Weekend Reads 060520
Memory isolation is a cornerstone security feature in the construction of every modern computer system. Allowing the simultaneous execution of multiple mutually distrusting applications at the same time on the same hardware, it is the basis of enabling secure execution of multiple processes on the same machine or in the cloud. The operating system is in charge of enforcing this isolation, as well Continue reading
Ciena Posts Strong Q2 Earnings Beat
Revenues during the quarter reached $894 million, up 3.4% year over year, exceeding investor...
VMware Buys Lastline to Boost Security NDR
Lastline is known for its anti-malware research and artificial intelligence-powered network...
Heavy Networking 521: Diving Into Dell Technologies’ SONiC Network OS For The Enterprise (Sponsored)
Today's Heavy Networking podcast explores Dell Technologies' SONiC network OS for enterprises. This distro offers hardware support across multiple ASIC platforms and full enterprise support. We dive into technical details, discuss the business and operational value propositions, explore use cases, and more. Dell Technologies is our sponsor for this episode. Our guest is Alley Hasan, Director, Product Strategy and Business Development.Heavy Networking 521: Diving Into Dell Technologies’ SONiC Network OS For The Enterprise (Sponsored)
Today's Heavy Networking podcast explores Dell Technologies' SONiC network OS for enterprises. This distro offers hardware support across multiple ASIC platforms and full enterprise support. We dive into technical details, discuss the business and operational value propositions, explore use cases, and more. Dell Technologies is our sponsor for this episode. Our guest is Alley Hasan, Director, Product Strategy and Business Development.
The post Heavy Networking 521: Diving Into Dell Technologies’ SONiC Network OS For The Enterprise (Sponsored) appeared first on Packet Pushers.
Attention Resource Deficit

How much did your last laptop cost? You probably know down to the penny. How much time did it take for you to put together your last Powerpoint deck or fix an issue for a customer? You can probably track that time in the hours you recorded on your timesheet. What about the last big meeting you had of the department? Can you figure out how many hours combined of time that it took to get the business discussed? Pretty easy to calculate when you know how many people and how long it took.
All of these examples are ways that we track resources in the workplace. We want to know how many dollars were invested in a particular tool. We want to figure out how many hours someone has worked on a project or a proposal. We want to know how much of the company’s resources are being invested so we can track it and understand productivity and such. But when’s the last time you tracked your personal resources? I’m not talking about work you do or money you spend. I’m talking about something more personal than that. Because one of the things that I’ve seen recently that is Continue reading
How to Train Employees Not to Fall for Phishing Attacks
“I know it’s an extremely overused term in security awareness, but gamification is extremely...
How we use HashiCorp Nomad
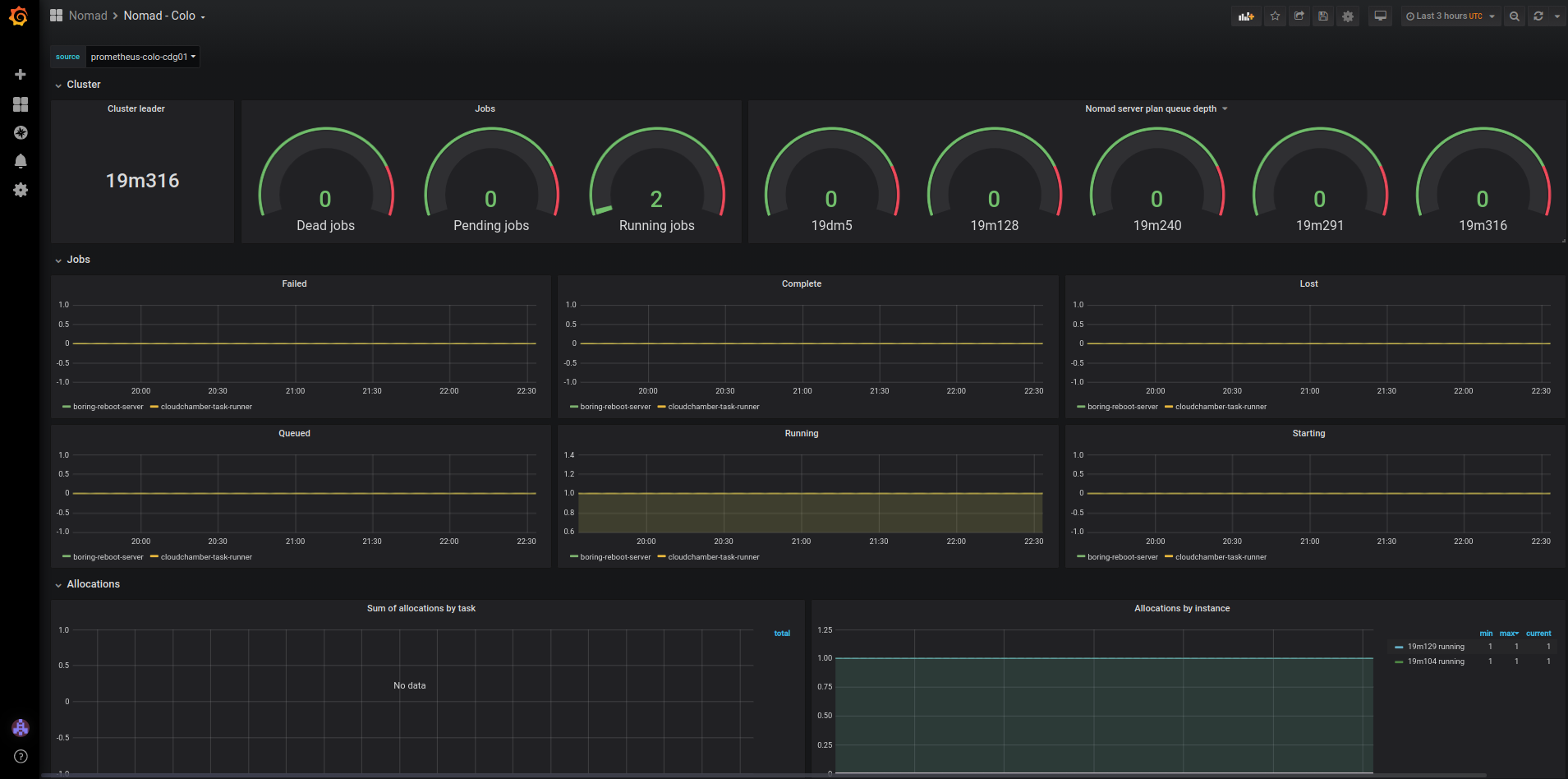
In this blog post, we will walk you through the reliability model of services running in our more than 200 edge cities worldwide. Then, we will go over how deploying a new dynamic task scheduling system, HashiCorp Nomad, helped us improve the availability of services in each of those data centers, covering how we deployed Nomad and the challenges we overcame along the way. Finally, we will show you both how we currently use Nomad and how we are planning on using it in the future.
Reliability model of services running in each data center
For this blog post, we will distinguish between two different categories of services running in each data center:
- Customer-facing services: all of our stack of products that our customers use, such as caching, WAF, DDoS protection, rate-limiting, load-balancing, etc.
- Management services: software required to operate the data center, that is not in the direct request path of customer traffic.
Customer-facing services
The reliability model of our customer-facing services is to run them on all machines in each data center. This works well as it allows each data center’s capacity to scale dynamically by adding more machines.
Scaling is especially made easy thanks to Continue reading
Weekly Wrap: Cisco Licks Wounds, Targets Next Cloud Computing Wave
SDxCentral Weekly Wrap for June 5, 2020: Cisco admits to missing cloud's first wave; ThousandEyes...
Video: Public Cloud Networking Overview
Donal O Duibhir was trying to get me to present at INOG for ages, and as much as I’d love to get to Ireland we always had a scheduling conflict.
Last week we finally made it work - unfortunately only in a virtual event, so I got none of the famous Irish beer - and the video about alternate universes of public cloud networking is already online.
Maximilian Wilhelm had great fun turning my usual black-and-white statements into tweets, here’s a selection of them:
DevAsc – Introduction to JSON
Introduction
JSON, JavaScript Object Notation, is one of the usual suspects when it comes to network automation. YAML and XML being the other two. It’s easy for machines to parse and generate and the readability is good, better than XML, although YAML is easier for humans to read.
JSON is based on a subset of the JavaScript programming language, as the name implies.
JSON, just like YAML, supports single values, lists, and key/value pairs.
JSON is commonly used to interchange between different formats.
Syntax
JSON has no requirement for indentation or white space, which YAML has. That said, to make it human readable, it still makes sense to use white space and spaces, most likely either two or four.
- Strings MUST use double quotes
- Object literal names MUST be lowercase (null, false, true etc)
- Special characters need to be escaped
- { says “begin object”
- } says “end object”
- [ says “begin array”
- ] says “end array”
- : separates key and value in key/value pair
- , separates key/value pair in an object or separates values in an array, think of it as “expect another one”
Data Types
JSON supports the following data types:
- Object
- String
- Number
- Boolean
- Null
- Array
We’ll Continue reading
Palo Alto Networks, Inc. Announces Proposed $1.75 Billion Offering of Convertible Senior Notes Due 2025
Palo Alto Networks will offer $1.75 billion aggregate principal amount of convertible senior notes...
Cisco Catches Dozens of IOS Security Bugs
The security vulnerabilities could have allowed attackers to gain remote access and execute...
Daily Roundup: VMware’s Gelsinger High on Tech, Software, Cloud
VMware’s Gelsinger rode a tech, software, cloud high; NetApp nabbed Spot; and the coronavirus...
Making Intermediaries Liable for Encrypted Content Breaks Trust and Security

In December 2018, the Indian Ministry of Electronics & Information Technology (MeitY) proposed a significant change to its intermediary rules. The draft Information Technology [Intermediaries Guidelines (Amendment) Rules] 2018 seeks to tie tech platforms’ (e.g., social media) protections from liability to an obligation to monitor and filter their users’ content. One of the proposed obligations is to ensure the traceability of messages, even if a service is end-to-end encrypted.
India is just one of many countries around the world experimenting with the idea that Internet intermediaries – specifically social media companies, like Facebook and Twitter – should no longer have immunity from liability for the content shared by their users. Other examples include the U.S. Eliminating Abusive and Rampant Neglect of Interactive Technologies Act of 2020 (the EARN IT Act), and the recent U.S. Executive Order on Preventing Online Censorship.
The motivation for changing the status quo varies, from wanting traceability of messages to counter the spread of disinformation or CSEM, to stopping objectionable content from being spread on social media, to preventing political messages from being labeled (e.g., as “misleading information”). Similarly, the approaches being considered to achieve this vary, ranging from Continue reading
Evolution of Virtual Conferences With Keith Townsend

A few weeks ago I sat down with Keith Townsend from the CTO Advisor and we discussed the future of physical and virtual events.
The post Evolution of Virtual Conferences With Keith Townsend appeared first on EtherealMind.
Coronavirus Cleaves SD-WAN Revenue Growth
The SD-WAN market was on track for another year of record revenue growth right up until the...
Telecom Gear Sales Dropped During Q1, Dell’Oro Says
Huawei, Nokia, and Cisco all saw their respective market share drop, while Ericsson was flat and...