New IP and Emerging Communications Technologies
A "New IP" framework was proposed to an ITU Study Group last year. This framework envisages a resurgence of a network-centric view of communications architectures where application behaviours are moderated by network-managed control mechanisms. It's not the first time that we’ve seen proposals to rethink the basic architecture of the Internet’s technology and it certainly won’t be the last. But is it going to really going to influence the evolution of the Internet? What can we observe about emerging technologies that will play a critical role in the coming years? Here’s my personal selection of recent technical innovations that I would add into the set of emerging technologies that will exercise a massive influence over the coming ten years.Is Open Source the Way Forward for SD-WAN?
An open source alternative to proprietary SD-WANs could become the de facto industry standard, said...
Worth Exploring: Arista EVPN-Based Automation Virtual Lab
David Varnum created a fantastic leaf-and-spine fabric of vEOS switches running with GNS3 and automated with Ansible playbooks.
Not only that - his blog post includes detailed setup instructions, and the corresponding GitHub repository contains all the source code you need to get it up and running.
Daily Roundup: HPE Slashes Salaries
COVID-19 wrecked HPE's latest earnings; Verizon updates its 5G plans; and Palo Alto Networks posted...
Heavy Networking 518: Learning To Live With SNMP
Perhaps the most arcane technology in networking is the Simple Network Management Protocol (SNMP), which, despite its name, is one of the utmost confusing pieces of technology to actually use. Guests Michael W. Lucas and Allan Jude share tips and lessons on how to get the most you can out of this protocol.
The post Heavy Networking 518: Learning To Live With SNMP appeared first on Packet Pushers.
Heavy Networking 518: Learning To Live With SNMP
Perhaps the most arcane technology in networking is the Simple Network Management Protocol (SNMP), which, despite its name, is one of the utmost confusing pieces of technology to actually use. Guests Michael W. Lucas and Allan Jude share tips and lessons on how to get the most you can out of this protocol.Member News: Internet Society Chapters Assist Communities with Telework, Remote Education

Keep working: In recent months, several Internet Society Chapters have focused on helping people to keep working during COVID-19 lockdowns. The Benin Chapter recently published a guide to remote work, with recommendations for videoconferencing apps, project management software, and file storage services. “We are facing a real health crisis, COVID-19, which is shaking up our habits and pushing companies to adapt to new working methods,” the Chapter’s post says. “Authorizing employees to telecommute is the ideal solution for the continuity of your activity and avoiding contagion within your teams.”
Building your brand: Meanwhile, the Israel Chapter hosted a webinar on employment and careers in the digital industry. Speaker Shani Haddad, CEO and founder of Brainnu, talked about the importance of people marketing themselves and telling their own stories.
Learning at a distance: It’s not just workers dealing with new situations during the COVID-19 pandemic. The Samoan Chapter has posted about distance learning, noting that the Samoa Information Technology Association has developed an e-learning platform for students attending school from home. Education is “one of the key areas that is being heavily affected by the lockdown,” the post notes.
No censorship: The Chapter in Spain has raised concerns Continue reading
Tom’s Virtual Corner at Cisco Live US 2020

One of the things that I look forward to most during Cisco Live is the opportunity to meet with people. It’s been quite a few years since I’ve been to a session during the conference. My work with Tech Field Day has kept me very busy for the past several Cisco Live events. But at the end of the day I enjoy strolling down to the Social Media hub and talking to anyone I see. Because people make Cisco Live what it is.
The Legend of Tom’s Corner has grown over the years. It’s more than just a few tables in a place where people hang out. It stands for a community. It means a lot to so many different people. It’s about meeting new friends and catching up with old ones and feeling like you belong. For so many, Tom’s Corner and the Social Media Hub is the center of Cisco Live.
And yet, we now live in extraordinary times. The plan we had for what Cisco Live would look like for us earlier this year is radically different right now. Prohibitions on travel and meetings in large groups means we will be experiencing Cisco Live from our homes Continue reading
Verizon 5G Challenges Linger as Network Gains Uplink
“Competition in the near term will be a marketing war of coverage and speed," said William Ho,...
Releasing Cloudflare Access’ most requested feature
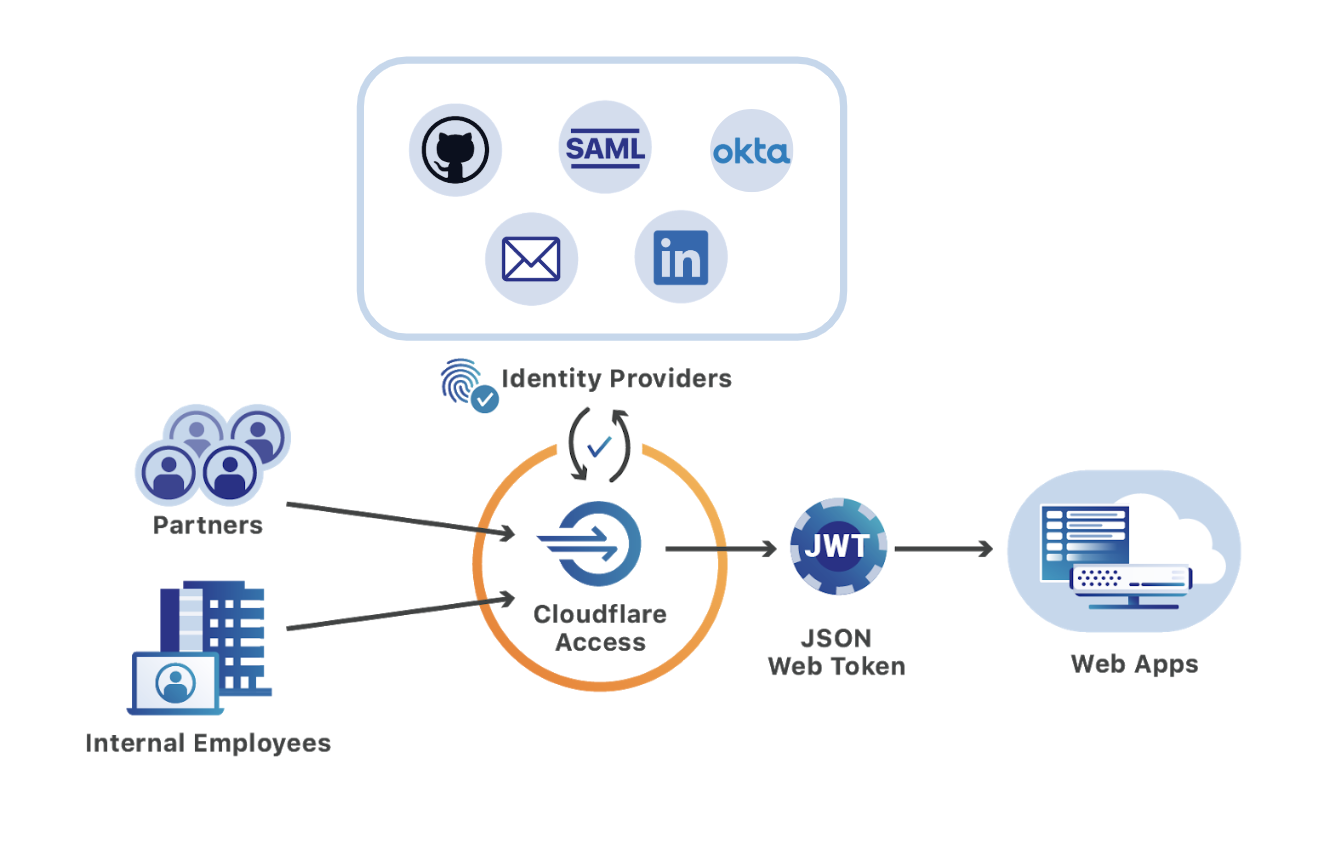
Cloudflare Access, part of Cloudflare for Teams, replaces legacy corporate VPNs with Cloudflare’s global network. Instead of starting a VPN client to backhaul traffic through an office, users visit the hostname of an internal application and login with your team’s SSO provider. While the applications feel like SaaS apps for end users, your security and IT departments can configure granular controls and audit logging in a single place.
Since Access launched two years ago, customers have been able to integrate multiple SSO providers at the same time. This MultiSSO option makes it seamless for teams to have employees login with Okta or Azure AD while partners and contractors use LinkedIN or GitHub.
The integrations always applied globally. Users would see all SSO options when connecting to any application protected by Cloudflare Access. As more organizations use Cloudflare Access to connect distributed and mixed workforces to resources, listing every provider on every app no longer scales.
For example, your team might have an internal GitLab instance that only employees need to access using your corporate G Suite login. Meanwhile, the marketing department needs to share QA versions of new sites with an external agency who authenticates with LinkedIn. Asking both Continue reading
Weekly Wrap: Oracle Challenges AWS to Cloud Calculator Duel
SDxCentral Weekly Wrap for May 22, 2020: Oracle claims cloud cost-superiority over AWS; Google hugs...
Video: Cisco SD-WAN Solution Architecture and Components
After describing Cisco SD-WAN fundamentals and its network abstraction mechanisms, David Penaloza explained the components of Cisco SD-WAN solution and its architecture, including in which plane each element operates and its assigned role in the overlay network.
It’s 2020 And Android’s IPv6 Is Still Broken
I got into some interesting discussions about IPv6 on Twitter. Then someone asked if Android is getting DHCPv6 support in version 11 of the OS.
When IPv6 was developed, initially with RFC 2460, there was this idea that:
Forget all you've learned about IPv4, and design IPv6 from the ground up
This sounds good in theory but ignores completely the lessons we’ve learned from IPv4. Not to mention, there is no such thing as greenfield. Almost all networks, are existing ones, you don’t get to start all over again. There was this very shiny view of end to end connectivity, /64 everywhere and only SLAAC allowed. I get all of that, it’s like saying “I wish there were no wars”, but unfortunately, people are stupid, so there will be wars. There’s this naivety, similar to a teenager that is growing up. You want to change the world, then you realize the world is run by money, mega corps, and dirty politicians.
This whole mess led to the holy wars of SLAAC + RDNSS vs DHCPv6. Please note that SLAAC Continue reading
HPE Cuts Salaries Companywide as COVID-19 Wrecks Q2
HPE reported fiscal 2020 Q2 revenues of $6 billion, down 15% from a year ago, with a drop in...
Palo Alto Networks Weathers Pandemic With Strong Earnings
The company’s Q3 revenues hit $869.4 million, up 20% year over year, bolstered by a pandemic...