IXPs: Keeping Local Infrastructure Resilient during COVID-19

The COVID-19 pandemic has proven how important a strong Internet infrastructure is.
Internet exchange points are a vital part of that. They are key to bringing better, faster, and more affordable Internet to people.
Recently, the Asia Pacific Internet Exchange Association (APIX) and the Internet Society did a comprehensive survey to understand the impact of COVID-19 on IXP operations in the region.
IXPs from Japan, Hong Kong, Taiwan, Thailand, Myanmar, Philippines, Singapore, Vietnam, Indonesia, Malaysia, Nepal, and Australia provided data. Here are some of the key findings.
What is an Internet Exchange Point?
If you want to see your neighbor, taking a route that sends you across town and back again is not the quickest or most efficient way to get there. And yet, in many parts of the world, that is what happens with Internet traffic. IXPs help create shorter, more direct routes for Internet traffic.
Read the Explainer
Changes in Internet Traffic
There was a significant increase in Internet exchange traffic, between 7- 40%. Traffic patterns during the pandemic show that there is either no difference left between peak and off-peak time or the peak time has increased from a few to more hours.
The increase is highest Continue reading
draft-knodel-terminology-03 – Terminology, Power, and Inclusive Language in Internet-Drafts and RFCs

Add to your documentation style guide.
The post draft-knodel-terminology-03 – Terminology, Power, and Inclusive Language in Internet-Drafts and RFCs appeared first on EtherealMind.
No Humans Involved: Mitigating a 754 Million PPS DDoS Attack Automatically


On June 21, Cloudflare automatically mitigated a highly volumetric DDoS attack that peaked at 754 million packets per second. The attack was part of an organized four day campaign starting on June 18 and ending on June 21: attack traffic was sent from over 316,000 IP addresses towards a single Cloudflare IP address that was mostly used for websites on our Free plan. No downtime or service degradation was reported during the attack, and no charges accrued to customers due to our unmetered mitigation guarantee.
The attack was detected and handled automatically by Gatebot, our global DDoS detection and mitigation system without any manual intervention by our teams. Notably, because our automated systems were able to mitigate the attack without issue, no alerts or pages were sent to our on-call teams and no humans were involved at all.

During those four days, the attack utilized a combination of three attack vectors over the TCP protocol: SYN floods, ACK floods and SYN-ACK floods. The attack campaign sustained for multiple hours at rates exceeding 400-600 million packets per second Continue reading
The Hedge Pdocast Episode 43: Ivan Pepelnjak and Trusting Routing Protocols
Can you really trust what a routing protocol tells you about how to reach a given destination? Ivan Pepelnjak joins Nick Russo and Russ White to provide a longer version of the tempting one-word answer: no! Join us as we discuss a wide range of issues including third-party next-hops, BGP communities, and the RPKI.
Day Two Cloud 056: (Not) Streaming Telemetry
Streaming telemetry is all the rage, but today's show dives into an architecture that forgoes streaming telemetry in favor of other options. We talk about why our guests went in a different direction, the problems they're trying to solve, and how it's working out. Our guests are Kevin Landreth, Director, Service Reliability; and Carl Montanari, Network Reliability Engineer, both at Packet Fabric.
The post Day Two Cloud 056: (Not) Streaming Telemetry appeared first on Packet Pushers.
Day Two Cloud 056: (Not) Streaming Telemetry
Streaming telemetry is all the rage, but today's show dives into an architecture that forgoes streaming telemetry in favor of other options. We talk about why our guests went in a different direction, the problems they're trying to solve, and how it's working out. Our guests are Kevin Landreth, Director, Service Reliability; and Carl Montanari, Network Reliability Engineer, both at Packet Fabric.NTC – A Chat With Jason Edelman
In today’s episode we sit down with Network to Code’s founder, Jason Edelman, to discuss his personal networking journey, how Network to Code came to be, and how he views the networking industry through the lens of network automation and orchestration.
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
The post NTC – A Chat With Jason Edelman appeared first on Network Collective.
Member News: Chapters Focus on Encryption

Lock it down: Several Internet Society chapters across the globe have written about the importance of encryption in recent weeks. The Namibia Chapter wrote about the way encryption can improve privacy and fight against the big business of criminal hacking. “Cybercrime is a global business, often run by multinational outfits,” the Chapter wrote. The Hong Kong Chapter, meanwhile, wrote that “encryption matters to all of us.” Internet users need to work together to protect encryption, the Chapter added. “No party can stand alone to persuade governments to stop creating laws or policies that harm encryption and digital security.”
Freedom for all: The Hong Kong Chapter also called for Internet freedoms to continue in the region as the Chinese government pushes for new security laws there. “We are convinced that the freedoms of speech, press and publication guaranteed by the Basic Law are also applicable to the media industry on the Internet,” the chapter wrote. “Internet users have the freedom and right to obtain, share information and express their expressions, and are protected from being censored, blocked or criminalized.”
Expanding the community: The Nepal Chapter recently wrote about community networks in the country, by highlighting the Rural Continue reading
Sandboxing in Linux with zero lines of code
Modern Linux operating systems provide many tools to run code more securely. There are namespaces (the basic building blocks for containers), Linux Security Modules, Integrity Measurement Architecture etc.
In this post we will review Linux seccomp and learn how to sandbox any (even a proprietary) application without writing a single line of code.
Tux by Iwan Gabovitch, GPL
Sandbox, Simplified Pixabay License
Linux system calls
System calls (syscalls) is a well-defined interface between userspace applications and the operating system (OS) kernel. On modern operating systems most applications provide only application-specific logic as code. Applications do not, and most of the time cannot, directly access low-level hardware or networking, when they need to store data or send something over the wire. Instead they use system calls to ask the OS kernel to do specific hardware and networking tasks on their behalf:
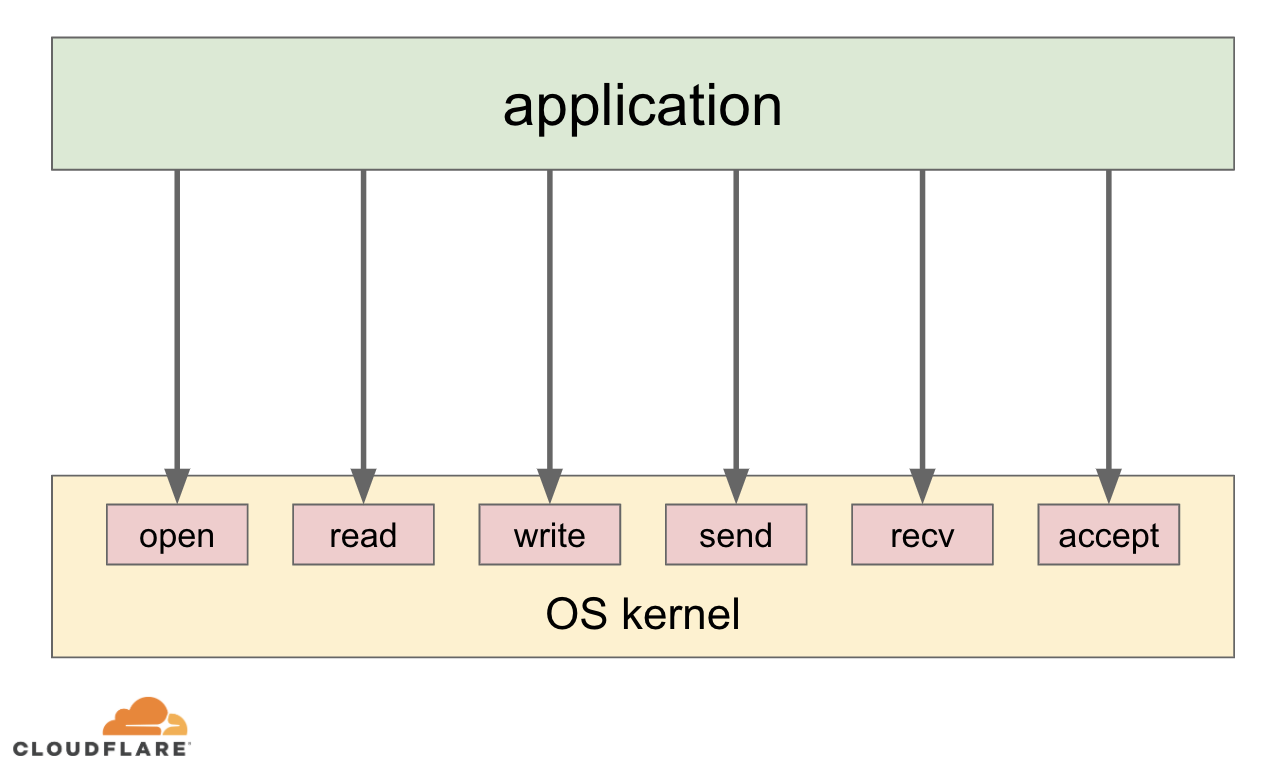
Apart from providing a generic high level way for applications to interact with the low level hardware, the system call architecture allows the OS kernel to manage available resources between applications as well as enforce policies, like application permissions, networking access control lists etc.
Linux seccomp
Linux seccomp is yet another syscall on Linux, but it is a bit Continue reading
Worth Reading: Lies, Damned Lies, and Keynotes
Got sick and tired of conference keynotes? You might love the Lies, Damned Lies, and Keynotes rant by Corey Quinn. Here are just two snippets:
They’re selling a fantasy, and you’ve been buying it all along.
We’re lying to ourselves. But it feels better than the unvarnished truth.
Enjoy!
CVE-2020-5902: Helping to protect against the F5 TMUI RCE vulnerability

Cloudflare has deployed a new managed rule protecting customers against a remote code execution vulnerability that has been found in F5 BIG-IP’s web-based Traffic Management User Interface (TMUI). Any customer who has access to the Cloudflare Web Application Firewall (WAF) is automatically protected by the new rule (100315) that has a default action of BLOCK.
Initial testing on our network has shown that attackers started probing and trying to exploit this vulnerability starting on July 3.
F5 has published detailed instructions on how to patch affected devices, how to detect if attempts have been made to exploit the vulnerability on a device and instructions on how to add a custom mitigation. If you have an F5 device, read their detailed mitigations before reading the rest of this blog post.
The most popular probe URL appears to be /tmui/login.jsp/..;/tmui/locallb/workspace/fileRead.jsp followed by /tmui/login.jsp/..;/tmui/util/getTabSet.jsp, /tmui/login.jsp/..;/tmui/system/user/authproperties.jsp and /tmui/login.jsp/..;/tmui/locallb/workspace/tmshCmd.jsp. All contain the critical pattern ..; which is at the heart of the vulnerability.
On July 3 we saw O(1k) probes ramping to O(1m) yesterday. This is because simple test patterns have been added to scanning tools and small test programs made available by Continue reading
History of USENET with Steve Bellovin
Steve Bellovin began working on networks as a system administrator, helping to build USENIX, which supports operating system research. His work as a system administrator drew his interest into security and cryptographic protection of data, leading him into working on some of the foundational protocols on the Internet.
Dictionary: Finger Defined Networking

Because 'command line' is deprectated
The post Dictionary: Finger Defined Networking appeared first on EtherealMind.
BGP EVPN Underlay Network with OSPF
Introduction
Infrastructure AS Numbering and IP Addressing Scheme
Latest U.S. ‘Anti-Encryption’ Bill Threatens Security of Millions

The Lawful Access to Encrypted Data Act recently introduced to U.S. Congress may be the worse in a recent string of attacks on encryption, our strongest digital security tool online.
While the recently-amended EARN IT Act would leave strong encryption on unstable ground if passed into law, the Lawful Access to Encrypted Data Act (LAEDA) is a direct assault on the tool millions of people rely on for personal and national security each day.
LAEDA would facilitate the death of end-to-end encryption by forcing companies to provide “technical assistance” to access encrypted data upon request by law enforcement investigations.
The problem is the only way for companies to comply would be to build backdoors into their products and services, or not use encryption at all, making everyone more vulnerable to the same crime we are all trying to prevent. To be clear – we’re talking about the same encryption used to keep activities like online banking, working from home, telehealth, and talking with friends secure online.
The Internet Society raised its concerns in an open letter to the co-sponsors of LAEDA in the Senate, which was signed by over 75 global cybersecurity experts, civil society organizations, companies, and Continue reading
Building Cloudflare TV from scratch


Cloudflare TV is inspired by television shows of the 90s that shared the newest, most exciting developments in computing and music videos. We had three basic requirements for Cloudflare TV:
- Guest participation should be as simple as joining a Zoom call
- There should be 24x7 programming. Something interesting should be playing all the time
- Everything should happen in the cloud and we should never have to ask anyone “to leave their computer on” to have the stream running 24 hours a day

We didn’t set out to build Cloudflare TV from scratch
Building a lot of the technology behind Cloudflare TV from scratch was not part of the plan, especially given our aggressive timeline. So why did we decide to pursue it? After evaluating multiple live streaming solutions, we reached the following conclusion:
- 24x7 linear streaming is not something that is a priority for most video streaming platforms. This makes sense: the rise of video-on-demand and event-based live streaming has come at the expense of linear streaming.
- Most broadcasting platforms have their own guest apps which must be downloaded and set up in advance. This introduces unnecessary friction compared to clicking a link in the calendar invite to join a Continue reading
