Lucky Webapp Use UUIDs For Primary Keys
By default, new Lucky projects use the Int64 type for primary keys. In this post I will cover the process of changing the Lucky database primary keys type from an Int64 to a UUID. Software Used The following software versions are used in this post. Crystal - 1.1.1 Lucky -...continue reading
MikroTik – RouterOSv7 first look – feedback on routing filters
Overview
Routing filters have been a hot topic lately in the world of RouterOSv7. The first implementation of routing filters in ROSv7 was difficult to work with and documented in the two articles below:
MikroTik – RouterOSv7 first look – Dynamic routing with IPv6 and OSPFv3/BGP
MikroTik RouterOS – v7.0.3 stable (chateau) and status of general release
MikroTik then made some changes and opened up discussion to get feedback. I did a lot of work and testing using ROS 7.1beta7 which never made it to public release and was close to publishing the results when 7.1rc1 came out so this post will use that version.
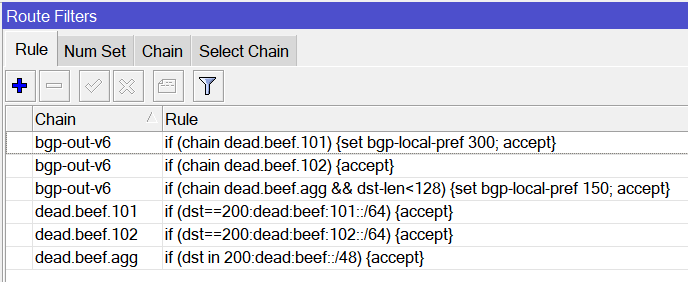
RouterOSv7.1rc1 syntax example
Here is an example of the latest syntax in ROSv7.1rc1
CLI
### MikroTik RouterOS 7.1rc1 ###
/routing filter rule
add chain=dead.beef.101 rule="if (dst==200:dead:beef:101::/64) {accept}"
add chain=dead.beef.102 rule="if (dst==200:dead:beef:102::/64) {accept}"
add chain=dead.beef.agg rule="if (dst in 200:dead:beef::/48) {accept}"
add chain=bgp-out-v6 rule="if (chain dead.beef.101) {set bgp-local-pref 300; accept}"
add chain=bgp-out-v6 rule="if (chain dead.beef.102) {accept}"
add chain=bgp-out-v6 rule="if (chain dead.beef.agg && dst-len<128) {set bgp-local-pref 150; accept}"Winbox
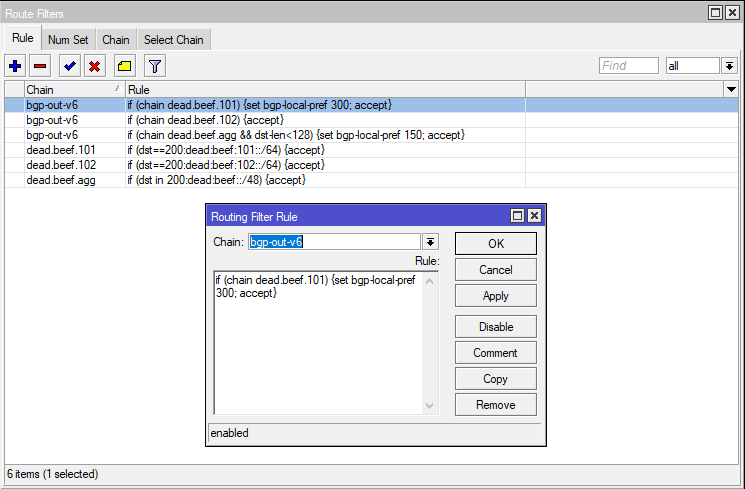
And the corresponding routes received Continue reading
Introducing logs from the dashboard for Cloudflare Workers

If you’re writing code: what can go wrong, will go wrong.
Many developers know the feeling: “It worked in the local testing suite, it worked in our staging environment, but… it’s broken in production?” Testing can reduce mistakes and debugging can help find them, but logs give us the tools to understand and improve what we are creating.
if (this === undefined) {
console.log("there’s no way… right?") // Narrator: there was.
}
While logging can help you understand when the seemingly impossible is actually possible, it’s something that no developer really wants to set up or maintain on their own. That’s why we’re excited to launch a new addition to the Cloudflare Workers platform: logs and exceptions from the dashboard.
Starting today, you can view and filter the console.log output and exceptions from a Worker… at no additional cost with no configuration needed!
View logs, just a click away
When you view a Worker in the dashboard, you’ll now see a “Logs” tab which you can click on to view a detailed stream of logs and exceptions. Here’s what it looks like in action:
Each log entry contains an event with a list of logs, exceptions, Continue reading
The Next Phase of Cloud-Grade Routing
In the past decade, the emergence of cloud networks has blurred the line between switching and routing versus traditional routers. Today the industry is at an inflection point, where the adoption of cloud principles for routing intersects the rapidly expanding capabilities of the merchant silicon feature set and scale, creating a disruption of legacy routing architectures.
eBPF: When (and when not) to use it
Extended Berkeley Packet Filter (eBPF) is a relatively new feature for Linux kernels that has many DevOps, SREs, and engineers excited. But is it a one-stop shop solution for all of your Linux kernel needs? Let’s take a look at what eBPF does well, and how it stacks up against standard Linux iptables.
What is eBPF?
eBPF is a feature available in Linux kernels that allows you to run a virtual machine inside the kernel. This virtual machine allows you to safely load programs into the kernel, in order to customize its operation. Why is this important?
In the past, making changes to the kernel was difficult: there were APIs you could call to get data, but you couldn’t influence what was inside the kernel or execute code. Instead, you had to submit a patch to the Linux community and wait for it to be approved. With eBPF, you can load a program into the kernel and instruct the kernel to execute your program if, for example, a certain packet is seen or another event occurs.
With eBPF, the kernel and its behavior become highly customizable, instead of being fixed. This can be extremely beneficial, when used Continue reading
Misconfigurations: Still the Biggest Threat to Cloud Security
With a bit of effort and attention, businesses can avoid cloud security problems that arise from misconfigurations.ThinkPad X1 Carbon (Gen 7): 2 years later
Two years ago, I replaced my ThinkPad X1 Carbon 2014 with the latest generation. The new configuration embeds an Intel Core i7-8565U, 16 Gib of RAM, a 1 Tib NVMe disk, and a WQHD display (2560×1440). I did not ask for a WWAN card. I think it is easier and more reliable to use the wifi hotspot feature of a phone instead: no unreliable firmware and unsupported drivers.1 Here is my opinion on this model.

While the second generation got a very odd keyboard, this one got a classic one with a full row of function keys. I don’t know if my model was defective, but the keyboard skips one keypress from time to time. I have got used to it, but the space key still has a hard time registering when hitting it with my right thumb. The travel course is also shorter and it is less comfortable to type on it than it was on the 2014 version. The trackpoint2 works well. The physical buttons are a welcome addition. I am only using the trackpad for scrolling with the two-finger gesture.

5 Key Cybersecurity Trends to Know For 2021
The fundamentals of cybersecurity in 2021: Scalability, user awareness, and the ability to evolve to meet changing network and security needs..Tech Bytes: How Kentik Enables Automated Performance Testing (Sponsored)
Today on the Tech Bytes podcast we get into the automation of network performance testing and synthetic transactions. Our sponsor is Kentik and our guest is Avi Freedman, Kentik's CEO and co-founder.
The post Tech Bytes: How Kentik Enables Automated Performance Testing (Sponsored) appeared first on Packet Pushers.
Tech Bytes: How Kentik Enables Automated Performance Testing (Sponsored)
Today on the Tech Bytes podcast we get into the automation of network performance testing and synthetic transactions. Our sponsor is Kentik and our guest is Avi Freedman, Kentik's CEO and co-founder.It always takes longer than you think

Everyone is aware that it always takes longer to find a problem in a network than it should. Moving through the troubleshooting process often feels like swimming in molasses—you’re pulling hard, and progress is being made, but never fast enough or far enough to get the application back up and running before that crucial deadline. The “swimming in molasses effect” doesn’t end when the problem is found out, either—repairing the problem requires juggling a thousand variables, most of which are unknown, combined with the wit and sagacity of a soothsayer to work with vendors, code releases, and unintended consequences.
It’s enough to make a network engineer want to find a mountain top and assume an all-knowing pose—even if they don’t know anything at all.
The problem of taking longer, though, applies in every area of computer networking. It takes too long for the packet to get there, it takes to long for the routing protocol to converge, it takes too long to support a new application or server. It takes so long to create and validate a network design change that the hardware, software and processes created are obsolete before they are used.
Why does it always take too long? Continue reading
Network Break 347: Cisco Acquires Container App Monitor; Intel Unwraps Mount Evans IPU
It's the Network Break! This week we analyze Cisco's $500 million acquisition of a container-based and serverless application monitor, Intel's announcement of Mount Evans, an Infrastructure Processing Unit (IPU) for network and storage offload, and more tech news. Guest analyst Johna Till Johnson, CEO and founder of Nemertes Research, joins Greg Ferro.
The post Network Break 347: Cisco Acquires Container App Monitor; Intel Unwraps Mount Evans IPU appeared first on Packet Pushers.
