Daily Roundup: Nokia Slashes Jobs
Nokia cut 180 jobs, with more to come; Equinix pushed to the edge with Packet acquisition; and...
Microsoft Patches Critical Windows Security Flaw
“For the U.S. government to share its discovery of a critical vulnerability with a vendor is...
SDxCentral Adds Career Resources for IT Professionals
SDxCentral announces the additional of career resources for IT professions to SDxCentral.com. Check...
AT&T Wins 5G Contract for Nellis Air Force Base
AT&T plans to equip the base with 5G infrastructure to support more than 40,000 Air Force...
Deep Dive: U.S. Federal Government’s Security and Privacy Practices

In April 2019, the Internet Society’s Online Trust Alliance released its 10th Annual Online Trust Audit & Honor Roll. The Audit looks at the security and privacy practices of over 1,000 of the top sites on the Internet, from retailers to government sites. In this post we will take a deeper dive into the U.S. Federal Government sector of the Audit. The Government sector is defined as the top 100 sites in the U.S. Federal Government by traffic (based on Alexa ranking). Given the nature of the U.S. Government compared to companies, this sample has some unique properties, namely site security.
The most obvious place the government excels is in the area of encryption. The reason for this is largely due to a mandate from the Homeland Security Department that all U.S. Government sites be encrypted, but the standard should still be the same for any site. Put another way, the other sectors in the Audit do not have an excuse for lagging in security.
In site security the Government sector fared the best with 100% adoption of “Always-On Secure Socket Layer” (AOSSL) and/or “HTTP Strict Transport Security” (HSTS), compared to 91% of sites overall. The Continue reading
Google Partners With CNCF, HackerOne on Kubernetes Bug Bounty
With more people looking for vulnerabilities, the safer and more secure Kubernetes will be,...
Embattled GTT Fortifies Its SD-WAN With Fortinet
The deal comes after a dismal second half of 2019 that saw the company's stock prices plunge from a...
A cost-effective and extensible testbed for transport protocol development
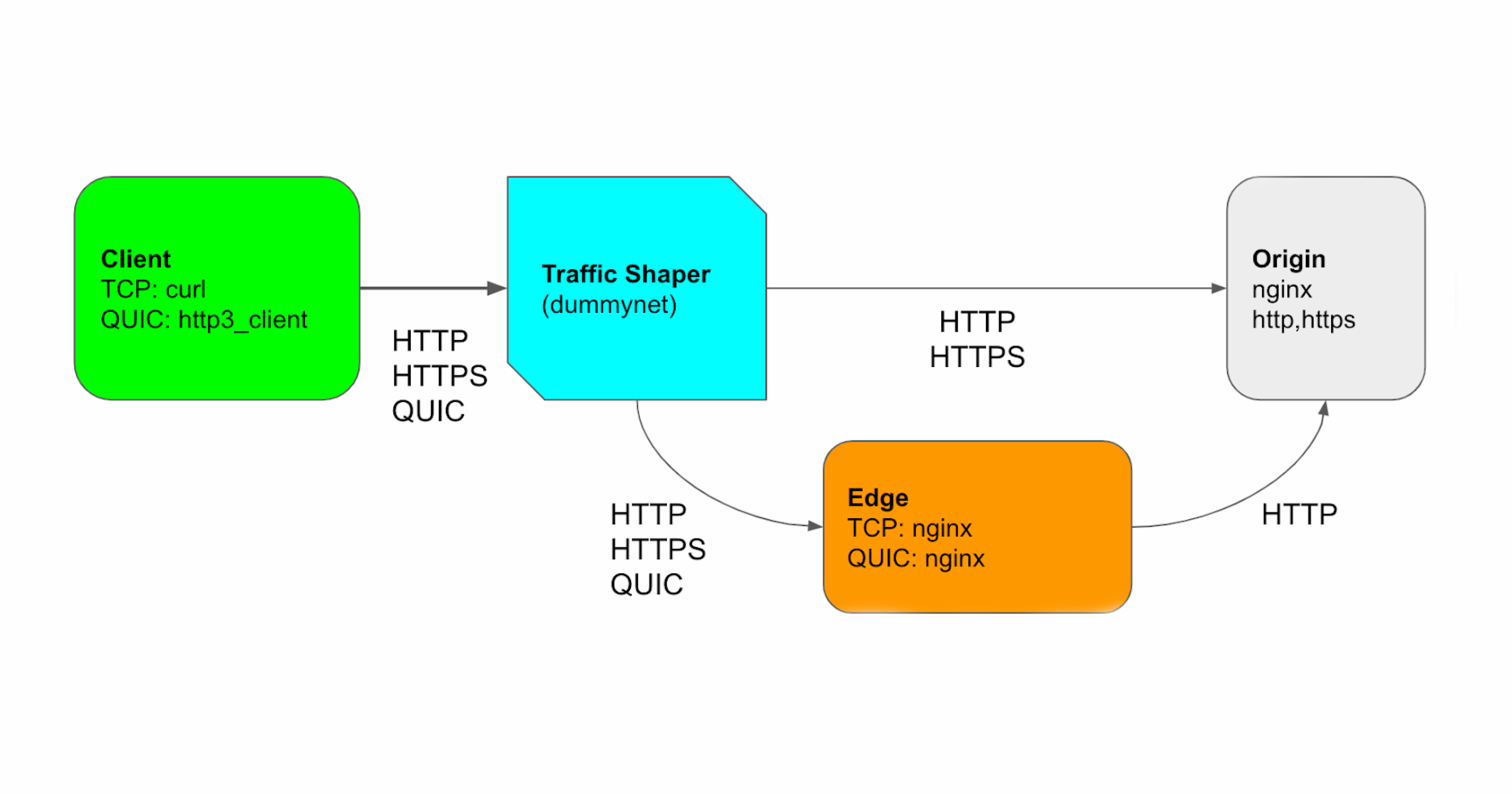
This was originally published on Perf Planet's 2019 Web Performance Calendar.
At Cloudflare, we develop protocols at multiple layers of the network stack. In the past, we focused on HTTP/1.1, HTTP/2, and TLS 1.3. Now, we are working on QUIC and HTTP/3, which are still in IETF draft, but gaining a lot of interest.
QUIC is a secure and multiplexed transport protocol that aims to perform better than TCP under some network conditions. It is specified in a family of documents: a transport layer which specifies packet format and basic state machine, recovery and congestion control, security based on TLS 1.3, and an HTTP application layer mapping, which is now called HTTP/3.
Let’s focus on the transport and recovery layer first. This layer provides a basis for what is sent on the wire (the packet binary format) and how we send it reliably. It includes how to open the connection, how to handshake a new secure session with the help of TLS, how to send data reliably and how to react when there is packet loss or reordering of packets. Also it includes flow control and congestion control to interact well with other transport protocols in Continue reading
Get Up To Speed on NSX Cloud with 5 Easy Resources
Over the last few years, as public and hybrid cloud adoption proliferated, organizations began looking for seamless and consistent manageability of their public cloud and private cloud workloads. This is one of the reasons why VMware brought NSX Cloud to the market.
Overview of NSX Cloud
In a nutshell, NSX Cloud provides consistent networking and security across hybrid and multi-cloud workloads. The key benefits and features of NSX Cloud include:
- Single-pane-of-glass visibility
- Essential networking capabilities
- Consistent security policy
- Granular micro-segmentation across on-premises and native public cloud environments such as AWS and Azure
NSX Cloud plays a key role in VMware’s Virtual Cloud Network vision of connecting and protecting workloads of all types (VMs, containers, bare metal) from data center to cloud to edge.
“With NSX Cloud, we got a very compact firewall policy—easy to review and easy to manage. The power, administratively, is that we go to one place to update our policy and when we publish it, it automatically deploys it to every cloud server instance. This was a big win for us.”
Brian Jemes, Network Manager, University of Idaho
VMworld US 2018, NET1516BU
Top 5 Resources on NSX Cloud
Here is a compilation of the Continue reading
Selective Activity has Consequences

On doing the things you do well
The post Selective Activity has Consequences appeared first on EtherealMind.
Public Cloud Networking Security is Different
If you’re running a typical (somewhat outdated) enterprise data center, you’re using tons of VLANs and firewalls, use VLANs as security zones, and push inter-VLAN traffic through firewalls for inspection. Security vendors love that approach - when inspecting traffic they can add no value to (like database- or backup sessions), the firewalls quickly become choke points that have to be upgraded.
Read more ...Network Break 266: Accenture Buys Symantec Security Services Biz; Cisco Reorganizes Around Intent-Based Networking
Today's Network Break analyzes an HPE/Cumulus Networks deal on Ethernet storage switches, yet another open-source network OS project from the Linux Foundation, Accenture's purchase of Symantec's security services biz from Broadcom, a Cisco reorganization of its enterprise networking businesses, and more tech and IT news.
The post Network Break 266: Accenture Buys Symantec Security Services Biz; Cisco Reorganizes Around Intent-Based Networking appeared first on Packet Pushers.
Network Break 266: Accenture Buys Symantec Security Services Biz; Cisco Reorganizes Around Intent-Based Networking
Today's Network Break analyzes an HPE/Cumulus Networks deal on Ethernet storage switches, yet another open-source network OS project from the Linux Foundation, Accenture's purchase of Symantec's security services biz from Broadcom, a Cisco reorganization of its enterprise networking businesses, and more tech and IT news.BGP in 2019
It has become a tradition each January for me to report on the behaviour of the inter-domain routing system over the past year, looking in some detail at some metrics from the routing system that can show the essential shape and behaviour of the underlying interconnection fabric of the Internet.Daily Roundup: Citrix Bug Gets Uglier
The bug impacts Citrix's ACD platform; Samsung acquired TeleWorld to boost its U.S. RAN efforts;...
Vodafone UK Activates 5G Multi-Operator RAN
5G network sharing deals have gained momentum as carriers look to decrease the cost of deploying...