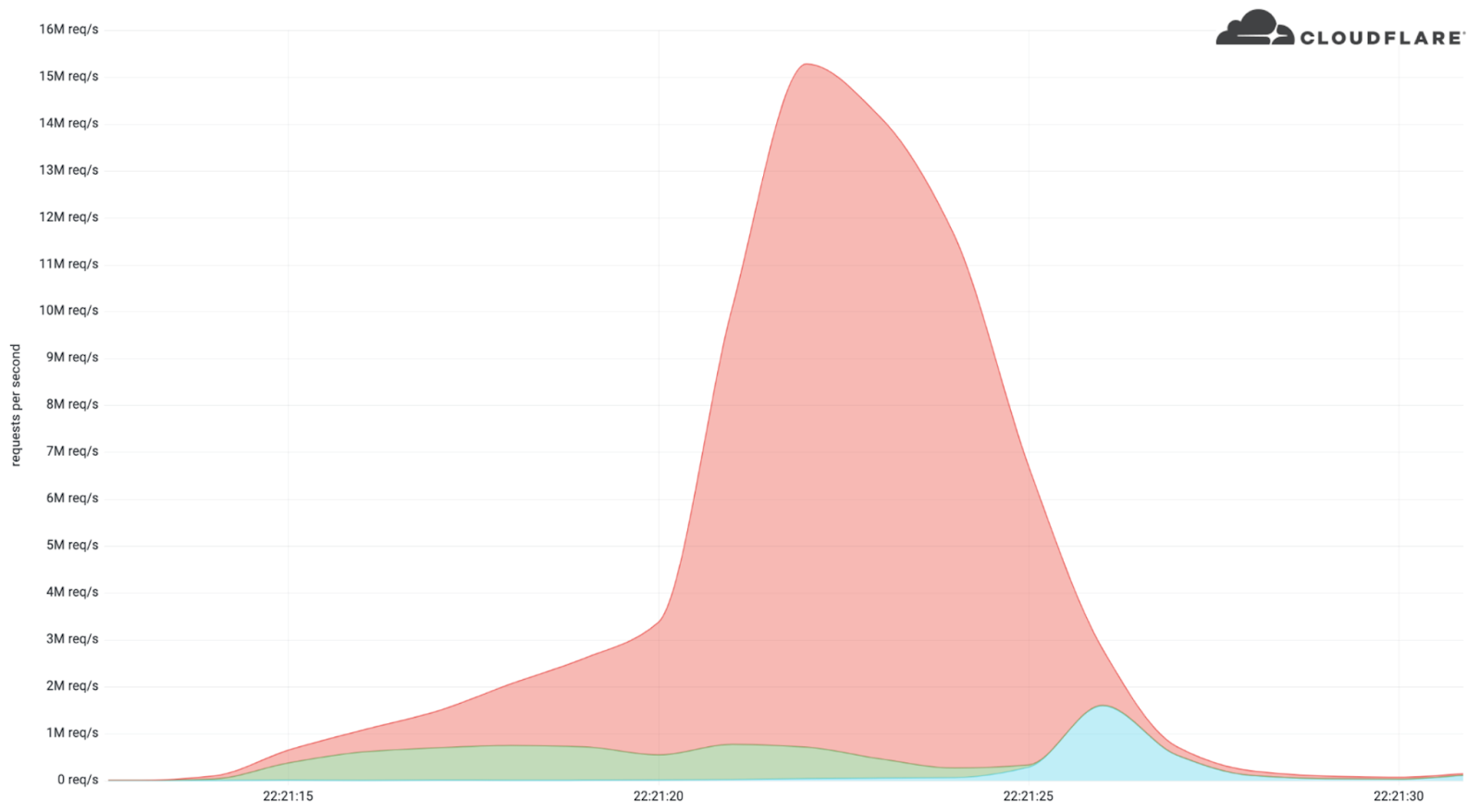
The attack
What’s interesting is that the attack mostly came from data centers. We’re Continue reading
Practical Python For Networking: 6.2 – Package Examples – Video
This lesson walks through basic examples of packages. Course files are in a GitHub repository: https://github.com/ericchou1/pp_practical_lessons_1_route_alerts Eric Chou is a network engineer with 20 years of experience, including managing networks at Amazon AWS and Microsoft Azure. He’s the founder of Network Automation Nerds and has written the books Mastering Python Networking and Distributed Denial Of […]
The post Practical Python For Networking: 6.2 – Package Examples – Video appeared first on Packet Pushers.
Is X.25 Still Alive?
Enrique Vallejo asked an interesting question a while ago:
When was X.25 official declared dead? Note that the wikipedia claims that it is still in use in parts of the world.
Wikipedia is probably right, and had several encounters with X.25 that would corroborate that claim. If you happen to have more up-to-date information, please leave a comment.
Is X.25 Still Alive?
Enrique Vallejo asked an interesting question a while ago:
When was X.25 official declared dead? Note that the wikipedia claims that it is still in use in parts of the world.
Wikipedia is probably right, and had several encounters with X.25 that would corroborate that claim. If you happen to have more up-to-date information, please leave a comment.
Two voting days, a debate and a polling rule in France impacts the Internet
We blogged previously about some trends concerning the first round of the 2022 French presidential election, held on April 10. Here we take a look at the run-off election this Sunday, April 24, that ended up re-electing Emmanuel Macron as President of France.
First, the two main trends: French-language news sites outside France were clearly impacted by the local rule that states that exit polls can only be published after 20:00.
And Internet traffic was similar on both the election days (April 10 and 24) and that includes the increase in use of mobile devices and interest in news websites — there we also saw a clear interest in the Macron-Le Pen debate on April 20.
We have discussed before that election days usually don’t have a major impact on overall Internet traffic. Let’s compare April 10 with 24, the two Sundays when the elections were held. The trends throughout the day are incredibly similar (with a slight increase in traffic on April 24), even with a two-week gap between them.
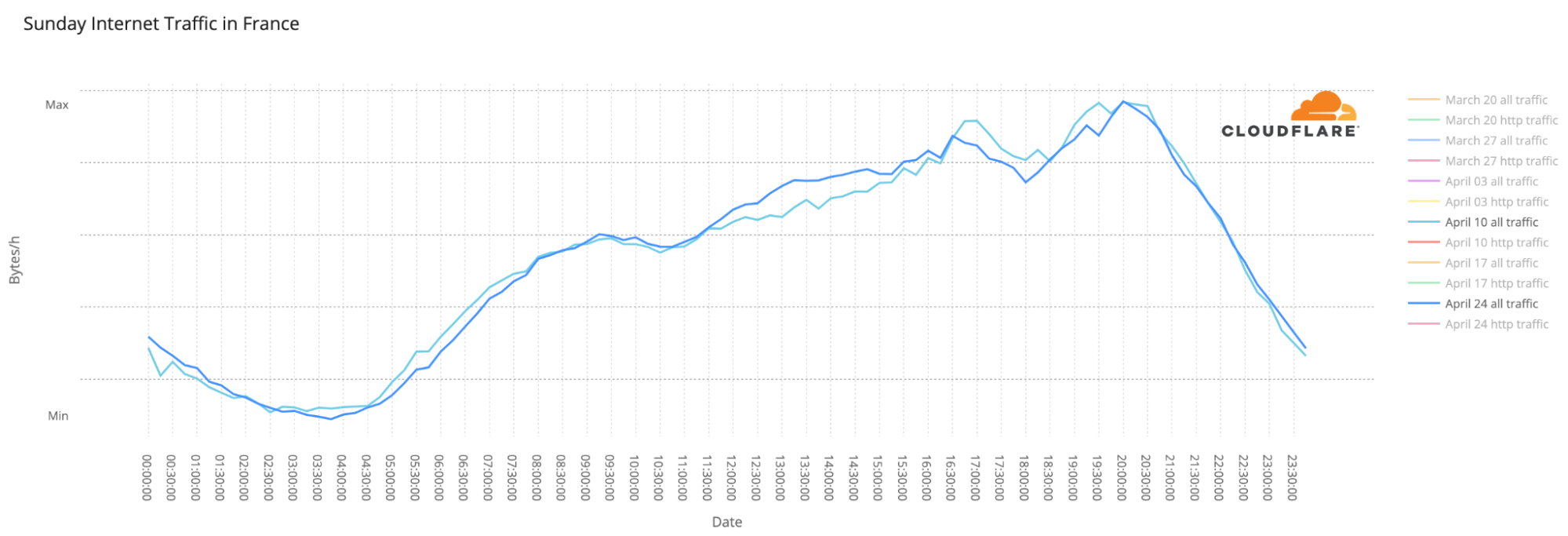
Another election-day trend is the use of mobile devices to access the Internet, mainly at night. The largest spikes in number of requests made using mobile devices in Continue reading
Deux jours de vote, un débat et une réglementation concernant les élections en France impactent l’Internet
Nous avons publié un article de blog consacré à certaines tendances concernant le premier tour de l'élection présidentielle française de 2022, qui s'est déroulé le 10 avril. Nous nous intéressons ici au second tour de l'élection, qui a eu lieu le dimanche 24 avril et a abouti à la réélection d'Emmanuel Macron à la présidence de la France.
Tout d'abord, les deux principales tendances : les sites d'information francophones situés hors de France ont été clairement impactés par la réglementation locale, qui stipule que les estimations ne peuvent être publiées qu'après 20 heures.
Le trafic Internet a été similaire les deux jours de l'élection (les 10 et 24 avril), et cela inclut l'augmentation de l'utilisation des appareils mobiles et l'intérêt pour les sites d'actualités – - là aussi, nous avons constaté un net intérêt pour le débat Macron-Le Pen du 20 avril.
Nous avons déjà évoqué le fait que les jours d'élections n'ont généralement pas un impact majeur sur le trafic Internet global. Comparons les journées des 10 et 24 avril, les deux dimanches où ont eu lieu les élections. Les tendances tout au long de la journée sont incroyablement similaires (avec une légère augmentation du trafic le 24 Continue reading