Beware the Abandoned Office and its Security Vulnerabilities
As an industry, we have not seen this problem at scale, but abandoned offices, abandoned assets, and out-of-business companies are a ripe target for cyber adversaries.MikroTik RouterOS – v7.0.3 stable (chateau) and status of general release
If you don’t already use it, the MIkroTik v7 BETA forum (forum.mikrotik.com) is a fantastic source of information
When will stable be released?
This is the million dollar question. Technically, it already has been for one hardware platform…
!! Spoiler Alert – There is *already* a stable release of ROSv7 – v7.0.3!!
The Chateau 5G router originally shipped with a beta version of ROSv7 but was quietly moved to a stable version that’s developed specifically for that platform.

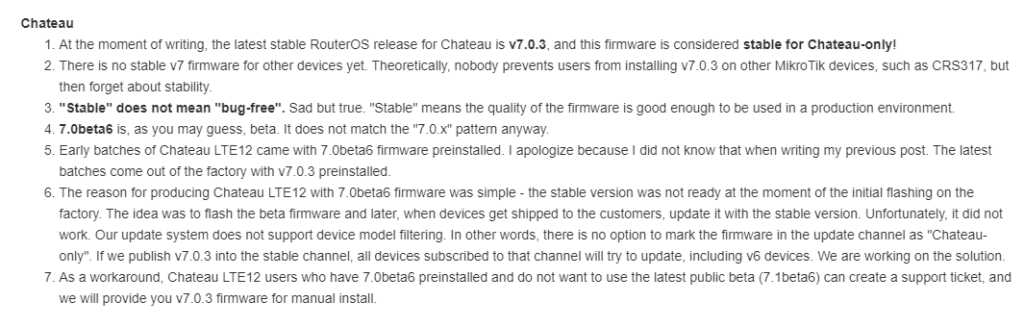
Because of the way MikroTik’s code repo works, this version can’t easily be added to the main download page and support provides the software:
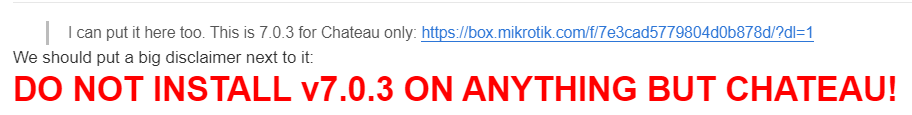
ROSv7.0.3 Stable Download (!!! Chateau Only – will brick other hardware !!!)
https://box.mikrotik.com/f/7e3cad5779804d0b878d/?dl=1
It’s worth repeating MikroTik’s warning about using this on any platform other than the Chateau

What’s holding up v7 from being released?
If you’ve been around MikroTik for a while, then you know that version 7 has been in the works for a long time to add new functionality and address limitations of the older Linux kernel in ROSv6.
MikroTik recently Continue reading
What’s new in Calico Enterprise 3.7: eBPF data plane, high availability, and more!
As our enterprise customers build out large, multi-cluster Kubernetes environments, they are encountering an entirely new set of complex security, observability, and networking challenges, requiring solutions that operate at scale and can be deployed both on-premises and across multiple clouds. New features in our latest release add to the already formidable capabilities of Calico Enterprise.
New feature: High-availability connectivity for Kubernetes with dual ToR
Many platform operators who run Kubernetes on-premises want to leverage Border Gateway Protocol (BGP) to peer with other infrastructure. Calico uses BGP to peer with infrastructure within the cluster as well as outside of the cluster, and integrates with top-of-rack (ToR) switches to provide that connectivity.
Calico ToR connectivity has existed for some time now. However, for cluster operators using BGP who need reliable, consistent connectivity to resources outside of the cluster as well as cluster nodes on different racks, Calico Enterprise dual ToR connectivity ensures high availability with active-active redundant connectivity planes between cluster nodes and ToR switches. A cluster that is peered to two ToR switches will still have an active link, even if one switch becomes unavailable, thus ensuring the cluster always has a network connection. Kubernetes cannot do this on its Continue reading
Distributed Cloud: The Future of Cloud Computing
Distributed cloud architectures enhance the benefits of traditional cloud adding more edge processing power and geo-specific data management.Convergence & Complexity Go Hand In Hand
 Many ways to converge .... Many types of converge
Many ways to converge .... Many types of converge
Private 5G is Anti-Cloud ?
 Because why own it ?
Because why own it ?
A Survey on Securing Inter-Domain Routing: Part 2 – Approaches to Securing BGP
In Part 2 we look at the various proposals to add security to the routing environment and also review the current state of the effort in the IETF to provide a standard specification of the elements of a secure BGP framework.Hedge 90: Andrew Wertkin and a Naïve Reliance on Automation

Automation is surely one of the best things to come to the networking world—the ability to consistently apply a set of changes across a wide array of network devices has speed at which network engineers can respond to customer requests, increased the security of the network, and reduced the number of hours required to build and maintain large-scale systems. There are downsides to automation, as well—particularly when operators begin to rely on automation to solve problems that really should be solved someplace else.
In this episode of the Hedge, Andrew Wertkin from Bluecat Networks joins Tom Ammon and Russ White to discuss the naïve reliance on automation.
We Can’t Achieve the Sustainable Development Goals without the Internet

The Internet is a critical enabler for sustainable development. It unlocks human capabilities and provides the platform upon which an emerging digital economy can thrive. As the Internet and digital technologies become more essential, it also becomes more urgent to connect the people who are being left behind.
The post We Can’t Achieve the Sustainable Development Goals without the Internet appeared first on Internet Society.
Day Two Cloud 105: How The Fly.io Cloud Brings Apps Closer To Users
Fly.io is a public cloud that can run your applications all over the world. The goal of Fly.io is to allow developers to self-service complicated infrastructure without an ops team, while making multi-region a default setting to get apps as close to the user as possible. Our guest is founder Kurt Mackey. This is not a sponsored show.
The post Day Two Cloud 105: How The Fly.io Cloud Brings Apps Closer To Users appeared first on Packet Pushers.