Automation Story: Building a Network Inventory Database
What’s the next logical automation step after you cleaned up device configurations and started using configuration templates? It obviously depends on your pain points; for Anne Baretta it was a network inventory database stored in SQL tables (and thus readily accessible from his other projects).
Notes
- I’m always amazed that we have to solve simple problems decades after the glitzy slide decks from network management vendors proclaimed them solved;
- I’m also saddened that it’s often really hard to get data out of a network management product;
- Check out our network automation course when you’re ready to start your own automation journey.
Automation Story: Building a Network Inventory Database
What’s the next logical automation step after you cleaned up device configurations and started using configuration templates? It obviously depends on your pain points; for Anne Baretta it was a network inventory database stored in SQL tables (and thus readily accessible from his other projects).
Notes
- I’m always amazed that we have to solve simple problems decades after the glitzy slide decks from network management vendors proclaimed them solved;
- I’m also saddened that it’s often really hard to get data out of a network management product;
- Check out our network automation course when you’re ready to start your own automation journey.
CEX (Code EXpress) 03. Variable is better than fixed.
Hello my friend,
We are slowly but surely start talking about more and more useful and interesting topics staying yet at a basic level. Today you will learn about variables in Python, as variables are obviously the basic building block of any tool.
Network automation training – boost your career
Don’t wait to be kicked out of IT business. Join our network automation training to secure your job in future. Come to NetDevOps side.
How does the training differ from this blog post series? Here you get the basics and learn some programming concepts in general, whereas in the training you get comprehensive set of knowledge with the detailed examples how to use Python for the network and IT automation. You need both.
What are we going to do today?
We will learn how to create and use in Python 3.8 several types of the variables such as:
- Numbers
- Strings
- Boolean
The different types of variables are used for the different purposes, that’s why the more variables’ type you know, the better code you can write. We must admit that this list of the variables isn’t complete. That is why in the next couple of blogposts you will see Continue reading
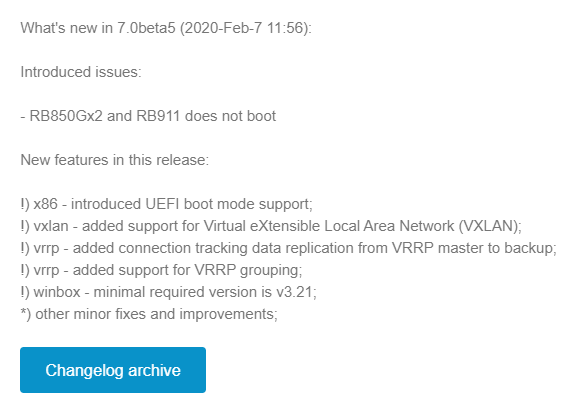
MikroTik – RouterOSv7 first look – VxLAN
VxLAN support added in 7.0beta5
MikroTik announced VxLAN support on Valentine’s Day (Feb 14th) of 2020.
This is a significant feature addition for RouterOSv7 as it will pave the way for a number of other additions like EVPN in BGP.
It will also give MikroTik the ability to appeal to enterprises and data centers that might need cost-effective VxLAN capable devices.
Service Providers are also moving towards VxLAN as a future replacement for VPLS so this is helpful for that market as well.
Download the OVA here:
https://download.mikrotik.com/routeros/7.0beta5/chr-7.0beta5.ova
Implementation
The initial release of VxLAN is based on unicast and multicast to deliver Layer 2 frames.
As there is no EVPN support, the VTEPs must be manually configured for each endpoint in a full mesh configuration.
The VxLAN interface can then be bridged to a physical ethernet port or VLAN interface to deliver the traffic to the end host.
Lab Example
Here is an overview lab in EVE-NG with a basic setup using 3 linux servers on the same 10.1.1.0/24 subnet which is carried as an overlay by VxLAN.
VxLAN reachability for VTEPs is acheived with OSPFv2 and loopback addresses.
VNI: 100
Continue reading
Real-time DDoS mitigation using BGP RTBH and FlowSpec
DDoS Protect is a recently released open source application running on the sFlow-RT real-time analytics engine. The software uses streaming analytics to rapidly detect and characterize DDoS flood attacks and automatically applies BGP remote triggered black hole (RTBH) and/or FlowSpec controls to mitigate their impact. The total time to detect and mitigate an attack is in the order of a second.The combination of multi-vendor standard telemetry (sFlow) and control (BGP FlowSpec) provide the real-time visibility and control needed to quickly and automatically adapt the network to address a range of challenging problems, including: DDoS, traffic engineering, and security.
Solutions are deployable today: Arista BGP FlowSpec describes the recent addition of BGP FlowSpec support to Arista EOS (EOS has long supported sFlow), and sFlow available on Juniper MX series routers describes the release of sFlow support on Juniper MX routers (which have long had BGP FlowSpec support). This article demonstrates DDoS mitigation using Arista EOS. Similar configurations should work with any router that supports sFlow and BGP FlowSpec.
The diagram shows a typical deployment scenario in which an instance of sFlow-RT (running the DDoS Protect application) receives sFlow from the site router (ce-router). A Continue reading
Must Read: Impact of Tomahawk-4 on Data Center Fabric Designs
Dinesh Dutt, a pragmatic IP routing guru, the mastermind behind great concepts like simplified BGP configuration, and one of the best ipSpace.net authors, finally decided to start blogging. His first article: describing the impact of having 256 100GE ports in a single ASIC (Tomahawk 4). Hope you’ll enjoy his musings as much as I did ;)
Must Read: Impact of Tomahawk-4 on Data Center Fabric Designs
Dinesh Dutt, a pragmatic IP routing guru, the mastermind behind great concepts like simplified BGP configuration, and one of the best ipSpace.net authors, finally decided to start blogging. His first article: describing the impact of having 256 100GE ports in a single ASIC (Tomahawk 4). Hope you’ll enjoy his musings as much as I did ;)
Daily Roundup: Cloud Titans Tank Arista’s Q4
Cloud titans tanked Arista’s Q4; US charged Huawei with theft and espionage; and Microsoft JEDI...
BiB 088: Mastering Python Networking Third Edition by Eric Chou
Eric Chou, author of Master Python Networking Third Edition, discusses what's new in this edition of the book. Quite a lot!
The post BiB 088: Mastering Python Networking Third Edition by Eric Chou appeared first on Packet Pushers.
BiB 088: Mastering Python Networking Third Edition by Eric Chou
Eric Chou, author of Master Python Networking Third Edition, discusses what's new in this edition of the book. Quite a lot!Is SD-Branch Worth the Hype?
As the SD-WAN market explodes, some service providers are pushing SD-branch as a way to build an...
Heavy Networking 502: Get Off My VLAN! Old Network Engineers On What New Engineers Should Know
As more abstractions and automation layers creep into the network, are network engineers losing their grasp on core fundamentals? Three grumpy old network engineers ponder this question, talk about how we got here, and what can be done about it. Our guests are Chris Young and Ivan Pepelnjak.Heavy Networking 502: Get Off My VLAN! Old Network Engineers On What New Engineers Should Know
As more abstractions and automation layers creep into the network, are network engineers losing their grasp on core fundamentals? Three grumpy old network engineers ponder this question, talk about how we got here, and what can be done about it. Our guests are Chris Young and Ivan Pepelnjak.
The post Heavy Networking 502: Get Off My VLAN! Old Network Engineers On What New Engineers Should Know appeared first on Packet Pushers.
Member News: Internet Society Chapters Focus on Security

Security on your mind: The Internet Society’s Chapter in Benin recently hosted a conference focused on online security and on connectivity issues. Much of the discussion focused on instability of connections in the country, with participants concerned about degraded connections. Participants also talked about limited coverage for mobile services. On the topic of security, speakers urged Internet users to regularly change their passwords, avoid default passwords, and prevent third-party apps from connecting to the services they use.
Secure messages: The Israeli Chapter has focused on the security of messaging and social media apps recently. The Chapter recently posted a guide on how to prevent Instagram accounts from being hacked and a guide on how users can protect their privacy on the Tik Tok messaging app.
Privacy for the young ones: Meanwhile, the Chapter in Portugal, working with the Kids Safe on the Net project, has launched an initiative to improve awareness among Portuguese youth about the importance of online privacy and how they can maintain their privacy.
Good privacy: The Netherlands Chapter recently gave its support to the Good ID initiative, an approach to identity management that prioritizes data privacy and security. Good ID aims to give Internet users Continue reading
Arista Finally Makes Big Switch Official, Disappoints in Q4
Meanwhile, Arista’s Q4 revenue declined, and took a big hit from cloud and service providers...
The Force Sides With Amazon, Microsoft JEDI Training Stalls
"It's important that the numerous evaluation errors and blatant political interference that impact...
US Charges Huawei With Theft, Espionage
Huawei is charged with conspiring to steal intellectual property from six U.S. companies, violating...
Weekly Wrap: Coronavirus Kills MWC Barcelona
SDxCentral Weekly Wrap for Feb. 14, 2020: GSMA cancels this year's MWC Barcelona event; Cisco CEO...
Fast Friday – Networking Field Day 22 Thoughts
Since I’m on the road again at Networking Field Day this week, I have had some great conversations with the delegates and presenters. A few stray thoughts that may develop into full blown blog posts at some point, but I figured I could get some of them out here for some quick entertainment.
- The startup model means flexibility. That also means you can think about problems in a new light. So it would follow that you get to develop some new idea without a mountain of technical debt. Things like archaic platforms and crusty old user interfaces. You’d be surprised the amount of stuff that gets carried forward as technical debt.
- Integrating products isn’t easy. Even if you think you’ve got the right slot for your newest acquisition you may find it isn’t the best fit overall. Or, even better, you may find a synergy you didn’t know existed because of a forgotten tool. Very rarely does anything just neatly fit into all your plans.
- The more guest Wi-Fi I have to register for, the more I long for the days of Passport and OpenRoaming. If you already know who I am, why oh why must I continually register. Who Continue reading
Podcast: BGP in Public Cloud Revisited
After my response to the BGP is a hot mess topic, Corey Quinn graciously invited me to discuss BGP issues on his podcast. It took us a long while to set it up, but we eventually got there… and the results were published last week. Hope you’ll enjoy our chat.

